Career Roadmap: Security Analyst to Cybersecurity Engineer (Expert Path)
Most people stuck in a security analyst role are not blocked by effort. They are blocked by translation. They know how to monitor alerts, investigate suspicious activity, escalate incidents, and work inside defined playbooks, but they struggle to convert that operational experience into engineering credibility. That gap is where careers stall, compensation flattens, and talented professionals start wondering why years of hands-on security work still are not unlocking better roles.
The move from analyst to cybersecurity engineer is absolutely achievable, but only if you stop treating it like a title jump and start treating it like a capability rebuild. This roadmap breaks down the exact shifts in thinking, skills, projects, technical depth, and career positioning that turn an alert-driven practitioner into a systems-minded security engineer employers actually trust.
1. What really changes when you move from security analyst to cybersecurity engineer
A security analyst is usually measured on detection quality, investigation discipline, escalation judgment, documentation, and response speed. A cybersecurity engineer is measured on control design, implementation quality, architecture decisions, tooling reliability, automation depth, resilience, and the ability to reduce risk before the alert ever fires. That difference sounds simple, but it changes everything about how you build your career.
Analysts live closer to symptoms. Engineers live closer to root causes. Analysts ask whether a suspicious event is malicious, how far it spread, and what the immediate containment path looks like. Engineers ask why the environment allowed it, which control failed silently, how to redesign the detection logic, where identity boundaries were too weak, and which system changes will prevent the same class of incident from recurring. That is why professionals who start with a strong foundation in how to become a SOC analyst, then deepen into career path from SOC analyst to SOC manager, often discover that engineering progression requires a different kind of technical ownership.
The painful part is that many analysts assume experience alone will eventually earn them the engineer title. In reality, employers do not promote on time served. They promote on evidence that you can build, tune, test, document, and improve controls. If your résumé still sounds like pure alert handling, triage, and ticket closure, hiring managers will keep reading you as operations support rather than engineering talent. This is where studying future skills for cybersecurity professionals by 2030, understanding predicting demand for specialized cybersecurity roles, and tracking cybersecurity job market trends becomes strategically useful.
The engineering path also forces a mindset shift from “I can work the tool” to “I understand the system behind the tool.” It is not enough to know how to operate a SIEM dashboard. You need to understand log sources, parser quality, rule tuning, ingestion tradeoffs, detection logic design, false-positive economics, alert severity modeling, and incident workflow dependencies. It is not enough to know how to review firewall alerts. You need to understand segmentation goals, rule architecture, exposure reduction, exception handling, and change control quality. Those deeper muscles are what separate someone who uses security infrastructure from someone who can engineer it.
Another difference is accountability. Analysts often escalate. Engineers are more often expected to decide. When identity policy changes create access risk, when telemetry coverage is incomplete, when a cloud deployment expands the attack surface, or when a detection rule breaks production workflows, engineering roles require judgment under uncertainty. That is why analysts who want to make this jump should study not only tactical topics like security information and event management, intrusion detection systems functionality and deployment, and vulnerability assessment techniques and tools, but also broader control logic through cybersecurity frameworks like NIST, ISO, and COBIT.
The core truth is this: the road from analyst to engineer is not about abandoning investigations. It is about using investigation experience to design stronger systems. If you know what attackers abuse, what analysts miss at 2 a.m., what alerts create fatigue, and what evidence investigators actually need, you already hold valuable engineering insight. The mistake is leaving that insight trapped inside operational work instead of converting it into architecture, automation, and control improvement.
| Career Stage | What You Usually Handle | What You Must Add to Advance | What Creates Promotion Leverage |
|---|---|---|---|
| 1. Junior security analyst | Alert review, escalation, ticket hygiene | Basic networking, log analysis, incident documentation | Consistency and reliable triage discipline |
| 2. Security analyst | Investigations, case handling, IOC review | Root-cause thinking and better detection context | Finding what others miss without over-escalating |
| 3. Senior analyst | Complex incidents, mentoring, tuning feedback | Rule logic, log-source depth, process improvement | Operational credibility plus pattern recognition |
| 4. Detection-focused analyst | Use-case refinement, false-positive reduction | Query writing, data normalization, tuning strategy | Measurable alert quality improvements |
| 5. Incident response analyst | Containment support, evidence review, coordination | Host artifacts, timeline reconstruction, playbook maturity | Handling pressure without losing rigor |
| 6. Threat hunting analyst | Hypothesis-driven hunts, anomaly discovery | Behavioral analytics, scripting, ATT&CK mapping | Proving proactive security value |
| 7. SIEM power user | Advanced searches and dashboard use | Parser awareness, ingestion tradeoffs, correlation logic | Moving from user to builder mindset |
| 8. Security tooling contributor | Minor config changes and rule suggestions | Change control, testing discipline, rollback planning | Low-risk technical ownership |
| 9. Endpoint security specialist | EDR investigations and response guidance | Policy design, exclusion strategy, deployment nuance | Reducing friction while improving protection |
| 10. IAM-aware analyst | Account misuse review and access anomalies | Role design, privilege boundaries, authentication flows | Identity fluency beyond ticket handling |
| 11. Network-aware analyst | Traffic review, firewall alerts, suspicious flows | Segmentation logic, ACL structure, exposure mapping | Understanding why the path was open |
| 12. Cloud-aware analyst | Cloud alerts, console reviews, IAM flags | Policy drift, service roles, storage exposure, workload context | Modern environment relevance |
| 13. Vulnerability operations analyst | Finding review and remediation tracking | Risk prioritization, exploit context, asset criticality | Separating noise from real exposure |
| 14. Scripting-capable analyst | Small automation and data cleanup tasks | Python, PowerShell, APIs, repeatable workflows | Saving time through automation |
| 15. Detection engineer trainee | Building and testing detections | Data engineering basics, testing datasets, attack simulation | Controls that perform in reality |
| 16. Security platform contributor | Config support across tools | Integration thinking, API connections, architecture awareness | Making tools work together |
| 17. Security automation builder | Workflow orchestration, case enrichment | SOAR logic, guardrails, exception handling | Speed without unsafe automation |
| 18. Security engineer I | Control implementation and tuning | Architecture literacy, documentation, design tradeoffs | Reliable delivery of security improvements |
| 19. Security engineer II | Cross-tool implementation and design ownership | Deeper system integration and risk modeling | Owning outcomes, not just tasks |
| 20. Cloud security engineer | IAM, workload controls, cloud logging, posture hardening | Multi-cloud patterns, infrastructure-as-code, policy testing | Modern engineering depth |
| 21. Detection engineer | Behavioral analytics, data pipelines, signal quality | Threat-informed engineering and metrics | Reducing alert fatigue while raising detection quality |
| 22. Security infrastructure engineer | Security tooling architecture and service reliability | Scale design, resilience, lifecycle management | Engineering credibility at platform level |
| 23. Application security engineer | Secure SDLC, tooling, remediation guidance | Developer workflows, CI/CD, code risk awareness | Shifting security left without blocking delivery |
| 24. Security architect-track engineer | Design guidance and control standardization | Reference architectures, business alignment, tradeoff communication | Seeing the whole system clearly |
| 25. Senior cybersecurity engineer | Multi-domain security engineering leadership | Mentorship, prioritization, reliability under scale | Repeated delivery of durable risk reduction |
| 26. Expert engineering path | Strategic control design across environment layers | Architecture influence, business translation, future-state planning | Trusted technical authority with implementation depth |
2. The skill stack you need before employers will trust you with engineering work
The jump does not happen when you collect random tools. It happens when you build a stack of technical depth that signals design capability. Security engineering is where infrastructure, software, identity, detection, and operational resilience start converging. That means your learning path has to stop being scattered. You do not need to know everything, but you do need clear strength in the layers engineers touch every week.
Start with network fluency. Engineers do not panic when traffic patterns get messy, when ports open for business reasons, or when segmentation debates get political. They understand how connectivity decisions reshape risk. If your network knowledge is still shallow, strengthen it through practical study of firewall technologies, types, and configurations, deeper review of virtual private networks security benefits and limitations, and constant exposure to denial-of-service attack prevention and mitigation. Network awareness will stop you from sounding like someone who only sees logs after the fact.
Then build identity depth. A surprising number of analyst résumés still present identity as a help-desk-adjacent topic rather than a core security layer. That is a career mistake. Engineering roles increasingly revolve around access design, role hygiene, trust boundaries, federation, service account risk, key handling, and privilege controls. You should know the logic behind access control models like DAC, MAC, and RBAC, understand where public key infrastructure components and applications fit into enterprise trust, and be comfortable discussing why identity misuse breaks both cloud and on-prem environments faster than many teams realize.
You also need hands-on familiarity with how detection systems are actually built. That means getting beyond “I used Splunk” or “I reviewed SIEM alerts.” Employers want evidence that you understand signal logic, not just dashboard usage. Learn rule writing, suppression logic, baselining, enrichment workflows, parser limitations, and the business cost of poor tuning. This is where strong command of SIEM overview and architecture, better awareness of intrusion detection systems deployment, and a grounded approach to cyber threat intelligence collection and analysis starts converting you from consumer to builder.
Cloud capability is now non-negotiable for most serious engineering tracks. Even if the role is not titled cloud security engineer, modern employers expect you to understand cloud IAM, storage exposure, service roles, telemetry, workload risk, and configuration drift. If you want to make yourself harder to ignore, build this area aggressively through how to become a cloud security engineer, related forecasting in future of cloud security predictive analysis, and supporting awareness from AI-powered cyberattacks future threats and defenses.
Finally, learn to automate. Security engineering without scripting creates a ceiling. You do not need to become a full software engineer, but you do need to manipulate APIs, handle structured data, automate repetitive tasks, enrich alerts, validate configurations, and prove you can save team time safely. Analysts who remain manual for too long often get trapped being “excellent operators” while more technical peers pass them. That is why the smartest upskilling is not just certification chasing. It is project-building that shows you can make systems cleaner, faster, and more reliable.
3. Step-by-step roadmap from analyst duties to engineering credibility
The best career roadmaps are not motivational. They are practical. If you want the expert path, your move should happen in stages that each create visible proof. A hiring manager does not need your intention. They need artifacts, language, and outcomes that scream engineering readiness.
Stage 1: Master the analyst role so thoroughly that patterns become obvious to you.
You cannot engineer stronger controls if you still struggle with investigation basics. Get excellent at triage, case notes, escalation quality, false-positive recognition, and evidence handling. Strengthen this foundation through incident response plan development and execution, ransomware detection, response, and recovery, and even niche topics like botnets structure and disruption methods because they sharpen your adversary pattern recognition.
Stage 2: Start documenting recurring control failures.
This is where many analysts miss a golden opportunity. Every repeated alert category, repeated misconfiguration, repeated access issue, repeated endpoint gap, or repeated logging weakness is an engineering clue. Build a running list. What breaks repeatedly? What detection logic is weak? What logs are missing? Which tickets should not exist if controls were better? That list becomes your future engineering portfolio.
Stage 3: Contribute to tuning, not just escalations.
Volunteer for detection refinement, whitelist cleanup, alert threshold suggestions, dashboard improvement, or automation ideas. Even small changes matter because they prove you are thinking upstream. This becomes far stronger when paired with practical study of vulnerability assessment techniques and tools, data loss prevention strategies and tools, and encryption standards such as AES, RSA, and beyond.
Quick Poll: What Is Actually Blocking Your Move from Analyst to Engineer?
Pick the pain point that hurts most, because the right roadmap depends on the bottleneck you have not solved yet.
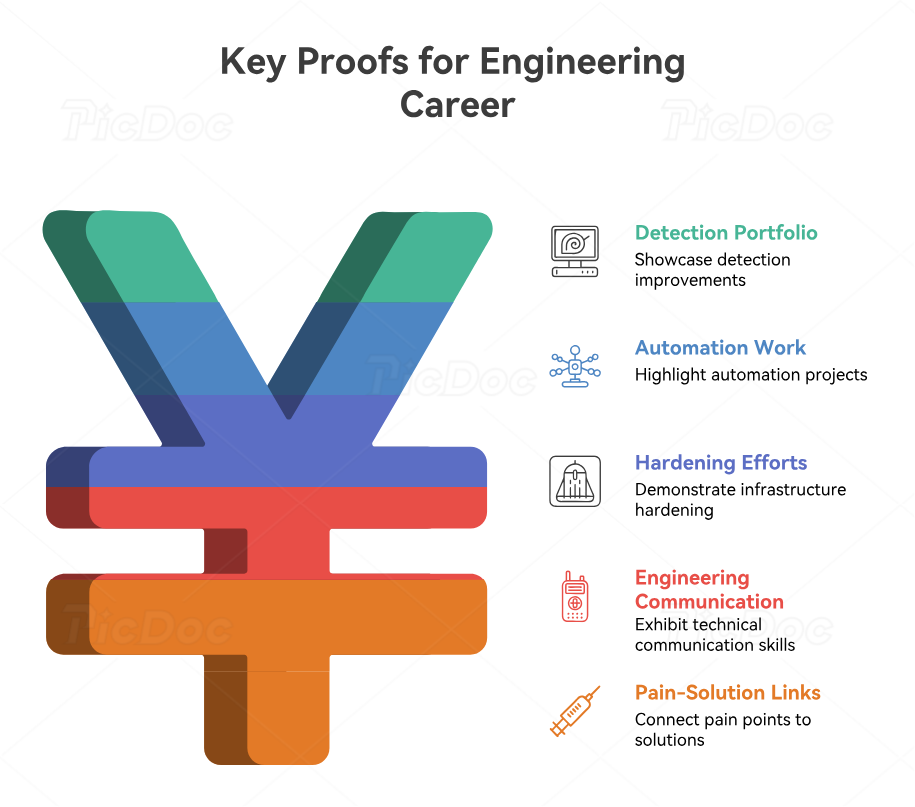
4. The projects, proof, and portfolio signals that make employers take you seriously
Career progression into engineering is won through proof, not aspiration. The strongest candidates show what they improved, built, tuned, automated, hardened, or redesigned. They do not hide behind vague lines like “worked closely with engineering teams.” They show impact. That is what separates someone who hopes to be trained from someone who already behaves like an engineer.
One excellent proof signal is a detection improvement portfolio. This can include examples of noisy alert types you reduced, logic changes you proposed, enrichment steps you automated, suspicious behaviors you mapped better, or dashboards you made more actionable. Even internal work can be sanitized into résumé-ready stories. Pair that experience with conceptual depth from next-gen SIEM trends to watch, practical grounding in security audits processes and best practices, and broader awareness from AI-driven cybersecurity tools top innovations.
A second strong signal is automation. Did you build a Python script that enriches indicators, normalize case data, compare logs, validate exposure, or reduce repetitive analyst work? Did you write PowerShell to support endpoint investigations or policy checks? Did you connect APIs between tools to shorten response time? These are exactly the kinds of things that tell employers you can move from human effort to engineered efficiency. They also align with larger workforce trends discussed in automation and the future cybersecurity workforce.
A third signal is infrastructure or cloud hardening work. Maybe you helped review IAM policies, validate cloud storage exposure, improve endpoint policy deployment, support segmentation, or test backup integrity. Even if you were not the final approver, being able to explain the risk, the control gap, the implementation logic, and the outcome makes your profile more engineering-shaped. That becomes stronger when you connect it naturally to predicting future cybersecurity audit practices, future of cybersecurity compliance, and technical depth from best cloud security tools directory.
A fourth signal is communication at engineering level. Can you write a design memo? Can you explain a detection gap to leadership without drowning them in jargon? Can you defend a security change that creates short-term friction but meaningful long-term resilience? Many technically decent candidates lose opportunities because they still communicate like ticket responders instead of control owners. Employers trust engineers who can explain tradeoffs, not just execute tasks.
The most overlooked portfolio signal is your ability to connect pain points to solutions. If analysts are drowning in noise, can you explain the tuning path? If cloud permissions are drifting, can you describe the governance and technical fix? If incident response keeps suffering from weak evidence, can you show how telemetry quality should change? Those bridges between operational pain and engineered outcome are where real hiring leverage lives.
5. Certifications, specialization paths, and mistakes that slow advancement
Certifications can help, but only when they reinforce a real direction. Too many analysts start stacking credentials without answering the harder question: what kind of engineer are you becoming? Security engineering is not one lane. It branches into cloud, detection, infrastructure, AppSec, identity, platform, and resilience-focused paths. Random certification accumulation does not solve that ambiguity. It often makes it worse.
If you want a detection-heavy path, focus on rule logic, data pipelines, attack simulation, query languages, SIEM architecture, and adversary behavior. If you want cloud security engineering, go hard on IAM, cloud telemetry, workload security, policy-as-code, secrets handling, and deployment pipelines. If you want infrastructure engineering, deepen your command of segmentation, endpoint controls, hardening, identity, and resilient architecture. If you want an offensive-leaning engineering track, study step-by-step guide to becoming a certified ethical hacker, career path from junior penetration tester to senior security consultant, and eventually more specialized routes like detailed roadmap to IoT security specialist careers.
The best certifications are the ones that help employers trust your judgment faster. Entry-level credentials may help you start, but expert-path progression comes from showing you can use knowledge inside real systems. That is why career-aligned reading matters too. Professionals moving toward leadership or specialist depth should also explore guide to a career as a cybersecurity auditor, how to become a cybersecurity manager, and even content on career roadmap to cybersecurity compliance officer, because engineering influence rises when you understand how controls are evaluated across the business.
Now the mistakes. The first is staying too long in passive analyst mode. If all your growth depends on somebody inviting you into technical work, your timeline will be slow. The second is hiding behind tools. “Used Splunk, Sentinel, CrowdStrike, Tenable” is not a compelling engineering story. The third is ignoring code and automation. The fourth is learning pieces without learning systems. The fifth is failing to update your résumé and interview stories to reflect engineering-shaped work you have already done.
The final mistake is chasing title over substance. Some people grab an “engineer” title in environments where they still do mostly reactive operations. That may help in the short term, but it creates a painful ceiling later when stronger employers test for genuine design depth. The expert path is slower than the shortcut path, but it compounds better. Real capability survives tougher interviews, more complex environments, and bigger opportunities.
6. FAQs
-
It depends on how quickly you add engineering proof, not just years worked. For many professionals, the jump becomes realistic once they can show tuning, automation, infrastructure understanding, and control improvement rather than only investigation work. A focused path can compress the timeline significantly.
-
No, but you do need technical comfort beyond tool clicking. Scripting, API usage, automation logic, and structured troubleshooting matter a lot. You do not need to be a full-time software engineer, but you do need enough coding ability to improve workflows and interact with systems intelligently.
-
You must stop thinking only in terms of alerts and start thinking in terms of system design. Engineers ask why a control failed, how to redesign it, how to validate it, and how to reduce repeated pain at scale. That shift is what makes your experience promotable.
-
The best path depends on the work that energizes you and the technical environment around you. Detection is strong for analysts who love signal logic and investigations. Cloud is excellent for those who enjoy modern infrastructure and identity complexity. Infrastructure suits people who like control design and reliability. AppSec fits those who enjoy secure development and software risk.
-
Not reliably. Certifications can strengthen credibility, but employers still want proof that you can implement, tune, automate, document, and improve controls. A credential without projects or engineering-shaped experience rarely carries enough weight on its own.
-
Focus on what you improved, built, tuned, automated, or hardened. Mention alert-quality improvements, policy changes, scripts, integrations, cloud reviews, detection logic, infrastructure changes, and measurable outcomes. Write like someone who changed systems, not like someone who only processed tickets.