Cybersecurity Workforce Demographics: Diversity & Inclusion Original Report (2026-2027)
Cybersecurity hiring teams keep saying they want more talent, but the harder truth is that many still draw from the same networks, screen for the same backgrounds, and promote through the same narrow patterns. That is exactly why workforce demographics matter. In this original 2026–2027 report, I am not treating diversity and inclusion as branding language. I am treating it as a pipeline, retention, promotion, leadership, and capability problem that directly affects cyber resilience, hiring velocity, burnout, and long-term team performance.
For ACSMI readers planning their next move, this is not a soft topic. It is a career strategy topic. Whether you want to move from a SOC analyst role into leadership, pivot toward cybersecurity compliance, grow into cybersecurity auditing, or build a future in cloud security engineering, understanding who gets hired, who gets supported, and who gets advanced is part of understanding the market itself.
1. The 2026–2027 Cybersecurity Demographics Story Is Really About Access, Retention, and Advancement
The biggest mistake people make when discussing cybersecurity workforce demographics is assuming the issue begins and ends with entry-level hiring. It does not. The demographics problem starts earlier, inside awareness and access, then becomes more visible at screening, sharper at promotion, and most damaging at leadership level. That means the real question is not simply whether employers say they value diversity. The real question is whether they redesign hiring and advancement systems so more people can actually stay, specialize, and rise.
Recent industry research still shows the sector has a representation problem. The Global Cybersecurity Forum and BCG reported women make up only 24% of the cybersecurity workforce, while ISC2 has consistently placed women’s representation in the roughly 20% to 25% range. ISACA also reported that 87% of IT professionals believe gender diversity is lacking, yet only 41% of businesses have programs in place to hire more women in tech.
That matters because cybersecurity is not a field with excess capacity. NICE’s 2024 testimony to Congress emphasized the need to “prepare, grow, and sustain” the workforce and highlighted alternative pathways, apprenticeships, and equitable access as part of the solution. When a field has shortage pressure and still underutilizes broad talent pools, the issue is no longer awareness alone. It becomes a systems design failure.
For professionals reading this, the implication is practical. If you are building a career through ethical hacking, aiming for security consulting, preparing for manager-level cybersecurity roles, or targeting a future CISO pathway, workforce demographics are not background noise. They influence mentorship access, visibility, stretch assignments, sponsorship, compensation leverage, and even who gets trusted with “high upside” work.
2. What the Data Suggests About the Real Bottlenecks
The market often talks about a “shortage” as if the problem is simply not enough interested people. That is too shallow. The data suggests a more layered picture: broad labor demand, narrow hiring filters, weak on-ramps, uneven access to specializations, and poor retention mechanics. In other words, the industry does not just have a supply problem. It has a conversion problem.
The World Economic Forum’s 2024 gender gap reporting showed overall global parity progress remains slow, with full parity projected to take 134 years at the current rate. Cybersecurity exists inside that wider labor reality, not outside it. So when employers expect cyber to somehow fix its own inclusion problem without changing hiring design, promotion design, and manager behavior, they are asking the market to do what organizations themselves have not done internally.
This is especially important in cyber because specialization compounds inequality quickly. The gap between a junior responder and a cloud security architect is not just skill depth. It is access to systems, projects, mentors, labs, budget, trust, and visibility. Someone following a SOC analyst career guide can become highly operationally strong and still be passed over for higher-earning architecture work if they are never staffed onto cloud, IAM, or detection engineering projects. Someone studying vulnerability assessment techniques and tools, SIEM fundamentals, incident response planning, and cyber threat intelligence analysis still needs deliberate exposure to strategic work to convert technical capability into advancement.
The implication for 2026–2027 is clear: employers that widen access only at the bottom but do not diversify specialization and leadership pipelines will create better-looking hiring dashboards without changing power distribution. That is why mature organizations now need workforce reviews that examine who gets the certification budget, who gets architecture exposure, who presents to leadership, who owns controls mapping, and who gets introduced to executives.
3. Diversity Without Inclusion Fails Fast, and Cyber Teams Feel That Damage First
Representation can improve on paper while team reality gets worse. That happens when organizations hire more broadly but keep the same unwritten rules. In cybersecurity, this failure becomes visible fast because the work is already high-pressure. If the environment also demands overperformance just to be seen as credible, attrition becomes predictable.
ISC2’s 2024 workforce study found rising layoffs and budget cuts in cyber, while ISACA’s 2024 reporting noted increasing stress among cybersecurity professionals. In a pressured environment, inclusion gaps become more costly because under-supported employees are often the first to absorb ambiguity, role confusion, and uneven evaluation standards.
That is why inclusion must be operational, not symbolic. For cybersecurity teams, operational inclusion means five things. First, job expectations must be explicit. Second, performance standards must be visible and role-based. Third, managers must distribute stretch work intentionally. Fourth, mentorship must evolve into sponsorship. Fifth, advancement must not depend on informal access to insider networks.
This is where ACSMI readers should think strategically about positioning. If you want long-term resilience in the field, do not only build technical depth. Build evidence of business translation. A professional who can connect security audits and best practices to NIST, ISO, and COBIT frameworks, explain access control models, evaluate DLP strategies, and connect this work to future cybersecurity compliance trends becomes harder to sideline because their value is visible across technical and governance lines.
4. The Highest-Value Inclusion Fixes for 2026–2027 Are Structural, Not Cosmetic
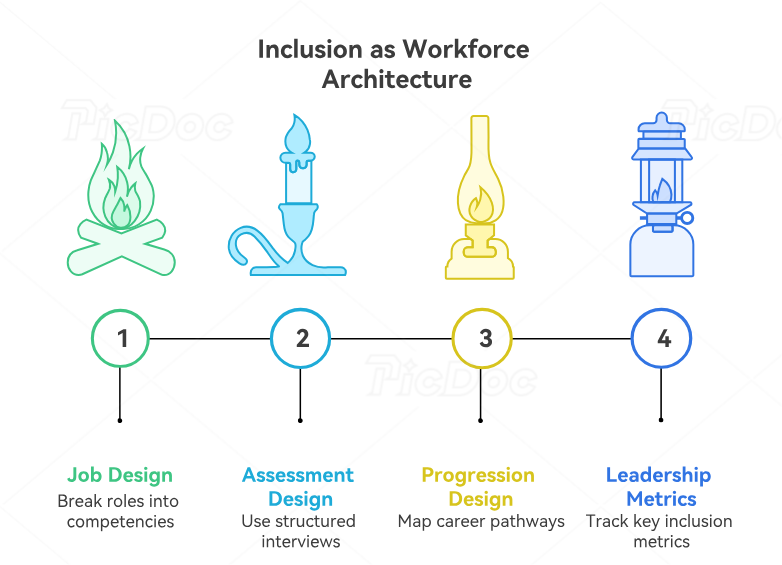
The most effective organizations over the next two years will stop treating diversity as a sourcing campaign and start treating inclusion as workforce architecture. That means redesigning the flow from awareness to hiring, from hiring to performance, and from performance to promotion.
Start with job design. Cybersecurity teams should break roles into demonstrated competencies rather than inflated credential wish lists. NICE’s workforce approach has long emphasized role clarity and multiple pathways into the profession. That matters because many strong future practitioners come through operations, networking, software, military service, career transitions, community college routes, apprenticeships, or adjacent risk functions.
Next comes assessment design. If interviews still reward the candidate who “sounds most familiar,” then headcount goals will never overcome gatekeeping. Structured scenario-based interviews, hands-on labs, and role-specific scorecards outperform vague “culture fit” conversations because they reveal capability rather than confidence theater.
Then comes progression design. This is where most organizations fail. They hire someone into SOC, governance, vulnerability management, or awareness, but they do not map how that person gets to engineering, architecture, leadership, product security, or executive influence. That creates stagnant middle layers. For readers who want to avoid that trap, study transition pathways early. Move from SOC analyst to SOC manager, understand the climb from security manager to director, examine the route into cybersecurity instructor or trainer roles, and even look at adjacent growth in curriculum development. Career visibility is inclusion infrastructure.
Finally, leadership metrics must mature. Tracking hiring alone is immature. The better scorecard tracks interview-stage conversion, offer acceptance, certification support, project assignment quality, promotion velocity, manager distribution of stretch work, and regrettable attrition by level. When these are visible, inclusion stops being rhetorical.
5. What This Means for Cybersecurity Professionals Planning Their Careers Right Now
If you are an individual professional, this report should change the way you manage your career. Do not wait for the market to become fairer before building leverage. Build leverage in a way that works even inside imperfect systems.
First, document outcomes, not just tasks. “Monitored alerts” is weak. “Reduced false positive triage time by tuning detections” is stronger. “Mapped controls to audit requirements and shortened evidence collection cycles” is stronger. “Improved phishing reporting workflows and increased user reporting rates” is stronger. Inclusion improves when value is harder to dismiss.
Second, build portable proof across technical and business layers. That means pairing technical credibility with framework literacy. Someone who understands firewall technologies and configurations, IDS deployment, VPN limitations and benefits, PKI components, and encryption standards but can also connect those topics to audit, compliance, identity, or business continuity becomes much more promotion-ready.
Third, target roles where market demand and inclusion opportunity intersect. The strongest opportunities in the next few years are likely to sit in fields where technical depth meets business necessity: cloud security, detection engineering, governance-risk-compliance, privacy engineering, cyber audit, resilience, sector-specific cyber advisory, and AI security oversight. ACSMI’s coverage of the future cybersecurity job market, specialized role demand, future skills by 2030, and automation’s impact on the workforce is especially useful here because it frames advancement in terms of capability shifts, not just job titles.
Fourth, choose employers like an investigator, not a hopeful applicant. Ask how they promote from within. Ask how budgets for training are allocated. Ask how they evaluate managers. Ask what percentage of leadership roles were filled internally. Ask whether remote staff advance at the same rate. Ask whether apprenticeships or internal transition programs exist. Inclusion is most visible in systems, not slogans.
6. FAQs
-
Cybersecurity decisions are made under uncertainty, pressure, and incomplete information. Teams that draw from a narrow set of experiences are more likely to miss blind spots in threat modeling, user behavior assumptions, crisis communications, insider risk patterns, and control design. Diversity alone does not guarantee better outcomes, but a more inclusive workforce expands perspective, strengthens problem framing, and helps organizations reach more of the talent they claim they cannot find.
-
Progress exists, but it is uneven and slower than many headlines imply. Women remain underrepresented in the field, and industry research continues to show that broad acknowledgment of the problem has outpaced structural action. Some employers are improving pathways through apprenticeships, alternative hiring models, and targeted workforce development, but many still have weak promotion and retention systems.
-
Diversity is who is present. Inclusion is who is heard, trusted, assigned meaningful work, promoted fairly, and retained. A team can improve representation and still fail inclusion if underrepresented professionals do not receive sponsorship, visibility, and advancement opportunities. In cybersecurity, inclusion is reflected in who gets staffed onto high-value projects like cloud migration, architecture reviews, detection engineering, audit leadership, and executive briefings.
-
The fastest high-impact changes are skills-based job descriptions, structured interviews, transparent promotion criteria, manager accountability, and real internal mobility pathways. Expanding sourcing without fixing evaluation and advancement only creates churn. NICE’s emphasis on multiple pathways and evidence-based workforce development supports this direction.
-
Focus on outcomes, specialization, visibility, and translation. Build measurable wins. Learn how your work maps to risk reduction and business priorities. Pursue one or two high-value specializations instead of scattered learning. Seek sponsors, not just mentors. And use career maps intentionally, whether you are pursuing cloud security engineering, cybersecurity management, auditing, or the long path to CISO.
-
Treating inclusion as a recruiting campaign instead of an operating model. The real failure is not always finding diverse candidates. It is failing to convert them into long-term, promoted, influential contributors. When certification support, stretch assignments, leadership exposure, and manager quality are uneven, the organization quietly recreates the same workforce shape it claims it wants to change.