Career Roadmap: From IT Professional to Cybersecurity Certification Trainer
Many IT professionals reach a point where solving tickets, hardening systems, and supporting infrastructure no longer feels like the full game. They want leverage. They want authority. They want to turn years of hard-won technical pattern recognition into career capital that compounds. Becoming a cybersecurity certification trainer offers exactly that, but only for people who can translate practice into teachable outcomes.
This path is not a soft exit from technical work. It is a credibility role. The strongest trainers are built from real operational scars, sharp instructional judgment, and a certification strategy that aligns with the roles employers actually hire for. This roadmap shows how to make that transition without becoming another theory-heavy instructor with weak market value.
1. Why IT Professionals Have an Unfair Advantage in Cybersecurity Training
An IT professional starts with something many aspiring trainers lack: operational context. Years spent in IT support to cybersecurity analyst transitions, network monitoring and security tools, firewall technologies and configurations, access control models, and VPN security benefits and limitations create instincts that cannot be faked in a classroom.
That matters because students do not just need facts. They need filtered judgment. They need someone who can explain why a log source matters in a SIEM environment, how a detection fails in a noisy SOC, why an incident response plan breaks down under pressure, and where a control that looks beautiful on paper collapses in production. Trainers with a pure academic background often miss those failure points.
The transition becomes powerful when you stop thinking of “trainer” as a person who reads slides and start thinking of it as a role that packages expertise into outcomes. Great trainers help learners pass certifications, but that is only one layer. They also help people understand cybersecurity frameworks like NIST, ISO, and COBIT, connect them to security audits and best practices, interpret vulnerability assessment techniques and tools, and translate abstract ideas into job-readiness.
This is where many mid-career professionals make a costly mistake. They assume subject expertise is enough. It is not. Employers, bootcamps, academies, and corporate training teams want people who can teach a learning sequence, diagnose confusion fast, build practical labs, and explain the “why” behind tool choices such as EDR tools, SIEM solutions, DLP software, and application security tools.
The strongest move is to leverage your current IT experience into a focused cybersecurity teaching brand. Someone coming from systems administration can teach identity, hardening, patching, baseline security, and control mapping. Someone from networking can teach segmentation, monitoring, packet analysis, and exposure reduction. Someone from cloud operations can evolve toward cloud security engineering. Someone from internal audit or governance can move toward cybersecurity compliance officer pathways and cybersecurity auditor roles.
The point is simple: your background is not baggage. It is positioning. A trainer with lived infrastructure experience can teach cause and effect. That creates trust faster than a wall of acronyms ever will.
2. The Certification Stack That Actually Builds Trainer Credibility
Certification stacking fails when it becomes résumé decoration. It works when each credential supports a teaching lane. Before selecting anything, study the top cybersecurity certifications directory, then compare that list with the impact of cybersecurity certifications on career advancement, the salary growth analysis for CISSP, CEH, and security certifications, and the entry-level to CISO salary progression analysis. Those resources help you choose credentials that move both students and your own market position.
For most IT professionals, the first layer is a baseline credential that proves security literacy. That often means Security+, ISC2 CC, or another beginner-friendly foundation. This does not make you trainer-ready. It makes you legible. The second layer is where positioning begins. Someone leaning defensive can study SOC analyst career paths, security analyst to engineer pathways, or incident responder roles. Someone leaning offensive can pursue ethical hacker pathways, CEH preparation, and OSCP-focused penetration testing paths.
The third layer is senior-trust credibility. This is where credentials such as CISSP, CISM, CCSP, audit-oriented certifications, and governance-focused learning begin to matter. Not because every student needs them immediately, but because they signal that you can connect technical controls to business risk, leadership expectations, and compliance obligations. That ability separates a content presenter from a trusted certification trainer.
A good trainer stack also reflects the training products you want to own. If you plan to teach bootcamp students entering the field, your stack should support free cybersecurity courses and resources, cybersecurity bootcamps and academies, global training providers, and YouTube learning channels. If you plan to teach experienced professionals, your content should align with cybersecurity manager pathways, director-level growth roadmaps, and the CISO step-by-step pathway only in the sense of mapping training toward executive relevance.
The hard truth is that students quickly sense when an instructor passed an exam but never built a framework for applying it. Your stack must tell a story: fundamentals, specialization, business context, then teaching authority.
3. How to Build Real Teaching Proof Before Anyone Pays You to Train
The fastest way to stall in this transition is to wait for a job title before acting like a trainer. Build proof first. That means turning your experience into demonstrable teaching assets. Start by creating a mini-curriculum around one lane: SOC analysis, vulnerability management, cloud security basics, compliance evidence handling, phishing defense, or incident response. Then make it visible.
A serious starter portfolio includes a course outline, three to five recorded micro-lessons, a slide deck, a lab worksheet, ten scenario-based quiz questions, and one capstone assignment. Each piece should align with real industry workflows such as ransomware detection, response, and recovery, cyber threat intelligence collection and analysis, intrusion detection systems deployment, PKI components and applications, and encryption standards like AES and RSA.
The most persuasive teaching proof solves confusion points that working learners actually struggle with. They do not only need definitions. They need guided translation. A student might understand what a vulnerability scan is, yet still fail to prioritize findings, explain business impact, or communicate remediation logic to non-technical stakeholders. Your content should close that gap. That is why resources like the vulnerability assessment guide, security audits best practices, NIST adoption analysis, and cybersecurity compliance trends are strong anchors for lesson design.
Do not ignore delivery mechanics. Trainers lose students when explanations are linear but the learner’s confusion is branching. You need modular teaching. One explanation for beginners. One for practitioners. One for managers. One for interview preparation. One for certification exam framing. That layered delivery model makes your teaching reusable across corporate training, bootcamps, cohort courses, and self-paced products.
You also need feedback data. Run small sessions for colleagues, junior professionals, or online communities. Track where learners slow down, what questions repeat, which lab steps fail, and where your examples feel too abstract. These friction points are not annoyances. They are curriculum gold. The better you diagnose misunderstanding, the more employable you become as a trainer or cybersecurity curriculum developer.
Quick Poll: What Result Are You Really Chasing by Becoming a Cybersecurity Trainer?
Pick the pressure point driving your move. Your roadmap changes depending on the real target.
4. The Skills That Separate a Respected Trainer From a Talking Head
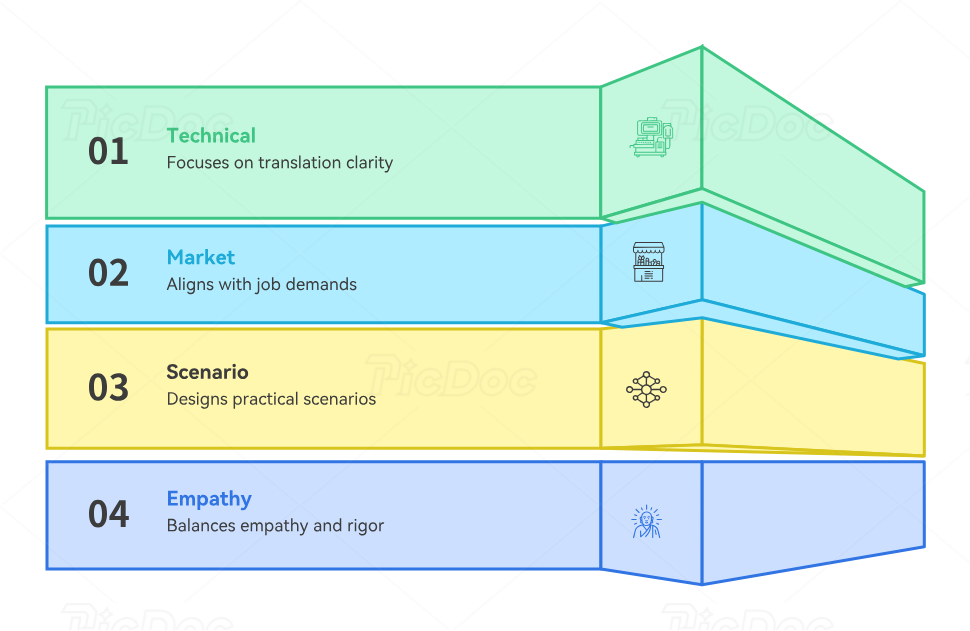
Students forgive polish gaps. They do not forgive wasted time. That is why respected trainers build around clarity, sequencing, and relevance. The first separator is technical translation. Can you explain botnet structure and disruption methods, DoS mitigation, email security solutions, endpoint security effectiveness, and phishing attack trends in a way that makes operational tradeoffs obvious?
The second separator is market alignment. A trainer who does not understand hiring demand teaches stale confidence. Use the cybersecurity job market trends report, the future skills for cybersecurity professionals, the roles predicted to thrive by 2030, and the demand for specialized cybersecurity roles to keep your curriculum connected to reality.
The third separator is scenario design. Good trainers do not just ask what a control is. They ask what fails when it is misconfigured, underfunded, or misapplied. That is why high-value teaching often draws from reports such as the state of ransomware analysis, the data breach report, the insider threat annual report, and the cloud threat analysis. These give learners texture, not just terminology.
The fourth separator is instructional empathy without intellectual softness. Adult learners are carrying insecurity, fatigue, impostor pressure, budget constraints, and job urgency. They do not need hand-holding. They need signal. A strong trainer identifies the exact misunderstanding, fixes it fast, and reconnects the concept to exam performance or career movement.
5. How to Land Roles as a Cybersecurity Certification Trainer
There are multiple lanes into this work. You can teach for bootcamps, private academies, internal enterprise L&D teams, certification prep companies, colleges, consulting firms, or your own training brand. Each lane rewards a different mix of proof. To understand the landscape, study cybersecurity instructor career guides, cybersecurity trainer pathways, curriculum developer paths, cybersecurity books and learning assets, and cybersecurity conferences where trainers often build authority.
Hiring managers usually look for five things: recent technical relevance, proof of structured teaching, certification alignment, learner outcomes, and communication under pressure. That means your application package should not be a generic résumé. It should include a trainer résumé, a teaching portfolio, a course sample, recorded delivery clips, a lab example, and a short note explaining the student outcome your material was designed to create.
You should also choose a specialization wedge. General cybersecurity trainers exist everywhere. Trainers known for SOC analyst growth, cloud security pathways, compliance analysis, ethical hacking careers, or security management advancement stand out faster.
Finally, understand compensation structure. Some roles pay for contact hours. Some pay for curriculum ownership. Some reward student placement, certification pass rates, or corporate client retention. The biggest long-term upside often comes from building training assets once and using them across workshops, cohorts, consulting, and digital products.
6. FAQs
-
You need enough real-world depth to explain why concepts matter, where they fail, and how they map to job tasks. A strong IT background plus focused cybersecurity practice, labs, and scoped teaching proof can be enough to start. For deeper credibility, stack operational exposure with relevant certifications and student-facing assets.
-
Start with a baseline credential, then choose a lane. Defensive trainers may lean toward Security+, CySA+, or blue-team pathways. Governance-focused trainers may move toward CISSP, CISM, audit, or compliance-aligned credentials. Offensive trainers should study CEH, OSCP, and penetration testing pathways. The right choice depends on what you want to teach repeatedly and profitably.
-
Yes, but your teaching must still feel operational. You can compensate for role gaps through labs, case studies, structured scenario design, shadow projects, and targeted specialization. The key is to avoid becoming purely exam-theoretical.
-
They collect credentials before building teaching proof. A portfolio with lessons, labs, assessments, and feedback data often creates more hiring confidence than an extra certification with no visible instructional output.
-
Build both in parallel, but start with small live sessions. Live teaching reveals where students get confused. That feedback makes your curriculum sharper. Then your sharper curriculum makes your delivery stronger. The two should compound together.
-
You are ready when you can clearly teach a certification-aligned topic, run a learner through a practical exercise, answer follow-up questions without collapsing into jargon, and show artifacts that prove your teaching creates outcomes. Once you have that, apply aggressively and refine from real feedback.