Complete Directory of Best Cloud Security Tools (2026-2027 Edition)
Cloud security in 2026-2027 is no longer about buying one “best” tool and calling it done. Most breaches now happen in the gaps between tools: misconfigured identity permissions, unmanaged SaaS exposure, weak API controls, silent data sprawl, broken detections, and cloud changes moving faster than security review cycles. This guide is built to help teams buy systems that work together—not just logos for a slide.
If you are building or upgrading a cloud security stack, this ACSMI directory gives you a practical map: categories that matter, where each tool class fits, how to shortlist vendors, how to avoid overlap, and how to run a proof of value that survives real-world operations.
1) How to Build a Cloud Security Tool Stack That Actually Reduces Risk
Most cloud security programs fail for one reason: they buy tools based on feature demos instead of attack paths. Security leaders end up with overlapping dashboards, weak ownership, and alert volume that grows faster than response quality. The result is familiar—cloud risk is “visible,” but not controlled.
The right way to buy cloud security tools is to map your stack to cloud attack chains:
identity abuse (stolen tokens, overprivileged roles, OAuth grants),
misconfiguration exposure,
workload compromise,
data exfiltration,
lateral movement,
weak detection and slow response.
To build that map properly, align cloud tooling decisions with your core ACSMI foundations: cybersecurity frameworks NIST ISO and COBIT, security audits processes and best practices, vulnerability assessment techniques and tools, incident response plan IRP development and execution, and security information and event management SIEM an overview.
Your cloud stack also has to fit emerging realities: future of cloud security predictive analysis of key trends 2026-2030, predicting the future of zero trust security innovations and implications by 2030, AI-powered cyberattacks predicting future threats and defenses 2026-2030, AI-driven cybersecurity tools predicting the top innovations for 2026-2030, and privacy regulations cybersecurity emerging global trends predictions 2026-2030.
What high-performing cloud security teams do differently
They do tool rationalization before tool expansion. Instead of asking “What’s the best CNAPP?” they ask:
Which risks are currently unowned?
Which alerts have no responder?
Which controls fail in multi-cloud?
Which tools create duplicate tickets?
Which cloud teams bypass us because security is too slow?
Those questions build trust fast—because they speak to pain the business already feels.
| # | Tool Category | What It Protects | Primary Use Case | Best-Fit Teams | Common Buying Mistake |
|---|---|---|---|---|---|
| 1 | CNAPP | Cloud posture + workloads + identity context | Unified cloud risk visibility and prioritization | Mid-market to enterprise multi-cloud | Assuming “unified” means easy implementation |
| 2 | CSPM | Cloud account/config misconfigurations | Posture management and compliance checks | Cloud platform/security teams | Treating posture alerts as auto-remediated risk |
| 3 | CWPP | Workloads (VMs, containers, Kubernetes) | Runtime protection and workload hardening | Platform + DevSecOps teams | Buying without runtime response ownership |
| 4 | DSPM | Sensitive data in cloud stores/services | Data discovery, exposure mapping, governance | Security + privacy + data teams | Confusing discovery with enforcement |
| 5 | CIEM | Cloud identities and permissions | Least privilege and entitlement control | IAM/cloud security teams | Ignoring app/service identity sprawl |
| 6 | CASB | SaaS use, shadow IT, data movement | SaaS governance and data policy enforcement | Remote/SaaS-heavy organizations | No sanctioned app catalog before rollout |
| 7 | SSE/SASE DLP | Web, SaaS, remote user data egress | Inline protection and policy enforcement | Distributed enterprises | Neglecting endpoint/offline leakage paths |
| 8 | Cloud DLP | Sensitive data in cloud apps/storage | Detection, classification, policy enforcement | Compliance-heavy cloud programs | No policy tuning plan |
| 9 | KSPM | Kubernetes posture/config | Cluster hardening and drift detection | Container/K8s teams | Buying without cluster inventory hygiene |
| 10 | Container Image Scanning | Images, dependencies, base layers | Shift-left vulnerability detection | DevSecOps/CI-CD teams | No exploitability prioritization |
| 11 | IaC Scanning | Terraform, CloudFormation, ARM, etc. | Pre-deploy policy validation | Engineering-led cloud teams | Rules too strict, developers bypass pipeline |
| 12 | Secrets Scanning | Keys, tokens, credentials in code/repos | Credential leak prevention | DevSecOps/AppSec | No rotation automation after detection |
| 13 | API Security (Discovery + Runtime) | APIs, endpoints, auth paths | API exposure and abuse prevention | Digital product/API teams | Only documenting known APIs |
| 14 | WAAP/WAF | Web apps and APIs | Layer 7 protection, bot mitigation, abuse defense | Internet-facing app owners | Treating WAF as full app security |
| 15 | CW NDR / Cloud Threat Detection | Cloud traffic patterns and behaviors | Detection of anomalies/lateral movement | SOC + cloud security | No tuning to cloud baseline behavior |
| 16 | Cloud SIEM / XDR Integration | Logs, detections, correlation | Cloud attack visibility and response coordination | SOC teams | Ingest everything, prioritize nothing |
| 17 | SSPM | SaaS app security posture | Configuration hardening for SaaS platforms | SaaS governance teams | No ownership for SaaS business admins |
| 18 | Email Security (Cloud-native) | Business email, phishing, data leakage | Inbound/outbound protection and abuse detection | Most organizations | Ignoring cloud app compromise after email |
| 19 | EDR/XDR for Cloud Workstations | User endpoints accessing cloud data | Endpoint telemetry and response | Hybrid/remote organizations | Separating endpoint and cloud investigations |
| 20 | PAM for Cloud Admin Access | Privileged access sessions/credentials | Admin access control and session accountability | Regulated or high-risk enterprises | Leaving break-glass accounts unmanaged |
| 21 | ZTNA | User-to-app access | Reduce VPN exposure, enforce context-based access | Remote-first or hybrid enterprises | No app segmentation strategy |
| 22 | Cloud Backup / Ransomware Resilience | Data recovery and continuity | Recovery from cloud account or data compromise | All cloud-reliant organizations | Assuming SaaS native retention equals recovery |
| 23 | ASM/EASM for Cloud Assets | Internet-exposed cloud assets | External attack surface discovery | SOC + platform + risk teams | No remediation owner per asset |
| 24 | Compliance Automation / GRC-Cloud Connectors | Control evidence and audit posture | Continuous evidence collection | Audit/compliance-heavy orgs | Treating screenshots as control proof |
| 25 | SOAR / Workflow Automation | Response workflows across cloud tools | Containment, routing, enrichment automation | Mature SOCs | Automating bad triage logic |
| 26 | Threat Intel Platforms (Cloud-relevant) | Indicators, actor patterns, prioritization | Cloud threat context and enrichment | Maturing SOCs | Buying feeds without analyst workflows |
| 27 | MDR / Managed Cloud Detection | 24/7 monitoring and response support | Coverage for lean teams | SMB to enterprise understaffed SOCs | Not validating service scope and SLAs |
| 28 | Cloud Native IAM Analytics | Role trust paths and privilege chains | Identity risk reduction | Cloud/IAM teams | Focusing only on human identities |
| 29 | Log Pipeline / Data Routing Controls | Security telemetry transport and retention | Cost control and detection reliability | SOC/platform engineering | Dropping fields needed for investigations |
| 30 | Cloud Security Training Labs / Sandboxes | Human capability and validation skills | Hands-on cloud attack/defense readiness | Teams upskilling fast | Training disconnected from production risks |
2) Best Cloud Security Tool Categories to Prioritize First (By Risk, Not Hype)
“Best tools” depends on what you are trying to stop. A startup with one cloud account and strong CI/CD discipline does not need the same stack as a regulated enterprise running multi-cloud workloads, hundreds of SaaS apps, and globally distributed contractors.
Priority Stack A: If your biggest pain is misconfiguration and compliance drift
Start with:
CSPM / CNAPP
IaC scanning
Cloud SIEM integration
Compliance automation
These teams usually feel pain during audits, client questionnaires, and incident retrospectives. They discover “known issues” were sitting in dashboards for months without a remediation owner. Fix that by tying findings to security audits processes and best practices, future of cybersecurity compliance predicting regulatory trends by 2030, GDPR 2.0 predicting the next evolution in data privacy regulations, and predicting future cybersecurity audit practices innovations changes 2026-2030.
Priority Stack B: If your biggest pain is identity abuse and privilege sprawl
Start with:
CIEM
PAM
ZTNA
Cloud identity analytics
Detection via SIEM/XDR
Cloud breaches increasingly succeed through identity, not malware. Teams must understand access control models DAC MAC and RBAC explained, improve public key infrastructure PKI components and applications, modernize intrusion detection systems IDS functionality and deployment, and connect identity signals into cyber threat intelligence CTI collection and analysis.
Priority Stack C: If your biggest pain is data exposure in SaaS and cloud storage
Start with:
DSPM
Cloud DLP / SSE DLP
CASB / SSPM
Email security
IR workflow integration
This is where teams realize data governance and security operations have to collaborate. Review ACSMI’s data loss prevention DLP strategies and tools, directory of best email security solutions for enterprises 2025, security information and event management SIEM an overview, incident response plan IRP development and execution, and best managed security service providers MSSPs ultimate 2025 guide.
The core lesson: buy sequence, not just tools. A smaller stack with clear owners beats a giant stack with no one responsible for remediation.
3) Cloud Security Tool Directory: What “Best” Looks Like in 2026-2027 by Category
This section is the practical shortlist logic you can use in internal planning meetings. Instead of arguing brands too early, first align on category outcomes and success metrics.
CNAPP / CSPM / CWPP platforms
These are your “visibility + prioritization + workload security” backbone. They are strongest when they reduce noise, map toxic combinations (misconfig + exposed workload + privilege path), and tie findings to remediation workflows. If they only generate posture findings without ownership, they become expensive reporting tools.
Pair these decisions with next gen SIEM future cybersecurity technologies you need to watch 2026-2030, leading endpoint security providers complete directory and comparison, ultimate guide to the best endpoint detection and response EDR tools, top 20 vulnerability scanners for 2025 expert guide and rankings, and complete directory of best SIEM solutions ranked and reviewed 2025.
CIEM / PAM / Zero Trust access tooling
This category is where mature cloud programs are winning major risk reduction because it directly addresses credential misuse and privilege escalation. Strong tools here should show:
entitlement graphing,
role trust path analysis,
least-privilege recommendations,
privileged session accountability,
integration with detection and response.
Use ACSMI support content like predicting demand for specialized cybersecurity roles ethical hacking threat intelligence 2026-2030, future skills for cybersecurity professionals essential competencies by 2030, predicting cybersecurity job market trends roles that will thrive by 2030, and cybersecurity certifications of the future what employers will value most 2026-2030 to frame staffing and capability planning.
DSPM / DLP / CASB / SSPM tools
These are essential when the organization’s biggest pain is “we don’t know where sensitive data is” and “business teams keep spinning up SaaS apps.” Good vendors don’t just classify data—they help you assign owners, understand exposure paths, and create enforceable policies with minimal business disruption.
Complement this with best data loss prevention DLP software directory and reviews, directory of best email security solutions for enterprises 2025, top 50 cybersecurity companies worldwide 2025 comprehensive directory, and global directory of cybersecurity training providers.
4) How to Evaluate Cloud Security Tools in a Real POC (Without Getting Trapped by Demos)
A cloud security tool POC should simulate operational pain, not ideal lab conditions. If your POC only proves the product can detect a known misconfiguration on a sample tenant, you learned almost nothing.
Build your POC around 10 high-value scenarios
Overprivileged cloud role with unused permissions
Publicly exposed storage with sensitive data
Risky SaaS OAuth grant or third-party app access
Container image with critical vulnerability entering pipeline
K8s misconfiguration drift after deployment
API endpoint exposed with weak auth policy
Suspicious data egress from cloud storage or SaaS app
Alert flood day: tune top 20 noisy findings
Multi-team remediation workflow (platform, app, security)
Executive reporting and audit evidence extraction
Tie evaluation to adjacent defenses and response mechanics using firewall technologies types and configurations, virtual private networks VPNs security benefits and limitations, ransomware detection response and recovery, denial of service DoS attacks prevention and mitigation, and botnets structure and disruption methods.
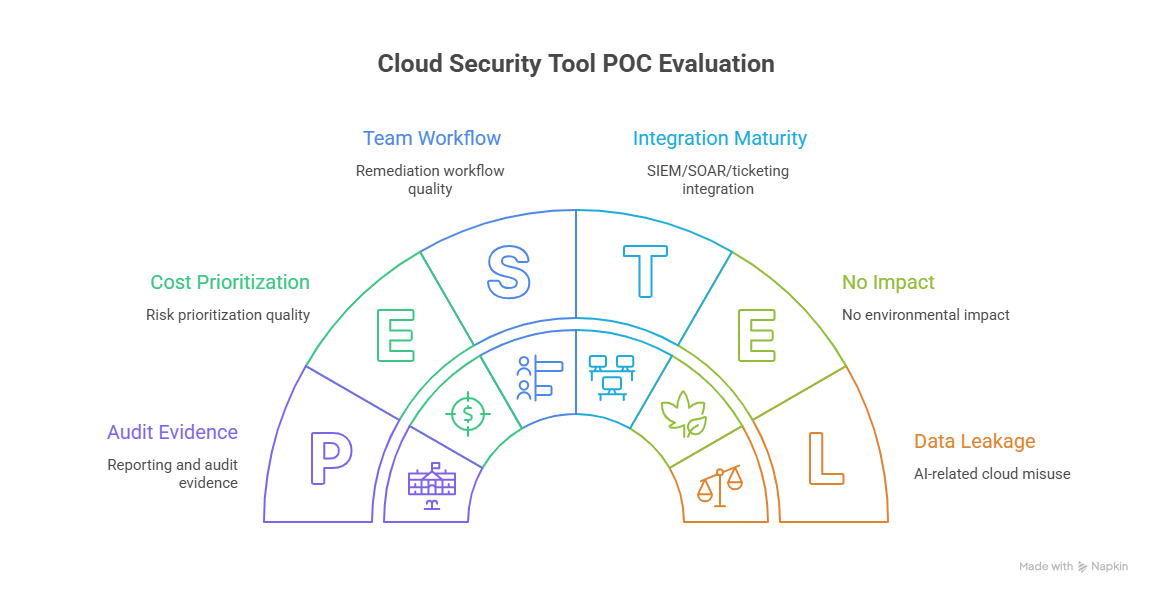
What to score (weighted, not vague)
Risk prioritization quality (20%): Does it surface what matters now?
Remediation workflow quality (20%): Can teams act quickly without confusion?
Identity context depth (15%): Can it explain privilege and access blast radius?
Coverage breadth (15%): Multi-cloud, SaaS, workloads, APIs, data, identities.
Alert noise and tuning (10%): Can analysts make it livable?
Integration maturity (10%): SIEM/SOAR/ticketing/IAM/dev pipelines.
Reporting and audit evidence (10%): Useful for leadership and auditors.
The hard questions buyers should ask every vendor
Show us a false-positive reduction workflow, not just detections.
Show us remediation ownership routing across engineering teams.
Show us how you handle service identities and machine roles.
Show us what breaks in multi-cloud at scale.
Show us evidence export for audits and incidents.
Show us how your product handles AI-related cloud misuse and data leakage.
These questions create immediate separation between mature platforms and polished demos.
5) Cloud Security Tool Buying Mistakes That Waste Budget (and How to Avoid Them)
Cloud security budgets are being spent, but not always converted into measurable risk reduction. The most expensive mistake is buying a tool category because it is trending, while your actual attack path remains unowned.
Mistake 1: Buying a “platform” without a remediation model
Platforms that aggregate findings are valuable only if findings get fixed. If you cannot map issues to owners (cloud platform, app team, IAM team, data team, SOC), your stack becomes a visibility museum.
Mistake 2: Ignoring identity because the focus is “cloud posture”
Many programs overinvest in posture scanning while underinvesting in identity controls. Meanwhile, attackers exploit stale access, permissive trust relationships, and service-account abuse. Strengthen this area with access control models DAC MAC and RBAC explained, predicting future of zero trust security innovations and implications by 2030, cyber threat intelligence CTI collection and analysis, and security information and event management SIEM an overview.
Mistake 3: Treating cloud security as separate from industry risk context
Healthcare, finance, retail, manufacturing, government, education, and utilities face different cloud risk patterns, regulatory pressure, and business continuity concerns. Use ACSMI’s sector analyses to tailor stack priorities: healthcare cybersecurity predictions emerging trends risks for 2026-2030, cybersecurity trends in finance predictive insights into emerging risks 2026-2030, retail e-commerce cybersecurity predicting the future landscape 2026 to 2030, manufacturing sector cybersecurity predicting key security trends by 2030, and predictive analysis of cybersecurity in government public sector by 2030.
Mistake 4: No staffing plan for cloud security operations
A great tool in the hands of an overloaded team becomes shelfware. Build realistic operating plans using automation and the future cybersecurity workforce will robots replace analysts 2026-2030, remote cybersecurity careers predicting long-term trends and opportunities 2026 insights, future skills for cybersecurity professionals essential competencies by 2030, and directory of free cybersecurity courses and resources 2025 edition.
6) FAQs: Complete Directory of Best Cloud Security Tools (2026-2027 Edition)
-
For most organizations, the highest-impact categories are CNAPP/CSPM, CIEM/IAM controls, cloud detection + SIEM integration, and data protection tooling (DSPM/DLP/CASB). The exact order depends on your biggest risk path: misconfiguration, identity abuse, data exposure, or detection blind spots.
-
If your team is small or your cloud stack is growing quickly, a CNAPP can reduce operational complexity and help with unified prioritization. If you have mature platform engineering, AppSec, IAM, and SOC teams, best-of-breed tools may provide deeper capabilities in identity, data security, or runtime protection. The decision should be based on workflow maturity—not just feature checklists.
-
No. Posture is critical, but many serious incidents involve identity misuse, token abuse, SaaS app exposure, API weaknesses, and slow response coordination. A posture-only program creates visibility without containment if detection, access control, and remediation operations are weak.
-
Too many is when the same issue appears in multiple dashboards and nobody knows which team owns remediation. A lean, integrated stack with clear owners is better than a large stack with duplicate alerts and no enforcement path. Track ownership, time-to-remediate, and false-positive burden—not just number of tools.
-
Use real scenarios from your environment: privilege sprawl, misconfiguration drift, exposed storage, risky SaaS OAuth access, API abuse, and noisy alerts. Score vendors on prioritization quality, remediation workflows, identity context, integrations, and reporting. Ask vendors to prove false-positive reduction, not just detection.
-
At minimum: cloud/platform engineering, IAM, SOC, incident response, compliance/audit, and application owners. Cloud security tooling fails when security buys it alone and expects engineering teams to adopt remediation workflows later.
-
Yes—especially for 24/7 monitoring, detection tuning, and incident escalation. But validate scope carefully: what they monitor, what they remediate, response SLAs, escalation paths, and which tools they support. A managed service can accelerate outcomes, but only if ownership boundaries are explicit.