How to Transition from IT Support to Cybersecurity Analyst
IT support professionals are often far closer to cybersecurity analyst work than they realize. They already troubleshoot endpoints, investigate user behavior, manage access issues, read logs, handle misconfigurations, and see where real-world control failures happen. The problem is not usually lack of relevance. It is lack of positioning, missing security depth, and an unclear roadmap for turning operational IT experience into analyst credibility.
This guide shows how to make that transition intelligently. It focuses on the skills that actually transfer, the gaps that block hiring, the evidence employers trust, and the steps that convert “help desk” or “systems support” into a serious cybersecurity analyst trajectory.
1. Why IT support is one of the strongest starting points for a cybersecurity analyst career
Many aspiring analysts waste time believing they need a dramatic reinvention before cybersecurity employers will take them seriously. That belief slows them down. IT support already develops some of the most important muscles for analyst work: technical troubleshooting, system visibility, user communication, escalation discipline, access issue resolution, endpoint familiarity, ticket documentation, and pattern recognition. Those are not side skills. They are part of the operating foundation behind strong SOC analyst performance.
A cybersecurity analyst is rarely paid just to know abstract security theory. They are paid to interpret signals inside messy environments. They need to see what “normal” looks like on endpoints, accounts, applications, networks, and user behavior, then catch what does not fit. IT support professionals live around that mess every day. They understand how devices break, how users behave, how permissions drift, how bad configurations create noise, and how rushed fixes introduce risk. That practical exposure becomes extremely valuable when studying vulnerability assessment techniques and tools, learning intrusion detection systems functionality and deployment, building familiarity with SIEM operations, and understanding incident response plan development and execution.
The real advantage of IT support is that it forces contact with the environments security teams protect. Help desk staff see password resets, account lockouts, MFA failures, suspicious user complaints, broken VPN access, remote tool misuse, patch issues, misconfigured software, and endpoint anomalies. Desktop and systems support teams see asset sprawl, privilege problems, shadow IT behaviors, and visibility gaps. Those are not “lesser” experiences. They are raw material for threat detection and response when paired with deeper security reasoning.
This is also why strong IT support candidates often outperform purely theoretical applicants. A person who has solved real Active Directory issues, investigated device problems, worked inside ticket queues, and handled production-user pressure may be more valuable than someone who memorized acronyms but has never touched operational reality. Employers looking at future cybersecurity job market trends, future skills for cybersecurity professionals, and specialized role demand forecasts increasingly care about applied readiness, not just textbook familiarity.
That said, IT support alone is not enough. Support experience gives you proximity, not automatic eligibility. Employers still want proof that you can think like a defender. They want to know whether you understand log analysis, suspicious activity triage, attack pathways, threat behavior, access control, control validation, and escalation judgment. That is where the transition succeeds or fails. The strongest candidates do not hide their support background. They reframe it as security-relevant operational experience and deliberately add the missing layers through projects, labs, targeted certifications, and security-focused narrative building.
| Support Experience / Gap | Why It Matters for Security | How to Reframe or Improve It | Career Leverage Created |
|---|---|---|---|
| 1. Password reset work | Builds identity awareness | Connect it to authentication risk, MFA, and account abuse patterns | Shows security-relevant identity exposure |
| 2. Account lockout troubleshooting | Reveals login anomalies and brute-force signals | Document recurring sources, timing, and suspicious patterns | Supports analyst-style detection thinking |
| 3. Endpoint support | Creates host-level familiarity | Learn process behavior, startup items, logs, and persistence basics | Helps with triage and containment credibility |
| 4. VPN issue handling | Touches remote access and trust boundaries | Map it to secure access, session risk, and exposure concerns | Strengthens remote access security narrative |
| 5. Ticket documentation | Good analysts document clearly under pressure | Highlight timelines, evidence quality, and escalation precision | Shows investigation discipline |
| 6. User communication | Security needs calm, clear guidance | Position it as incident communication and security awareness support | Improves interview strength |
| 7. Active Directory exposure | Identity is central to modern defense | Study groups, OUs, GPOs, permissions, and admin delegation | Builds IAM relevance fast |
| 8. Privileged access handling | Overprivilege drives risk | Learn [PAM solution](https://acsmi.org/blogs/best-privileged-access-management-pam-solutions-ranked-amp-reviewed) basics and approval logic | Signals maturity beyond support |
| 9. Patch support | Patch gaps drive exposure | Frame work in terms of risk reduction and remediation prioritization | Links support to vulnerability management |
| 10. Malware cleanup assistance | Touches early incident response | Learn evidence preservation, not just removal | Makes response experience more credible |
| 11. Email troubleshooting | Phishing starts in inboxes | Study spoofing, malicious links, and mailbox investigation basics | Supports phishing analysis readiness |
| 12. Network troubleshooting | Security analysts need flow awareness | Learn ports, protocols, segmentation, and suspicious traffic indicators | Bridges support and detection work |
| 13. Asset inventory work | You cannot defend unknown assets | Position inventory work as visibility and attack surface control | Shows governance mindset |
| 14. Remote tool administration | Legitimate tools can be abused | Learn dual-use risk and monitoring expectations | Improves threat-hunting logic |
| 15. Basic scripting | Automation helps scale analysis | Use PowerShell or Python for log parsing and enrichment tasks | Adds analyst efficiency signal |
| 16. Weak resume framing | Good experience can look irrelevant if poorly described | Rewrite bullets around risk, access, troubleshooting, and escalation | Improves interview conversion |
| 17. No home lab | Employers want practical proof | Build small labs for Windows logs, phishing analysis, and alert triage | Creates talking points that stand out |
| 18. No detection practice | Security requires interpretation, not just administration | Practice reviewing logs, auth failures, and suspicious event chains | Demonstrates analyst mindset |
| 19. No incident narrative examples | Hiring managers trust concrete stories | Prepare 5 detailed examples of anomalies, escalation, and problem isolation | Strengthens behavioral interviews |
| 20. Limited cloud exposure | Cloud security keeps growing | Learn identity, storage, logging, and access basics in cloud platforms | Improves future-facing relevance |
| 21. No framework knowledge | Analysts must understand control language | Study [NIST, ISO, and COBIT](https://acsmi.org/blogs/cybersecurity-frameworks-nist-iso-and-cobit) at a practical level | Improves governance fluency |
| 22. Weak log familiarity | Log reading is core analyst work | Use Windows Event Viewer, Sysmon, and firewall logs in labs | Builds real screening ability |
| 23. No certification strategy | Certs help reduce perception risk | Choose certs aligned to entry analyst roles, not random prestige chasing | Improves recruiter traction |
| 24. No networking in security community | Opportunities often move through visibility | Use [cybersecurity conferences](https://acsmi.org/blogs/best-cybersecurity-conferences-directory-2026-2027-global-guide), [podcasts](https://acsmi.org/blogs/directory-of-top-cybersecurity-podcasts-for-industry-professionals), and learning circles | Expands opportunity surface |
| 25. Generic job applications | Security hiring is competitive | Tailor each application to monitoring, triage, IAM, or incident response emphasis | Raises application quality sharply |
| 26. No long-term plan | Analyst role should lead somewhere | Map future options like [cloud security engineer](https://acsmi.org/blogs/how-to-become-a-cloud-security-engineer-complete-career-guide), [cybersecurity manager](https://acsmi.org/blogs/how-to-become-a-cybersecurity-manager-clear-pathway-and-certifications), or [CISO](https://acsmi.org/blogs/step-by-step-guide-to-becoming-a-chief-information-security-officer-ciso) | Creates focused career momentum |
2. The exact skills from IT support that transfer into cybersecurity analyst work
The smartest transition strategy starts with extracting value from skills you already have. Many candidates sabotage themselves by presenting their background too narrowly. They say they “resolved tickets” or “helped users with technical problems,” which sounds generic and disposable. But underneath that wording are real security-relevant functions: identity troubleshooting, access management, endpoint triage, remote access support, software integrity checks, escalation handling, and issue pattern analysis. The issue is not always weak experience. It is weak translation.
Identity exposure is one of the biggest transferable strengths. If you have handled password resets, account unlocks, MFA troubleshooting, access permission issues, group assignments, or directory-related escalations, you have already been close to one of the most attacked areas in modern enterprise security. Cybersecurity analysts spend major portions of their time around authentication anomalies, suspicious login activity, privilege misuse, access policy issues, and identity investigation. That makes your support experience valuable when paired with stronger understanding of access control models, public key infrastructure components and applications, VPN security benefits and limitations, and practical data loss prevention strategies and tools.
Endpoint familiarity transfers strongly too. Support professionals who troubleshoot machines, software installs, suspicious performance issues, failed updates, strange processes, or unauthorized applications are already close to the environment where many alerts originate. A good cybersecurity analyst needs to understand what a normal endpoint looks like, how software behaves, how user actions create artifacts, and which changes deserve attention. This becomes even more useful when building literacy around encryption standards, firewall technologies and configurations, botnet disruption methods, and DoS prevention and mitigation.
Escalation handling is another hidden asset. IT support staff routinely decide which issues can be resolved locally, which require infrastructure teams, which need urgent action, and how to capture enough detail for others to act. That logic sits close to analyst triage. In cybersecurity, the names change, but the judgment pattern is familiar: determine severity, gather context, avoid premature assumptions, preserve useful evidence, and escalate with clarity. Support professionals with strong ticket hygiene already have a head start when learning incident response, security audits, cyber threat intelligence collection and analysis, and practical analyst workflows inside next-gen SIEM environments.
User behavior exposure matters as well. Security teams constantly deal with the human layer of risk: suspicious emails, unsafe downloads, weak password habits, risky workarounds, shadow IT, oversharing, improper remote access behavior, and delayed reporting of suspicious events. IT support sees those human patterns long before many dedicated security professionals do. That insight becomes powerful when you start speaking the language of defensive controls, attacker pathways, and business risk instead of just technical inconvenience.
3. The biggest gaps blocking IT support professionals from landing cybersecurity analyst roles
Most support professionals do not lose cybersecurity opportunities because their past is irrelevant. They lose because hiring managers see unresolved doubt. Can this person read logs? Can they investigate suspicious behavior instead of just fixing user problems? Can they reason about threats, not just outages? Can they preserve evidence, understand severity, and explain security implications? Closing those doubts is the transition.
The first major gap is shallow security vocabulary without operational depth. Many candidates can define phishing, malware, zero trust, or ransomware, but that does not prove analyst readiness. Employers want to hear how you would validate an alert, distinguish false positives from suspicious patterns, investigate authentication anomalies, interpret host or network artifacts, and escalate based on business impact. You close this gap by practicing real defensive workflows, not just memorizing terms. That means using labs, writing mini case studies, reviewing logs, and learning how controls behave under normal and abnormal conditions. Resources on ransomware detection, response, and recovery, deepfake threat preparation, AI-powered cyberattack trends, and top cybersecurity threats predicted by 2030 help shape modern threat thinking, but you still need hands-on evidence.
The second gap is weak log and alert familiarity. Support teams often work with symptoms, while analysts must work with signals. If you cannot confidently discuss Windows event logs, failed logon patterns, PowerShell activity, endpoint alerts, firewall events, DNS clues, or suspicious process behavior, your transition story will feel thin. This is one of the most fixable weaknesses because you can practice at home. Build a lab. Generate failed logins. Create account changes. Review logs. Forward data into an open-source or trial SIEM. The goal is not perfection. The goal is comfort.
The third gap is no visible security proof. Hiring managers see many applicants claiming passion for cybersecurity. Very few show disciplined proof. A home lab, GitHub notes, short write-ups, alert analysis screenshots, study summaries, phishing breakdowns, mini incident reports, or control-comparison notes can all help. Even a thoughtful comparison of best cloud security tools, application security platforms, network monitoring tools, and security awareness training platforms can show applied curiosity if done intelligently.
The fourth gap is poor narrative positioning. A weak resume makes the candidate look like a generalist fixer with no security direction. A stronger resume highlights risk-relevant responsibilities: managed authentication issues, supported access controls, escalated suspicious endpoint behavior, maintained patch compliance, documented technical incidents, supported remote access hygiene, assisted with malware-related troubleshooting, or improved asset visibility. The truth often already exists inside the work. It just needs sharper language.
The fifth gap is random learning. Many candidates study scattered topics without a role-based roadmap. They chase every certification, every trending tool, and every viral topic, then end up with fragmented knowledge and no hiring signal. The better path is to study like someone aiming at a specific role: entry-level cybersecurity analyst, SOC analyst, junior detection analyst, or incident triage analyst. Role clarity makes learning more convincing.
4. A practical step-by-step roadmap to move from IT support into cybersecurity analyst work
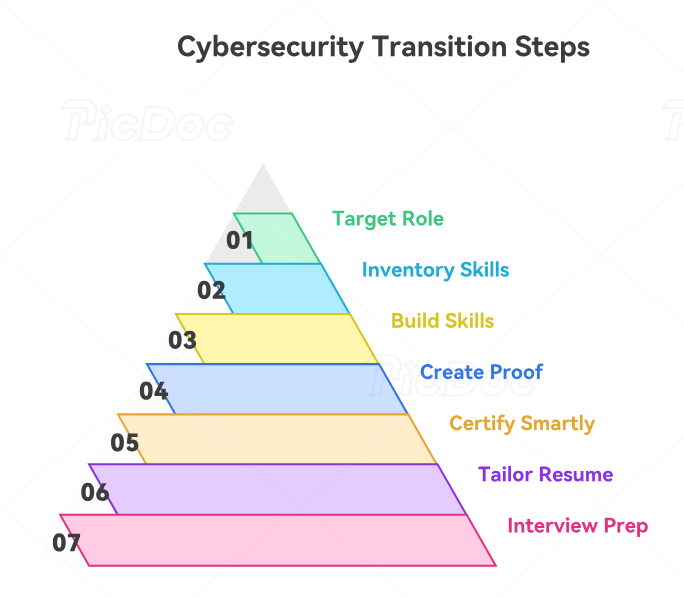
The first step is to choose the right target title. Do not say you want to “get into cybersecurity” in a vague way. That is too broad and too passive. Aim at specific entry points such as cybersecurity analyst, SOC analyst, junior security analyst, security operations analyst, or incident triage analyst. Those roles are much easier to map to your current background than highly specialized titles. Once your target is specific, your study, resume, projects, and networking become more coherent.
The second step is to inventory your current support experience through a security lens. List everything you have touched that relates to identity, endpoints, access, patching, remote access, logging, escalations, malware, email issues, asset tracking, or permissions. Then rewrite each item in security-adjacent language. This is not dishonesty. It is precision. A candidate who says “supported user authentication troubleshooting across enterprise accounts” sounds stronger than someone who says “reset passwords.” A candidate who says “triaged suspicious endpoint issues and escalated unresolved anomalies” sounds more security-ready than someone who says “fixed device problems.”
The third step is to build a narrow, serious skill stack. For this transition, focus on endpoint fundamentals, Windows logs, authentication events, networking basics, common attack patterns, incident triage, and defensive tooling concepts. Pair that with practical reading on cybersecurity certifications of the future, remote cybersecurity career trends, AI-driven cybersecurity tools, and cloud security trend analysis, because employers increasingly value candidates who understand where analyst work is heading.
The fourth step is to create proof. Build a simple lab and make it work for you. Set up a Windows VM. Trigger failed logins. Review event logs. Install Sysmon. Practice reading process creation events. Send safe test emails through a phishing-analysis workflow. Generate basic suspicious scenarios and document how you investigated them. You do not need a giant home SOC. You need enough hands-on familiarity to speak confidently and concretely.
The fifth step is to choose certifications strategically. Early-career transitions usually benefit from certifications that reduce recruiter hesitation and show structured commitment. But do not collect certifications like trophies. Pick the ones that align with analyst work and your current level. Combine that with selective exposure to global cybersecurity training providers, research organizations and institutes, top cybersecurity books, and YouTube channels for cybersecurity learning so your learning becomes deeper, not just broader.
The sixth step is to tailor your resume and LinkedIn around analyst outcomes. Use bullets that emphasize investigation, access, risk, endpoint support, escalation, evidence, and operational discipline. Add labs, projects, and mini case studies. Then apply selectively, not blindly. A targeted application to a SOC analyst role with a sharp narrative is stronger than fifty generic applications to every job with the word “security” in it.
The seventh step is interview preparation. You need strong stories about suspicious behavior, urgent troubleshooting, access-related problems, escalation judgment, documentation discipline, and times you had to isolate root cause under pressure. Support professionals often have excellent examples but tell them weakly. The interview should make the hiring manager feel that you are already thinking like an analyst, just from a different operational seat.
5. How to make employers trust your transition and accelerate your first cybersecurity analyst opportunity
The hiring risk in a career transition is rarely talent alone. It is uncertainty. Employers worry that you may be interested in cybersecurity but not actually ready for its pressures. Your job is to reduce that uncertainty everywhere they look: resume, LinkedIn, projects, networking, interview answers, and learning choices.
First, make your transition legible. A resume that mixes random support tasks with generic security buzzwords creates doubt. A stronger profile tells a clean story: IT support professional building toward analyst work through identity exposure, endpoint troubleshooting, log analysis, home lab practice, incident triage projects, and targeted security study. That story should feel intentional. When employers see a deliberate transition, they become much more comfortable betting on you.
Second, build visible seriousness. Hiring managers trust candidates who create evidence without being asked. That can mean publishing short LinkedIn posts on lessons from security audits, comparing cybersecurity consulting firms, analyzing SMB cybersecurity providers, or discussing the implications of cybersecurity compliance trends. You do not need to become a thought leader. You need to look active, thoughtful, and role-aligned.
Third, network like someone changing categories, not just jobs. People who stay inside IT support circles often hear about more support roles. To move into security, start participating in security-oriented communities, events, meetups, webinars, and professional conversations. Use cybersecurity conferences, podcasts for industry professionals, and directories of cybersecurity firms in financial services, healthcare cybersecurity firms, and top cybersecurity companies worldwide to understand where analyst roles live and how the market describes them.
Fourth, use your current job as a transition asset. Many candidates ignore internal opportunities. If your current employer has a security team, SOC, compliance group, audit function, IAM team, or vulnerability management process, find ways to contribute. Volunteer for security awareness efforts, patch-related reporting, access reviews, asset inventory improvement, phishing escalation processes, or endpoint control rollouts. Internal trust can open doors faster than external cold applications.
Fifth, think beyond the first job title. Your goal is not merely to escape support. It is to enter a trajectory. A first analyst role can later lead toward cloud security engineer, cybersecurity compliance officer, cybersecurity auditor, security manager, director of cybersecurity, or even long-term leadership paths like CISO. That future matters because it helps you make better early choices now.
6. FAQs
-
Yes, and often more naturally than people think. IT support creates operational familiarity with users, endpoints, access issues, systems, remote tools, and troubleshooting patterns. The transition works when you intentionally add security depth, log familiarity, incident reasoning, and stronger role-specific proof.
-
They present themselves as general troubleshooters instead of risk-aware operators. The issue is often not weak experience but weak framing. If your resume and interviews do not translate your support work into identity, endpoint, escalation, and security-relevant language, hiring managers may underestimate you.
-
Not always, but certifications can reduce perception risk and improve recruiter traction, especially early in a transition. The key is to choose them strategically. One relevant certification backed by hands-on proof is usually better than several unrelated certifications with no practical evidence.
-
Projects that show investigation and defensive thinking work best. Examples include log analysis labs, phishing investigations, basic incident write-ups, suspicious authentication event reviews, Windows event analysis, Sysmon-based host activity review, and small SIEM practice environments.
-
Focus on authentication, access management, endpoint troubleshooting, escalation, incident-like problem handling, patch support, remote access, documentation quality, and any suspicious activity review. Use language tied to risk, investigation, control support, and operational reliability rather than generic “customer support” phrasing.
-
It depends on your current exposure, consistency, and how intentionally you build proof. Someone with strong support experience, targeted study, practical labs, and well-positioned applications can move much faster than someone studying randomly without evidence or role clarity.