Detailed Career Guide: Becoming a Cybersecurity Bootcamp Instructor
Becoming a cybersecurity bootcamp instructor is one of the strongest career pivots for professionals who already have real-world security experience, strong pattern recognition, and the patience to make difficult ideas usable for beginners. The opportunity is larger than “teaching classes.” Bootcamps need instructors who can translate live operations, hiring expectations, certification pressure, and rapidly changing tools into training that gets students interview-ready. This guide shows how to build that transition deliberately, prove credibility, create teaching assets, and position yourself for instructor roles that actually grow your long-term career.
1. What a Cybersecurity Bootcamp Instructor Actually Does and Why Many Practitioners Misread the Role
A cybersecurity bootcamp instructor does far more than explain tools on slides. The real job sits at the intersection of practitioner credibility, structured teaching, student confidence-building, employer expectations, and curriculum execution. Bootcamps hire people who can take what matters in SOC analyst work, incident response, cloud security engineering, and cybersecurity compliance analysis and turn it into a sequence students can actually absorb under time pressure.
That difference matters because many experienced professionals assume subject matter depth alone is enough. Bootcamps rarely need another person who can impress a room of experts for twenty minutes. They need someone who can explain why security information and event management, vulnerability assessment techniques, incident response planning, and cyber threat intelligence collection matter to entry-level learners who still confuse terminology, overestimate tool importance, and underestimate process discipline.
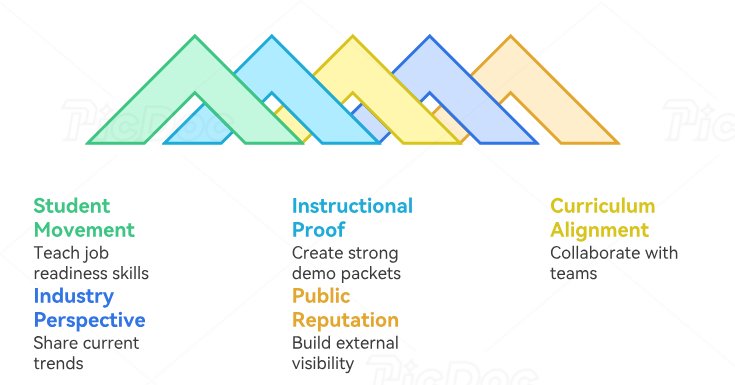
The strongest instructors also understand that bootcamp teaching is attached to outcomes. Students join programs because they want movement: a better job, a cleaner transition from IT, a first role in security, a stronger foundation for certifications, or a practical bridge into specialized paths like ethical hacking, OSCP-focused penetration testing, threat intelligence analysis, or cybersecurity auditing. A good instructor teaches content. A great instructor teaches decisions, confidence, judgment, and employability.
This role also attracts professionals who are tired of pure operations. Someone coming from SOC analyst to SOC manager growth, from the security analyst to cybersecurity engineer path, from IT support into cyber analysis, or from a senior cybersecurity analyst track often wants work with more leverage. Teaching can provide that leverage because one good instructor shapes dozens or hundreds of future practitioners through labs, frameworks, feedback, and standards.
What makes the role difficult is that it exposes every weak spot fast. If your knowledge is shallow, students feel it. If your explanations are messy, students drift. If you cannot connect the classroom to current hiring realities, your sessions feel academic. Bootcamps therefore value instructors who understand future cybersecurity skills employers will reward, the cybersecurity job market trendline, the cybersecurity workforce shortage, and the kinds of certifications employers respect. That context lets you teach the student in front of you and the role they are trying to reach.
Cybersecurity Bootcamp Instructor Readiness Matrix: 26 Areas You Need to Prove
| Readiness Area | What Bootcamps Want to See | How You Can Prove It | Common Mistake |
|---|---|---|---|
| 1. Technical foundation | Broad understanding of defensive security workflows | Show experience in operations, labs, projects, or applied training | Listing tools without showing judgment |
| 2. Role clarity | Understanding of the jobs students want | Teach using real tasks from analyst, engineer, or GRC roles | Teaching theory disconnected from hiring realities |
| 3. Beginner empathy | Ability to simplify without dumbing down | Use layered explanations and examples | Talking at expert speed from minute one |
| 4. Instructional structure | Clear sequencing from concept to practice | Build modules with objective, demo, lab, debrief, checkpoint | Jumping between topics with no learning arc |
| 5. Live teaching presence | Calm communication and class control | Record sample lessons and manage Q&A clearly | Sounding scattered under student questions |
| 6. Lab design | Hands-on exercises that reinforce the lesson | Create guided labs with expected outcomes and failure notes | Using labs that feel flashy and teach little |
| 7. Assessment quality | Ability to measure understanding accurately | Write quizzes, scenario prompts, and practical checks | Testing memorization instead of reasoning |
| 8. Feedback skill | Specific, actionable student feedback | Annotate submissions and explain how to improve | Saying “good job” without guidance |
| 9. Career alignment | Connection between class tasks and real interviews | Map labs to entry-level job expectations | Ignoring resume and interview relevance |
| 10. Certification awareness | Practical knowledge of common certification paths | Explain where certifications help and where practice matters more | Overselling credentials as a magic fix |
| 11. Curriculum discipline | Ability to follow or improve a syllabus | Show lesson maps and revision suggestions | Freelancing every class with no consistency |
| 12. Tool adaptability | Comfort teaching changing platforms and interfaces | Demonstrate concept-first teaching across tools | Building the whole class around one vendor UI |
| 13. Compliance fluency | Ability to explain controls and governance simply | Use real examples from frameworks and audits | Treating compliance as dry paperwork |
| 14. Incident reasoning | Ability to teach decisions during pressure | Use tabletop walk-throughs and case reviews | Teaching steps without showing prioritization |
| 15. Documentation quality | Clear notes, answer keys, and lab guides | Create clean instructor and student versions | Messy materials that confuse students |
| 16. Classroom pacing | Ability to keep weaker learners engaged without losing stronger ones | Use checkpoints and stretch tasks | Letting half the room get lost |
| 17. Remote teaching readiness | Comfort with online delivery and engagement | Use polls, breakout prompts, and live troubleshooting | Reading slides in a flat voice |
| 18. Credibility signals | Public proof of expertise and clarity | Publish lessons, demos, guides, or mini-courses | Having strong knowledge with zero visible evidence |
| 19. Student support mindset | Patience with repeat confusion and skill gaps | Show office hours, mentoring, or coaching experience | Becoming visibly irritated by basic questions |
| 20. Hiring manager awareness | Real sense of what gets students hired | Teach portfolio, lab writeups, and interview explanations | Focusing on content completion only |
| 21. Specialty depth | Recognizable strength in one or two lanes | Anchor your teaching brand around a practical specialty | Trying to appear expert in every domain |
| 22. Updating ability | Willingness to refresh lessons as the field changes | Revise content based on trends and tool shifts | Using stale labs year after year |
| 23. Collaboration | Ability to work with curriculum teams and support staff | Share revisions, notes, and student issue patterns | Acting like a solo operator inside a program |
| 24. Outcome ownership | Focus on student progress, retention, and readiness | Track weak spots and improve modules | Measuring success by “covered the slides” |
| 25. Leadership potential | Capacity to mentor junior instructors later | Standardize teaching assets and playbooks | Keeping everything inside your head |
| 26. Long-term value | Ability to grow from instructor into program leader or curriculum owner | Build systems, not one-off classes | Thinking of the role as delivery only |
2. The Step-by-Step Path From Cybersecurity Practitioner to Bootcamp Instructor
Most people reach this role through one of three routes. The first is the practitioner route: you already work in security and want to turn your field experience into teaching. This is common for professionals coming from security operations, ethical hacking and penetration testing, cloud security engineering, or cybersecurity management. The second is the mentor route: you become known for helping teammates, onboarding juniors, leading study groups, or explaining messy workflows clearly. The third is the curriculum route: you start creating lesson plans, labs, and training systems before you ever hold the formal instructor title, which aligns closely with the path to cybersecurity curriculum developer and the broader step-by-step pathway to become a curriculum developer.
The first major step is choosing the lane you can teach with authority. Bootcamps prefer instructors who can own something concrete. That could be foundational defensive security, blue-team operations, GRC, cloud security, security awareness, threat hunting, or entry-level pentesting. Someone with depth in firewall technologies, intrusion detection systems, data loss prevention strategies, and access control models has a credible base for defensive instruction. Someone with stronger offensive skills may anchor around penetration testing tools, vulnerability scanners, ethical hacker career paths, and the junior penetration tester to consultant track.
The second step is turning tacit knowledge into teachable structure. Practitioners often know what to do and why it works, yet bootcamps need that knowledge packaged into objectives, exercises, answer keys, pacing blocks, and review checkpoints. One useful way to build that discipline is to study the role of cybersecurity instructor or trainer, compare delivery styles from the best cybersecurity bootcamps and academies, examine the global directory of cybersecurity training providers, and borrow learning inputs from free cybersecurity courses and resources. The goal is not to copy materials. The goal is to understand what makes a lesson easy to follow, practical to run, and useful to students under pressure.
The third step is building visible proof before you apply. Bootcamps love candidates who already behave like instructors. Create a short lesson on SIEM fundamentals, record a case-based walkthrough on ransomware detection and recovery, write a beginner guide that simplifies public key infrastructure, or build a practice lab around encryption standards like AES and RSA. Add explanation, sequencing, common errors, and what “good” output looks like. This gives hiring teams something far stronger than a résumé claim.
The fourth step is aligning yourself with the student outcomes the market actually rewards. A bootcamp instructor should understand entry-level and growth-stage role maps. That includes the route from IT support to cybersecurity analyst, the climb from SOC analyst to SOC manager, the shift into compliance officer work, and even longer-range paths like director of cybersecurity advancement or the CISO track. Students trust instructors who can explain where today’s lab leads tomorrow.
3. Skills, Teaching Systems, and Portfolio Assets That Make Bootcamps Trust You
The first skill that separates strong instructor candidates is explanation design. You need to know how to teach difficult concepts in layers. Start with the plain-language purpose, move to the operating concept, show the workflow, then run the lab, then debrief the mistakes. This structure works especially well when teaching cybersecurity frameworks like NIST, ISO, and COBIT, security audits and best practices, cybersecurity compliance trends, and future cybersecurity audit practices. Those areas intimidate beginners because the language feels abstract until a teacher gives it operational shape.
The second skill is lab realism. Bootcamp students need practice that looks close enough to real work to build usable instincts. That does not require enterprise-scale infrastructure. It requires intentional design. A lab on incident response planning should teach prioritization, communication, containment logic, and documentation. A lab on botnet disruption methods or denial-of-service mitigation should show traffic reasoning, detection clues, defensive thinking, and the limits of simplistic answers. A lab on endpoint security or cloud environment threats should teach students how to interpret signals, not admire dashboards.
The third skill is industry translation. Students are hungry for clarity on what employers actually value. A credible instructor can connect lesson content to the cybersecurity salary landscape, the salary progression from entry level to CISO, the impact of certifications on advancement, and the future cybersecurity job market. That does two things at once. It keeps motivation high, and it teaches students which skills compound.
The fourth skill is content currency. Bootcamps do not need perfect futurists, yet they do need instructors who know where the field is moving. Students expect perspective on AI-powered cyberattacks, deepfake cybersecurity threats, the future of zero trust, and AI-driven cybersecurity tools. They also need grounded explanation on why fundamentals still matter even when tools and headlines shift. That balance makes instruction feel serious rather than trend-chasing.
The fifth skill is teaching asset creation. A strong candidate should build a portfolio containing sample slides, lab guides, rubric sheets, troubleshooting notes, quiz questions, office-hour prompts, and short lesson clips. Support that portfolio with learning inputs from top cybersecurity books, industry podcasts, YouTube channels for cybersecurity learning, and the best cybersecurity blogs and news sites. Bootcamps trust instructors who clearly invest in their own teaching craft.
Quick Poll: What Is the Biggest Thing Delaying Your Move Into Cybersecurity Instruction?
Choose the barrier that feels most real right now. The right transition strategy depends on the obstacle.
4. How to Get Hired by a Cybersecurity Bootcamp
The first thing hiring teams look for is evidence that you can create student movement, not merely deliver information. In interviews, talk about how you would teach toward job readiness. That means connecting modules to entry-level analyst roles, security engineering growth, compliance pathways, and cloud security careers. Explain how you would help students speak about a lab in an interview, troubleshoot a task under time pressure, and distinguish tool familiarity from actual security reasoning.
The second hiring lever is visible instructional proof. Create a strong demo packet. Include a short recorded lesson, a live-teaching outline, a lab exercise, a debrief document, and a one-page teaching philosophy. Use topics with immediate relevance, such as security awareness training platforms, best SIEM solutions, best cloud security tools, and leading endpoint security providers. The point is not to review products. The point is to show you can translate market categories into student-ready decisions, comparisons, and practical workflows.
The third lever is alignment with curriculum teams. Bootcamps need instructors who can collaborate with program managers, curriculum developers, teaching assistants, and career support staff. Show that you understand sequence, consistency, and revision. This is where familiarity with cybersecurity curriculum developer work, the broader cybersecurity instructor guide, training provider ecosystems, and the bootcamp landscape becomes useful. Hiring managers trust candidates who already think in systems.
The fourth lever is current industry perspective. Hiring teams want to know that your examples will feel relevant six months from now, not fossilized. Bring intelligent perspective on remote cybersecurity career trends, automation and the future workforce, specialized role demand, and future certifications employers will value. Students feel safer with instructors who understand both today’s role expectations and tomorrow’s movement.
The fifth lever is your reputation outside the application itself. Publish useful content. Run a webinar. Lead a study group. Build a practice lab repo. Offer micro-lessons based on top cybersecurity books, top cybersecurity podcasts, industry research organizations, and the best cybersecurity conferences. Visibility lowers hiring risk. Bootcamps are much more comfortable with candidates who already look like instructors in public.
5. Salary Growth, Long-Term Career Value, and How Instruction Can Expand Your Future Options
A cybersecurity bootcamp instructor role can create income and career leverage in several ways. For some professionals, it becomes a full-time track with room to grow into lead instructor, curriculum owner, program director, or education-focused security leader. For others, it becomes a parallel lane that strengthens consulting, content, coaching, or recruiting value. The smartest way to view compensation is through range and leverage, which is why it helps to understand the global cybersecurity salary report, remote versus on-site salary differences, the cybersecurity freelance and consulting market, and the salary growth tied to major certifications.
What makes teaching especially valuable is that it compounds adjacent strengths. Instructors get better at communication, curriculum design, assessment, mentoring, and public authority. Those strengths carry directly into cybersecurity management, director-level advancement, VP of cybersecurity progression, and even the CISO path. The instructor title does not shrink a strong career when the work stays practical and the field connection stays active. It can actually strengthen leadership readiness because teaching forces clarity, structure, and repeated explanation of risk and controls.
Instruction also opens doors into educational product design. Someone who becomes excellent at teaching labs, updating coursework, and diagnosing where students fail can evolve into curriculum development, training operations, certification prep design, or education strategy. This becomes even more valuable as the field absorbs AI-driven cybersecurity tools, new cloud security patterns, the next generation of cybersecurity standards, and rising demand for structured reskilling through training providers. The people who can convert industry change into teachable systems become strategically useful.
There is also brand value in being a respected teacher. Students, hiring managers, course platforms, conferences, and cybersecurity communities pay attention to instructors who teach clearly and practically. That brand can support future work in consulting firms, managed security service providers, small-business security services, or specialized markets like healthcare cybersecurity and financial services cybersecurity. Teaching turns expertise into reputation. Reputation creates optionality.
6. FAQs About Becoming a Cybersecurity Bootcamp Instructor
-
You need credible practical understanding, teaching discipline, and the ability to simplify complex topics clearly. Seniority helps, yet it is the combination of real-world context, student empathy, and strong instructional structure that matters most. Studying paths like how to become a cybersecurity instructor, the complete career guide to becoming a trainer, the bootcamp and academy landscape, and the training provider directory will show how programs value applied clarity.
-
Several do. Defensive operations, GRC, cloud security, security engineering, and offensive security all create strong paths. A SOC analyst background, a cloud security engineer track, a compliance analyst roadmap, or an ethical hacker path can all work when you can translate the work into student-ready lessons and labs.
-
They usually want practitioner credibility, classroom control, student empathy, lesson structure, lab quality, and visible instructional proof. That proof can include sample lessons, recorded teaching clips, lab guides, or curriculum notes. Reviewing the cybersecurity instructor guide, the curriculum developer path, the best cybersecurity bootcamps and academies, and the future skills employers will value helps you align your profile with what programs actually need.
-
They matter as supporting proof, especially when they match the material you teach or the roles students want. Their value grows when combined with practical teaching assets. Use the certifications directory, the career advancement report on certifications, the salary growth analysis for major certifications, and the future certification outlook to choose strategically.
-
Build visible proof before you apply. Record short lessons. Design one or two solid labs. Publish a practical guide. Mentor learners. Lead study sessions. Create rubrics and troubleshooting notes. This mirrors the growth patterns seen in the trainer career guide, the curriculum developer path, free course ecosystems, and the broader cybersecurity learning content landscape.
-
It can strengthen it when you stay connected to real practice, keep your material current, and turn teaching into systems, mentoring, and curriculum leadership. Teaching sharpens communication, management, and structured thinking. Those are strong assets for cybersecurity management, VP-level progression, director advancement, and even the CISO track.
-
Include a sample syllabus, one or two lesson decks, a hands-on lab, an answer key, a rubric, a recorded lesson clip, student feedback examples if available, and a short document explaining how you teach for job readiness. Strengthen that portfolio with informed perspective from cybersecurity blogs and industry news, research institutes, podcasts, and cybersecurity conferences. A strong portfolio shows how you think, teach, and improve outcomes.