Best YouTube Channels for Cybersecurity Learning & Updates
Cybersecurity YouTube can either sharpen your skills fast or waste months in entertainment disguised as education. The difference is selection and sequence: choosing creators who teach real workflows, then watching with a plan that maps to the way attacks and defenses actually work. This guide gives you a ranked, high-signal directory plus a learning blueprint so you build job-ready capability—not random trivia.
If you’re battling “too many tabs, no structure,” weak fundamentals, or nonstop news noise, this is built to fix that—with a stack-aligned approach grounded in security frameworks, SIEM fundamentals, incident response execution, and vulnerability assessment strategy.
1: How to Judge a Cybersecurity YouTube Channel Like a Pro (Not a Fan)
Most learners pick channels by charisma. Professionals pick channels by signal density and transferability—how quickly the content turns into skills you can use in labs, tickets, and real incidents. The fastest path is to treat YouTube as a “guided apprenticeship” that supports your core roadmap in future cybersecurity skills and your role direction (SOC, pentest, cloud, GRC, DFIR, etc.) from job market trend predictions.
The 7 criteria that separate “good content” from “career content”
Workflow clarity: Do they show end-to-end steps (triage → investigation → containment → reporting) that match incident response plans and evidence expectations in security audits?
Tool realism: Do they use tools professionals actually deploy (or explain alternatives) and connect telemetry into SIEM operations, EDR concepts, and IDS deployment?
Threat model maturity: Do they map attacks to modern realities like AI-powered cyberattacks, ransomware evolution, and deepfake-driven threats?
Security fundamentals: Great channels don’t skip core building blocks like firewall technologies, VPN strengths and limits, PKI components, and encryption standards.
Repeatable practice: Do they give lab prompts you can repeat weekly using penetration testing tools, vulnerability scanners, and realistic ticket-style investigation?
Bias control: Some creators are entertainment-first. That’s fine—unless you confuse it for training. Your learning stack must still connect to cyber threat intelligence and practical defenses like DLP strategies.
Update quality: “Updates” must be contextual: what changed, why it matters, what to patch or tune, and how it affects compliance trends and privacy regulation direction.
The biggest mistake learners make
They binge random creators, learn fragments, then feel “busy” but remain unhirable. Fix that by picking channels that map to specific skill lanes—SOC detection, pentest execution, cloud security engineering, DFIR, GRC/audit—then reinforcing each lane with ACSMI resources like security audits, framework alignment, and ransomware response.
2: Ranked Directory — The Best YouTube Channels by Learning Outcome (Not Hype)
Instead of a single “top list,” use this ranking based on what you need right now: hands-on labs, blue-team detection, malware/DFIR, networking fundamentals, or professional webcasts. Many widely recommended cybersecurity channels include creators like The Cyber Mentor, John Hammond, NetworkChuck, LiveOverflow, Hak5, David Bombal, IppSec, and SANS Institute.
Tier 1 (Best Overall): Hands-on creators who teach transferable workflows
These are channels you can build weekly practice around because the content translates into real operational competence: reconnaissance discipline, exploitation logic, defensive triage, artifact thinking, and structured analysis.
To make this Tier 1 content career-grade, pair it with ACSMI fundamentals: vulnerability assessment methods, SIEM foundations, incident response plans, CTI collection/analysis, and encryption standards.
How to watch Tier 1 properly (so it sticks):
Watch once for the “story” of the attack/defense.
Watch again and pause at each decision point: write what you’d do and why.
Rebuild the workflow using your own lab notes, then validate with a second source like penetration testing tools comparisons and vulnerability scanners directory.
Tier 2 (Strong Supporting): Channels that accelerate fundamentals, cloud, and blue-team depth
Tier 2 channels are powerful when they reinforce your skills stack and reduce blind spots—especially around network visibility, cloud identity mistakes, logging discipline, and practical detection engineering. This matters because modern threats increasingly mix attack lanes described in AI-powered cyberattacks, future endpoint security trends, and zero trust evolution.
Use Tier 2 channels to close gaps around:
Network controls: firewall types/configurations, IDS deployment, DoS mitigation, and botnet disruption methods.
Remote access realities: VPN benefits and limitations plus PKI components.
Data protection: DLP strategies and tools with privacy alignment via global privacy regulation trends.
Tier 3 (Use Carefully): News/commentary and vendor content
These can be valuable for awareness but dangerous for skill-building if they become your primary input. The rule is simple: every “update” you consume should trigger one of these actions:
A control review mapped to frameworks (NIST/ISO/COBIT)
A logging/detection update mapped to SIEM workflows
A response rehearsal mapped to incident response execution
A resilience check mapped to ransomware response and recovery
If a channel doesn’t reliably produce “actions you can take,” keep it secondary.
3: A 30-Day YouTube Learning Plan That Builds Real Cybersecurity Competence
The most effective learners don’t watch “more.” They watch with a weekly output. This plan converts YouTube time into artifacts you can show in interviews: writeups, mini playbooks, detection notes, lab reports, and portfolio projects.
Week 1: Foundations that prevent future confusion
Goal: build the mental model that makes every later lesson easier.
Map identity and permissions using DAC/MAC/RBAC and framework alignment.
Learn why encryption decisions matter using AES/RSA and beyond and trust systems with PKI components and applications.
Build your first “security operations glossary” around SIEM concepts and IDS deployment.
Deliverable: a 1-page “Security Fundamentals Map” you can update monthly.
Week 2: Detection and triage (SOC-ready)
Goal: learn how to think when alerts hit.
Pick one incident type and build a triage checklist using incident response planning and security audits evidence expectations.
Learn how ransomware behaves and how teams respond using ransomware detection/response/recovery plus forecasting context from ransomware evolution by 2027.
Add threat context using CTI collection and analysis.
Deliverable: an “Incident Triage Playbook v1” (1–2 pages).
Week 3: Offensive learning to improve defense
Goal: understand attacker workflows so your defenses stop being generic.
Do one lab per week using a channel that walks through methodology, then cross-check with penetration testing tools comparisons.
Validate the gaps you exploited using vulnerability assessment techniques and vulnerability scanners directory.
Connect network controls to your exploit chain using firewall technologies and resiliency topics like DoS prevention.
Deliverable: one writeup: “What I exploited, what would have stopped me, what to monitor.”
Week 4: Specialize (choose one lane)
Goal: stop being “general interest,” start being employable.
Pick one lane and build a mini portfolio:
Lane A: Cloud security
Pair YouTube cloud lessons with cloud security career guidance and future trend context via future cloud security trends.
Lane B: GRC / audit
Translate videos into evidence: align to security audits best practices, compliance direction via future compliance trends, and privacy evolution via privacy regulation trends.
Lane C: DFIR / malware
Build repeatable analysis habits and map response steps into incident response execution and structured reporting supported by CTI analysis.
Deliverable: 3 artifacts: one checklist, one writeup, one detection idea.
Choose the biggest pain point so you can build a channel stack that fixes it.
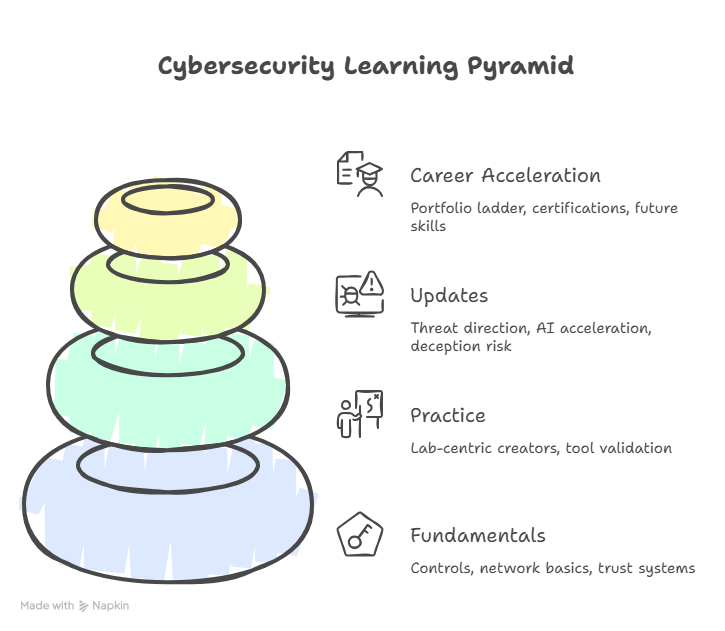
4: The “Channel Stack” Method — Build a Personal Cyber Curriculum That Doesn’t Fail
A professional YouTube learning system uses a stack, not a single favorite creator. Your stack should mirror a real security program:
Stack Layer 1: Fundamentals (prevents future gaps)
Anchor your fundamentals with:
Controls and governance via NIST/ISO/COBIT frameworks and security audits
Network basics via firewall technologies, IDS deployment, and VPN security tradeoffs
Trust systems via PKI and encryption standards
Why this matters: without fundamentals, you’ll misinterpret “advanced” content and adopt unsafe shortcuts.
Stack Layer 2: Practice (turns knowledge into skill)
Use lab-centric creators and reinforce with:
Tool validation via penetration testing tools
Exposure prioritization via vulnerability assessment and top vulnerability scanners
Defensive context via SIEM and incident response
Rule: every video you watch produces a note, a checklist item, or a lab replication.
Stack Layer 3: Updates (keeps you current without panic)
Choose channels that help you translate change into action. The cybersecurity “update stream” is huge; your job is to filter for what affects controls and skills:
Threat direction via top threats by 2030
AI acceleration via AI-powered attack predictions and tool evolution via AI-driven cybersecurity innovations
Identity/media deception risk via deepfake threat prep
Operational resilience via ransomware response/recovery
Rule: convert each update into one control change, one detection idea, or one training task.
Stack Layer 4: Career acceleration (turn learning into proof)
Most learners never translate content into “proof.” Fix that with a portfolio ladder:
One detection writeup tied to SIEM concepts
One incident timeline writeup tied to IR planning
One security assessment writeup tied to audit best practices
One scanning/prioritization report tied to vulnerability assessment
Then align your next steps with future cybersecurity certifications employers value and career direction (SOC, cloud, GRC, pentest) via future skills.
5: How to Use YouTube for “Updates” Without Becoming a Doom-Scroller
Security updates are useful only when they improve decisions. Otherwise, they generate anxiety and distract you from core competence. Here’s how professionals consume updates.
Step 1: Put updates inside a control framework
Whenever a channel covers a breach, vulnerability, or threat trend, force it into a structured lens:
What control failed?
What detection would have caught it earlier?
What evidence would auditors ask for?
Then map the answers to:
Step 2: Build a weekly “Update → Action” ritual
Each week, do the following:
Watch 1 update video.
Write 3 bullet takeaways.
Convert them into one action: patch check, logging improvement, detection idea, playbook update, training drill.
This keeps you aligned with macro trends like future cybersecurity compliance, privacy regulation evolution, and attack acceleration from AI-powered threats.
Step 3: Use “update channels” as pointers—not teachers
Update-first creators are best as signal beacons. When something matters, you follow up with deeper sources:
For detection and correlation: next-gen SIEM direction
For ransomware: ransomware response and recovery
For network disruption: DoS prevention and botnet disruption
For cloud: future cloud security trends
Step 4: Recognize channel patterns that waste your time
Avoid channels that:
Promote “secret methods” without fundamentals like encryption standards and PKI trust basics
Teach only tools, not decisions (especially when ignoring vulnerability assessment methods)
Skip defensive outcomes like SIEM integration and incident response
(Your goal is skill compounding, not content consumption.)
6: FAQs — Best YouTube Channels for Cybersecurity Learning & Updates
-
Many lists consistently recommend channels such as The Cyber Mentor, John Hammond, NetworkChuck, LiveOverflow, Hak5, David Bombal, and SANS Institute for a mix of hands-on learning and professional webcasts. Pair foundational watching with ACSMI guides on frameworks, SIEM basics, firewall fundamentals, and IDS deployment.
-
Pick channels that teach triage logic, evidence handling, and detection thinking. Then reinforce with ACSMI resources like incident response plans, CTI collection/analysis, and SIEM foundations. Add weekly practice using vulnerability assessment techniques so you learn how exposure becomes incidents.
-
They’re worth it if you convert them into actions: one control update, one detection idea, one playbook improvement. This is especially valuable for staying aligned with future threats and modern changes like AI-powered attacks and zero trust evolution.
-
Use the rule: every offensive video must be paired with one defensive concept. For example, match a lab with firewall design, IDS deployment, SIEM correlation, and IR execution. Add core trust understanding via PKI and encryption standards.
-
Use a weekly cadence: one update video → three takeaways → one action. Tie actions to compliance trends, privacy changes, and high-impact threat areas like ransomware response and DoS mitigation.
-
Training-organization channels (e.g., SANS Institute webcasts) are often used as structured reinforcement rather than entertainment-based learning. For best results, pair them with ACSMI study anchors like security audits, framework alignment, and operational depth via SIEM and incident response.
-
Build a portfolio ladder:
One detection writeup tied to SIEM fundamentals
One incident timeline tied to IR planning
One audit evidence checklist tied to security audits
One exposure report tied to vulnerability assessment techniques
Then align your growth with future skills and future certifications employers value.