How to Become a Threat Intelligence Analyst: Detailed Career Guide
Threat intelligence is where raw cyber noise turns into business-grade decision-making. Companies do not hire strong analysts just to collect indicators; they hire them to explain who is targeting them, why it matters, what is likely to happen next, and which response will reduce damage fastest. If you want a role that sits closer to real adversary behavior, strategic foresight, and high-trust security judgment, threat intelligence is one of the most leverage-rich paths in cybersecurity.
This guide breaks down exactly how to enter the field, what skills hiring teams actually respect, where most candidates fail, how to build a portfolio that proves you can think like an analyst, and which certifications create signal instead of résumé clutter. Along the way, you will see how this path connects to adjacent growth options such as SOC analyst, cloud security engineer, cybersecurity auditor, cybersecurity manager, and even long-range leadership tracks like CISO.
1. What a Threat Intelligence Analyst Actually Does and Why the Role Matters
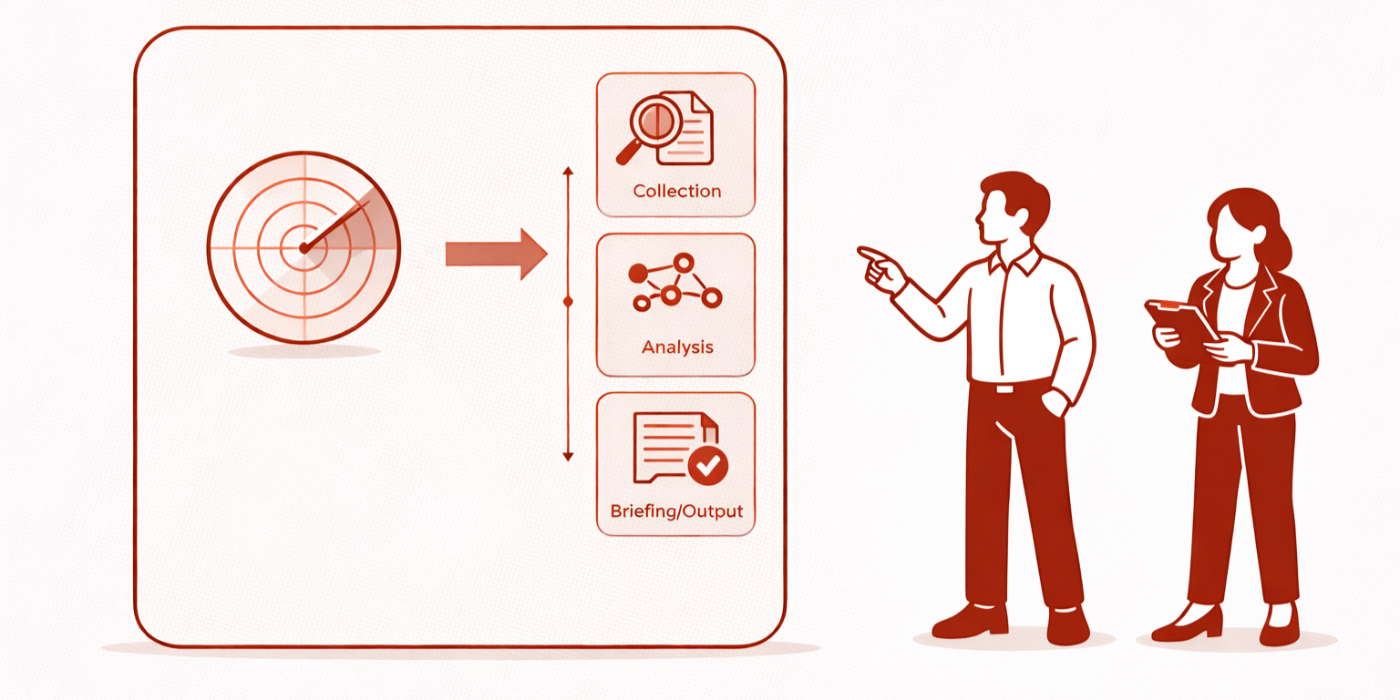
A threat intelligence analyst studies threat actors, intrusion patterns, malware campaigns, geopolitical drivers, attacker infrastructure, victimology, and adversary tradecraft to produce actionable intelligence for defenders. The job is not just “researching cyber threats.” It is translating technical and contextual evidence into decisions that improve detection, prioritization, resilience, and executive awareness.
In mature teams, threat intelligence sits between engineering, defense operations, risk, and leadership. That means a good analyst must understand how intelligence supports incident response plan development and execution, strengthens SIEM visibility, informs vulnerability assessment techniques and tools, improves ransomware detection, response, and recovery, and sharpens cyber threat intelligence collection and analysis.
The value of the role becomes obvious when defenders are drowning in alerts. Security teams fail when they cannot distinguish background internet noise from adversary activity that matches their sector, technology stack, or business exposure. Threat intelligence cuts through that chaos. It helps teams prioritize the attacker most likely to target them, the technique most likely to succeed, and the weakness most likely to be exploited next. That is why threat intelligence connects so naturally to broader market shifts discussed in predicting cyber threats by 2030, AI-powered cyberattacks and future defenses, deepfake cybersecurity threats, and future cybersecurity job market trends.
Another reason this role matters: it develops judgment. A junior defender may learn how to investigate alerts, but a strong intelligence analyst learns how campaigns evolve, how threat groups adapt when controls improve, how reporting biases distort the picture, and how to communicate uncertainty without sounding weak. Those are the skills that later open doors into SOC management, security consulting, cybersecurity compliance leadership, and long-term strategy roles tied to future skills for cybersecurity professionals.
Threat Intelligence Analyst Career Roadmap: 26 High-Value Skills, Tools, and Milestones
| Stage / Focus Area | What You Need to Build | Why It Matters in Hiring | Best Internal Learning Path |
|---|---|---|---|
| 1. Cyber basics | Networking, systems, authentication, logs | Without foundations, intelligence reports stay shallow | Study [firewall technologies](https://acsmi.org/blogs/firewall-technologies-types-and-configurations) and [VPN security](https://acsmi.org/blogs/virtual-private-networks-vpns-security-benefits-and-limitations) |
| 2. Threat landscape awareness | Actor categories, common motives, campaign types | Shows you can separate noise from targeted risk | Read [top threats by 2030](https://acsmi.org/blogs/top-10-cybersecurity-threats-predicted-to-dominate-by-2030) |
| 3. Log interpretation | Recognize suspicious authentication, DNS, proxy, endpoint patterns | Makes intel actionable for defenders | Review [SIEM overview](https://acsmi.org/blogs/security-information-and-event-management-siem-an-overview) |
| 4. OSINT collection | Source validation, collection discipline, relevance filtering | Hiring teams want analysts who do not just scrape headlines | Use [CTI collection and analysis](https://acsmi.org/blogs/cyber-threat-intelligence-cti-collection-and-analysis) |
| 5. Malware literacy | Families, loaders, delivery chains, evasion behavior | Improves actor and campaign attribution quality | Pair with [ransomware response](https://acsmi.org/blogs/ransomware-detection-response-and-recovery) |
| 6. ATT&CK-style thinking | Map techniques to detections and controls | Turns research into security value | Connect with [intrusion detection systems](https://acsmi.org/blogs/intrusion-detection-systems-ids-functionality-and-deployment) |
| 7. Reporting skill | Write clearly for technical and executive audiences | Weak writing kills strong analysis | Study leadership paths like [cybersecurity instructor](https://acsmi.org/blogs/how-to-become-a-cybersecurity-instructor-step-by-step-career-guide) |
| 8. Intelligence requirements | Know what stakeholders actually need answered | Prevents irrelevant “interesting but useless” intel | Learn from [security audits process and best practices](https://acsmi.org/blogs/security-audits-processes-and-best-practices) |
| 9. Sector context | Finance, healthcare, government, manufacturing exposure | Sector fluency increases hiring leverage | Compare [finance risks](https://acsmi.org/blogs/cybersecurity-trends-in-finance-predictive-insights-into-emerging-risks-20262030) and [healthcare predictions](https://acsmi.org/blogs/healthcare-cybersecurity-predictions-emerging-trends-risks-for-20262030) |
| 10. Adversary infrastructure analysis | Domains, hosting, certificates, pivots | Shows analytical depth beyond headlines | Pair with [PKI components](https://acsmi.org/blogs/public-key-infrastructure-pki-components-and-applications) |
| 11. Detection alignment | Recommend rules, hunts, watchlists, controls | Proves your intel can reduce risk | Use [next-gen SIEM](https://www.acsmi.org/blogs/next-gen-siem-future-cybersecurity-technologies-you-need-to-watch-20262030) |
| 12. Threat prioritization | Rank threats by business relevance, not drama | Mature teams reward practical judgment | Read [future compliance trends](https://acsmi.org/blogs/future-of-cybersecurity-compliance-predicting-regulatory-trends-by-2030) |
| 13. Cloud awareness | Identity abuse, storage exposure, cloud-native attack paths | Cloud knowledge is increasingly non-negotiable | Study [future of cloud security](https://acsmi.org/blogs/future-of-cloud-security-predictive-analysis-of-key-trends-20262030) |
| 14. Vulnerability context | Exploitability, chaining, exposure, asset criticality | Makes remediation advice credible | Use [vulnerability assessment techniques](https://acsmi.org/blogs/vulnerability-assessment-techniques-and-tools) |
| 15. Ransomware actor understanding | Initial access, extortion patterns, affiliate models | High-value in operational teams | Read [ransomware evolution by 2027](https://acsmi.org/blogs/predicting-the-next-big-ransomware-evolution-what-businesses-must-know-by-2027) |
| 16. AI threat awareness | Synthetic social engineering, scale, automation risk | Keeps your intelligence current | Use [AI-driven tools predictions](https://acsmi.org/blogs/ai-driven-cybersecurity-tools-predicting-the-top-innovations-for-20262030) |
| 17. Writing portfolio | Publish briefings, actor profiles, detection notes | Portfolio often beats generic certificates | Model structure from [cybersecurity curriculum developer](https://acsmi.org/blogs/career-roadmap-becoming-a-cybersecurity-curriculum-developer) |
| 18. Communication under uncertainty | Confidence calibration, caveats, scenario framing | Critical for trust with leadership | See pathways like [security manager to director](https://acsmi.org/blogs/career-roadmap-advancing-from-security-manager-to-director-of-cybersecurity) |
| 19. Defensive empathy | Know what SOC, IR, and engineering teams need | Intel must be usable, not decorative | Connect with [SOC analyst guide](https://www.acsmi.org/blogs/how-to-become-a-soc-analyst-step-by-step-career-guide) |
| 20. Governance awareness | Policies, risk framing, control language | Useful for regulated environments | Read [NIST, ISO, and COBIT frameworks](https://acsmi.org/blogs/cybersecurity-frameworks-nist-iso-and-cobit) |
| 21. Sector-specific reporting | Tailor intelligence to business model and exposure | Generic reports rarely create trust | Use [government sector predictions](https://acsmi.org/blogs/predictive-analysis-of-cybersecurity-in-government-public-sector-by-2030) |
| 22. Tool familiarity | Threat feeds, TIPs, SIEM, case management, enrichment tools | Shows operational readiness | Explore [top network monitoring and security tools](https://acsmi.org/blogs/top-network-monitoring-amp-security-tools-directory-2026-2027-updated) |
| 23. Presentation skill | Deliver concise updates to mixed audiences | Senior progression depends on this | See [cybersecurity instructor career guide](https://acsmi.org/blogs/complete-career-guide-to-becoming-a-cybersecurity-instructor-or-trainer) |
| 24. Certification discipline | Choose certs that support role direction | Avoids wasting time on low-signal stacking | Read [cybersecurity certifications of the future](https://acsmi.org/blogs/cybersecurity-certifications-of-the-future-what-employers-will-value-most-20262030) |
| 25. Career branching strategy | Know adjacent options like consulting, SOC, management, cloud | Improves long-term positioning | Compare [security consultant path](https://acsmi.org/blogs/complete-career-path-from-junior-penetration-tester-to-senior-security-consultant) |
| 26. Long-range market awareness | Track how demand is shifting across specialties | Smart candidates align with future demand early | Study [specialized role demand](https://www.acsmi.org/blogs/predicting-demand-for-specialized-cybersecurity-roles-ethical-hacking-threat-intelligence-20262030) |
2. Skills You Need First: The Core Foundation Before You Specialize
One of the biggest mistakes candidates make is trying to “become a threat intelligence analyst” before they understand the environments they are supposed to protect. Intelligence without technical grounding becomes recycled commentary. Hiring managers can spot that instantly. They see candidates who can repeat headlines about APT groups, but cannot explain how attacker behavior would appear in endpoint telemetry, cloud logs, email security data, or identity events.
Start with foundations. You need working knowledge of networking, operating systems, authentication flows, common enterprise architecture, and detection logic. Learn how access works, how logs are generated, how attackers move laterally, and how weak visibility creates blind spots. Core topics such as access control models, encryption standards, public key infrastructure, IDS deployment, and firewall configurations are not optional background reading; they are the grammar of credible intelligence.
Then build analytical skills. A threat intelligence analyst must collect, validate, compare, prioritize, and communicate. That requires disciplined note-taking, evidence handling, source skepticism, hypothesis testing, and clean writing. Good analysts distinguish observed facts from inferred judgments. Great analysts explain confidence levels. That difference matters when leadership is deciding whether to escalate, hunt, patch, isolate, notify, or simply monitor.
You also need adversary mindset. Study how campaigns form, how operators monetize access, why certain sectors are repeatedly targeted, and how techniques evolve when defenders get smarter. Deep dives into botnets and disruption methods, DoS attack prevention, data loss prevention strategies, application security tools, and endpoint security trends help you understand where intelligence becomes operationally useful.
Finally, build business context. Intelligence is stronger when it answers, “Why should this organization care?” A healthcare company, bank, manufacturer, retailer, and public-sector agency do not share the same exposure profile. Sector context changes reporting, prioritization, and executive relevance. That is why analysts who understand healthcare cybersecurity trends, finance cybersecurity risks, manufacturing sector security trends, retail and e-commerce risks, and government threat evolution often rise faster than candidates who only know generic threat names.
3. The Best Entry Routes Into Threat Intelligence Without Wasting Years
Most people do not start in threat intelligence directly. They transition into it. The strongest feeders are SOC, incident response, vulnerability management, OSINT-heavy research, malware analysis support, and cyber risk functions that require external threat awareness. If you are early in your journey, roles connected to SOC operations, security consulting, cybersecurity auditing, compliance officer pathways, and ethical hacking preparation can all create relevant stepping stones.
The SOC route is especially powerful because it teaches pattern recognition. You see alerts, false positives, noisy telemetry, attacker behavior, and incident pressure in real time. That experience makes your later intelligence work less theoretical. You start recognizing what defenders actually need from intelligence: fewer vanity reports, more usable context. That is why many strong intelligence professionals either began in a SOC or worked very closely with one, then expanded toward SOC manager progression or broader operational leadership.
A second route is research-first. Some candidates are naturally strong at analysis, writing, trend tracking, and source triangulation. They may come from journalism-style research, policy, open-source investigations, or security content development. That path can work, but only if it is grounded in technical reality. Without that, your reports will sound polished but weak. To avoid that trap, connect your research to security frameworks, security audits, incident response execution, and threat intelligence collection methods.
A third path is specialization. Candidates with cloud security exposure, fraud intelligence experience, geopolitical analysis, or malware research can pivot into intelligence when they frame their skills correctly. Someone with cloud focus may connect well with cloud security career pathways and future cloud security trends. Someone interested in IoT or sector-specific research may benefit from IoT security specialist careers or energy and utilities cybersecurity predictions.
The pain point here is that candidates often wait for permission. They assume they need a job title first. They do not. If you can produce actor profiles, campaign analyses, sector threat summaries, and intelligence-driven detection ideas, you can begin acting like an intelligence analyst before your résumé says so.
Quick Poll: What Is the Hardest Part of Breaking Into Threat Intelligence?
Pick the obstacle that feels most real, because the right career plan depends on the bottleneck.
4. Certifications, Projects, and Portfolio Moves That Actually Create Leverage
Certifications help, but only when they support a visible story. A certificate by itself does not prove you can reason through adversary behavior, assess source credibility, or produce stakeholder-ready intelligence. It proves you studied. That has value, but it is not enough.
For early-career candidates, foundational certs can help reduce hiring friction, especially when paired with demonstrable work. More important than stacking random credentials is choosing certifications that reinforce your direction. The broader lesson from cybersecurity certifications of the future is that employers increasingly reward relevance, application, and judgment over empty accumulation. If you are coming from operations, a baseline security cert plus intelligence portfolio pieces can be more powerful than three unrelated badges. If you are transitioning from research, technical validation matters more.
Your portfolio is where real leverage is built. Publish short threat briefings. Write a monthly sector threat summary. Take one major ransomware group and explain its access methods, monetization pattern, and likely detection opportunities. Review ransomware evolution trends, compare them with AI-powered attack trends, and build your own structured view of how campaign scale and deception are changing. That kind of work signals analytical maturity.
Also build actionable deliverables, not just descriptive ones. For example, after studying deepfake threats, create an intelligence note on executive impersonation risk for a healthcare firm. After reading privacy regulation trends and GDPR evolution, write a short brief showing how threat reporting should adapt for regulated environments. After reviewing zero trust innovation, produce a note explaining how intelligence can influence control prioritization.
This is where many candidates miss the mark. They produce content that is interesting but not useful. Hiring teams want to see whether you can answer questions like these: Which actor matters most to this organization? Which technique is most relevant to its environment? What should defenders monitor this month? What changed since last quarter? Which assumptions are weak? Those are intelligence questions. When your portfolio starts answering them, your candidacy becomes harder to ignore.
5. A Realistic Step-by-Step Career Plan From Beginner to Trusted Threat Intelligence Analyst
Start by choosing your base lane. If you are brand new, target an operations-friendly role or build the equivalent knowledge independently. Spend serious time on networking, authentication, system behavior, logging, and enterprise attack paths. Use resources connected to SOC work, incident response, SIEM operations, and vulnerability analysis until security telemetry feels interpretable, not mysterious.
Next, build intelligence habits. Track one threat actor cluster, one malware family, one sector, and one technique category for 60 to 90 days. Write weekly notes. Force yourself to separate fact from assumption. Identify what would matter to a SOC, what would matter to leadership, and what is just noise. Read strategically across future threat predictions, specialized role demand, automation and workforce shifts, and remote cybersecurity career trends so your understanding stays market-aware.
Then create public proof. Publish three to five strong pieces instead of twenty shallow ones. A candidate with five sharp reports is often stronger than one with endless generic posting. Your work should show source discipline, analytical structure, technical grounding, and communication range. Include one executive brief, one operational brief, one actor profile, one sector risk analysis, and one “what defenders should do next” memo. That portfolio begins to resemble the work intelligence teams actually need.
After that, sharpen adjacent strength. Learn how intelligence supports security audits, compliance priorities, managed security services, and security awareness platforms. Mature analysts do not live in a silo; they understand how their work influences prevention, detection, governance, training, and executive reporting.
Finally, think long-term. Threat intelligence can branch into threat hunting, detection engineering, strategic intelligence, cyber risk, consulting, security leadership, and niche specialties. That is why this path pairs well with later transitions into cybersecurity manager roles, director-level progression, cybersecurity auditor tracks, and even executive strategy through the CISO pathway. The skill that compounds across all of them is judgment under uncertainty. Threat intelligence trains that better than most roles.
6. FAQs About Becoming a Threat Intelligence Analyst
-
No, but SOC experience is one of the strongest entry routes because it teaches what real defensive teams need from intelligence. It helps you understand alert fatigue, telemetry quality, incident pressure, and operational prioritization. Candidates without SOC exposure can still break in, but they must compensate with stronger technical grounding, better reporting samples, and clearer evidence that they can make intelligence actionable rather than theoretical.
-
It is both, and weak candidates usually lean too hard to one side. Purely technical candidates may miss strategic significance, source quality, and stakeholder communication. Purely analytical candidates may produce elegant reports that defenders cannot use. The sweet spot is technical enough to understand attacker behavior and operational enough to recommend action, while analytical enough to interpret trends, uncertainty, and business relevance.
-
Include an actor profile, a campaign summary, a sector-specific risk brief, an executive one-pager, and at least one intelligence-to-detection memo. Tie your thinking to areas such as CTI collection and analysis, incident response, SIEM operations, and future threat trends. Employers want to see how you think, not just what you know.
-
The best certifications are the ones that reinforce your gap. If you lack security fundamentals, start there. If you already have operations experience, choose credentials that add intelligence relevance or strengthen an adjacent specialty. Avoid stacking certificates with no coherent story. A cert becomes more valuable when it sits next to strong writing samples, technical familiarity, and visible analytical discipline.
-
Absolutely. Threat intelligence can lead into strategic intelligence leadership, threat hunting, consulting, cyber risk, SOC leadership, governance, sector-specialized advisory work, and executive security planning. Because the role develops communication, prioritization, and adversary-centered thinking, it creates strong preparation for manager pathways, director advancement, and eventually the CISO track.
-
Trying to look informed instead of becoming useful. Many candidates consume endless threat news, repeat popular talking points, and chase attribution drama, but they never learn how to translate intelligence into better decisions. The strongest analysts focus on relevance, clarity, confidence levels, and action. They do not just ask, “What happened?” They ask, “Why does it matter here, what changes next, and what should defenders do now?”