Detailed Career Path: Red Team Operator in Cybersecurity
Red team work attracts a lot of attention for the wrong reasons. Many candidates chase the title before they build the habits that let them survive inside it. A real red team operator does far more than run tools or collect flashy screenshots. The role demands adversary thinking, disciplined technical depth, precise writing, calm decision-making, and the ability to turn attack simulation into defensive improvement. This path works best when it is approached in layers, not leaps.
That is why the smartest route into red teaming starts with foundations, then moves through proof, specialization, operational maturity, and business trust. The goal is not to look dangerous on paper. The goal is to become useful in environments where mistakes are expensive.
1. Understand What a Red Team Operator Actually Does
A red team operator is hired to emulate a capable adversary in a controlled, ethical, and scoped way. That sounds simple until the work begins. The role sits at the intersection of penetration testing, adversary simulation, social engineering awareness, stealth, post-exploitation tradecraft, reporting, and risk translation. Someone who only knows how to exploit a web bug is not ready. Someone who can move from reconnaissance to initial access, privilege escalation, lateral movement, persistence, objective execution, and clean reporting starts looking far more credible.
This is why a serious candidate should first understand how red teaming differs from broader offensive security and from standard pentesting. A penetration test often focuses on finding exploitable weaknesses inside a defined target and proving impact quickly. Red team work is usually slower, more layered, and more outcome-driven. It tests detection, response, communication, escalation paths, and decision quality across the defender’s environment. Reading through the ACSMI guide on penetration testing tools, the breakdown of vulnerability assessment techniques and tools, the overview of security information and event management, and the directory of EDR tools helps clarify the difference between breaking in and operating against a mature defense stack.
A candidate aiming for red team work should also stop romanticizing the role as a pure exploit job. Most real career progress comes from being reliable under pressure. That means understanding incident response plans, knowing how intrusion detection systems are deployed, understanding firewall technologies, recognizing where access control models create friction, and being able to explain how an attack path would appear inside SIEM environments. Red team operators are dangerous partly because they understand the blue side deeply enough to move around it.
The fastest way to stall in this field is to build an identity around payloads, implants, and buzzwords before mastering operating systems, networking, Active Directory, cloud identity, authentication, logging, and privilege boundaries. Someone who has read the ACSMI pathway on becoming an ethical hacker, the guide to OSCP-oriented penetration testing growth, the roadmap for a security analyst to cybersecurity engineer path, and the guide on how to become a cloud security engineer usually develops a more realistic picture of the skills stack involved.
2. Build the Foundation Before You Touch Advanced Tradecraft
A red team career usually begins somewhere much less glamorous. Many strong operators start in help desk, systems administration, network support, SOC analysis, vulnerability management, or junior security engineering. That is not a detour. That is where pattern recognition is built. Someone who has spent time with messy enterprise reality understands where credentials are mishandled, where segmentation fails in practice, how endpoint teams triage alerts, and why identity sprawl creates hidden opportunity. The ACSMI path on transitioning from IT support to cybersecurity analyst, the guide to becoming a SOC analyst, the article on SOC analyst to SOC manager growth, and the roadmap for a cybersecurity auditor all show why enterprise context matters before specialization.
The real foundation has five layers. First, learn networking until traffic patterns make intuitive sense. Second, get comfortable in Linux and Windows, especially permissions, services, logs, and scripting. Third, understand web applications and APIs well enough to see weak trust boundaries. Fourth, build an Active Directory lab and break it repeatedly. Fifth, learn how defenders see the world through EDR, SIEM, and incident response workflows. Reading ACSMI’s guides on EDR solutions, best SIEM platforms, ransomware detection and recovery, cyber threat intelligence collection and analysis, and security audits and best practices strengthens that foundation from the defensive angle.
A lot of candidates sabotage themselves by trying to skip this phase with pure tool familiarity. Tool familiarity fades fast in interviews. Deep understanding travels. A candidate who can explain Kerberos abuse, identity trust, token handling, segmentation gaps, PowerShell logging, and detection blind spots sounds far more employable than someone who drops ten framework names and cannot explain why a move was noisy. That is also why studying CEH career preparation, reviewing the top cybersecurity certifications directory, exploring free cybersecurity courses and resources, and comparing bootcamps and academies should be treated as a sequencing problem, not a shopping spree.
3. Move From Offensive Learner to Employable Red Team Candidate
The jump from “I study hacking” to “I can be trusted on an engagement” happens when your work starts looking structured. That means building labs with purpose, documenting decisions, choosing realistic scenarios, and proving that you understand scope, ethics, cleanup, and communication. At this stage, your portfolio should not read like a trophy shelf. It should read like evidence that you can think through an operation. Write about reconnaissance logic. Show how a privilege boundary was identified. Explain how post-exploitation paths were prioritized. Break down where defenders would have caught the activity. Link every technical action to a reason.
This is where targeted career content becomes useful. ACSMI’s guides on the junior penetration tester to senior security consultant path, the route to an OSCP-certified penetration tester, the guide on how to become a threat intelligence analyst, the path to incident responder roles, and the roadmap for a cybersecurity compliance analyst may look like adjacent tracks, but each one develops a piece of the judgment red teamers need. Threat intelligence sharpens realism. Incident response sharpens defender empathy. Compliance work sharpens control awareness. Consulting paths sharpen communication and client trust.
The strongest candidates at this point usually develop three visible strengths. They can test. They can explain. They can learn in public without sounding reckless. That might mean publishing sanitized lab writeups, contributing to community projects, presenting a local talk, or building a personal knowledge base around encryption standards, PKI components, VPN limitations and benefits, botnet structure, and DoS prevention. That breadth matters. Red teamers rarely operate inside one tidy technology box.
Quick Poll: What Result Are You Really Chasing With a Red Team Career?
Pick the pressure point that matters most. The smartest red team path changes when the goal changes.
4. Choose Certifications and Milestones That Actually Help
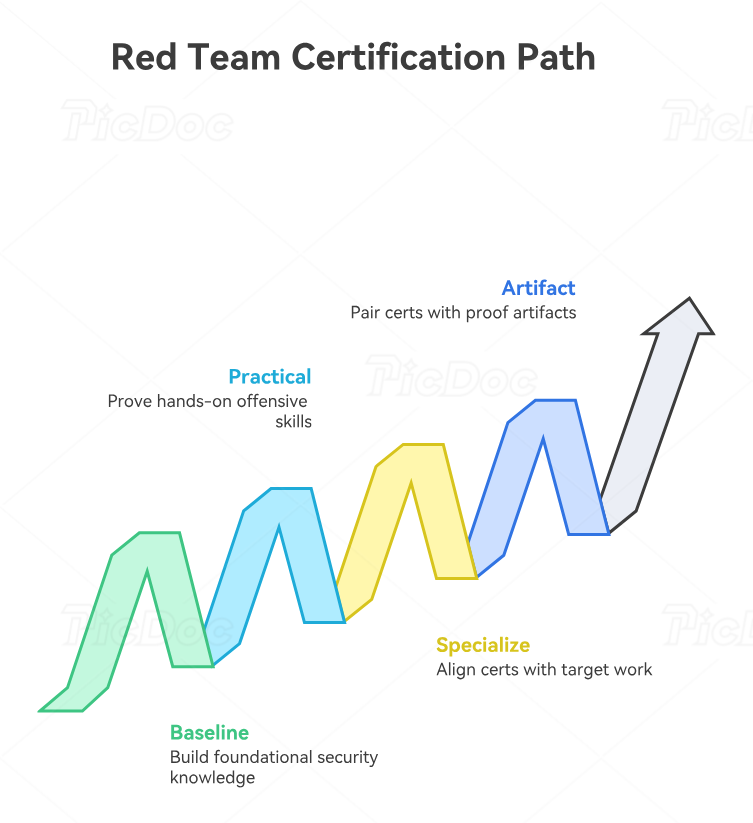
Certifications can help a red team candidate, but poor sequencing wastes enormous time. Early on, broad foundational proof can reduce hiring risk. Midway through the path, practical offensive proof becomes more valuable. Later, what matters most is not how many badges are on the résumé but whether they match the work being targeted. The ACSMI pieces on salary growth tied to certifications, the career impact of certifications, the entry-level to CISO salary progression analysis, and the article on future cybersecurity certifications employers may value most are useful because they frame certifications as leverage, not identity.
For a red team path, the strongest sequence often looks like this: first secure baseline cybersecurity fundamentals, then prove hands-on offensive competence, then deepen into specialization. Someone entering from general IT may begin with a fundamentals-oriented credential or broad security study path. Someone already in security can move more aggressively toward practical offensive certifications. OSCP-style validation often matters because it signals persistence, lab discipline, and technical problem solving. CEH may help in some HR filters, but it rarely carries the same technical weight in offensive circles. That is why candidates should compare the ACSMI resources on CEH preparation, OSCP-focused penetration testing growth, global cybersecurity training providers, and the broader cybersecurity job market trends before investing.
Still, credentials alone do not solve the biggest interview pain points. Hiring managers worry about operational judgment, report quality, and whether a candidate can function in real client or internal environments. So every milestone should have a paired proof artifact. After a lab-heavy certification, produce a better portfolio. After a reconnaissance or web-app phase, publish structured notes. After studying cloud identity, build a small hybrid attack-path simulation. After learning detection concepts, map likely red team activity to NIST-oriented defensive thinking, compliance realities, and the future of cybersecurity audit practices. That paired proof is what turns study into career movement.
5. Advance From Operator to Senior Red Team Value
Once a candidate can execute well, the next leap comes from becoming useful at a higher level than raw exploitation. Senior red team value lives in planning, realism, communication, and the ability to improve the organization after the exercise ends. A mature operator can design a threat-informed campaign, align with objectives, manage scope safely, collaborate with defenders when appropriate, and produce remediation guidance that engineering teams can act on without translating it first. That is why many senior operators eventually grow into purple teaming, adversary emulation leadership, internal security architecture influence, or consulting leadership.
This phase benefits from reading outside narrow offensive content. ACSMI’s guides on cybersecurity frameworks like NIST, ISO, and COBIT, the article on security audits, the guide to cybersecurity manager pathways, the roadmap from security manager to director of cybersecurity, and the path to CISO-level growth matter here. The point is not that every red teamer should leave technical work. The point is that senior technical credibility grows when the operator understands how the business organizes risk.
This is also where specialization can sharpen leverage. Some operators lean into cloud-heavy adversary simulation. Others grow into application security testing, identity-focused operations, social engineering, or threat-informed emulation. Market direction matters too. ACSMI’s pieces on the future of cloud security, AI-powered cyberattacks, deepfake threats, predicting demand for specialized cybersecurity roles, and future skills for cybersecurity professionals help candidates decide where offensive work is moving, not just where it has been.
The harsh truth is that many technically decent operators plateau because they never become easy to trust. They write weak reports. They miss business context. They create noise where precision was needed. They present findings dramatically instead of usefully. Promotion usually goes to the operator who can lead an exercise, protect the relationship, teach defenders something painful but actionable, and still hold technical respect.
6. FAQs
-
A SOC background helps, but it is not mandatory. What matters is whether you understand how defenders detect, escalate, investigate, and contain activity. A SOC role builds that quickly, which is why the ACSMI guides on becoming a SOC analyst, SOC-to-manager growth, and incident response careers are useful even for offensive candidates. A systems, network, or engineering background can also work if it produces the same operational depth.
-
It is not mandatory everywhere, but it remains one of the clearest practical signals for offensive discipline. It proves lab stamina, troubleshooting ability, and hands-on persistence. It does not prove full red team maturity on its own. That is why it should sit beside portfolio work, realistic labs, and communication skill. The ACSMI route for an OSCP-certified penetration tester is worth reviewing before you plan your study sequence.
-
They chase advanced tradecraft too early. A candidate who cannot explain Windows permissions, identity trust, network segmentation, logging, and basic detection logic is building on sand. The fix is boring in the best possible way: stronger fundamentals, cleaner documentation, deeper labs, and better understanding of endpoint detection, SIEM visibility, and threat intelligence analysis.
-
Yes, and many strong operators do. Those backgrounds build troubleshooting instincts, enterprise realism, and operating system depth. The transition becomes stronger when paired with offensive labs, web testing basics, Active Directory work, and proof through writeups. ACSMI’s article on moving from IT support to cybersecurity analyst is a solid stepping stone for that pivot.
-
Show structured evidence. Build a lab. Document attack paths. Publish sanitized writeups. Explain the defender view. Demonstrate clear methodology rather than flashy claims. A portfolio that connects recon, access, privilege escalation, lateral movement, reporting, and remediation will do far more for you than vague statements about passion. Pair that with smart study from free cybersecurity resources, trusted training providers, and career guides like the ACSMI path for ethical hacking.
-
Several strong paths open up: senior operator, adversary emulation lead, purple team specialist, security consultant, security engineering leadership, detection engineering collaboration, or longer-term executive growth. The best next move depends on whether your strength is technical depth, exercise design, communication, or organizational influence. ACSMI’s pathways toward cybersecurity manager roles, director-level leadership, and even CISO progression help frame what senior growth can look like.