How to Become a Cybersecurity Program Manager: Expert Career Guide
Cybersecurity program management is where technical credibility meets execution discipline. It is the career path for professionals who can turn scattered security activity into coordinated outcomes across people, budgets, controls, timelines, and executive priorities. Many candidates misunderstand the role and assume it is a softer version of security leadership. It is harder than that. A strong program manager must understand how threats, controls, stakeholders, governance, delivery risk, and business pressure collide in the real world.
The path into this role is not random. It usually grows out of security operations, governance, risk, engineering coordination, compliance work, consulting, or technical project delivery. The goal is to become the person trusted to move security initiatives from intention to measurable execution.
1. Understand What a Cybersecurity Program Manager Actually Owns
A cybersecurity program manager does not simply “keep projects on track.” That description is too weak for what the role actually demands. A real cybersecurity program manager coordinates multiple related security initiatives, aligns them with business priorities, manages dependencies, handles stakeholder friction, tracks risk, translates technical work into executive decisions, and makes sure security investments produce outcomes instead of slide decks. In practice, that can mean overseeing identity modernization, cloud security initiatives, audit remediation, third-party risk programs, incident readiness work, awareness rollouts, or enterprise control uplift across several teams at once.
This is why the role sits closer to business execution leadership than to ordinary task administration. Someone in this position needs enough technical understanding to ask the right questions, enough governance awareness to manage compliance pressure, and enough delivery discipline to keep complex work moving when priorities shift. Reading ACSMI’s guides on how to become a cybersecurity manager, career growth toward director-level cybersecurity leadership, the pathway to chief information security officer, and the guide to a cybersecurity compliance officer career helps clarify that this is a coordination-heavy leadership path with serious operational weight.
The strongest program managers understand both security content and execution mechanics. They know what NIST adoption means for control planning, how cybersecurity compliance trends affect timelines, how security audits create remediation pressure, and how technical decisions inside cloud security programs, endpoint security initiatives, SIEM modernization efforts, and incident response readiness change staffing, cost, and sequencing.
A lot of candidates are attracted to cybersecurity program management because they like leadership but do not want to remain buried in deep technical specialization forever. That can work. Still, this role punishes superficiality. A program manager who cannot understand the downstream implications of an audit gap, a delayed IAM rollout, or incomplete asset visibility becomes a meeting machine instead of an execution leader. The job is to connect moving parts, not narrate them.
2. Build the Right Foundation Before You Chase the Title
Most people do not start their careers as cybersecurity program managers. They grow into the role after spending time in technical operations, GRC, compliance, consulting, PMO environments, engineering coordination, or security analysis. That matters because the program manager must understand how security work behaves when it leaves a strategy document and enters actual teams. Someone who has seen detection fatigue in a SOC, audit scramble before an assessment, procurement delays in tool rollouts, or remediation slippage after a vulnerability review walks into the role with better instincts.
The foundation usually has four pillars. First, build enough security fluency to understand the major domains. That means being comfortable with endpoint security, SIEM and logging, cloud security trends, vulnerability assessment methods, and incident response effectiveness. Second, learn delivery discipline through projects, dependencies, timelines, and stakeholder management. Third, understand governance and regulation through content like GDPR and cybersecurity best practices, healthcare compliance realities, and the future of cybersecurity compliance. Fourth, develop the ability to write and present clearly under pressure.
A common trap appears here. Candidates sometimes think that generic project management experience automatically transfers. It helps, but cybersecurity programs carry their own friction. Tool implementation is not just tool implementation when the SOC must retune detections, engineering must rework integrations, audit teams must validate evidence, and leadership wants measurable risk reduction before quarter-end. That is why it is smart to study ACSMI’s guides on cybersecurity frameworks, security audits and best practices, the route to a cybersecurity auditor role, and the path to a cybersecurity compliance officer position. They build the kind of context that lets a program manager anticipate failure before the calendar exposes it.
There is another uncomfortable truth. Security programs often fail for human reasons long before they fail for technical reasons. Teams resist ownership. Executives want progress without tradeoffs. Control owners underestimate effort. Vendors overpromise. Requirements change late. A future cybersecurity program manager needs to become unusually good at diagnosing friction without dramatizing it.
3. Map the Career Path Stage by Stage
The earliest step into this career often begins with adjacent roles: security analyst, GRC analyst, project coordinator, PMO analyst, IT risk analyst, compliance specialist, junior consultant, or delivery-oriented security engineer. In these roles, the future program manager should focus less on title prestige and more on exposure to multi-team work. The valuable questions are practical. Did this role teach cross-functional coordination? Did it involve risk reporting? Did it expose regulatory or audit cycles? Did it require executive communication? Did it show how security tools and controls are actually rolled out?
From there, the next stage is usually some form of initiative ownership. That may mean leading a security awareness rollout, coordinating audit remediation, supporting an IAM modernization effort, managing a cloud security uplift, or helping with DLP strategy and tool deployment, PAM solution rollout, network security tooling evaluation, or application security tooling adoption. The point is not just to touch a project. The point is to learn how scope changes, implementation constraints, and success metrics behave across multiple stakeholders.
The next jump is into formal program responsibility. At this point, the candidate is no longer managing only one initiative or one timeline. They are managing a portfolio of related work with shared objectives, governance routines, risk logs, and executive visibility. Salary and demand data can also help frame where this role sits in the market. ACSMI’s reports on global cybersecurity salaries, entry-level to CISO salary progression, job market trends and salary predictions, and the cybersecurity workforce shortage are useful because they show why leaders who can orchestrate cybersecurity delivery are increasingly valuable.
Senior growth beyond this point can lead in several directions. Some program managers move toward director-level security operations or governance leadership. Some move into enterprise risk. Some become chiefs of staff to CISOs. Some move toward full cybersecurity manager or CISO-track leadership. The path depends on whether the person’s strongest muscle is execution, stakeholder influence, strategic planning, or business translation.
Quick Poll: What Result Are You Really Chasing With a Cybersecurity Program Management Career?
Pick the pressure point that matters most. The smartest career strategy changes when the target changes.
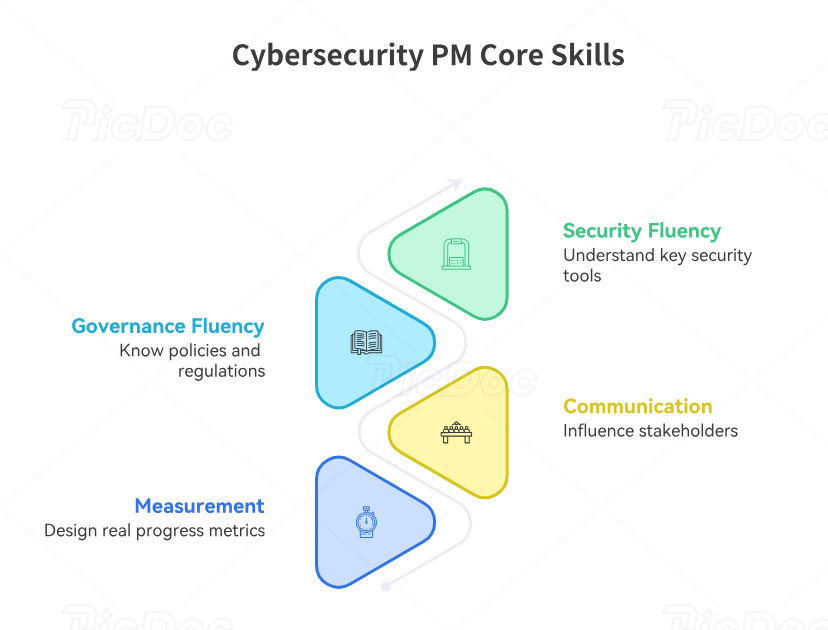
4. Build the Skills That Make Hiring Managers Trust You
A hiring team rarely worries that a cybersecurity program manager candidate is too organized. The real worry is whether the candidate can operate with enough security awareness and enough influence to keep programs from drifting into performative motion. That means the core skill stack is unusually blended.
First comes security domain fluency. The candidate should understand what major control categories do and how they impact delivery. That includes EDR tooling, SIEM platforms, cloud security tools, email security solutions, security awareness training platforms, and DLP software. A program manager does not need engineer-level depth in every one of these categories. They do need enough understanding to judge scope, risk, resource needs, and sequencing.
Second comes governance fluency. This role is constantly shaped by policies, audit findings, third-party expectations, and legal or regulatory constraints. That is why studying GDPR-related cybersecurity issues, privacy regulation trends, healthcare cybersecurity compliance, and the broader future of cybersecurity legislation for SMBs is strategically useful. Governance drives deadlines, evidence needs, ownership mapping, and executive urgency.
Third comes communication and influence. This is the part many technically strong candidates underestimate. The cybersecurity program manager spends a huge amount of time clarifying ambiguity, preventing silent drift, securing decisions, escalating intelligently, and turning complex work into language that different audiences can act on. Weak communicators become status-updaters. Strong communicators become decision-enablers. That difference affects promotion, compensation, and trust.
Fourth comes measurement. A mature program manager knows how to design progress indicators that expose reality instead of decorating it. A rollout with green dashboards but low adoption, poor evidence quality, unclosed risk acceptance, or constantly slipping dependencies is not healthy. It is just being presented attractively.
5. Certifications, Experience, and Positioning Strategy
Certifications can help in this path, but they should support the story rather than replace it. A cybersecurity program manager benefits from credentials that signal structured management ability, governance awareness, or broad security credibility. The exact combination depends on entry point. A technical candidate moving upward may need more visible program and leadership proof. A project manager moving into security may need more visible domain credibility. A compliance-oriented candidate may need broader execution proof.
That is why cert selection should be tied to the candidate’s gap. The ACSMI directory of top cybersecurity certifications, the report on the impact of certifications on career advancement, the analysis of salary growth across major certifications, and the article on future certifications employers may value most all reinforce the same lesson: sequence matters more than accumulation.
Experience positioning matters even more. Candidates often undersell relevant work because it did not carry the exact title they want now. That is a mistake. If you coordinated audit remediation across departments, managed control implementation, supported a cloud security program, drove third-party risk workflows, or led policy uplift tied to security frameworks, you already have relevant material. The key is to present it as program work. That means highlighting objective, scope, budget or resource constraints, governance rhythm, executive visibility, risk decisions, metrics, and outcomes.
The most persuasive positioning also uses adjacent market context. ACSMI’s reporting on remote versus on-site cybersecurity salaries, workforce demographics and inclusion, the global cybersecurity market outlook, and future cybersecurity job market predictions helps candidates understand how to frame themselves in a growing but demanding market. Organizations need people who can drive security execution across complexity. That is the real opening.
6. FAQs
-
They need meaningful technical fluency, not necessarily engineer-level depth in every domain. The role requires enough understanding to evaluate scope, ask sharp questions, manage risk, and translate decisions intelligently. Someone who cannot speak confidently about cloud security, SIEM environments, incident response readiness, and security frameworks will struggle to lead credible programs.
-
Yes, but the transition works best when the person builds visible security fluency quickly. Generic delivery skills help with planning, cadence, and stakeholder management. The missing piece is domain awareness. Studying free cybersecurity learning resources, following cybersecurity blogs and industry news sites, and reviewing the global directory of cybersecurity training providers can strengthen that transition.
-
Security operations, GRC, IT risk, audit, compliance, PMO, technical consulting, security engineering coordination, and enterprise transformation work are all common feeder paths. The strongest candidates usually have experience where security work crossed teams and required reporting, risk handling, and delivery pressure. ACSMI’s guides on cybersecurity manager careers, auditor pathways, and compliance officer growth all reflect that pattern.
-
They present themselves as coordinators instead of owners. Hiring teams want to see initiative design, dependency management, risk escalation, executive communication, and measurable outcomes. A résumé full of meetings, trackers, and support tasks does not inspire confidence. A résumé showing control rollout, audit closure, vendor implementation governance, and cross-functional execution does.
-
Certifications help, but they rarely close the deal alone. Hiring decisions in this role are shaped by evidence of execution. The strongest candidates pair certifications with initiative ownership, better reporting, and a clear story around how they handled risk, delays, resistance, and delivery outcomes. The ACSMI content on certification impact and salary growth tied to credentials is useful for choosing what actually adds leverage.
-
This role can lead toward senior program leadership, director of cybersecurity, governance leadership, enterprise risk leadership, chief of staff to the CISO, or eventually broader executive tracks. The next move depends on whether the person’s greatest strength is execution leadership, security strategy, or cross-functional influence. ACSMI’s pathways to director-level growth and CISO-track leadership are natural next reads.