How to Transition from IT Support Specialist to Cybersecurity Analyst
Cybersecurity rarely rewards vague ambition. It rewards proof. That is why IT support professionals often sit closer to a security career than they realize. Daily exposure to endpoints, identity issues, privilege mistakes, ticket triage, user behavior, misconfigurations, and escalation patterns builds the exact operational instincts many entry-level analysts still need to develop.
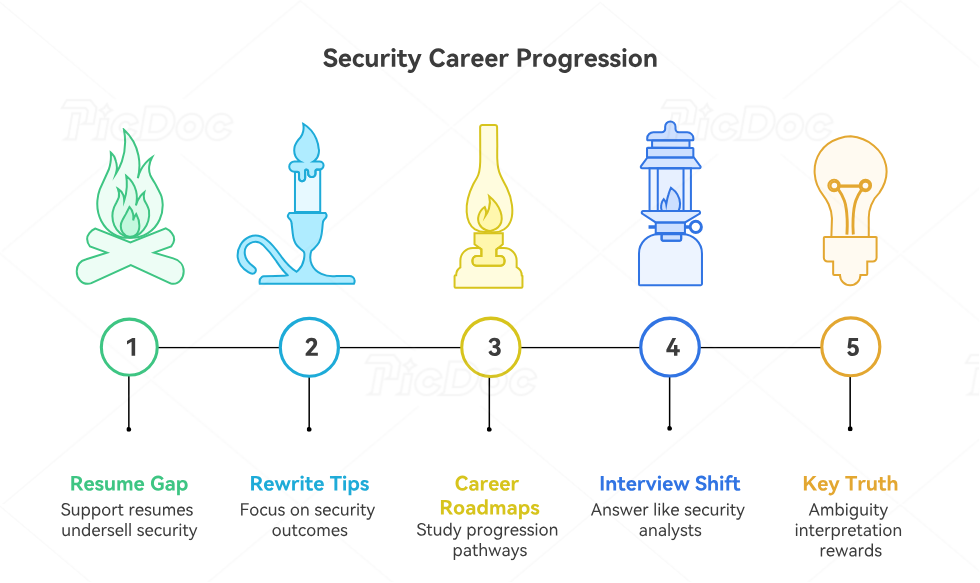
The gap is real, though. Help desk experience alone does not automatically turn into analyst credibility. Hiring managers want evidence that troubleshooting has matured into threat thinking. That means reframing existing experience, closing specific skill gaps, choosing the right certifications, and building a portfolio that proves security judgment under pressure.
1. Why IT Support Is a Strong Launchpad Into Cybersecurity Analysis
A lot of IT support professionals underestimate how much analyst-adjacent work they already do. Password reset abuse, suspicious login complaints, malware cleanup, MFA friction, endpoint instability, rogue software installations, phishing reports, VPN failures, privilege issues, and patching headaches all sit near the security surface. Time spent handling those incidents builds practical familiarity with identity, endpoints, user behavior, and operational weak points. That matters more than many career changers think, especially for security operations roles. Anyone studying the path laid out in the complete guide to becoming a security operations center SOC analyst, the how to become a SOC analyst step-by-step career guide, the career roadmap security analyst to cybersecurity engineer expert path, the pathway to cybersecurity incident responder roles skills certifications, and the career pathway to a senior cybersecurity analyst certifications skills needed will notice a pattern: strong analysts recognize abnormal activity quickly because they already understand normal operations deeply.
That background becomes powerful when it is translated correctly. Support experience should not be framed as “I fixed user issues.” It should be framed as “I handled endpoint anomalies, access disruptions, authentication failures, configuration drift, and escalations involving potentially suspicious activity.” Security teams care about risk recognition, signal quality, documentation, escalation maturity, and discipline under time pressure. Those are already visible in good support work. A professional who has spent time with vulnerability assessment techniques and tools, security information and event management SIEM an overview, intrusion detection systems IDS functionality and deployment, incident response plan IRP development and execution, and cyber threat intelligence CTI collection and analysis can turn that foundation into a credible analyst narrative fast.
2. The Skills Gap You Actually Need to Close
The biggest mistake in this transition is chasing everything at once. IT support professionals often panic and assume they need reverse engineering, advanced malware analysis, exploit development, cloud forensics, threat hunting, governance knowledge, red-team depth, and SIEM mastery before they can qualify for an analyst role. That scattered approach burns time and produces shallow competence. The real goal is narrower: build enough analyst readiness to investigate alerts, validate suspicious activity, escalate cleanly, and communicate business risk. Focus first on security fundamentals tied directly to analyst work: networking, authentication, log reading, endpoint behavior, attack patterns, ticket quality, documentation, and triage. The strongest roadmap usually blends the how to transition from IT support to cybersecurity analyst, step-by-step guide to becoming a certified ethical hacker CEH, guide to becoming an OSCP certified penetration tester, global directory of cybersecurity training providers, and the directory of free cybersecurity courses and resources 2025 edition with role-specific practice.
That means mastering concrete topics that show up in analyst interviews. Learn how authentication breaks, how phishing campaigns unfold, how endpoint alerts differ from noise, how DNS and VPN issues can mask malicious activity, how access misuse looks in logs, and how common attacks travel through real environments. Reading the access control models DAC MAC and RBAC explained, firewall technologies types and configurations, public key infrastructure PKI components and applications, encryption standards AES RSA and beyond, and virtual private networks VPNs security benefits and limitations gives structure. Then add threat reality through the ransomware detection response and recovery, denial of service DoS attacks prevention and mitigation, botnets structure and disruption methods, phishing attacks trends report analysis and prevention strategies 2025 original data, and 2025 data breach report industries most at risk and mitigation strategies. That combination starts turning general IT knowledge into defensible analyst judgment.
3. Certifications, Projects, and Proof That Make Recruiters Take You Seriously
Certifications help most when they solve a trust problem. For IT support professionals, the trust problem is usually this: “Can this person do more than fix tickets?” A carefully chosen certification signals seriousness, but it only moves the needle when matched with proof. Security+ remains useful for foundational credibility. CySA+ starts aligning better with blue-team work. If the long-term aim includes offensive depth, CEH or OSCP can help later, though many first analyst roles do not require them. A smarter strategy is to pair one baseline credential with visible hands-on work. The top cybersecurity certifications directory ranked and reviewed, salary growth analysis for CISSP CEH and security certifications, impact of cybersecurity certifications on career advancement original survey report, cybersecurity certifications of the future what employers will value most 2026-2030, and predicting cybersecurity job market trends roles that will thrive by 2030 make that point from different angles: credentials create leverage when they connect to role evidence.
Projects are what close the deal. Build a home lab that generates login anomalies, failed MFA flows, endpoint alerts, suspicious PowerShell usage, fake phishing reports, and patch drift scenarios. Write mini incident reports. Show alert triage screenshots. Explain why an event mattered, what evidence was reviewed, what could be ruled out, and when escalation was necessary. That turns learning into proof. The same principle sits behind the security audits processes and best practices, cybersecurity frameworks NIST ISO and COBIT, NIST cybersecurity framework adoption original data and industry analysis 2025, state of endpoint security 2025 original data on solutions effectiveness, and the ultimate guide to the best endpoint detection and response EDR tools: security careers accelerate when a candidate can show repeatable analysis, not just course completion.
Quick Poll: What Is Blocking Your Move Out of IT Support Right Now?
Pick the friction point that feels most real, because the right transition strategy depends on the bottleneck.
4. How to Rewrite Your Résumé and Interview Story for Analyst Roles
A support résumé usually undersells security potential through language that sounds reactive, generic, and low-impact. Phrases like “provided technical support,” “resolved user issues,” and “helped maintain systems” bury the actual risk-facing parts of the job. Rewrite bullets around security-relevant outcomes: access control handling, endpoint triage, suspicious activity escalation, asset visibility, authentication troubleshooting, privileged access review, patch follow-up, and incident documentation. Numbers help, but judgment helps more. A bullet that says you “reviewed suspicious email complaints, validated probable phishing indicators, and escalated confirmed cases using established workflows” lands harder than ten generic support bullets. Good examples and role framing can be sharpened further by studying the career roadmap from junior penetration tester to senior security consultant, how to become a cybersecurity manager clear pathway and certifications, career roadmap to cybersecurity compliance officer, detailed guide to becoming a cybersecurity auditor, and complete career roadmap for cybersecurity compliance analyst. Each one shows how role progression depends on framing responsibility in terms of risk, control, and business trust.
Interviews demand the same shift. Many support professionals answer security questions like technicians when they need to answer like analysts. Analysts explain how they validate, prioritize, document, and escalate. They talk through uncertainty cleanly. They separate evidence from assumption. They explain why a false positive still mattered enough to inspect. They understand business impact, even at a junior level. Practice answering with a structure: what was observed, why it raised concern, what evidence was checked, what was ruled out, what remained uncertain, and what action followed. That style aligns naturally with the cybersecurity incident response report effectiveness and improvements 2026-2027 original data, annual report on insider threats identification and prevention 2026-2027 original data, emerging cybersecurity threats in cloud environments original data and analysis, how to become a threat intelligence analyst detailed career guide, and security analyst to cybersecurity engineer expert path, all of which reflect one truth: security careers reward professionals who can interpret ambiguity without becoming vague.
5. A 90-Day Transition Plan That Creates Real Momentum
The first 30 days should tighten fundamentals and inventory your existing overlap. Audit your support experience and isolate every task with security relevance. Start a spreadsheet or tracker of incidents involving accounts, endpoints, phishing, access, patching, remote access, suspicious behavior, and escalation. In parallel, build a focused study plan around network basics, access control, common attacks, log interpretation, and incident handling. Use the directory of free cybersecurity courses and resources 2025 edition, directory of best cybersecurity bootcamps and academies 2025 update, best YouTube channels for cybersecurity learning updates, directory of top cybersecurity podcasts for industry professionals, and top cybersecurity books directory essential reads 2026-2027 edition to support that sprint without drifting into random consumption.
Days 31 through 60 should produce evidence. Stand up a small lab. Simulate phishing events. Review Windows logs. Create sample incident tickets. Practice reading alerts from free or trial tools. Compare detection and response categories using the complete directory of best SIEM solutions ranked and reviewed 2025, top 20 vulnerability scanners for 2025 expert guide and rankings, best application security tools 2026-2027 expert directory reviews, complete directory of best cloud security tools 2026-2027 edition, and top network monitoring and security tools directory 2026-2027 updated. Then turn your outputs into a portfolio with short write-ups: event summary, evidence reviewed, conclusion, and recommended action.
Days 61 through 90 should turn that proof into applications and interview leverage. Update your résumé, optimize LinkedIn around analyst language, apply to SOC, junior analyst, incident response coordinator, vulnerability management assistant, and security operations support roles. Practice interview answers against real-world market pressure by reading the global cybersecurity salary report 2025 industry benchmarks and trends, entry-level to CISO complete salary progression analysis 2026-2027 data, remote vs on-site cybersecurity salaries original data and insights 2025, cybersecurity freelance and consulting market original income data and trends, and future skills for cybersecurity professionals essential competencies by 2030. That perspective matters. It keeps the move strategic instead of desperate. The real win is not just escaping support. It is entering cybersecurity with a path that compounds.
6. FAQs
-
Yes, when the experience includes identity troubleshooting, endpoint issues, phishing reports, remote access problems, patch follow-up, and escalation discipline. Those duties build operational instincts that many junior analyst roles need immediately. The key is presenting that work in security language rather than generic support language.
-
Security+ is often the strongest first move for broad entry-level credibility. CySA+ becomes more attractive when targeting blue-team or SOC work specifically. The decision gets easier when paired with the top cybersecurity certifications directory ranked and reviewed and your target role description. Certification choice should solve a hiring problem, not just collect a badge.
-
A home lab is not mandatory, but it is one of the fastest ways to prove hands-on ability when your current title is outside security. Even a modest lab that produces authentication anomalies, endpoint alerts, suspicious scripts, and incident notes can make interview answers sharper and more credible.
-
Start with SOC analyst, junior cybersecurity analyst, security operations analyst, incident response coordinator, vulnerability management analyst, security monitoring analyst, or IAM support roles. Those openings tend to value technical operations background and evidence of structured security thinking.
-
Focus on adjacent evidence. Explain the security-relevant incidents you handled, how you recognized risk, what evidence you reviewed, how you escalated, and what control weakness or user behavior sat behind the issue. That answer sounds far stronger than simply saying you are “passionate about cybersecurity.”
-
For a disciplined IT support professional, three to six months is enough to become materially more competitive if the effort is focused. The timeline stretches when study stays abstract, projects never become visible proof, or the résumé continues to sound like generic help desk work.
-
They try to learn the whole field at once. Cybersecurity is too wide for that approach. Analyst readiness comes from building narrow, usable competence in triage, evidence reading, escalation, documentation, and foundational threat understanding. Depth in the right slice beats scattered familiarity across everything.