Financial Sector Cybersecurity Incidents: Detailed Original Analysis (2026-2027 Data)
Financial-sector cybersecurity is no longer a story about isolated bank breaches or one-off ransomware headlines. In 2026–2027, it is a systemic pressure story: credential abuse hitting customer-facing channels, exploit activity against public-facing apps, third-party concentration risk, fraud operations scaling through social engineering, and resilience questions moving from IT operations into board-level financial-stability discussions. This analysis treats incidents not as random events, but as patterns that reveal where banks, insurers, fintechs, payment firms, and capital-markets players are most exposed now.
For ACSMI readers, this matters whether you are building toward a role in cyber threat intelligence, planning a move into cloud security engineering, strengthening your path toward cybersecurity auditing, or studying the long climb from SOC analyst to SOC manager. The incident data shows exactly where employers, regulators, and financial institutions now need sharper defensive talent.
1. Financial-sector incidents in 2026–2027 are being shaped by concentration risk, identity abuse, and high-value monetization
The first hard truth is that financial institutions remain one of the most attractive targets in the threat landscape because attackers know where liquid value, rich identity data, regulatory pressure, and operational urgency meet. The IMF has warned that nearly one-fifth of reported cyber incidents over the past two decades affected financial firms, with banks the most frequent targets, and direct reported losses from incidents affecting the sector reached $2.5 billion from 2020 through 2023. The IMF also stresses that indirect losses are likely far higher because incidents are underreported and broader business harm exceeds direct loss tallies.
That is why a financial-sector incident should never be read narrowly as “just phishing,” “just ransomware,” or “just service disruption.” A successful intrusion at a bank can cascade into payment delays, customer mistrust, regulatory reporting burdens, incident-response overtime, third-party review costs, legal exposure, and strategic project slowdowns. Anyone studying incident response planning, SIEM fundamentals, DLP strategy, or security audits should understand that finance-sector cyber incidents are expensive not only because money can be stolen, but because trust, uptime, and evidentiary integrity all matter at once.
The second hard truth is that the 2026 pattern is tilting toward identity and exposure gaps rather than purely exotic zero-days. IBM’s 2026 X-Force Threat Intelligence Index found that exploitation of public-facing applications rose 44% year over year in its 2025 incident-response and investigation data, and that many exploited vulnerabilities did not require authentication. IBM also noted that financial services and insurance was the second most targeted industry after manufacturing. That finding matters because it tells defenders something uncomfortable: many of the incidents hitting finance are still fed by foundational weaknesses in access control, patch discipline, exposed applications, and identity governance.
2. The strongest incident patterns are not evenly distributed — they cluster around three pressure points
Verizon’s 2025 finance snapshot is especially useful because it shows what actually keeps repeating inside the financial and insurance vertical. It recorded 3,336 incidents and 927 confirmed-data-disclosure breaches. The top breach patterns were System Intrusion, Social Engineering, and Basic Web Application Attacks, and together they represented 74% of breaches in the sector. External actors drove 78% of breaches, while financial motives accounted for 90% and espionage 12%. That is not random noise. It is a pattern of monetizable intrusion against organizations with rich data and urgent operational workflows.
The first pressure point is system intrusion. In finance, this usually means the attacker is not satisfied with low-value access. They want durable footholds, access to valuable systems, or leverage for extortion. Verizon notes that System Intrusion remains the top pattern in the sector, while IBM’s 2026 reporting shows rising exploitation of public-facing applications. When you combine those two findings, the message is brutal but useful: institutions that still treat vulnerability assessment, firewall hardening, IDS deployment, and access control design as routine hygiene work are missing the strategic reality. In 2026–2027, those “basic” disciplines are what keep major incident chains from starting.
The second pressure point is social engineering tied to fraud and credential theft. Verizon found phishing and pretexting lead social actions in finance-related social-engineering incidents, while the FBI’s 2024 IC3 report said total reported losses exceeded $16.6 billion across internet crime and that business email compromise remained a major loss category nationally. The important analytical point is that finance-sector cyber teams can no longer separate cybersecurity cleanly from fraud defense, payment control, and executive approval workflows. The attack surface now includes human urgency, payment exception handling, vendor impersonation, and approval-chain weakness.
The third pressure point is web and cloud exposure. Verizon’s finance snapshot notes that stolen credentials are heavily involved in Basic Web Application Attacks, while IBM highlights the rise of exposed public-facing applications and supply-chain risk. This is why so many finance employers are increasing demand for talent that can connect cloud security, PKI and identity controls, encryption architecture, and zero-trust direction. Attackers are exploiting seams between application, identity, and external exposure management.
3. What the 2026–2027 data says about where finance teams are most likely to fail
The most dangerous misconception in financial cybersecurity is that the biggest threat is always the most sophisticated one. Often, it is the one that meets the weakest process at the highest-value moment. ENISA’s 2025 threat-landscape reporting shows finance accounted for 4.7% of all collected incidents, and within that set hacktivist-led DDoS dominated by volume at 83.5% of incidents. At the same time, ENISA’s finance-sector threat-landscape work also noted that 9% of observed incidents in its 2024 landscape targeted finance organizations. Those two findings together matter because they show a split reality: high-volume disruption risk on one side and higher-consequence intrusion, fraud, and compromise risk on the other.
For many institutions, the first major failure point is resilience under disruption. Finance is a top DDoS target in Verizon’s reporting, with 35% of denial-of-service targeting hitting finance, more than manufacturing and professional services. That means institutions cannot build their incident model around breach only. Customer-facing uptime, payment continuity, crisis communications, and traffic-surge absorption are part of cyber defense now. Professionals studying ransomware response, DoS mitigation, and the future of SIEM need to think in terms of service assurance, not just malware containment.
The second failure point is third-party dependency. Verizon’s 2025 DBIR materials flag third-party involvement as an ever-present subject, and IBM reports major supply-chain incidents have increased nearly fourfold over five years. In finance, that translates into concentrated risk around core processors, cloud providers, managed security partners, SaaS tooling, identity providers, and development ecosystems. A bank may harden its own perimeter and still inherit serious exposure through vendors, integrations, and connected services. That is why cybersecurity frameworks like NIST, ISO, and COBIT, audit practices, and future compliance trends are increasingly inseparable from operational defense.
The third failure point is evidence quality after compromise. Smaller institutions often underinvest in logging depth, retention, identity telemetry, and cloud forensics readiness. But in finance, incomplete evidence is not just a technical inconvenience. It weakens regulatory reporting, delays root-cause clarity, and prolongs customer and supervisory uncertainty. That is exactly why cyber incidents in finance now matter at the financial-stability level, not merely the IT-operations level. The IMF’s work on cyber risk and macrofinancial stability is essentially a warning that severe incidents at major institutions could become broader confidence events.
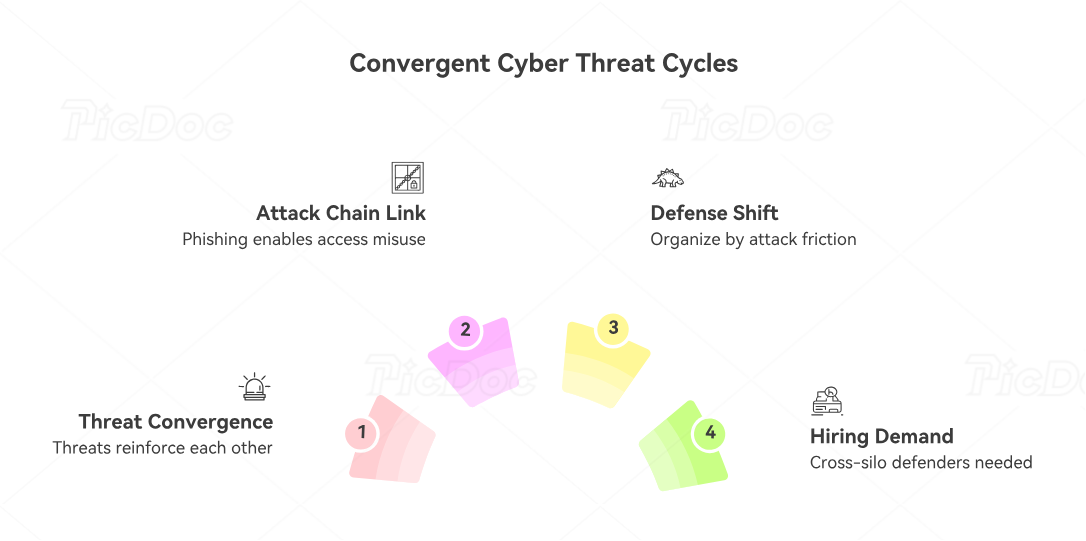
4. Original analysis: the financial sector’s incident problem is becoming a convergence problem
Here is the core analytical conclusion from the latest 2025–2026 evidence: the sector is not facing one dominant incident type but a convergence model. Identity abuse, application exploitation, social engineering, DDoS disruption, fraud operations, and third-party compromise increasingly reinforce one another. That is why many institutions still feel “busy” in security but not proportionately safer.
A phishing event may produce stolen credentials. Those credentials may unlock a cloud console, email system, or customer-support workflow. That access may then support fraud, lateral movement, data theft, or destructive disruption. Or a public-facing application flaw may provide initial access, which is then stabilized through privilege misuse or token abuse. In another case, a DDoS campaign may function as pressure, distraction, or customer-trust erosion while other attack paths are explored. The operational lesson is that defenders should stop organizing solely by tool domain and start organizing by attack-chain friction. IBM, Verizon, and ENISA are all pointing in that direction even when they use different language.
That convergence also explains why hiring demand is shifting. Institutions need defenders who can move across silos: analysts who understand threat intelligence, engineers who understand application security tooling, practitioners who can evaluate cloud security tools, specialists who understand PAM strategy, and leaders who can bridge cybersecurity management with director-level strategy. The sector’s incident pattern is rewarding defenders who can connect systems, not just own tools.
5. What financial institutions should do differently in 2026–2027
First, they need to treat identity as the front line. Password resets, MFA prompts, federated sessions, admin roles, device trust, and service-account governance now sit much closer to real financial loss than many institutions still admit. If attackers can bypass “login security” through stolen sessions, token abuse, or trusted access paths, then identity design has become a core incident-prevention layer, not an IAM side project. IBM’s 2026 findings and Verizon’s finance snapshot both support that conclusion.
Second, financial institutions need to stop measuring readiness only by breach prevention. In finance, outage resilience matters because DDoS volume, service disruption, and crisis communication can damage customer trust even without large-scale data exfiltration. ENISA’s 2025 landscape and Verizon’s DDoS targeting data make that plain. Institutions need tested traffic-management playbooks, customer communications plans, alternate service procedures, and leadership teams that can distinguish noise from severity without underreacting.
Third, third-party governance has to move from paperwork to operational validation. Vendor questionnaires alone will not solve the real problem of access concentration, integration sprawl, and hidden dependency chains. Financial firms should know which partners can affect payment operations, customer data, identity systems, development environments, and incident visibility. This is where audit careers, compliance pathways, and managerial cyber roles become commercially important, because financial institutions need people who can test control reality, not just collect attestations.
Fourth, they need to tighten the link between cyber telemetry and fraud intelligence. BEC, phishing, credential theft, account takeover, and social-engineering-driven approvals are no longer separate disciplines. Mature institutions will be the ones that fuse SOC data, fraud analytics, customer-behavior monitoring, and executive protection workflows into one response picture. This is also why ACSMI’s broader material on the future cybersecurity job market, specialized role demand, and future skills is useful here: the market increasingly rewards defenders who can correlate technical compromise with business harm.
6. FAQs
-
The strongest recurring patterns are system intrusion, social engineering, and basic web application attacks. Verizon’s 2025 finance snapshot says those three categories account for 74% of breaches in the financial and insurance vertical. DDoS also remains strategically important because finance is the top-targeted industry for denial-of-service in Verizon’s data.
-
Because the sector combines money movement, rich identity data, reputational sensitivity, regulated operations, and urgency-heavy workflows. The IMF says nearly one-fifth of reported cyber incidents have affected financial firms, and banks are the most frequent targets. Attackers go where liquid value and pressure coexist.
-
Increasingly, they are both. Social engineering, stolen credentials, cloud access abuse, BEC, and public-facing application exploitation often connect in the same attack chain. The old boundary between “fraud” and “cybersecurity” is getting weaker, especially for digital banking, payments, and executive approvals.
-
Identity hardening is still underappreciated relative to its impact. IBM’s 2026 reporting shows exploitation of public-facing applications rose 44% year over year and highlights persistent access-control and authentication weaknesses. Financial institutions that still treat IAM as a support function are underestimating the attack surface.
-
Finance increasingly rewards professionals who can connect incident response, identity, fraud, cloud, resilience, and governance. Strong career paths include SOC analysis, cloud security engineering, compliance leadership, security management, and eventually the CISO track. The institutions under pressure are looking for people who understand both controls and consequence.
-
The sector’s biggest issue is convergence. Finance is not being hit by one neat threat class but by linked attack chains spanning identity, apps, fraud, disruption, and third parties. Institutions that respond with separate, siloed controls will keep feeling overwhelmed. Institutions that reduce friction across the full incident chain will outperform.