Cybersecurity Directory for the Education Sector & Solutions
From K-12 school districts to global research universities, cyberattacks targeting the education sector have surged by 44% year-over-year, driven by poor endpoint security, open-access networks, and underfunded IT infrastructure. Academic institutions manage vast troves of student records, health data, and research IP—all high-value targets for ransomware groups, data brokers, and state-sponsored hackers. The diversity of devices, from BYOD student laptops to unmanaged lab systems, creates a fragmented digital perimeter with exploitable blind spots across every layer of the network.
Education leaders can no longer treat cybersecurity as an IT add-on. It’s a core operational priority. This directory dives into field-tested cybersecurity tools for academic environments, the top-rated vendors serving U.S. and international institutions, and how to choose the right solution depending on campus size and budget. Whether you're a district administrator or university CIO, the insights here are built to secure classrooms, protect compliance, and future-proof learning environments.
Why the Education Sector Is a Prime Cyber Target
The education sector has become one of the most heavily attacked industries, surpassing even finance in certain breach reports. Schools and universities store sensitive PII, academic records, medical information, and payroll systems, all of which command high black-market value. Yet their cybersecurity funding is disproportionately low—often less than 8% of total IT budgets, leaving wide attack surfaces open across campus systems.
Adversaries also recognize the high uptime demand of academic environments. A successful ransomware strike can halt online learning, disrupt access to LMS platforms, and jeopardize semester schedules—pressuring institutions to pay quickly. With thousands of endpoints, third-party education apps, and remote login systems, the threat landscape is uniquely complex.
K-12 vs University Threat Landscapes
K-12 districts face constant phishing attempts and credential theft via student devices and staff email. Most have limited IT oversight, rely on outdated systems, and often lack centralized identity access control. In contrast, universities operate sprawling networks across research labs, dorms, and departments. These environments often include high-performance computing clusters vulnerable to data exfiltration, nation-state attacks, or IP theft.
Universities also engage in international collaboration, expanding exposure to supply chain risks and unauthorized remote access. While both sectors are vulnerable, the nature and motivation of attacks differ—financial extortion dominates K-12, while espionage and data theft loom large for higher education.
Real Breach Examples & Vulnerabilities
In 2023, Los Angeles Unified School District experienced a massive ransomware breach, exposing data from over 500,000 students and staff. Attackers exploited unpatched VPN vulnerabilities and lateral movement through flat network architecture. Similar breaches at Lincoln College and the University of Vermont Medical Center highlighted a pattern: institutions failing to implement multi-factor authentication, real-time monitoring, and incident response plans.
Common vectors include misconfigured Google Workspace accounts, open RDP ports, and lack of user training. Education-specific EdTech platforms also suffer from default admin credentials and unsecured APIs, making them easy targets. Cybersecurity is no longer optional—it’s a survival requirement.
Must-Have Cyber Tools for Academic Institutions
The cybersecurity stack for educational institutions must address diverse user types, distributed networks, and high device turnover. A reactive or piecemeal approach leaves critical infrastructure vulnerable. Instead, schools and universities require integrated, scalable tools that defend at every layer—from device to data center.
Endpoint Security, SIEM, MFA, Backup
Endpoint Protection Platforms (EPPs) like CrowdStrike or SentinelOne are essential for device-level threat detection. These platforms provide real-time behavioral analytics, isolate infected machines, and automate remediation. For K-12 environments with unmanaged Chromebooks or tablets, lightweight agents that support remote wiping and device geofencing offer high value.
Security Information and Event Management (SIEM) tools like Splunk, LogRhythm, or Microsoft Sentinel aggregate logs from across systems. They provide centralized visibility, enabling IT teams to correlate anomalies—such as unusual login times, data spikes, or policy violations—and respond fast.
Multi-Factor Authentication (MFA) must be non-negotiable for staff and admin logins. Tools like Duo Security or Microsoft Authenticator can block over 90% of credential-based breaches. For students, adaptive MFA (triggered by geographic anomalies or suspicious behavior) offers balance between security and usability.
Automated backup and disaster recovery tools, like Veeam or Rubrik, protect against ransomware lockouts and hardware failures. These tools should support immutable backup chains and air-gapped storage to ensure full recovery even after encrypted attacks.
Identity Access & Data Loss Prevention
Identity and Access Management (IAM) systems such as Okta or JumpCloud provide fine-grained control over who can access what. Role-based access ensures that students don’t inherit staff permissions and that privileged accounts require step-up verification.
Data Loss Prevention (DLP) solutions like Symantec DLP or Microsoft Purview actively monitor outgoing communications (email, uploads, transfers) for sensitive content. They can flag or block attempts to send student records, financial info, or test materials outside authorized domains.
Cloud-focused DLP systems also integrate with Google Workspace or Microsoft 365, enabling inline content inspection, encryption enforcement, and real-time threat alerting—essential in hybrid or remote learning setups.
With these layers in place, institutions can reduce breach probability, meet compliance obligations, and maintain uninterrupted academic delivery.
| Tool Type | Recommended Solution(s) | Key Use in Education |
|---|---|---|
| Endpoint Protection | CrowdStrike, SentinelOne | Real-time malware defense, device isolation, and automated remediation for school-issued and BYOD devices |
| SIEM (Security Monitoring) | Splunk, Microsoft Sentinel | Log aggregation, anomaly detection, centralized visibility across distributed campus systems |
| Multi-Factor Authentication (MFA) | Duo Security, Microsoft Authenticator | Credential protection for admin and faculty portals, conditional access for students |
| Backup & Disaster Recovery | Veeam, Rubrik | Immutable backups, ransomware rollback, and rapid data restoration for critical systems |
| Identity & Access Management (IAM) | Okta, JumpCloud | Role-based access control, password policies, and account lifecycle management |
| Cloud-Native Data Loss Prevention (DLP) | Microsoft Purview, Symantec DLP | Monitors outbound communication for sensitive data leaks on Google Workspace and Microsoft 365 |
| Content Filtering & CIPA Compliance | Lightspeed Systems, Smoothwall | Web filtering, keyword monitoring, and CIPA-ready classroom management tools |
Directory: Top Cybersecurity Providers for Schools
Educational institutions require vendors that specialize in both security and academic infrastructure—solutions that integrate with student information systems, learning management platforms, and compliance frameworks. Below is a curated directory of leading cybersecurity providers for the education sector, divided by category and geography, offering tools for all institutional sizes.
| Provider | Category | Region | Key Strengths for Education |
|---|---|---|---|
| CrowdStrike | Endpoint Protection | U.S. | Lightweight agents, real-time device control, threat intel |
| Splunk | SIEM (Security Monitoring) | U.S. | Log aggregation, academic IT integrations, anomaly detection |
| Okta | Identity & Access Management | U.S. | SSO, role-based access, secure hybrid learning support |
| Veeam | Backup & Recovery | U.S. | Immutable backup, ransomware recovery, cloud failover |
| Lightspeed Systems | Web Filtering & CIPA Compliance | U.S. | Student content filtering, LMS integration, CIPA-ready |
| Gaggle | Student Threat Detection | U.S. | AI-based safety risk monitoring in student digital behavior |
| ManagedMethods | K-12 Security Suite | U.S. | Google/M365 DLP, FERPA reports, district-level threat dashboards |
| Fortinet | Unified Threat Management | Global | Firewalls, AV, web filtering in one; used by top universities |
| Symantec DLP | Cloud-Native DLP | Global | Cross-platform data protection, real-time cloud inspection |
| Palo Alto Networks | Network Security | Global | High-throughput firewalls, lab-grade role-based access control |
| Netskope | CASB & Compliance Visibility | Global | SaaS usage enforcement, cloud security posture monitoring |
| IBM Security | Managed Security Services | Global | Full-scale MSSP with education-specific policies and SOCs |
| Smoothwall | Web Filtering & Student Safety | U.K. | Live keyword alerts, self-harm prevention, digital wellbeing tools |
Choosing the Right Solution Based on Budget & Size
Cybersecurity solutions must match the operational scale and funding reality of each institution. A 3-school district and a 30,000-student university have fundamentally different needs—yet both face targeted attacks. Budget, deployment speed, user training, and licensing flexibility are critical factors that determine whether a solution sticks or stalls.
Small Districts vs Large Campuses
Small K-12 districts often work with tight IT budgets and part-time staff, making plug-and-play, cloud-managed solutions ideal. These districts benefit from bundled platforms offering endpoint protection, content filtering, and email security—like Lightspeed Systems or ManagedMethods—with minimal configuration overhead. Their tools must be compliance-ready out of the box (e.g., CIPA, FERPA) and come with responsive vendor support.
Large universities, on the other hand, manage heterogeneous environments: student dorms, research centers, medical schools, and international collaboration hubs. These require modular and scalable security architectures. Institutions in this bracket often deploy SIEMs like Splunk, custom IAM with tools like Okta, and MSSPs such as IBM Security to support 24/7 monitoring and advanced response orchestration.
Deployment Considerations & Licensing
Most K–12 institutions prefer cloud-first solutions with rapid deployment (under 30 days), role-based dashboards, and per-student or per-device licensing. This allows cost control and phased rollout across schools. Vendors like Gaggle and Veeam offer predictable pricing and tools that scale with enrollment growth or hybrid learning pivots.
Universities typically require multi-tenant environments and granular policy enforcement across departments. Licensing for these environments often includes enterprise site-wide contracts or consumption-based pricing models, depending on research data usage and compliance exposure. Flexible API access and federated identity integrations are key, particularly when syncing with LDAP, Azure AD, or Eduroam systems.
A misfit between budget and architecture stalls adoption. Choosing right means aligning security maturity, funding cycles, and campus infrastructure realities.
Compliance Standards in EdTech Security
Academic institutions must meet a complex matrix of federal, state, and internal data protection regulations. Non-compliance not only risks funding loss—it can also trigger lawsuits, FERPA complaints, and permanent reputational damage. As cyberattacks rise, regulatory scrutiny of EdTech platforms and district-level IT practices is intensifying.
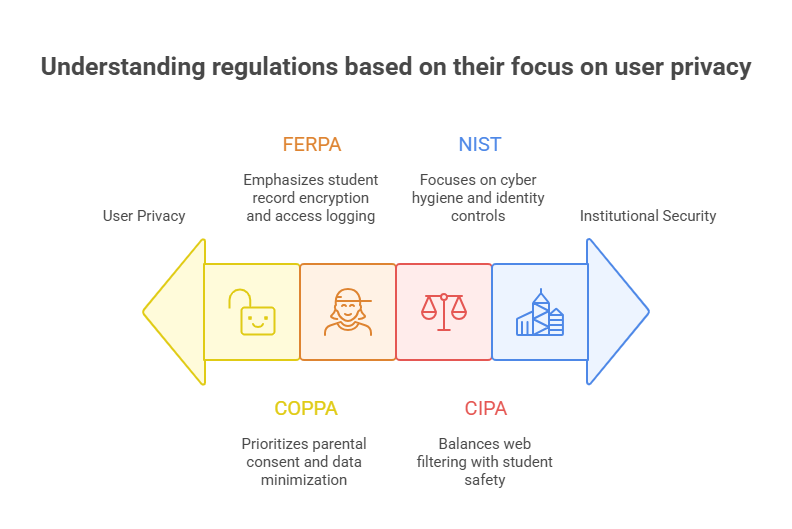
FERPA, COPPA, CIPA, NIST
FERPA (Family Educational Rights and Privacy Act) mandates strict control over student education records. Institutions must implement access logs, encryption, and role-based access control to prevent unauthorized data exposure. Many districts fail audits due to poorly managed Google Workspace or shared drives.
COPPA (Children’s Online Privacy Protection Act) applies to platforms used by children under 13. EdTech vendors must have explicit parental consent mechanisms, limit tracking cookies, and restrict third-party data sharing. Districts are liable if they deploy non-compliant tools—even if vendors are at fault.
CIPA (Children’s Internet Protection Act) is essential for any K–12 school receiving E-Rate discounts. Institutions must deploy content filters, monitor online behavior, and educate users about digital safety. Tools like Lightspeed Systems and Smoothwall are built to meet CIPA out-of-the-box.
NIST (National Institute of Standards and Technology) frameworks, especially NIST 800-53 and CSF, offer baseline controls for cyber hygiene, incident response, and identity management. While not mandatory, they are widely adopted by universities seeking grant funding or research accreditation.
Meeting these standards requires more than paperwork—they demand architectural alignment, technical enforcement, and routine audits. Even a single exposed Google Doc with student names can trigger a FERPA violation.
Internal Policy Audits & Readiness
Schools and universities should conduct annual security readiness audits to align with FERPA, CIPA, and state-specific mandates. This includes reviewing:
Administrative access logs
Third-party EdTech data-sharing policies
MFA enforcement status
Disaster recovery drill outcomes
Patch management cadence
Institutions should also maintain an up-to-date data protection impact assessment (DPIA) and a pre-approved vendor list. Many breaches occur because of shadow IT—tools teachers use without district vetting. Continuous policy review helps eliminate these blind spots.
Build Cybersecurity Leadership with the ACSMC Certification
The most critical vulnerability in education isn't software—it's the skills gap among leadership and IT decision-makers. Most school systems and universities lack internal cybersecurity expertise at the strategic level, making them reliant on vendors or exposed to misconfigured tools. To lead confidently, education leaders need formal cybersecurity training grounded in real-world applications.
The Advanced Cybersecurity & Management Certification (ACSMC) by ACSMI equips IT directors, school administrators, and digital safety officers with the expertise to evaluate threats, vet vendors, and implement NIST-aligned controls. With 379 lessons, CPD accreditation, and modules covering EdTech-specific risk management, it’s designed for security oversight roles in education.
Whether managing incident response, navigating compliance (FERPA, CIPA, COPPA), or guiding institutional policy, the ACSMC program builds institutional resilience from the top down. For schools looking to build sustainable, in-house cyber capacity, this certification offers a strategic edge.
Frequently Asked Questions
-
The education sector has become a preferred target due to its underfunded cybersecurity infrastructure, large attack surface, and valuable data—ranging from student PII to proprietary research. Most institutions operate on legacy systems with limited endpoint protection and open access networks, making them vulnerable to ransomware, phishing, and insider threats. Additionally, schools rely on third-party EdTech platforms that often lack robust security controls. Cybercriminals also know that downtime can force fast ransom payments, especially during peak academic periods. This unique mix of high-value data and low security maturity puts educational institutions at greater risk than many private enterprises.
-
K–12 schools need a layered security stack that’s affordable, scalable, and easy to manage with limited IT staff. Core tools include:
Endpoint Protection Platforms (EPPs) for real-time malware and ransomware defense
Content filtering and monitoring solutions that meet CIPA standards
Email security and phishing prevention tools
Cloud-native DLP for Google Workspace or Microsoft 365
MFA and role-based access controls for admin accounts
Solutions from vendors like Lightspeed Systems, ManagedMethods, and Gaggle provide built-in compliance support and minimal configuration, making them ideal for districts without a dedicated security team.
-
Universities must manage complex, decentralized networks, high research data sensitivity, and international collaboration risks. Unlike K–12 schools, universities typically operate open networks to support academic freedom, which introduces unique vulnerabilities. These institutions benefit from modular security frameworks—including SIEM platforms like Splunk, enterprise IAM tools like Okta, and MSSPs (Managed Security Service Providers) such as IBM Security for 24/7 monitoring. Universities should also implement federated identity systems, encrypt research data at rest and in transit, and enforce policy segmentation across departments. Their security posture must reflect compliance needs for grants, partnerships, and cross-border data protection laws.
-
Vendors with pre-configured compliance frameworks are essential for educational institutions.
Lightspeed Systems and Smoothwall are top choices for CIPA compliance, offering real-time web filtering, content monitoring, and student safety alerts.
Gaggle provides AI-powered communication monitoring to help meet FERPA obligations by detecting threats involving student records.
For COPPA, tools like ManagedMethods and Symantec DLP help monitor and restrict third-party data flows, enforcing parental consent mechanisms.
These vendors not only address the regulatory needs technically, but also offer audit trails, incident logs, and pre-built reporting templates to meet documentation standards.
-
Schools with tight budgets should prioritize security solutions that offer bundled features, compliance readiness, and cloud-managed dashboards. Many vendors offer per-student or per-device pricing models, making cost predictable. Opting for platforms like Veeam for backup, Okta for simplified IAM, and Lightspeed for CIPA filtering gives institutions a strong foundation. Grants such as the E-Rate program can subsidize CIPA-compliant filtering tools. Moreover, adopting NIST cybersecurity framework tiers helps schools scale their defenses over time. The key is to invest in tools that cover multiple risk areas at once and require minimal local infrastructure.
-
DLP (Data Loss Prevention) focuses on monitoring and controlling the flow of sensitive information, such as student records, test results, or HR data. It prevents unauthorized access, sharing, or exfiltration of sensitive content—especially important in cloud platforms like Google Workspace or Microsoft 365.
SIEM (Security Information and Event Management), on the other hand, is about centralized threat detection. It collects logs and event data from across systems, analyzes patterns, and alerts on anomalies.
In short, DLP prevents data from leaving, while SIEM detects malicious behavior across the environment. Institutions benefit from using both. -
Institutions should perform a comprehensive cybersecurity audit at least once per year, but more frequent quarterly reviews or policy spot-checks are recommended—especially after EdTech expansions or remote learning shifts. Audits should include:
Access and identity policy reviews
Vulnerability scans and patch update checks
Incident response drill simulations
Compliance checklists for FERPA, CIPA, and COPPA
Vendor risk assessments
An audit is not just technical—it should include interviews with staff, checks for shadow IT, and evaluations of student safety monitoring. Documentation should feed directly into board or superintendent-level reports.
-
The Advanced Cybersecurity & Management Certification (ACSMC) by ACSMI trains professionals in:
NIST-aligned risk management for school environments
Threat detection and incident response playbooks tailored to education
Data governance and compliance strategy across FERPA, CIPA, COPPA
Vendor evaluation frameworks and EdTech due diligence
Secure network architecture for hybrid learning and BYOD scenarios
The program is ideal for IT leads, EdTech directors, and administrators seeking to build in-house cybersecurity leadership. It bridges the gap between technical controls and strategic decision-making, preparing teams to navigate the real-world risks faced by modern academic institutions.
Final Thoughts
Cybersecurity in education is no longer an IT expense—it’s a mission-critical investment. From K–12 districts to research universities, every institution is now a digital campus, and every digital campus is a target. The stakes are high: student privacy, academic integrity, federal funding, and even physical safety depend on secure digital environments.
This directory provides a vetted blueprint for choosing cybersecurity vendors, deploying must-have tools, and aligning with compliance frameworks like FERPA, CIPA, and COPPA. But tools alone aren’t enough. Building lasting resilience requires internal capacity and leadership fluency, which is why programs like the Advanced Cybersecurity & Management Certification (ACSMC) from ACSMI are vital for long-term protection.
As cyber threats evolve, your response must scale accordingly—not just reactively, but proactively. Invest in security literacy. Vet your vendors rigorously. Audit your systems regularly. Most importantly, treat cybersecurity as a core pillar of educational excellence, not a background function.
📊 Quick Poll
What is your institution’s top cybersecurity priority for 2025?