Cybersecurity Incident Responder Career Path: Complete Guide & Salary Outlook
Incident response attracts a certain kind of security professional. Not the one who wants abstract theory, and not the one who wants a quiet checklist life. This path rewards people who can think under pressure, move through messy evidence, make disciplined decisions with incomplete information, and help organizations regain control when systems, data, and trust are all on the line.
That intensity is exactly why this career path creates strong long-term value. Incident responders sit close to real business pain, real technical failures, and real executive urgency. The analysts who grow well in this lane build rare judgment fast, and that judgment can open doors into senior response roles, threat hunting, detection engineering, security leadership, consulting, and high-trust specialist work.
1. What the Incident Responder Role Really Looks Like in Practice
A lot of people imagine incident response as dramatic breach handling and midnight war rooms. Those moments exist, but they are only a fraction of the job. Real incident response is disciplined triage, evidence preservation, timeline building, containment decision-making, root cause analysis, stakeholder coordination, and post-incident improvement. It sits at the intersection of technical analysis and operational control.
The fastest way to understand the role is to study the pathway to cybersecurity incident responder roles, the incident response plan development and execution guide, the cybersecurity incident response report on effectiveness and improvements, and the complete guide to becoming a SOC analyst. Those resources show how incident response grows from alert triage into deeper investigative ownership.
In practical terms, responders spend time analyzing suspicious activity, validating whether something is a real incident, determining scope, assessing affected assets, gathering logs and artifacts, and coordinating with IT, infrastructure, cloud, legal, compliance, and leadership. That means responders must understand more than indicators. They need fluency in SIEM workflows, intrusion detection systems, endpoint security controls, network monitoring tools, and firewall technologies and configurations.
This role also demands stronger judgment than many people expect. In incident response, technical accuracy matters, but decision quality matters just as much. A responder has to know when an event is contained enough to avoid unnecessary business disruption, when a compromise is broad enough to justify aggressive isolation, when evidence is clean enough to support confident escalation, and when uncertainty needs to be stated plainly rather than disguised behind jargon.
That is where many professionals stall. They learn tools, memorize playbooks, and practice ticket handling, yet never grow into the person others trust during the messy middle of an incident. The messy middle is the job. It is where half the evidence is incomplete, the pressure is rising, executives want answers early, and rushed assumptions can make the situation worse.
The good news is that this path compounds fast for people who build operational calm, investigative depth, and clean communication. Incident response is one of the clearest examples in cybersecurity where repeated exposure to difficult situations can quickly increase your market value.
2. The Skills You Need Before You Can Grow Into a Serious Incident Response Career
Incident response is brutally revealing. Weak log analysis gets exposed fast. Sloppy documentation gets exposed fast. Unclear thinking gets exposed fast. That is why the path starts with technical fundamentals that hold up when events are noisy and timelines are messy.
First, responders need strong visibility instincts. You should understand how to extract meaning from SIEM events, how endpoint alerts fit into EDR workflows, how network clues show up in IDS deployments, and how network monitoring and security tools complement one another during scoping. Many early-career responders know one console well and mistake that for broad investigative readiness. Real response work demands more connective tissue than that.
Second, responders need to understand control and architecture basics. You cannot diagnose failure well if you do not understand what was supposed to protect the asset in the first place. Study access control models, firewall technologies, VPN security limitations, PKI components and applications, and encryption standards. This turns your investigations from symptom-chasing into actual failure analysis.
Third, incident responders need attack-pattern familiarity. You do not need to become a malware reverse engineer on day one, but you do need to understand how common threats behave. That is where resources on ransomware detection response and recovery, botnet structure and disruption, DoS mitigation, and phishing trends and prevention become practical rather than theoretical. Attack familiarity helps you spot what matters faster and stop wasting time on low-value noise.
Fourth, communication is a hard skill here, not a soft extra. A responder may need to brief a manager, sync with infrastructure, ask legal for guidance, request cloud action from another team, or explain why a containment action cannot wait. Readable case notes and concise updates are not administrative chores. They are part of the response surface. The responder who can explain risk clearly gets pulled into bigger incidents sooner.
3. Certifications, Entry Routes, and Salary Outlook for Incident Responders
There is no single doorway into incident response. Many professionals arrive from SOC analysis, IT support, system administration, network operations, or broader security analyst roles. That is why the best route is often the one that converts your current strengths into responder-ready judgment the fastest.
For people entering from operations or support, the how to transition from IT support to cybersecurity analyst article is useful because it explains how foundational troubleshooting instincts can become security analysis leverage. From there, the career pathway to a senior cybersecurity analyst, the security analyst to cybersecurity engineer path, and the threat intelligence analyst career guide help frame adjacent growth options once response experience starts to deepen.
Certification strategy should support the response path, not distract from it. Foundational credentials can help you break in, especially when paired with hands-on labs and clean case thinking. Mid-level and advanced certifications become more valuable when they prove operational depth or specialty direction. The top cybersecurity certifications directory, the impact of cybersecurity certifications on career advancement report, and the salary growth analysis for CISSP CEH and security certifications help you decide whether a credential supports immediate responder growth, future specialization, or long-term management positioning.
As for salary outlook, incident response tends to reward depth, urgency tolerance, and specialization. Professionals who only validate alerts are competing in a broader pool. Professionals who can scope compromise, lead containment, influence post-incident improvement, and communicate with authority tend to move into better-paying roles much faster. To understand the broader financial picture, review the global cybersecurity salary report, the cybersecurity job market trends and salary predictions, the remote versus on-site cybersecurity salaries analysis, and the entry-level to CISO salary progression analysis. Those reports reinforce a clear pattern: pay rises fastest when responders add specialized judgment, cross-functional influence, and visible ownership of outcomes.
The salary ceiling also expands when you move into sectors with more sensitive environments, stricter regulations, or heavier breach exposure. Finance, healthcare, public sector, and critical infrastructure often place a premium on responders who can handle pressure without losing discipline.
Quick Poll: What Is Driving You Toward Incident Response?
Choose the real pressure point. The best incident response path depends on what you want the role to unlock.
4. How Incident Responders Advance Into Senior and Specialist Roles
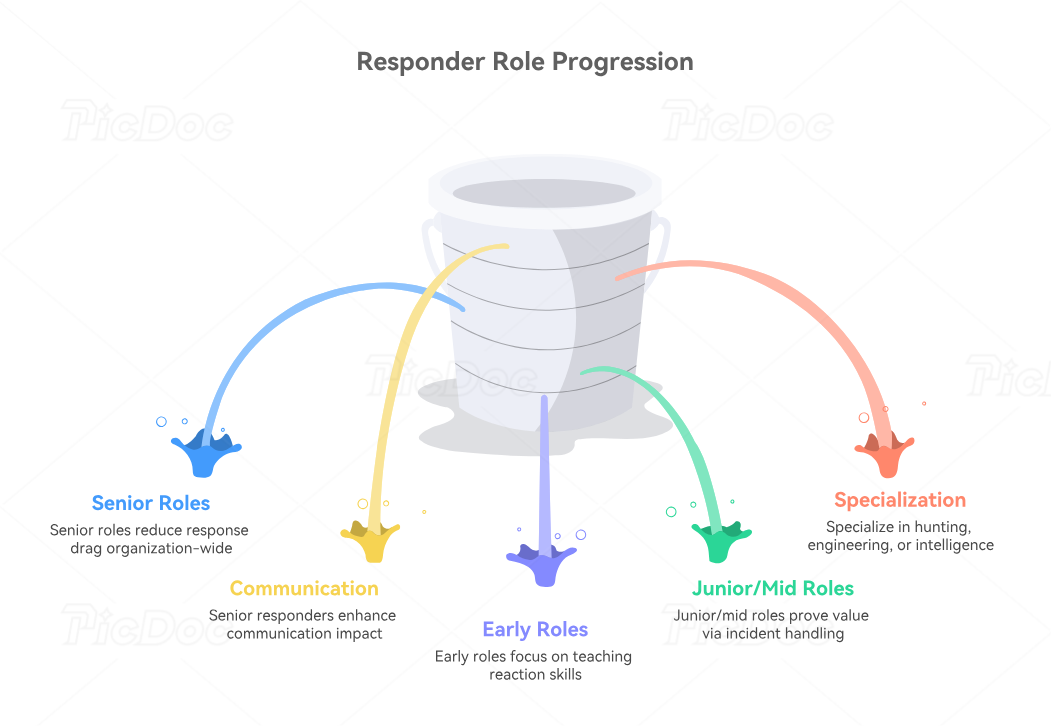
Early response roles teach you how to react. Senior response roles reward people who improve the organization’s overall resilience. That is a major difference, and understanding it early helps you grow with more intention.
A junior or mid-level responder often proves value by handling incidents carefully, documenting cleanly, and escalating well. A senior responder proves value by reducing response drag across the organization. That can mean refining playbooks, improving detection feedback loops, shaping tabletop exercises, strengthening communication templates, mentoring junior staff, or influencing tool and process decisions. Reports like the state of ransomware analysis, the data breach report on industries most at risk, the annual insider threats report, and the emerging cloud threats analysis are valuable here because they help responders anchor process improvements to actual threat realities.
Specialization usually opens next. Some responders move toward threat hunting through stronger hypothesis-driven investigation. Some move toward detection engineering by feeding better logic back into rules and pipelines. Some move toward threat intelligence by becoming better at adversary pattern interpretation. Some move toward governance and compliance when incident evidence, reporting, and control failure analysis become central to their work. Paths such as cybersecurity compliance analyst, cybersecurity auditor, cloud security engineer, and cybersecurity manager become more realistic once response experience gives you broader organizational context.
This is also where communication becomes a multiplier. Senior responders do not merely know more. They make the room calmer. They help others see the path forward, frame uncertainty honestly, and stop organizations from making expensive decisions based on panic.
5. The Smartest Ways to Increase Your Earning Power as an Incident Responder
Responder salaries grow fastest when your work becomes harder to replace. That usually means three things: deeper technical range, stronger stakeholder trust, and sharper specialization. Simply surviving lots of incidents is not enough. You need to turn that experience into repeatable leverage.
One lever is industry specialization. Incident responders who understand the operational realities of finance, healthcare, education, government, utilities, or manufacturing can become more valuable than equally technical responders with generic exposure. Explore the best cybersecurity firms for financial services, the directory of leading healthcare cybersecurity firms, the cybersecurity solutions directory for small businesses, the best cybersecurity companies for energy and utilities, and the best cybersecurity solutions for manufacturing and industrial firms. Vertical context helps you understand what kinds of incidents matter most, what business disruptions hurt hardest, and which containment decisions carry the heaviest tradeoffs.
Another lever is future relevance. Incident response is evolving as tooling, attack patterns, and regulatory expectations change. Stay ahead by reading the AI-powered cyberattacks predictions, the deepfake cybersecurity threats report, the future of cloud security predictive analysis, the privacy regulations and cybersecurity emerging trends, and the future of cybersecurity compliance predictions. Responders who understand where incident patterns are heading position themselves for higher-value roles before the market becomes crowded.
A third lever is portfolio quality. Keep clean records of incidents handled, response workflows improved, false assumptions caught, containment choices made, communications delivered, lessons learned, and risk reductions achieved. Confidential work still produces describable value if you document outcomes carefully. The more precisely you can explain how your judgment changed results, the stronger your salary conversations become.
Long-term, incident response can lead into consulting, lead response roles, threat hunting, engineering-adjacent security functions, education, and leadership. It is one of the best career lanes for professionals who want technical work that compounds into strategic influence.
6. FAQs
-
It can be, but it is easier to enter from adjacent roles such as SOC analyst, security analyst, IT support, network operations, or systems administration. The role moves quickly and punishes weak fundamentals, so foundational security and troubleshooting skills matter a lot.
-
Foundational certifications help establish basic credibility early. Beyond that, the best certifications depend on the type of response work you want to do and where you want to go next. Credentials become far more valuable when backed by hands-on investigation, case discipline, and good communication.
-
Often, yes, especially as your responsibilities move beyond initial triage into scoping, containment, stakeholder coordination, and post-incident improvement. The salary upside grows further when you add specialization, sector knowledge, and leadership signals.
-
Many rush into action before building enough clarity. Speed matters, but sloppy speed can widen disruption, damage evidence quality, or lead teams down the wrong path. Strong responders move decisively without pretending uncertainty does not exist.
-
They go beyond handling incidents and start improving how the organization responds overall. That includes better playbooks, clearer communication, stronger mentoring, smarter escalation patterns, and better feedback into controls and detections.
-
Absolutely. It is a strong launchpad into threat hunting, detection engineering, threat intelligence, security leadership, consulting, cloud security, compliance-heavy roles, and broader security management. The path stays versatile because the work sits close to real organizational risk.