Cybersecurity Solutions Directory for Small Businesses
Small businesses don’t get breached because they “didn’t care.” They get breached because they’re forced to run enterprise-level risk on a lean budget: shared inboxes, weak identity controls, unmanaged devices, outsourced IT with blurry accountability, and zero time to tune alerts. Attackers love that combination—fast compromise, low friction, high payoff. This directory is built to solve that reality: what to buy, why it matters, what to configure, and how to prove it works—so your security stack becomes a business advantage, not a constant anxiety loop.
1) The Small Business Cybersecurity Reality: Where Attacks Actually Land
If you’re a small business, the threat model isn’t “nation-state sophistication” as your daily baseline—it’s repeatable compromise patterns that scale cheaply for criminals: credential theft, email compromise, ransomware/extortion, vulnerable internet-facing services, and exposed data flows. The most painful part isn’t the breach itself; it’s the secondary damage—downtime, legal exposure, lost customer trust, and the chaos of not knowing what’s true.
Most small businesses fail in the same five places:
Identity is soft (no MFA enforcement, shared logins, weak admin hygiene). Your access decisions need to be designed, not improvised—ground your thinking with access control models like DAC, MAC, and RBAC.
Email is under-defended (phishing, spoofing, malicious attachments, account takeovers).
Endpoints are unmanaged (patching gaps, local admin sprawl, weak ransomware controls). Strengthen your selection criteria by understanding modern endpoint defense patterns via the EDR tools guide.
Visibility is missing (you don’t know what happened fast enough). Build the minimum viable monitoring mindset using SIEM fundamentals so “alerts” become actionable signals.
Recovery isn’t real (backups exist, but restores aren’t tested; ransomware response is undefined). If ransomware is in your threat model, treat response and recovery as a discipline using ransomware detection, response, and recovery and lock the process in a real playbook with incident response plan development and execution.
A small business stack shouldn’t chase perfection. It should remove entire breach classes (identity hardening), reduce blast radius (least privilege + segmentation), detect fast enough to contain, and recover without negotiation. When you build your stack with that intent, you also become more audit-ready—because you can explain what you did, why you did it, and how you know it’s working, using audit logic from security audits and best practices.
2) What to Buy First: A Small Business Priority Order That Actually Reduces Risk
Buying security out of order is how small businesses overspend and still get hit. The correct order is not “tools first.” It’s identity first, then email and endpoints, then visibility, then recovery, then hardening depth.
Tier 1 (Non-negotiable foundation)
Identity controls: enforce MFA, eliminate shared accounts, and apply least privilege. Use access design principles from DAC/MAC/RBAC explained to stop building your business on “everyone is basically admin.”
Email security + domain protections: reduce phishing success and spoofing. Keep a realistic view of attacker evolution (especially AI-assisted lures) using AI-powered cyberattacks predictions so you don’t treat yesterday’s phishing as your baseline.
Endpoint baseline: MDM/UEM, patching, and EDR (or a managed EDR). If you’re comparing endpoint tools, ground your feature checklist using EDR tools guidance and cross-check vendor claims with endpoint security providers comparisons.
Tier 2 (Containment + evidence)
Logging and alerting: you don’t need a massive SOC; you need enough visibility to answer: “Who logged in?”, “From where?”, “What changed?”, “What got accessed?” Build the monitoring mindset with SIEM fundamentals and define what you must detect with cyber threat intelligence collection basics.
Incident response plan: the plan is how you convert panic into steps. Don’t “write a PDF”; operationalize through IRP development and execution so your team can contain, preserve evidence, and communicate clearly.
Tier 3 (Resilience and future-proofing)
Immutable backups + restore drills: ransomware readiness is mostly recovery readiness. Pair your backup strategy with ransomware detection/response/recovery and track how extortion keeps changing using ransomware evolution forecasts.
DLP and SaaS controls: when your business runs on SaaS, data leaks become your most expensive “quiet incident.” Build your understanding of protections with data loss prevention strategies and keep your compliance posture from drifting with future cybersecurity compliance trends.
The goal is a stack that’s defensible in two directions: defensible against attackers and defensible in reviews/audits. That second part is where small businesses get burned—because they rely on “our IT guy said so” instead of evidence. Fix that using the mentality in security audits and best practices and the structure of NIST/ISO/COBIT frameworks.
3) How to Evaluate Cybersecurity Solutions Like a Pro (Even With a Small Business Budget)
Small businesses get trapped in two dangerous vendor games:
The “checkbox demo”: a beautiful UI that can’t prove outcomes.
The “fear pitch”: you buy fast, configure later, and never get measurable security.
A professional evaluation is simple: capability → implementation → evidence. You’re not buying features; you’re buying reduced probability of a class of incident.
1) Demand evidence-friendly answers (not marketing)
Ask vendors questions that force operational detail:
“Show me the policy controls that enforce MFA and block risky authentication paths.”
“Show me the audit trail for admin actions and configuration changes.”
“Show me how I isolate an endpoint and collect evidence in under 2 minutes.”
“Show me what logs you generate, and how I export them for investigations.”
If a vendor can’t answer cleanly, you’re buying confusion.
When you build this habit, you naturally align with audit-grade thinking from security audits best practices and technical validation discipline from vulnerability assessment techniques and tools.
2) Evaluate integrations like they’re security controls
A “great tool” that doesn’t integrate becomes shelfware. For small businesses, integration targets are predictable:
Identity provider / SSO
Endpoint management
Email platform
Backup platform
A central place for logs and alerts
If you want your central nervous system to exist, you’ll lean on monitoring patterns described in SIEM overview and basic perimeter/segmentation controls from firewall technologies.
3) Measure outcomes with 5 concrete metrics
Pick metrics that reflect reality, not vanity:
MFA coverage: % of accounts enforced, especially admins
Patch SLA: time to patch critical issues on all devices
Phishing resilience: report rate vs click rate trend
Detection speed: time from alert to human acknowledgment
Restore success: successful restore tests per month
These metrics give you a program you can explain, improve, and defend—especially when your monitoring and testing approach is grounded in IDS deployment concepts and incident response execution.
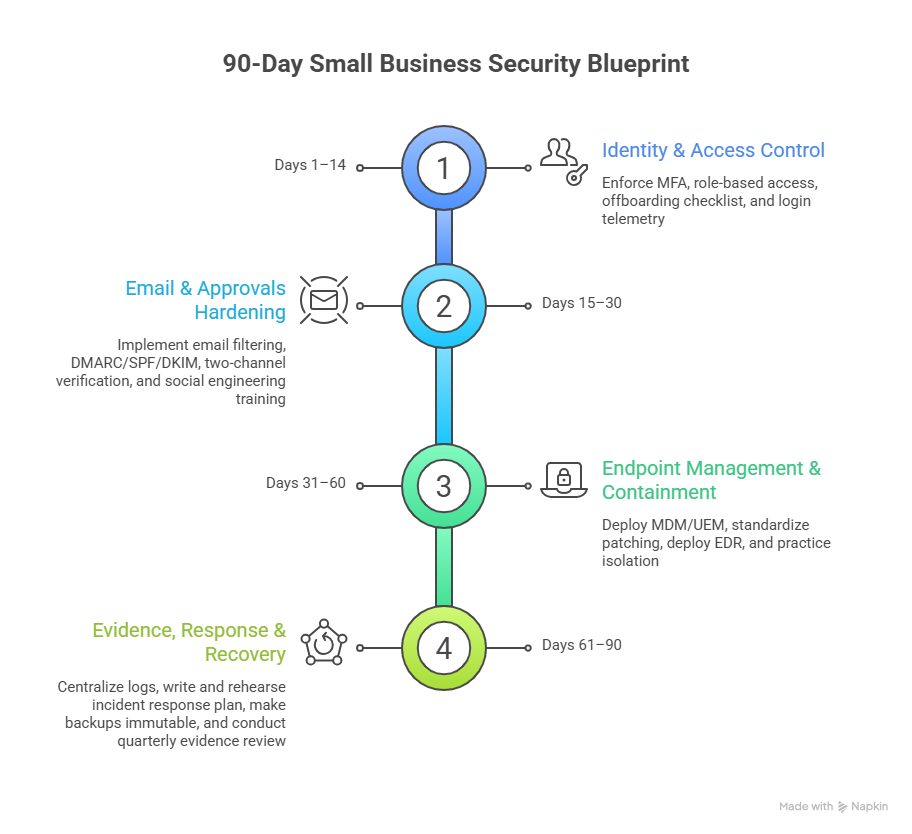
4) 90-Day Blueprint: Build a Small Business Stack That Actually Holds Under Attack
Most small businesses do security in bursts—after a scare, after an incident, after a renewal. A 90-day blueprint forces sequence, ownership, and proof.
Days 1–14: Lock identity and stop easy takeover
Enforce MFA everywhere (admins first).
Kill shared accounts; create role-based access. If role design is fuzzy, use DAC/MAC/RBAC clarity to formalize who can do what, and why.
Establish an offboarding checklist (disable access, revoke shares, rotate secrets).
Confirm login telemetry is visible—your “who logged in?” answer should come from logs, not feelings. Build the mental model with SIEM overview.
Days 15–30: Harden email and approvals (where fraud lives)
Implement email filtering + sandboxing.
Enforce DMARC/SPF/DKIM (or at minimum, move toward enforcement).
Add a “two-channel verification” rule for money movement and vendor changes.
Train staff on modern social engineering, including AI-assisted lures—your awareness baseline should reflect where attacker scale is going, informed by AI-driven cyber threat predictions and manipulation risk like deepfake threat preparation.
Days 31–60: Make endpoints controllable and containable
Deploy MDM/UEM for encryption, compliance, and remote wipe.
Standardize patching with reporting and SLAs.
Deploy EDR (or managed EDR) and practice isolation.
Choose endpoint tooling with realism: what matters is telemetry + response actions, not dashboards. If you’re unsure what “good” looks like, anchor your evaluation using EDR tools guidance and compare vendor approaches via endpoint security providers directory.
Days 61–90: Build evidence, response, and recovery that survive stress
Centralize key logs (identity, email, endpoints, firewall) to reduce blind time. Use SIEM basics and reinforce monitoring design with IDS deployment guidance.
Write and rehearse an incident response plan that people can execute at 2 a.m. Build it properly with IRP development and execution.
Make backups immutable and prove restore success monthly. Treat ransomware readiness as operational maturity using ransomware response and recovery, and pressure-test assumptions against how extortion keeps evolving in ransomware evolution by 2027.
Create a quarterly evidence review so you can prove controls work—borrow the structure from security audits best practices and map your controls to NIST/ISO/COBIT frameworks.
This blueprint doesn’t require enterprise headcount. It requires sequence, ownership, and proof.
5) Practical Stack Examples (Lean, Balanced, and “We Need Help” Managed)
Small businesses often choose between “do it ourselves” and “fully managed.” The smarter approach is hybrid: keep control of identity and backups (because they’re business survival), and selectively outsource monitoring/response if you can’t staff it.
Stack A: Lean DIY (security owner is also doing other jobs)
Identity + MFA enforcement + SSO
Email security + DMARC hygiene
MDM + patching baseline
Lightweight EDR
Immutable backups + restore drills
Minimal logging with defined alert routing
This stack works if you keep it disciplined and build a simple verification routine using vulnerability assessment techniques and a basic monitoring mindset from SIEM overview.
Stack B: Balanced (small IT team, needs visibility)
Everything in Stack A
Central log visibility with identity/email/endpoint correlation
DLP for the highest-risk data flows
Vulnerability scanning + quarterly remediation evidence
If you’re building this, your biggest risk is tool sprawl without outcomes. Keep governance clear using security audits best practices and control mapping from NIST/ISO/COBIT frameworks.
Stack C: Managed Security (you need response speed, not more dashboards)
Identity + MFA + offboarding discipline owned internally
Managed EDR + MDR/MSSP monitoring
Backup strategy owned internally + restore tests documented
IR retainer for major incidents, aligned to IRP execution
This stack works when SLAs are real and you test them. If you’re exploring managed providers, benchmark what “good service” looks like using the MSSP guide and keep a vendor short-list grounded with top cybersecurity companies directory.
6) FAQs: Cybersecurity Solutions for Small Businesses
-
Start with identity protection, email defense, and endpoint control. Identity hardening (MFA + least privilege) blocks the fastest compromise paths—use DAC/MAC/RBAC guidance to structure access. Then secure email to reduce phishing success, and deploy endpoint controls with an EDR mindset informed by EDR tools guidance.
-
Not always a traditional SIEM, but you do need central visibility for identity, email, and endpoints so you can answer core incident questions fast. Build the right expectations with SIEM overview, then start small: log what matters, route alerts to humans, and verify completeness.
-
Ransomware readiness is mostly recovery readiness + containment: immutable backups, restore tests, endpoint isolation capability, and an incident response plan you can execute. Build your foundation with ransomware detection/response/recovery and formalize response steps using IRP development and execution.
-
If you can’t guarantee monitoring follow-through and response speed, a managed provider can reduce risk—if SLAs and escalation are real. Use the MSSP ultimate guide to benchmark providers, and keep identity and backups internally owned because they’re business survival systems.
-
Create a simple evidence routine: MFA coverage reports, patch compliance, phishing metrics, EDR isolation drills, and restore test logs. Structure your proof around security audits best practices and map controls to a framework using NIST/ISO/COBIT guidance.
-
Expect faster, more scalable social engineering and more targeted identity abuse. Build defenses around identity, verification workflows, and detection speed. Keep your threat radar aligned with AI-powered cyberattack predictions and manipulation risk such as deepfake threat preparation.