Healthcare Cybersecurity Threat Report 2026-2027: Original Data & Actionable Insights
Healthcare cybersecurity in 2026–2027 is no longer just a privacy problem. It is an uptime problem, a patient-safety problem, a revenue-cycle problem, a medical-device problem, and a board-level resilience problem. The most dangerous healthcare attacks now succeed by exploiting operational dependence: EHR availability, lab systems, imaging workflows, identity systems, third-party platforms, and overworked teams that cannot patch fast enough. Recent HHS, Verizon, Microsoft, FDA, and Sophos findings all point in the same direction: attackers are moving faster, healthcare environments remain highly patch-fragile, and the cost of weak cyber hygiene is increasingly clinical as well as financial.
For ACSMI readers, the real value is not another recycled list of “top threats.” It is understanding which healthcare threats are actually rising, why they keep working, where the most damaging weak points are, and what actions create the highest defensive return over the next 12 to 24 months. That is why this report connects healthcare-specific risk with future cybersecurity compliance trends, incident response planning, ransomware detection and recovery, and cyber threat intelligence collection and analysis.
1. Why healthcare remains one of the most dangerous cybersecurity battlegrounds
Healthcare is uniquely exposed because it combines irreplaceable data, complex legacy infrastructure, distributed users, time-critical workflows, third-party dependencies, and environments where downtime quickly becomes operational harm. HHS OCR says there have been substantial increases in large breaches involving hacking and ransomware, enough that its 2024–2025 HIPAA audits are focusing specifically on Security Rule provisions most relevant to hacking and ransomware. That is a major signal: healthcare is not being pushed toward better security because of theory, but because the breach pattern has become too large to ignore.
The sector’s structural weakness is not just “old systems.” It is the collision of old systems with modern attack speed. Verizon’s 2025 findings show exploitation of vulnerabilities rose to 20% as an initial access vector, up 34% year over year, while only about 54% of edge-device vulnerabilities were fully remediated across the year and median remediation time was 32 days. In healthcare, 32 days is not a technical footnote. It is a large window for compromise in environments that cannot always patch aggressively because of uptime, vendor, and interoperability concerns. This is exactly why vulnerability assessment techniques and tools, firewall technologies, VPN security benefits and limitations, and intrusion detection systems deployment matter so much in healthcare settings.
Healthcare also suffers because cyber incidents have unusually broad blast radius. A successful attack does not just expose records. It can freeze scheduling, disrupt claims, delay procedures, interrupt labs, slow medication workflows, and force manual workarounds that increase human error. The Change Healthcare incident illustrates this brutally: HHS says approximately 190 million individuals were impacted, making it one of the most consequential healthcare cyber events on record. That one breach became a warning about concentration risk, third-party dependency, and what happens when healthcare operations sit on a few critical digital rails. Pair that with cybersecurity in healthcare predictions, small-business cybersecurity solutions, managed security service providers, and best cybersecurity companies for SMBs, and the pattern becomes hard to miss.
| Threat / Risk Area | Why It Hits Healthcare Hard | 2026–2027 Direction | Operational Consequence | Highest-Value Action |
|---|---|---|---|---|
| Ransomware | Downtime pressure makes hospitals vulnerable to coercion | Still severe | Care delays, claims disruption, recovery cost | Segment backups, test restoration, IR playbooks |
| Exploited edge vulnerabilities | Internet-facing devices remain slow to patch | Rising | Initial foothold into core systems | Exposure inventory plus fast patch triage |
| Credential abuse | Large workforces and shared urgency create weak identity habits | Persistent | Account compromise and lateral movement | Phishing-resistant MFA and privileged access control |
| Third-party platform compromise | Healthcare runs on external billing, EHR, lab, and claims vendors | High growth | System-wide outage or data spill | Tier vendors by clinical criticality |
| Phishing and email takeover | Staff speed and inbox overload create openings | Still common | PHI exposure and credential theft | Mailbox hardening and focused simulations |
| Medical device cybersecurity gaps | Long-lived devices and vendor constraints slow remediation | Increasing importance | Patient-safety and service-delivery risk | Device inventory and vendor security clauses |
| Unmanaged endpoints | Clinician workflows spread access across many devices | Rising | Stealer infections and hidden persistence | Managed endpoint policy and isolation |
| Infostealer malware | Stolen sessions and browser secrets fuel reuse | Growing | Silent account compromise | Session hygiene and credential rotation |
| Cloud misconfiguration | Fast migration often outpaces governance | Rising | Data exposure and policy drift | Posture management and IAM review |
| Identity sprawl | Contractors, partners, clinicians, and vendors expand access paths | Rising | Privilege creep and hidden attack paths | Lifecycle access governance |
| Legacy systems | Critical apps may depend on unsupported infrastructure | Persistent | Patch delays and compensating-control burden | Segmentation and migration roadmap |
| AI-assisted phishing | Healthcare brands, patients, and vendors are easy to impersonate | Fast growth | More convincing lures and fraud | Human verification workflows |
| Deepfake social engineering | Voice and identity trust are high in care settings | Emerging | Payment, access, or approval fraud | Out-of-band verification |
| Bot-driven account abuse | Portals and digital services attract automation | Rising | Fraud, fake signups, credential stuffing | Bot detection and adaptive controls |
| Third-party secrets exposure | Repositories and integrations leak access paths | Rising | Vendor-linked compromise | Secret scanning and rotation SLAs |
| Remote access abuse | Distributed care and vendors rely on remote tools | Persistent | Unauthorized administrative reach | Tighten remote access scope |
| Poor backup discipline | Recovery complexity is underestimated | Still dangerous | Long outages and ransom leverage | Immutable backups and restoration drills |
| Weak incident coordination | Clinical and IT teams often rehearse separately | High concern | Slower containment under pressure | Joint clinical-IT tabletop exercises |
| Asset visibility gaps | Healthcare estates are sprawling and unevenly documented | Persistent | Unknown exposure and blind spots | One authoritative asset inventory |
| Data exfiltration without encryption | Attackers monetize PHI even without locking systems | Rising | Extortion and compliance fallout | Egress monitoring and DLP |
| Overprivileged service accounts | Complex integrations create long-lived access | Persistent | Stealthy broad compromise | Least privilege review |
| Patch-approval bottlenecks | Clinical validation slows normal patch cycles | Still major | Exploit windows stay open | Risk-ranked patch governance |
| Compliance-only security mindset | Paper compliance creates false confidence | Dangerous | Auditable but fragile posture | Operational control testing |
| Vendor lock-in security limits | Some platforms restrict hardening flexibility | Persistent | Long-term inherited risk | Security terms in procurement |
| Staff cyber fatigue | High-volume care work reduces attention margin | Increasing | Higher click and bypass rates | Short, role-specific training |
| Recovery communication failures | Patients, partners, and clinicians need coordinated updates | Underrated risk | Confusion, trust loss, slower restoration | Crisis communication playbooks |
2. The most important healthcare threat signals for 2026–2027
Ransomware remains the headline risk, but the deeper pattern is more revealing: the threat is being sustained by slow remediation, exposed edge infrastructure, credential abuse, and dependencies that create broad operational choke points. Verizon says ransomware was present in 44% of all breaches reviewed, up from 32% the prior year, while third-party involvement in breaches doubled from 15% to 30%. Those two facts matter together. Healthcare defenders often discuss ransomware as if it were just a malware problem, when in reality it is frequently an ecosystem fragility problem. Best data loss prevention software, top network monitoring and security tools, best PAM solutions, and security audits process and best practices all become more valuable when ransomware is treated as a systems issue rather than a single-tool issue.
The second major signal is that healthcare identity risk is becoming more dangerous, not less. Verizon still found credential abuse to be the most common initial access vector, while Microsoft reports AI-driven phishing is now three times more effective than traditional campaigns. In a sector where staff routinely act under urgency and trust-based communication is constant, that is a serious multiplier. Attackers do not need perfect technical elegance if they can get a real user to open the door. This is exactly why access control models, public key infrastructure, encryption standards, and future zero-trust innovation should be seen as healthcare-relevant, not abstract infrastructure topics.
A third signal is device and digital-service expansion. FDA finalized updated medical device cybersecurity guidance in June 2025, explicitly framing cybersecurity as a shared responsibility across healthcare facilities, providers, patients, and manufacturers. That is important because device risk is no longer a narrow biomed niche. It is part of everyday healthcare exposure. At the same time, Microsoft says more than 90% of 15.9 billion Microsoft account creation requests in the first half of 2025 were from bad bots, and it blocked about 1.6 million bot-driven or fake-account signup attempts per hour across its services. Healthcare portals, patient apps, and digital-service interfaces sit directly inside this broader automated threat environment. Future of cloud security, AI-driven cybersecurity tools, deepfake cybersecurity threats, and next-gen SIEM connect directly to this shift.
3. Original ACSMI threat interpretation: what the data really says
The clearest interpretation from current evidence is that healthcare is not losing mainly because adversaries are unbeatable. It is losing because attackers keep finding environments where urgency outpaces control discipline. Verizon’s figures on vulnerability exploitation, remediation lag, third-party involvement, and ransomware growth show the same thing from different angles: healthcare defense is too often reactive around the exact assets that matter most. HHS OCR’s audit focus reinforces this by zeroing in on ransomware- and hacking-relevant Security Rule controls. Cybersecurity frameworks NIST ISO and COBIT, future audit practices, future privacy regulation trends, and GDPR 2.0 predictions all point toward the same conclusion: healthcare organizations will be pushed toward evidence-backed control maturity, not checkbox comfort.
A second ACSMI insight is that healthcare cyber risk is now inseparable from dependency mapping. The Change Healthcare breach was not merely “a big breach.” It was a demonstration that concentration risk can turn a vendor incident into industry-scale disruption. Verizon’s doubling of third-party involvement in breaches adds a broader pattern behind that headline event. In practical terms, healthcare security leaders should stop treating vendor risk as paperwork owned by procurement and start treating it as continuity engineering. Best cybersecurity firms specializing in financial services, directory of leading healthcare cybersecurity firms, top cybersecurity providers for nonprofits, and cybersecurity solutions for small businesses are useful because they highlight how different sectors are increasingly evaluating provider capability and resilience posture.
A third insight is that AI is not only a defender story. Microsoft’s report makes clear that AI is pushing threats to new levels of speed, scale, and sophistication, with AI-driven phishing materially outperforming older campaigns. In healthcare, that matters because high-trust communication channels are everywhere: physicians, nurses, billing teams, labs, pharmacies, vendors, patients, and administrators all interact across urgent workflows. That creates ideal conditions for AI-enhanced impersonation, more convincing fraud, and faster social engineering. AI-powered cyberattacks, future threats by 2030, predicting the next ransomware evolution, and future endpoint security trends become directly useful when healthcare leaders start planning for persuasion attacks, not just malware attacks.
4. Actionable healthcare defense priorities for 2026–2027
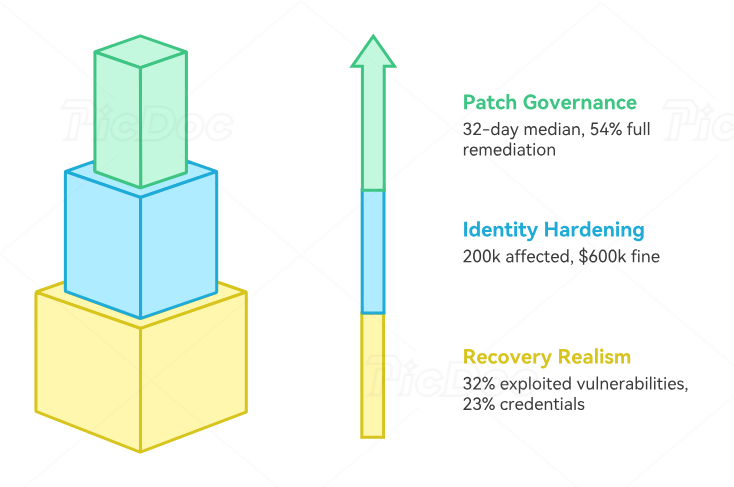
The first action priority is patch governance by clinical consequence, not by generic severity alone. Verizon’s data on 32-day median remediation and 54% full remediation across the year shows that many organizations are still losing too much time between discovery and actual closure. Healthcare teams need a patch process that distinguishes between “internet-facing, credential-bearing, care-adjacent, third-party-connected” assets and everything else. That is a different discipline from simply running vulnerability scans. Vulnerability assessment techniques, best endpoint security solutions, top network monitoring tools, and cloud security tools directory all support that effort.
The second priority is identity hardening around real healthcare behavior. The right move is not generic awareness training blasted to everyone equally. The right move is role-specific friction where fraud would be most costly: privileged approvals, vendor-access changes, payment instructions, patient-data exports, account recovery, and remote-access elevation. HHS’s 2025 phishing settlement with PIH Health, involving nearly 200,000 affected individuals and a $600,000 settlement, is a reminder that mailbox compromise is still operationally and regulatorily expensive. Best privileged access management solutions, directory of security awareness platforms, DLP strategies and tools, and security awareness training platforms are especially relevant here.
The third priority is recovery realism. Sophos says exploited vulnerabilities were the most common root cause of ransomware incidents in 2025 at 32%, followed by compromised credentials at 23%, while malicious email and phishing remained meaningful vectors. That means healthcare recovery planning must assume a mixed-cause incident, not a neat single-entry scenario. Backups matter, but so do isolation logic, identity recovery, dependency prioritization, and manual workflow rehearsals for care continuity. Incident response execution, ransomware response and recovery, cybersecurity in government public sector, and cybersecurity in energy and utilities are valuable comparison points because other critical sectors are solving similar resilience problems.
5. What healthcare leaders should expect next
The 2026–2027 threat environment is likely to become more identity-heavy, more automated, and more dependency-driven. Expect more attacks that blend credential theft, bot activity, social engineering, and third-party weaknesses instead of relying only on loud encryption events. Expect regulatory scrutiny to intensify around whether organizations can show concrete Security Rule discipline against exactly these patterns. And expect medical-device security to become more operationally important as FDA guidance continues pushing lifecycle thinking and shared responsibility.
The organizations that will look strongest by the end of 2027 are not necessarily the ones with the most tools. They are the ones that can answer five uncomfortable questions honestly: Which clinical and revenue functions would break first? Which vendors could take us down with them? Which identities would create the biggest blast radius if compromised? Which devices and edge assets cannot be patched cleanly? And how long would it really take us to restore trusted operations under pressure? Those are the questions that turn security audits, cybersecurity managers, cybersecurity auditors, and compliance officer pathways into practical healthcare value.
The bottom line is simple. Healthcare cyber defense can no longer be built around the hope that “we are too important to be disrupted.” Importance is exactly what makes healthcare attractive to attackers. The winning posture for 2026–2027 is disciplined resilience: faster exposure closure, stronger identity trust controls, real vendor criticality mapping, medical-device visibility, and recovery plans tested against the messiness of actual healthcare operations. Future skills for cybersecurity professionals, predicting healthcare cyber trends, best healthcare cybersecurity firms, and cybersecurity job market trends all fit into that same future-facing picture.
6. FAQs
-
Ransomware remains the biggest single operational threat, but the more useful answer is this: healthcare’s biggest risk is the combination of ransomware, vulnerability exploitation, identity abuse, and third-party dependency. Those factors reinforce each other and create large operational disruption potential.
-
Because healthcare combines sensitive data, urgent workflows, legacy systems, distributed users, vendor dependence, and environments where downtime is unusually costly. Attackers know pressure changes defender behavior.
-
Yes. HHS OCR’s 2025 PIH Health settlement shows mailbox compromise still leads to large exposures, and Microsoft says AI-driven phishing is now far more effective than traditional campaigns. That combination keeps phishing highly relevant.
-
Extremely important. The incident showed that a single critical healthcare platform can become a systemic disruption point, and Verizon’s 2025 data shows third-party involvement in breaches doubled to 30%. Vendor risk now has to be treated as continuity risk.
-
Yes. FDA’s 2025 final guidance underscores that device cybersecurity is a shared responsibility and should be handled as a lifecycle issue. As digital care expands, device security becomes more operationally important, not less.
-
Start with exposure management for internet-facing assets, identity hardening for privileged and high-trust workflows, vendor criticality mapping, recovery testing, and clinical-IT incident coordination. Those actions address the patterns the current evidence says are doing the most damage.