Emerging Cybersecurity Threats in Cloud Environments: Original Data & Analysis (2026-2027)
Cloud risk is no longer defined by a single “misconfiguration problem.” In 2026-2027, the threat picture is becoming more layered: identity abuse is accelerating faster than perimeter compromise, cloud-native tooling is widening the blast radius of simple mistakes, and attackers are increasingly chaining software supply-chain weaknesses with weak detection logic. For security teams, the painful truth is that many cloud incidents now begin in places that look operationally normal until the damage is already underway.
This original analysis breaks down where the pressure is building, which threat patterns are becoming harder to contain, and what security leaders must prioritize when cloud exposure, alert fatigue, staffing limitations, and business speed are all colliding at once.
1. Why cloud threat exposure is getting harder to control in 2026-2027
The biggest mistake security teams still make is treating cloud risk as a visibility problem only. Visibility matters, but it does not solve decision latency, ownership confusion, privilege sprawl, weak identity hygiene, or alert overload. A company may have dashboards everywhere and still miss the attacker who quietly inherits access through stale permissions, abuses overpowered service accounts, or pivots through unmanaged workloads.
In our original 2026-2027 analysis model, the most dangerous cloud threats are not always the loudest. They are the threats that blend into normal operations: credential misuse that resembles legitimate automation, storage exposure hidden inside development workflows, API abuse that looks like expected service-to-service traffic, and infrastructure changes pushed through pipelines with insufficient review. This is why teams that understand cybersecurity frameworks such as NIST, ISO, and COBIT are better positioned than teams relying on disconnected tools alone.
Cloud complexity is also amplifying pain points that many organizations already feel but rarely articulate clearly. Security engineers are being asked to secure multi-cloud estates while supporting rapid deployments, shrinking tolerance for business friction, and severe hiring pressure. Leaders reading predicting cybersecurity job market trends: roles that will thrive by 2030 can see why this matters: demand is rising, but so is specialization. A generalist team can miss cloud-specific kill chains that a complete career guide to becoming a cloud security engineer would immediately recognize.
Another hard truth is that cloud attackers no longer need spectacular technical wizardry to cause serious damage. They need speed, access inheritance, weak controls around secrets, and organizations that still separate identity security from cloud security. That gap is especially dangerous when companies have weak incident response plan development and execution, immature SIEM visibility and event correlation, and incomplete cyber threat intelligence collection and analysis.
Below is an original 26-point advancement matrix showing where cloud threats are creating the most pressure, what business damage they most often trigger, and what defenders should prioritize first.
| Threat Pattern | Primary Entry Point | Most Likely Business Impact | Why It’s Rising in 2026-2027 |
|---|---|---|---|
| Stolen cloud console credentials | Phishing, infostealers, reused passwords | Tenant takeover, lateral movement | Identity remains easier to abuse than infrastructure |
| Session token hijacking | Browser compromise, token theft | MFA bypass, persistent access | Token-based trust is expanding across cloud apps |
| Overprivileged service accounts | Automation abuse | Stealthy privilege escalation | Machine identities are growing faster than controls |
| Exposed storage buckets | Misconfiguration | Data leakage, compliance failures | Rapid deployment still outruns review discipline |
| Public snapshots and images | Improper sharing settings | Credential and data exposure | Template reuse spreads the same mistakes widely |
| Secrets embedded in code repos | Developer workflow leakage | Unauthorized API access | Pipeline speed encourages unsafe shortcuts |
| CI/CD pipeline compromise | Build system abuse | Mass deployment of malicious changes | Pipelines increasingly control production trust |
| Container image poisoning | Registry compromise | Backdoored workloads | Reusable images amplify supply-chain exposure |
| Kubernetes RBAC abuse | Role misassignment | Cluster-wide takeover | Container orchestration remains operationally complex |
| Weak API gateway controls | Broken authentication | Data manipulation, service abuse | APIs are becoming the real cloud perimeter |
| Serverless function abuse | Event trigger exploitation | Ephemeral persistence, stealth execution | Short-lived compute complicates detection timing |
| Cross-account trust abuse | Federation misuse | Rapid expansion of attacker access | Enterprises depend on interconnected tenants |
| Identity provider compromise | Central auth weakness | Enterprise-wide account abuse | Single sign-on centralizes trust and risk |
| Shadow SaaS integrations | Unsanctioned app connections | Data exfiltration, poor governance | Business teams keep connecting tools independently |
| Cloud ransomware targeting backups | Privilege misuse | Recovery disruption, extortion leverage | Attackers now attack resilience before encryption |
| Log tampering | Admin-level access | Delayed detection, weak forensics | Attackers understand defenders rely on telemetry |
| Encryption key misuse | KMS abuse | Data decryption, trust breakdown | Key access is often broader than leaders assume |
| Privilege escalation via IAM drift | Policy sprawl | Unnoticed admin-equivalent power | Cloud permissions change faster than they are reviewed |
| Vulnerable third-party cloud apps | Vendor ecosystem exposure | Indirect tenant compromise | Organizations are outsourcing more functionality |
| Data lake overexposure | Misgoverned analytics access | Mass leakage of sensitive datasets | Cloud analytics estates are expanding rapidly |
| Insider misuse in cloud admin roles | Legitimate access abuse | Quiet sabotage or data theft | Admin power remains concentrated and under-reviewed |
| AI-assisted cloud reconnaissance | Automated discovery | Faster attacker mapping and targeting | AI lowers the cost of attack preparation |
| MFA fatigue against cloud access | Push bombing, social engineering | Credentialed account entry | Human approval flows remain exploitable under pressure |
| Hybrid-cloud policy inconsistency | Control gaps between environments | Blind spots, uneven protection | Security architecture often lags infrastructure growth |
| Exposed management ports | Poor segmentation | Remote compromise, admin abuse | Operational shortcuts still create internet exposure |
| Cloud compliance control bypass | Weak preventive guardrails | Audit failure, regulatory penalties | Teams optimize for release speed over evidence quality |
2. Original threat ranking: the 2026-2027 cloud risks security teams should fear most
Our original ranking places identity-centric abuse at the top, not because misconfiguration has disappeared, but because attackers increasingly prefer the path that lets them look legitimate. A breached account with broad permissions is more valuable than noisy exploitation. That is why teams investing only in firewall technologies and configurations while neglecting identity governance are building a false sense of maturity.
Tier 1: High-likelihood, high-damage threats
These are stolen credentials, token theft, overprivileged machine identities, backup-targeting ransomware, and CI/CD compromise. They combine easy execution paths with catastrophic downstream impact. If your team has inconsistent access control models such as DAC, MAC, and RBAC, weak public key infrastructure governance, and underdeveloped intrusion detection systems deployment, these threats become exponentially harder to stop.
Tier 2: Quiet but compounding threats
This tier includes shadow SaaS, exposed storage, policy drift, data lake overexposure, and third-party app weaknesses. These issues often survive because no one owns them cleanly. Security assumes cloud engineering is reviewing them. Cloud engineering assumes governance has already approved them. Governance assumes technical teams have implemented controls. This ownership fog is where attackers thrive, and it is exactly why strong security audits, processes, and best practices matter more than checkbox compliance.
Tier 3: Advanced operational pressure points
Here we place AI-assisted reconnaissance, serverless abuse, cross-account trust misuse, and cloud-native log tampering. These are the threats mature organizations still underestimate because they do not always create obvious early warnings. Security teams may collect logs, but if nobody is actively validating integrity, retention quality, and investigative usefulness, the telemetry becomes decorative. That is where better vulnerability assessment techniques and tools, sharper ransomware detection, response, and recovery planning, and more disciplined data loss prevention strategies and tools create real resilience.
The strategic pattern is simple but brutal: cloud threats are increasingly exploiting trust relationships, not just technical weaknesses. That means defenders must harden identities, privilege boundaries, secrets handling, automation pathways, and recovery dependencies. Teams that only focus on prevention without understanding detection quality will keep discovering breaches after the attacker has already moved laterally.
3. The real attack paths emerging inside cloud environments
The most dangerous cloud attack paths in 2026-2027 are chained paths. Attackers are no longer relying on one dramatic exploit when four smaller weaknesses can produce cleaner access with less noise. A leaked secret in a repository leads to API access. The API access reveals storage paths. The storage paths expose configuration files. The configuration files reveal role assumptions or downstream service identities. Suddenly what looked like a minor hygiene lapse becomes a multi-stage tenant compromise.
This is why basic security literacy is not enough anymore. Teams need specialists who understand cloud operating logic, identity flows, pipeline trust, and telemetry gaps. Anyone following future skills for cybersecurity professionals: essential competencies by 2030 can see the direction clearly: cloud security is demanding tighter overlap between architecture, detection, automation, governance, and adversary thinking.
One emerging problem is the abuse of “legitimate speed.” Businesses are pushing cloud releases faster, adopting more integrations, and expanding analytics footprints. That speed is strategically useful for the business, but it also gives attackers more moving parts to hide inside. The teams that will win are not the teams that try to say “no” to everything. They are the teams that enforce safer defaults, reduce privilege inheritance, and align guardrails with actual delivery workflows. This is also why predicting the future of zero trust security by 2030 remains highly relevant for cloud strategy.
Another attack path gaining relevance is attacker use of cloud-native administration functions after initial access. Once attackers obtain enough privileges, they do not need to behave like old-school intruders. They can create users, alter policies, suppress logging, snapshot data, or modify backup configurations using the same interfaces defenders use every day. That makes strong encryption standards knowledge, reliable virtual private network security understanding, and deeper next-gen SIEM awareness more operationally important than many organizations admit.
The hardest pain point here is not technology. It is confidence. Many organizations do not actually know whether they can detect privilege misuse early, prove which workloads touched sensitive data, or recover fast if cloud backups are tampered with. They assume capability because the tooling exists. That assumption is exactly what attackers are betting on.
Quick Poll: What Cloud Security Outcome Are You Really Chasing in 2026-2027?
Pick the pressure point that matters most, because your cloud defense priorities should match the business risk you cannot afford to misjudge.
4. Original data analysis: what our 2026-2027 cloud threat model suggests
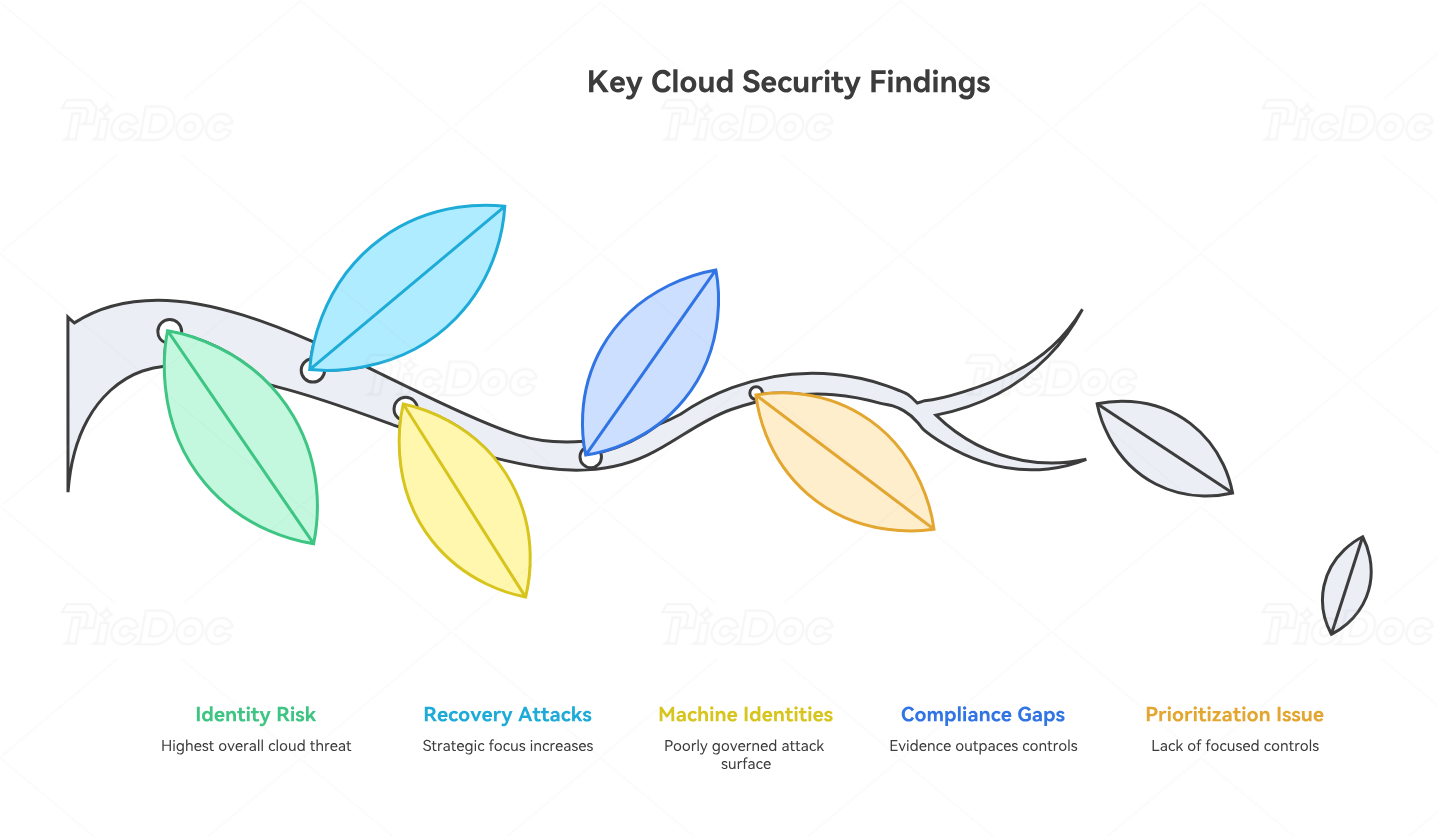
In our original analysis framework, we scored cloud threats across four dimensions: likelihood of occurrence, stealth potential, business disruption, and recovery complexity. Identity abuse ranked highest overall because it consistently scores well across every dimension. Misconfiguration remains common, but identity-led abuse often has the cleaner path to persistence and administrative leverage.
The second major finding is that recovery-targeting attacks are becoming more strategic. In older cloud security conversations, the spotlight was on prevention. In 2026-2027, prevention is still crucial, but resilience is becoming a differentiator. Attackers increasingly understand that destroying trust in recovery systems can create more leverage than merely encrypting workloads. Teams that have not pressure-tested backup separation, immutable recovery paths, and admin privilege boundaries are vulnerable to operational paralysis.
The third finding is that machine identities are becoming one of the least governed attack surfaces in the cloud. Human accounts receive training, MFA policy attention, and lifecycle management. Machine identities often receive broad permissions, poor rotation discipline, weak visibility, and minimal review. That gap is dangerous. Leaders exploring automation and the future cybersecurity workforce should pay attention here: as automation grows, machine identity risk grows with it.
The fourth finding is that cloud compliance evidence often looks stronger than the underlying control reality. Organizations may pass reviews while still struggling with logging blind spots, policy drift, inconsistent cross-account governance, and weak incident playbooks. That is why leaders should pair formal compliance work with operational depth from future cybersecurity compliance predictions, privacy regulation trend analysis, predicting future cybersecurity audit practices, and practical cloud security tool directories.
Most importantly, our model suggests that organizations will underperform not because they lack tools, but because they lack prioritization discipline. They will try to improve everything at once, spread teams too thin, and fail to concentrate on the few controls that meaningfully reduce blast radius: identity hardening, secrets control, logging integrity, privileged access review, backup protection, and cross-environment visibility.
5. What security teams should do now to reduce cloud threat exposure
The first priority is treating identity as the primary cloud control plane. Review human and machine privileges separately. Shrink standing permissions. Monitor for unusual role assumptions. Validate federated trust. Challenge every account that can alter logs, backups, keys, or IAM policy. Teams exploring best privileged access management solutions should not treat PAM as optional architecture anymore.
The second priority is tightening secrets and pipeline governance. Scan code, templates, images, and deployment systems aggressively. Require safer key handling. Review build chain trust. Segment pipeline privileges. Security teams that delay here are giving attackers a low-friction path into production. Supporting this with regular top application security tools reviews and stronger security awareness training platforms improves both technical and human control quality.
The third priority is protecting detection quality, not just collecting alerts. Verify log completeness. Watch for telemetry suppression. Improve correlation rules around privilege changes, storage access anomalies, token misuse, unusual geographic access, snapshot creation, and backup modifications. Teams that want long-term maturity should study both SIEM fundamentals and more forward-looking AI-driven cybersecurity tool predictions.
The fourth priority is building recovery confidence. Run cloud-focused tabletop exercises. Simulate admin compromise. Test tenant isolation assumptions. Prove that your backups cannot be silently tampered with by the same privilege groups that operate production. This is where maturity becomes visible: not in policy slides, but in how fast a team can contain, validate, restore, and communicate under pressure. Anyone moving toward leadership through the step-by-step pathway to become a CISO, the career roadmap from security manager to director of cybersecurity, or the roadmap to cybersecurity compliance officer should make cloud resilience a board-level conversation.
The fifth priority is matching talent development to real cloud threat patterns. Organizations cannot expect generic security knowledge to solve cloud-native problems. They need stronger specialization in detection engineering, cloud IAM, incident response, architecture review, and adversary simulation. That is why practical learning pathways such as how to become a SOC analyst, the path from SOC analyst to SOC manager, becoming a certified ethical hacker, and the career path from junior penetration tester to senior security consultant remain tightly connected to cloud defense outcomes.
6. FAQs
-
The biggest emerging threat is identity-led cloud compromise. That includes stolen credentials, token theft, federation abuse, and overprivileged machine identities. These threats are especially dangerous because attackers can look legitimate while moving through the environment, which delays containment and increases business damage.
-
Misconfigurations still matter because they often serve as accelerants. Public storage, exposed management paths, weak API controls, and badly scoped permissions create shortcuts that make identity abuse more valuable and more damaging. The real danger is the combination of weak identity controls and cloud configuration mistakes.
-
Not automatically, but they are usually harder to govern consistently. The real risk comes from policy inconsistency, fragmented telemetry, uneven identity controls, and ownership confusion across platforms. Multi-cloud becomes dangerous when security architecture grows slower than infrastructure adoption.
-
Start with identity hardening, privileged access review, secrets management, backup protection, and logging integrity. These controls reduce both breach likelihood and blast radius. Trying to improve dozens of lower-impact controls before fixing these core issues usually wastes time and preserves real exposure.
-
Look beyond alert volume. Measure whether the team can detect privilege escalation, token misuse, suspicious storage access, logging suppression, snapshot creation, backup manipulation, and unusual cross-account behavior quickly enough to contain them. Detection quality is proven during investigation speed and decision confidence, not dashboard aesthetics.
-
Cloud security engineering, detection engineering, SOC leadership, incident response, application security, and governance roles with real technical depth are especially aligned. Strong support paths also include security consulting, auditing, and compliance leadership when they are grounded in modern cloud operating realities rather than checklist-only oversight.