How to Advance from Cybersecurity Specialist to Cybersecurity Educator
Cybersecurity specialists often discover that technical mastery alone does not create scale. Solving incidents, hardening systems, and closing findings matter, but teaching other people how to think, decide, and respond multiplies that impact far beyond one queue, one team, or one environment. The move from practitioner to educator becomes especially attractive when you want stronger influence, longer-term career durability, and work that compounds your expertise instead of trapping it inside daily operational churn.
The challenge is that great practitioners are not automatically great teachers. Hiring managers for training, curriculum, and instructor roles look for clarity, structure, empathy, assessment design, and the ability to translate complexity without dumbing it down. That transition is learnable. Done right, it can take you from being the person who knows security to the person who helps others perform it at a professional standard.
1. Why the Move From Cybersecurity Specialist to Educator Is a Serious Career Upgrade
A lot of cybersecurity professionals reach a point where pure technical execution stops feeling like enough. You may be excellent at investigations, hardening, control validation, or stakeholder communication, yet still feel boxed in by alert queues, ticket fatigue, audit cycles, or endless reactive work. The shift into education creates a different kind of leverage: instead of fixing one issue at a time, you improve how dozens, hundreds, or even thousands of people approach security work.
That is why this move is not an “escape hatch” for burned-out practitioners. It is a real advancement path. A strong educator shapes talent pipelines, reduces onboarding failure, improves operational consistency, and helps organizations avoid the expensive mistake of promoting technically strong people into roles they were never trained to perform well. If you have spent time studying cybersecurity frameworks like NIST, ISO, and COBIT, running security audits and best-practice reviews, working through incident response plan development and execution, and learning how SIEM works in real environments, you already hold the raw material that many aspiring professionals desperately need.
What changes is the output. As an educator, you stop proving value only through personal execution. You start proving value through learner outcomes. Can you help an entry-level analyst understand vulnerability assessment techniques and tools without confusing them? Can you train future defenders to recognize the operational realities behind ransomware detection, response, and recovery? Can you explain access control models like DAC, MAC, and RBAC in a way that holds up in both exam prep and live environments? Can you connect tactical skills to market realities using the global cybersecurity salary report and broader job market trend analysis?
The professionals who succeed in this transition understand a critical truth: education in cybersecurity is not motivational speaking with security jargon attached. It is structured performance enablement. That is why studying the path outlined in ACSMI’s career guide to becoming a cybersecurity instructor or trainer, the more tactical step-by-step guide to becoming a cybersecurity instructor, and the adjacent roadmap for cybersecurity curriculum developers gives you a much sharper picture of what employers actually reward.
| Transition Asset | Why It Matters for Educator Roles | How to Prove It | What It Unlocks |
|---|---|---|---|
| SOC workflow fluency | Lets you teach live detection, triage, and escalation realistically | Create a mini SOC case lab | Analyst bootcamp instructor roles |
| Incident response experience | Adds credibility when teaching decision pressure | Write tabletop scenarios with debrief notes | Corporate trainer positions |
| Vulnerability management | Helps learners understand prioritization instead of tool worship | Build remediation ranking exercises | Technical course authoring |
| Pen testing exposure | Improves offensive content quality and realism | Record safe demo walkthroughs | Bootcamp mentoring roles |
| Compliance knowledge | Makes training useful for regulated sectors | Design control-mapping worksheets | GRC education pathways |
| Cloud security depth | Supports modern infrastructure teaching demand | Publish cloud misconfiguration labs | Cloud training roles |
| Threat intelligence skills | Sharpens analytical instruction and reporting methods | Create indicator triage exercises | CTI instructor work |
| Log analysis ability | Critical for learner confidence in practical detection work | Produce annotated log packets | Hands-on lab facilitation |
| Network security fundamentals | Prevents shallow teaching and tool-only explanations | Build packet flow teaching diagrams | Foundational course delivery |
| Endpoint security knowledge | Aligns with common employer demand in training | Compare control stacks and use cases | Enterprise enablement roles |
| Email security understanding | Useful for awareness and detection-focused programs | Create phishing analysis labs | Awareness instructor roles |
| IAM and access control | Supports secure design and governance instruction | Build role-design case studies | Architecture education roles |
| Risk communication | Separates instructors from jargon-heavy practitioners | Rewrite findings for executive audiences | Leadership training roles |
| Presentation skill | Directly impacts learner engagement and retention | Teach short sessions and collect feedback | Instructor shortlist credibility |
| Curriculum sequencing | Shows you can build progression, not just explain topics | Design a 6-module syllabus | Curriculum developer roles |
| Assessment design | Employers want proof learners can perform, not just watch | Write rubrics and scenario-based quizzes | Academic and enterprise training roles |
| Coaching ability | Important for helping struggling learners recover | Document learner intervention plans | Mentor-led programs |
| Documentation discipline | Improves handouts, labs, and learner consistency | Publish clean SOP-style guides | Training operations roles |
| Video teaching comfort | Essential for online academies and asynchronous programs | Record concise lesson videos | Remote instructor jobs |
| Workshop facilitation | Shows you can manage live energy and timing | Lead practice-driven labs | Conference and bootcamp work |
| Learning tool familiarity | Helps deliver smoother learner experience | Build LMS-ready lesson assets | Program delivery roles |
| Industry trend awareness | Keeps your teaching relevant rather than stale | Update modules quarterly | Thought leadership positioning |
| Certification relevance | Signals alignment with employer-recognized standards | Tie lessons to cert outcomes | Exam-prep instruction roles |
| Portfolio publishing | Creates visible evidence beyond résumé claims | Host labs, outlines, and teaching clips | Faster recruiter trust |
| Executive translation | Useful for leadership education and security culture work | Build board-friendly explainer decks | Leadership enablement positions |
| Feedback integration | Great educators refine constantly | Show before/after course improvements | Long-term instructional growth |
2. The Skills Gap You Must Close Before Anyone Trusts You to Teach
Most cybersecurity specialists underestimate where the real gap sits. It is rarely the technical side. The real gap is instructional design. Many strong practitioners can explain what they do. Far fewer can sequence learning in a way that moves someone from confusion to competent execution under pressure. That is the difference between being useful in a meeting and being employable as an educator.
You need to learn how adults actually absorb difficult material. For example, a learner does not benefit much from hearing a polished lecture on firewall technologies and configurations if they still cannot reason through traffic flow, logging blind spots, or rule-ordering mistakes. A junior analyst gains little from hearing definitions about intrusion detection systems and deployment if you never teach how to distinguish noise from escalation-worthy signals. The same applies when covering DLP strategies and tools, PKI components and applications, or encryption standards such as AES and RSA. Knowledge is not the finish line. Transfer is.
That means your next stage of growth should include lesson architecture, learning objectives, assessment logic, and remediation methods for struggling learners. Spend time studying how structured training providers operate by reviewing the global directory of cybersecurity training providers, comparing formats in the best cybersecurity bootcamps and academies, and evaluating how different channels teach using the best YouTube channels for cybersecurity learning and updates, the top cybersecurity podcasts directory, and the top cybersecurity books directory.
Another gap is audience adaptation. Teaching peers is one thing. Teaching career-changers, executives, first-job candidates, or compliance-heavy teams is another. Someone transitioning from IT support to cybersecurity analyst work needs clarity, progression, and confidence-building. Someone aiming for a SOC analyst path or a more advanced security analyst to engineer roadmap needs rigor and performance benchmarks. Someone exploring compliance analyst roles or auditor pathways needs translation between technical control reality and governance language.
If your teaching still sounds like expert-to-expert shorthand, you are not ready yet. The educator’s job is not to impress the strongest person in the room. It is to elevate the weakest serious learner without insulting the strongest one.
3. A Step-by-Step Plan to Reposition Yourself as a Cybersecurity Educator
The smartest way to make this transition is to build evidence before you need the title. Do not wait for someone to “give you a chance” as an instructor. Start behaving like one while still in your current role.
First, define the educational lane you can teach credibly. You do not need to teach everything. In fact, broad positioning usually hurts you. Pick a lane such as SOC operations, incident response, cloud security, security awareness, GRC, or ethical hacking. If your background leans toward detection and response, map your positioning to resources like the SOC analyst guide, the progression from SOC analyst to SOC manager, and the adjacent incident responder career path. If your strength is offensive security, align with the ethical hacker roadmap, the CEH pathway, and the OSCP-focused guide.
Second, build teaching assets, not just content. A strong educator portfolio includes a course outline, two to three sample lessons, one lab or case exercise, one assessment rubric, and proof that you can explain hard topics cleanly. That could mean a short lesson on botnet structure and disruption methods, a guided exercise on denial-of-service prevention and mitigation, or a scenario that teaches cyber threat intelligence collection and analysis. The goal is to demonstrate learning design, not just subject familiarity.
Third, teach in low-risk environments. Run internal workshops. Mentor junior staff. Host lunch-and-learns. Volunteer for onboarding. Offer mock interview coaching. Even a short internal session on VPN security benefits and limitations or a debrief on phishing trends and prevention strategies can create the practice loop you need. Real teaching exposes pacing problems, assumption gaps, and explanation weaknesses fast.
Fourth, connect your educator positioning to market demand. Use the impact of cybersecurity certifications on career advancement, the analysis on salary growth for CISSP, CEH, and other security certifications, and the broader entry-level to CISO salary progression study to show you understand what learners care about: employability, progression, credibility, and return on effort. Learners do not want content. They want movement.
Quick Poll: What Kind of Cybersecurity Educator Are You Trying to Become?
Pick the path that fits your real goal, because teaching strategy changes with the audience you want to serve.
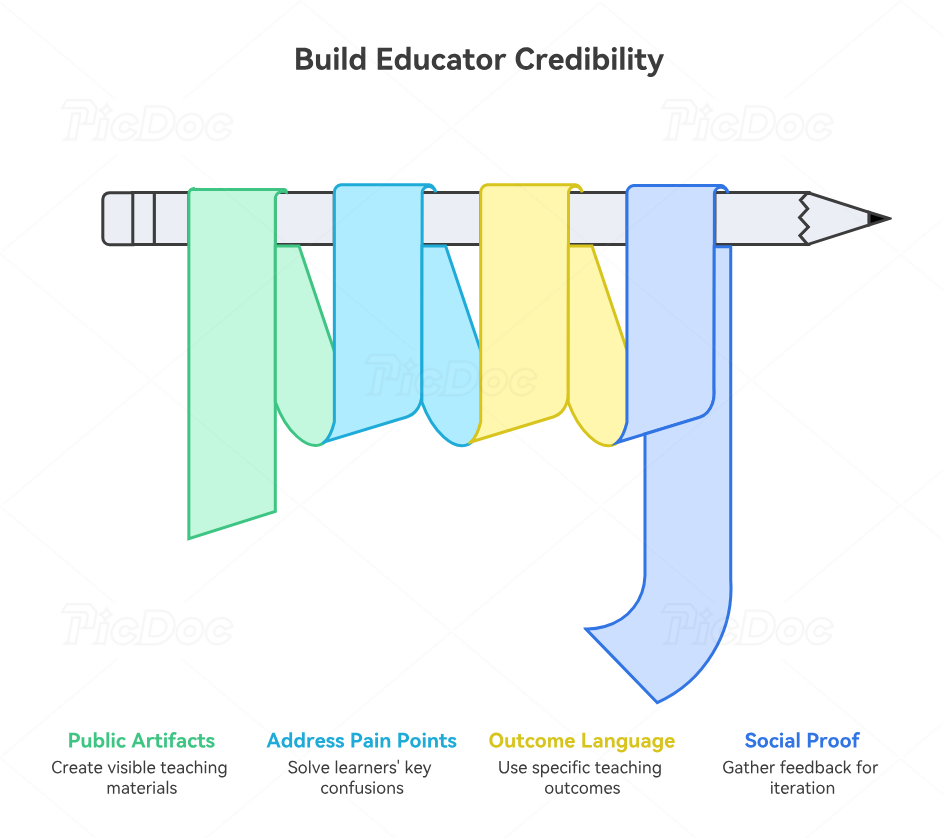
4. How to Build Educator Credibility Without Waiting for Permission
The biggest mistake specialists make is assuming that educator credibility appears after they land an educator title. In reality, the title usually follows visible teaching proof. That proof can be built now.
Start with public artifacts. Write short explainers. Publish practical breakdowns. Create comparison guides, mini syllabi, annotated diagrams, role-based learning maps, and scenario walkthroughs. Good artifacts make your thinking inspectable. A hiring manager can quickly tell whether you merely know the subject or whether you can structure it for somebody else. If you are teaching future analysts, reference the ecosystem they are entering through materials such as the directory of free cybersecurity courses and resources, the top cybersecurity certifications directory, and the forward-looking guide to cybersecurity certifications employers may value most by 2030.
Next, position your expertise where learners already have pain. That pain includes confusion about role differences, overhyped tools, unrealistic roadmaps, shallow bootcamp promises, and fear that they are studying the wrong things. You become more valuable when you reduce those risks. A specialist who can explain the practical differences between EDR tools, SIEM solutions, vulnerability scanners, application security tools, and cloud security tools in plain language is already doing educator work.
Then develop outcome-based teaching language. Learners and employers both trust specificity. Instead of saying, “I can teach incident response,” say, “I teach analysts how to scope an incident, preserve evidence, communicate severity, and make containment decisions without overreacting.” Instead of saying, “I teach cloud security,” say, “I help learners identify misconfigurations, understand identity boundaries, and connect architecture decisions to actual risk.” Clear outcomes feel credible because they sound operational.
Finally, build social proof from feedback loops. Save learner comments. Track workshop satisfaction. Document pre- and post-training improvements. Capture examples of lessons you revised after seeing learner confusion. Strong educators are iterative. They do not cling to explanations that sound smart but fail learners. That same humility is what makes someone effective in adjacent roles like curriculum development, security management, or the broader leadership path toward director of cybersecurity.
5. The Best Career Paths, Positioning Angles, and Mistakes to Avoid
There is more than one version of a cybersecurity educator. Some professionals thrive in internal enterprise training. Some are strongest in bootcamps or workforce academies. Some move into certification prep. Others evolve into full curriculum architects, technical content leads, or public-facing instructors. The right path depends on your technical background, patience for learner variability, communication style, and appetite for content creation.
If you enjoy live facilitation, corporate training or bootcamp instruction may fit you. If you are deeply structured and love sequence, curriculum development may be stronger. If you prefer one-to-many authority building, public education through courses, writing, and workshops can become a durable lane. Reviewing adjacent market demand helps here. The predicting demand for specialized cybersecurity roles, the analysis of future skills for cybersecurity professionals, and the discussion around automation and the future cybersecurity workforce all point to one enduring truth: organizations still need people who can build capable humans, not just deploy capable tools.
The worst mistake is trying to sound too advanced. Many specialists entering education overload lessons with jargon, skip foundational reasoning, and mistake density for rigor. Another common mistake is teaching only what is interesting rather than what is job-relevant. Learners do not need ten exotic threat examples if they still cannot reason through alert context, asset criticality, escalation thresholds, or basic defensive priorities. A third mistake is building a portfolio around opinions instead of teachable systems. Employers want to see modules, labs, rubrics, lesson plans, and learner outcomes.
A final mistake is ignoring the business side of education. Programs succeed when they help organizations fill talent gaps, reduce onboarding time, improve operational consistency, and align skills with actual market needs. That is why educator candidates should understand the broader landscape through resources like the cybersecurity workforce shortage study, the remote versus on-site cybersecurity salary analysis, and the deeper look at cybersecurity freelance and consulting income trends. When you can connect teaching to workforce outcomes, you stop looking like a hobbyist and start looking like an education asset.
6. FAQs
-
You need evidence more than a formal title. Internal workshops, mentorship, onboarding support, lab creation, recorded lessons, written learning guides, and sample assessments can all count. The strongest applications show that you can turn expert knowledge into learner progress.
-
Professionals in SOC, incident response, GRC, cloud security, awareness training, and offensive security often transition well because their work produces teachable systems, repeatable decisions, and scenario-rich material. The key factor is not specialty alone. It is whether you can explain decisions clearly and build structured learning around them.
-
Sometimes, but only when the certification strengthens your teaching market, credibility, or curriculum alignment. Chasing badges without improving your ability to explain, sequence, and assess learning will not solve the real transition problem. Relevant certifications help. Teaching proof closes the deal.
-
Include a short teaching bio, a defined learner audience, a course outline, one or two lesson samples, one practical exercise or lab, one assessment rubric, and proof of feedback or learner response. A clean portfolio beats a bloated one.
-
It can be, especially if you are strong at structure, sequencing, and assessment design. Live instruction rewards presence, pacing, and facilitation. Curriculum development rewards architecture, clarity, and systems thinking. Many professionals should start with both in small doses before choosing a dominant lane.
-
A credible shift can begin within a few months if you deliberately build proof. Landing a strong educator role may take longer depending on your niche, visibility, and portfolio quality. The professionals who move fastest usually stop waiting for permission and start publishing, teaching, and refining in public or semi-public settings.
-
Yes, and that is often the strongest positioning early on. Hybrid credibility is powerful. Practicing while teaching keeps your examples current, prevents stale instruction, and gives learners confidence that your content reflects real environments rather than recycled theory.
-
Structured evidence that learners can understand and apply what you teach. Technical credibility gets attention. Instructional clarity gets trust. Demonstrated learner outcomes get offers.