Best Cybersecurity Solutions for Manufacturing & Industrial Firms
Manufacturing companies do not lose money from cyber incidents the same way office-based businesses do. They lose production hours, quality control visibility, supplier coordination, machine availability, maintenance timing, operator trust, and in some cases physical safety. That is why industrial security buying decisions cannot be reduced to “what endpoint tool is most popular” or “which firewall has the best dashboard.” A factory needs layered protection built for uptime, segmented operations, vendor access control, ransomware resilience, and audit-ready response.
The strongest manufacturing security strategy usually combines proven controls from cybersecurity frameworks, disciplined security audits, continuous vulnerability assessment techniques, resilient firewall technologies, and practical incident response planning. This guide breaks down the best cybersecurity solutions for manufacturing and industrial firms by actual operational need, not by hype.
1. Why Manufacturing Needs a Different Cybersecurity Stack Than Traditional IT
Manufacturing environments run on a fragile balance: production continuity, plant-floor visibility, safety logic, remote vendor access, and aging assets that were never designed for hostile networks. A law firm can survive temporary email disruption. A factory facing compromised programmable systems, unavailable HMIs, or frozen ERP-to-warehouse integration can bleed cash every hour. That is why a manufacturing leader should not shop for tools in the same way a generic enterprise IT team would.
The first difference is attack impact. When cyber risk hits industry, the blast radius often reaches scheduling, maintenance, supply chain timing, product quality, and compliance evidence all at once. This is why firms should evaluate solutions through the lens of manufacturing sector cybersecurity trends, not just general enterprise risk. Many plants also need controls influenced by lessons from cybersecurity in energy and utilities, government and public sector security, and healthcare cybersecurity predictions, because all three sectors wrestle with high-consequence operations, legacy infrastructure, and uptime sensitivity.
The second difference is that manufacturing risk is often hidden in connection points. Plants may secure laptops but ignore engineering workstations, third-party maintenance tunnels, shared admin accounts, flat VLANs, weak VPN hygiene, and over-trusted machine-to-server communication. A strong defense starts with access control models, reinforced by virtual private networks, hardened public key infrastructure, and visibility from intrusion detection systems. If these foundations are weak, the fanciest platform in the world will only help you watch your breach in high definition.
The third difference is speed of containment. Manufacturing firms need solutions that do not just alert, but support isolation, failover thinking, evidence capture, and recovery sequencing. That is why decision-makers should pair security information and event management with cyber threat intelligence, plan explicitly for ransomware detection and recovery, and invest in data loss prevention strategies before sensitive design data, formulas, production specs, or supplier documents walk out the door.
2. The Best Cybersecurity Solution Categories for Manufacturing Firms
The best solution for a manufacturer is rarely a single product. It is a coordinated stack chosen by operational pain point. For example, if your real risk is uncontrolled vendor access, then buying another dashboard-heavy analytics platform will not save you. You need identity discipline, time-bound sessions, approval workflows, and privileged session recording. That means focusing on controls aligned with zero trust security innovations, stronger VPN security limitations and benefits, better PKI components and applications, and smarter access control models.
If ransomware is your top board-level fear, start with resilience rather than theater. Mature plants build layers around ransomware response and recovery, integrate detection with SIEM workflows, enrich with threat intelligence collection and analysis, and validate controls through recurring security audits and best practices. The key question is not “can we detect ransomware?” but “can we detect privilege abuse, abnormal encryption activity, backup targeting, and remote access misuse early enough to keep a single workstation infection from becoming a plant-wide shutdown?”
If your environment is highly connected, cloud-enabled, or IoT-heavy, you need solutions that account for manufacturing’s expanding digital surface. Industrial organizations increasingly blend plant telemetry, SaaS operations, cloud analytics, and smart device management. That means your buying criteria should reflect lessons from the future of cloud security, the roadmap to IoT security specialist careers, AI-powered cyberattacks and defenses, and the top 10 cybersecurity threats predicted to dominate by 2030. In practice, that means prioritizing visibility into unmanaged assets, insecure protocols, shadow integrations, and identity-based abuse.
Manufacturers also need to evaluate outside support intelligently. A mid-market firm with limited internal analysts may be better served by strong managed monitoring than by a premium platform nobody has time to tune. Reviewing the best managed security service providers, the top 50 cybersecurity companies worldwide, leading endpoint security providers, and the complete directory of SIEM solutions can help buyers compare operating models, not just feature lists. The right choice is the one your team can actually deploy, govern, monitor, and recover with under pressure.
3. How to Choose the Right Stack Based on Real Industrial Risk
A manufacturer should choose cybersecurity solutions by mapping them to failure scenarios that hurt the business most. Start by asking what would actually stop shipments, degrade quality, freeze maintenance visibility, or trigger regulatory panic. That is a far better buying framework than letting vendors drive the conversation toward whatever product category they sell. If your biggest concern is production downtime, then network segmentation, endpoint isolation, fast-response logging, and backup integrity should sit above cosmetic tooling. If the pain point is supplier-driven exposure, then third-party access governance and credential control become the priority.
For network defense, plants need more than perimeter thinking. Firewall technologies and configurations matter, but internal separation matters just as much. Once attackers breach one foothold through phishing, credential abuse, exposed VPN, or remote maintenance software, the question becomes whether they can move sideways into engineering stations, file shares, historian servers, or line-control support systems. This is why manufacturers should pair network controls with IDS deployment strategies, DoS mitigation planning, and where relevant, botnet disruption awareness. Industrial downtime is expensive enough without discovering too late that “flat network convenience” was actually attacker convenience.
For data protection, think beyond customer records. Manufacturers hold sensitive CAD files, formulas, production tolerances, supplier contracts, firmware, product test results, and internal process know-how. These assets require data loss prevention strategies, encryption standards, and in some cases stronger privacy and regulatory alignment. If a competitor or extortion group steals process documentation, the damage may continue long after systems are restored. That is why “we have backups” is not a full strategy. Recovery without confidentiality protection still leaves a company exposed.
For operational maturity, solution choice must match internal capability. A stretched team should not buy ten loosely integrated tools and hope dashboards will compensate for scarce analysts. A better path may be guided skill development through future skills for cybersecurity professionals, supported by top cybersecurity certifications, selective partner help from training providers, and practical tooling aligned with job market demand for specialized roles. Good security architecture fails all the time because organizations buy sophistication they cannot operate.
Quick Poll: Which Manufacturing Cyber Risk Would Hurt You Fastest?
Pick the exposure that would create the most financial pain, operational disruption, or leadership panic in your environment.
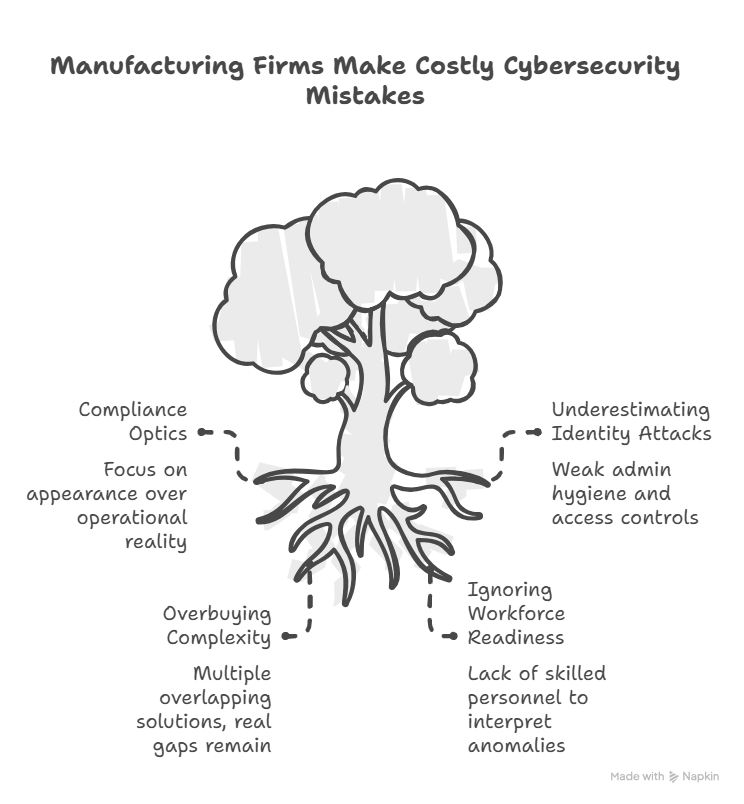
4. The Most Costly Buying Mistakes Manufacturing Firms Keep Making
One of the most common mistakes is buying for compliance optics instead of operational reality. A plant may pass a review, produce neat control documentation, and still be dangerously exposed because its vendor access paths are sloppy, logs are untriaged, backup recovery is untested, or segmentation is incomplete. That is why firms should study the direction of future cybersecurity compliance, the next generation of cybersecurity standards, and evolving cybersecurity audit practices without confusing evidence collection with actual resilience.
Another major mistake is underestimating identity-based attacks. Plants still spend heavily on infrastructure controls while tolerating weak admin hygiene, stale accounts, broad remote trust, and poor approval chains for access. That gap becomes disastrous as adversaries lean into deepfake cybersecurity threats, AI-driven cyberattacks, and stealthier credential abuse highlighted in the future threat landscape. In manufacturing, one compromised privileged identity can punch far above its apparent scope because access often spans systems, vendors, and production support workflows.
A third mistake is overbuying complexity. Some industrial firms install multiple overlapping solutions—an EDR no one tunes, a SIEM that drowns analysts in noise, a vulnerability platform that generates endless findings without plant-aware prioritization, and a compliance system with no accountable owners. Meanwhile the real gaps remain: no line-by-line segmentation roadmap, weak phishing resistance, incomplete asset inventory, and no tested recovery sequence. Buyers should compare tools against practical references like the best EDR tools guide, top vulnerability scanners, top penetration testing tools, and top penetration testing companies to identify what will truly close risk rather than just decorate the stack.
The last big mistake is ignoring workforce readiness. Security tools do not replace judgment under pressure. Teams need analysts who can interpret network anomalies, engineers who understand secure change windows, leaders who can make shutdown decisions under uncertainty, and responders who know how to preserve evidence while protecting operations. That is why staffing and upskilling matter alongside product selection, whether through cybersecurity certifications of the future, remote cybersecurity career trends, automation and the future workforce, or even specialized career paths like cybersecurity auditor, cloud security engineer, and cyber threat intelligence analysis.
5. A Practical 90-Day Roadmap for Implementing the Right Solutions
In the first 30 days, focus on clarity. Build or validate your asset inventory, identify critical production dependencies, map all remote access paths, and rank systems by operational consequence. During this phase, run targeted reviews using vulnerability assessment techniques, compare current logging against SIEM best practices, validate incident response execution, and assess whether existing firewall configurations truly separate risk. The goal is not to generate a huge remediation spreadsheet. The goal is to expose the few weaknesses most likely to cause real plant disruption.
In days 31 through 60, move into control tightening. Prioritize identity hardening, remote access cleanup, segmentation enforcement, email defense, backup validation, and high-value alerting. This is also the time to review whether current controls align with the future of endpoint security, next-gen SIEM directions, email security solution directories, and AI-driven cybersecurity tools. If vendor support is part of your strategy, this is where you evaluate service providers with eyes wide open: coverage windows, escalation speed, OT familiarity, false-positive discipline, and recovery support matter more than sales decks.
In days 61 through 90, stress-test the program. Run tabletop exercises around ransomware, stolen admin credentials, vendor compromise, and plant-floor lateral movement. Validate evidence collection, escalation thresholds, business decision rights, and communication chains. Mature firms reinforce this phase with security audit process reviews, threat-informed exercises using CTI collection and analysis, and scenario planning inspired by predicting the next big ransomware evolution and future legislative impact on SMBs. What you want by day 90 is not perfection. You want sharper visibility, tighter access, cleaner escalation, and fewer single points of failure.
The strongest manufacturing programs continue improving after the roadmap. They benchmark suppliers, tune detections against real operations, measure recovery speed honestly, and revisit architecture as plants digitize further. As lines become more connected and attacker tradecraft becomes more adaptive, firms should keep learning from blockchain innovations in cybersecurity, future compliance trends, privacy regulation evolution including GDPR 2.0 discussions, and strategic outlook pieces on job market trends that will shape security teams by 2030. The stack that works today will need governance and refinement tomorrow.
6. FAQs About Cybersecurity Solutions for Manufacturing & Industrial Firms
-
There usually is not one universal “single best” investment, but identity control and network segmentation are the two areas that most consistently reduce catastrophic risk. If attackers can move laterally with privileged access across loosely separated environments, many other tools become reactive rather than preventive. Manufacturers should combine privileged access controls, MFA, remote session governance, and internal segmentation before chasing flashy analytics.
-
Not always. Many enterprise tools can play an important role, especially for email security, endpoint visibility, identity control, and cloud posture management. But industrial environments often require passive asset discovery, OT-aware monitoring, tolerance for legacy systems, and response workflows that account for uptime and safety constraints. Tool fit matters more than product popularity.
-
The deciding factor is not company pride; it is operating capacity. If your team cannot monitor high-value alerts continuously, tune detections, investigate suspicious behavior, and support recovery under pressure, a capable provider may be the better path. However, the provider must understand industrial operations, change control, downtime sensitivity, and escalation discipline. Outsourcing without operational alignment simply hides the problem.
-
The most effective combination includes EDR, high-value SIEM use cases, strong identity controls, secure remote access, segmentation, immutable backups, phishing-resistant email security, and a tested incident response plan. Ransomware defense is never just one product. It is a chain of prevention, detection, containment, and recovery decisions.
-
At minimum, reassess after major architecture changes, plant expansions, significant cloud adoption, new vendor integrations, or material threat changes. In practice, a structured quarterly review and a deeper annual assessment work well. Security drift happens quietly in manufacturing through exceptions, temporary access, rushed integrations, and inherited legacy dependencies.
-
Uncontrolled trust. That includes old vendor accounts, shared admin credentials, permissive VPN access, undocumented assets, flat networks, and poor visibility into who touched what and when. Many firms think they have a tooling problem when they actually have a trust-governance problem. Solving that often produces bigger risk reduction than buying another dashboard.
-
Yes, but only if the rollout is sequenced around operational reality. Passive discovery, access reviews, log consolidation, email hardening, backup validation, and remote access cleanup can often begin with minimal disruption. More sensitive efforts like segmentation or aggressive endpoint controls need staged testing, maintenance-window planning, and cross-functional involvement from operations, engineering, and IT.
-
Measure business-relevant outcomes, not vendor metrics alone. Look at mean time to detect meaningful incidents, time to isolate compromised systems, number of unmanaged assets discovered, reduction in privileged sprawl, success rate of backup recovery tests, closure rate on high-risk exposures, and leadership confidence during exercises. Real value shows up in resilience, not prettier dashboards.