Blogs
Cybersecurity Frameworks: NIST, ISO, and COBIT
Stop framework theater. Start running security.
Access Control Models: DAC, MAC, and RBAC Explained
Permissions drift quietly—until attackers notice.
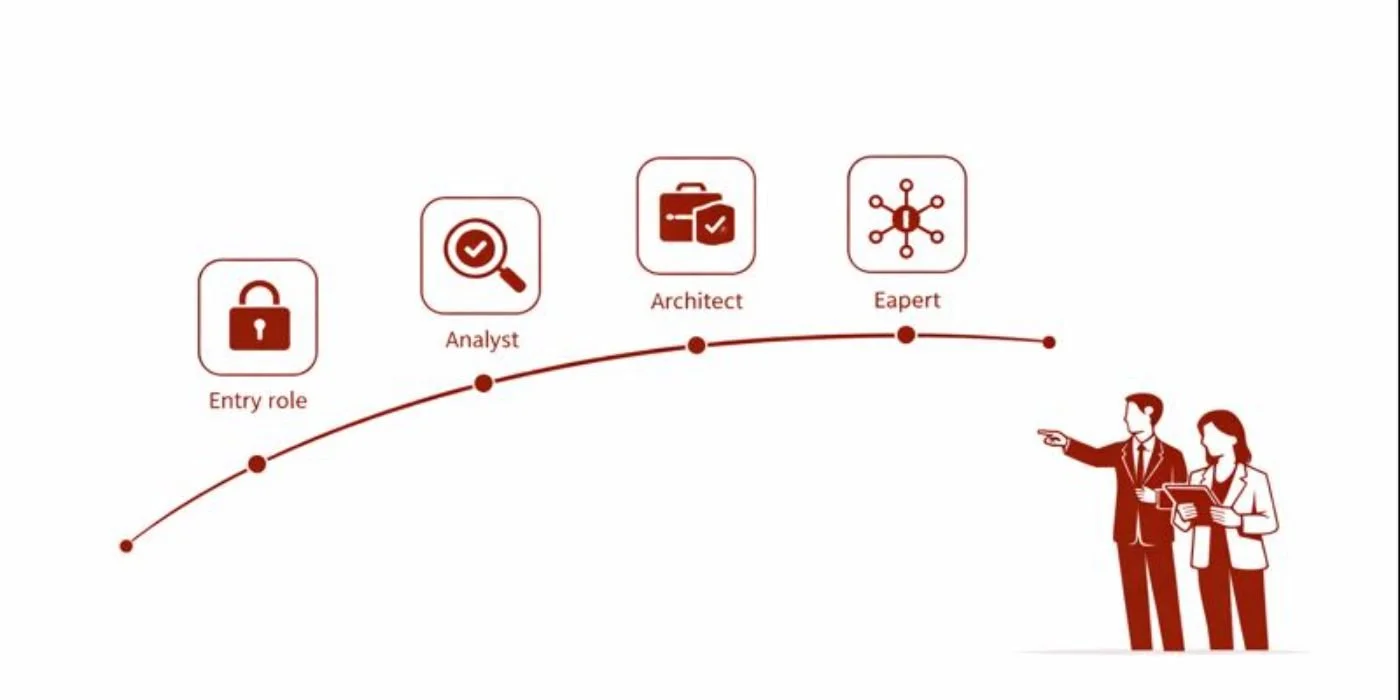
Career Roadmap to Cybersecurity Compliance Officer
Turn audits into your competitive advantage.
Top 10 Cybersecurity Threats Predicted to Dominate by 2030
2030 threats move faster than you.
Detailed Roadmap to IoT Security Specialist Careers
Secure devices before they secure attackers.
How to Become a Cloud Security Engineer: Complete Career Guide
Build guardrails. Catch drift. Get hired.
Career Roadmap: Becoming a Cybersecurity Curriculum Developer
Stop teaching theory. Ship job-ready labs.
How to Become a Cybersecurity Instructor: Step-by-Step Career Guide
Teach security with proof, not hype.
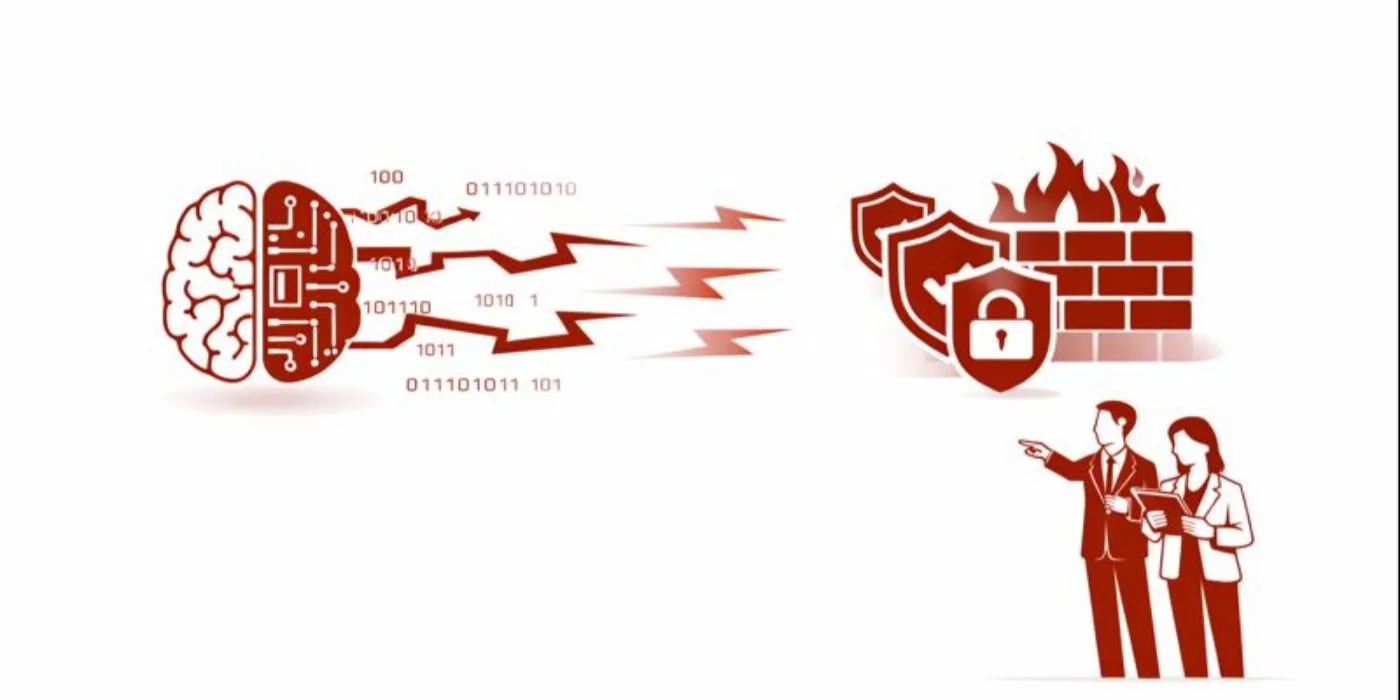
AI-Driven Cybersecurity Tools: Predicting the Top Innovations for 2026–2030
Less noise. More proof. Faster containment.
Predicting the Future of Zero Trust Security: Innovations & Implications by 2030
Zero Trust wins when access keeps changing.
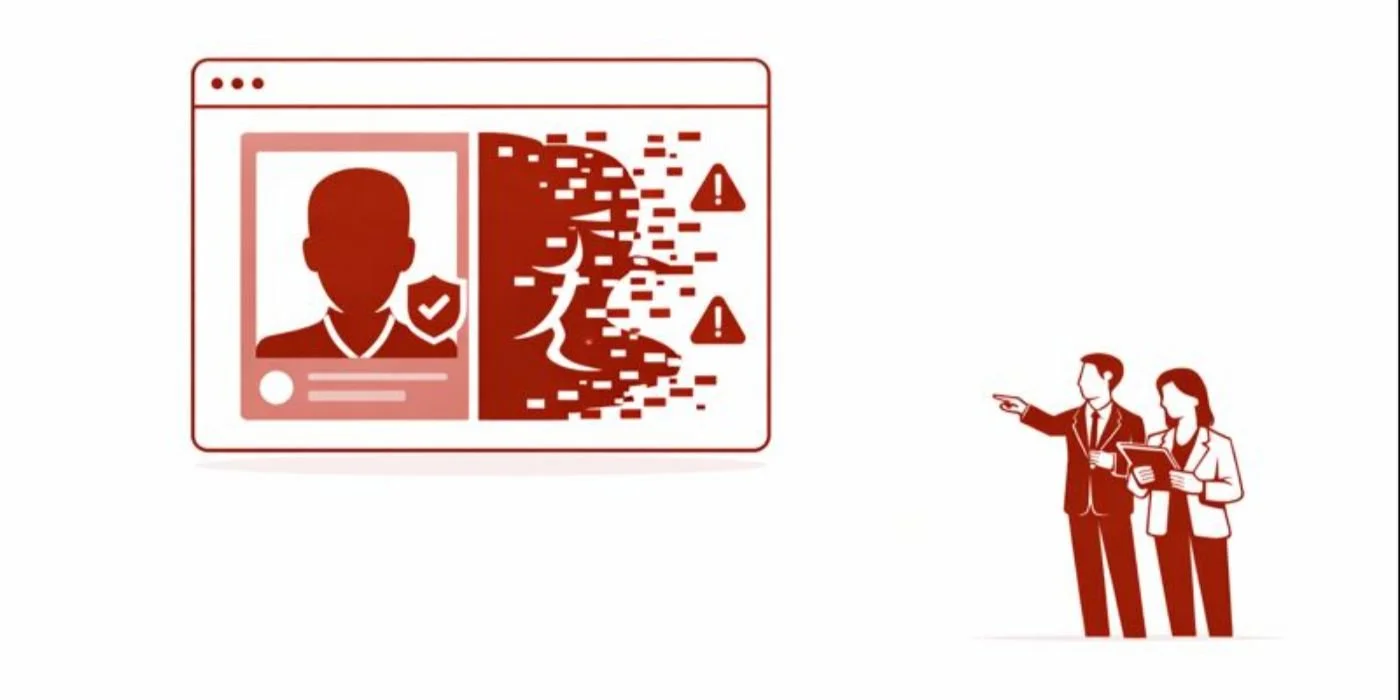
Deepfake Cybersecurity Threats: How to Prepare for the Upcoming Wave (2026 Insights)
Verify the request, not the voice.
AI-Powered Cyberattacks: Predicting Future Threats & Defenses (2026–2030)
AI attacks scale fast. Your defenses must.
Predicting the Next Big Ransomware Evolution: What Businesses Must Know by 2027
Stop ransomware leverage before encryption starts.
Remote Cybersecurity Careers: Predicting Long-term Trends & Opportunities (2026 Insights)
Remote work rewards proof, not promises.
Cybersecurity Certifications of the Future: What Employers Will Value Most (2026–2030)
Badges fade. Proof gets you hired.
Predicting Cybersecurity Job Market Trends: Roles That Will Thrive by 2030
Stop collecting tools. Start proving impact.