How to Transition from IT to Ethical Hacking: Clear Career Guide
Moving from IT into ethical hacking is not a fantasy jump. It is usually a skill reframing problem, a proof problem, and a positioning problem. The professionals who make it happen fastest do not start by chasing flashy tools. They start by translating their existing operating system, network, cloud, and troubleshooting depth into offensive value. If you already understand how infrastructure breaks, you are closer than you think to the path described in this ethical hacker career roadmap, this guide on transitioning from IT support to cybersecurity analyst, and this broader security analyst to cybersecurity engineer path.
The hard part is that many IT professionals sabotage themselves. They collect theory without building evidence, chase certifications without understanding sequencing, and apply for pentesting roles before they can scope, enumerate, validate, exploit safely, and report clearly. This article fixes that. It will show you how to convert technical experience into hiring leverage, how to choose between paths like CEH and OSCP, and how to build the kind of proof employers actually trust.
1. Understand What Ethical Hacking Really Pays For
Ethical hacking is not paid curiosity. It is paid risk discovery under authorization. That distinction matters because employers do not hire you just to run scanners. They hire you to think like an attacker while behaving like a disciplined consultant. You must understand reconnaissance, attack paths, privilege escalation, lateral movement, impact validation, and reporting, but you also need the judgment found in work on security audits and best practices, cybersecurity frameworks like NIST, ISO, and COBIT, and incident response plan development. Ethical hacking careers reward technical sharpness, but they advance faster when that sharpness is wrapped in scope control, documentation discipline, and business context.
This is why many strong IT professionals can transition well. A network administrator already understands routing behavior, segmentation weakness, firewall logic, and service exposure through work similar to firewall technologies and configurations, intrusion detection systems deployment, and VPN security benefits and limitations. A systems administrator already knows authentication pain points, patching failures, misconfigurations, and privilege issues that connect directly to access control models, public key infrastructure components, and encryption standards. A SOC-minded professional already sees attacker behavior through lenses like SIEM fundamentals, EDR operations, and cyber threat intelligence collection and analysis.
Where people fail is assuming adjacent knowledge automatically equals offensive competence. It does not. Ethical hacking requires you to move from “I know how this system works” to “I can prove how an attacker would abuse it and explain the business impact clearly.” That means your path should include structured exposure to vulnerability assessment techniques and tools, practical familiarity with top penetration testing tools, and a realistic understanding of how junior penetration testers grow into senior security consultants. The transition is not about becoming someone else. It is about turning your IT experience into offensive evidence.
IT-to-Ethical-Hacking Transfer Matrix: 26 Backgrounds, Hidden Advantages, Gaps to Close, and Proof to Build
| Current IT Background | What Already Transfers Into Ethical Hacking | Gap You Must Close Fast | Best Proof Artifact to Build |
|---|---|---|---|
| Help Desk | User environment awareness, ticket triage, common misconfigurations, authentication pain points | Attack methodology and deeper technical enumeration | Write-up showing how weak password hygiene becomes privilege abuse |
| Desktop Support | Endpoint behavior, software deployment issues, local privilege patterns | Post-exploitation logic and Windows internals depth | Windows privilege escalation lab notes with screenshots |
| System Administrator | Server hardening, service exposure, patching realities, permissions | Exploit chaining and reporting like a tester | Home lab attack-path report on an intentionally misconfigured server |
| Linux Administrator | Shell fluency, process awareness, file permissions, service auditing | Web exploitation and Active Directory exposure | Linux enumeration checklist plus privilege escalation walkthrough |
| Windows Administrator | AD, GPO, account lifecycle, trust relationships, PowerShell | Offensive AD abuse patterns and detection-aware testing | AD attack simulation with remediation recommendations |
| Network Administrator | Segmentation, routing, ACL logic, service exposure, protocol behavior | Application-layer testing and finding validation | Network segmentation bypass case study in a lab |
| NOC Engineer | Traffic anomalies, uptime pressure, infrastructure visibility | Offensive tooling depth and exploit validation | Recon-to-impact exercise on exposed services |
| Cloud Support Engineer | IAM, cloud resources, policy missteps, exposed storage patterns | Cloud attack paths and identity abuse | Misconfigured cloud tenant assessment report |
| DevOps Engineer | CI/CD, containers, secrets handling, infrastructure as code | Secure exploitation boundaries and appsec reporting | Pipeline weakness review with attacker-use scenarios |
| Site Reliability Engineer | Architecture visibility, observability, outage analysis | Offensive web logic and exploit discipline | Attack-surface map for a staged application environment |
| Application Support | Business logic familiarity, bug patterns, config drift awareness | Web app testing methodology | OWASP-style lab report with validated findings |
| QA Tester | Reproducibility, test discipline, evidence capture | Security mindset and exploitation strategy | Security-focused test cases for auth, session, and input flaws |
| Database Administrator | Permissions, query behavior, data exposure, backup risk | Injection testing and lateral movement concepts | SQL injection lab plus least-privilege remediation memo |
| IAM Administrator | Identity lifecycle, privilege design, access mistakes | AD abuse, federation weaknesses, token misuse | Identity attack-path narrative from low privilege to high privilege |
| Virtualization Administrator | Host management, segmentation, guest isolation assumptions | Escape research literacy and pivoting logic | Lab notes on hypervisor exposure and management plane risk |
| Endpoint Management Admin | Policy rollout, agent behavior, local control weaknesses | EDR-aware tradecraft and bypass thinking | Endpoint hardening gap analysis with attacker perspective |
| Backup / Recovery Admin | Resilience design, storage exposure, recovery dependencies | Ransomware behavior and privilege abuse | Backup environment attack scenario with recovery-risk analysis |
| IT Auditor | Control logic, evidence review, gap identification | Hands-on exploitation and technical depth | Technical validation report proving one control failure end to end |
| GRC Analyst | Risk language, policy alignment, compliance framing | Practical exploitation credibility | Control failure demonstration tied to business impact |
| SOC Analyst | Adversary patterns, log interpretation, attacker behavior awareness | Offensive workflow execution and reporting from tester view | Detection-to-attack-chain lab write-up |
| Security Analyst | Defensive tooling, alerts, vulnerabilities, hardening context | Deep exploit repetition under time pressure | Portfolio of three validated findings across host, web, and network |
| Incident Response Coordinator | Scoping, severity judgment, documentation, business communication | Proactive exploitation and reconnaissance | Breach simulation showing initial access route and blast radius |
| MSP Technician | Wide technology exposure, client communication, rapid troubleshooting | Methodical depth and specialization | Multi-client style assessment template with risk ranking |
| SaaS Administrator | SSO, permissions, third-party integrations, workflow logic | Tenant abuse patterns and web attack surface skills | SaaS configuration review from attacker viewpoint |
| Web Administrator | Hosting, deployment, CMS patterns, plugin risk | Manual web exploitation and chaining | Mini web app pentest with screenshots and business impact |
| Technical Trainer | Concept clarity, communication, structured explanation | Real attack-path depth and hands-on proof | Walkthrough article teaching one exploit chain from start to fix |
2. Map Your Existing IT Experience to Offensive Security Work
Your fastest route into ethical hacking is to stop describing your past in job-title language and start describing it in attacker-value language. If you say, “I handled Windows administration,” that sounds operational. If you say, “I identified privilege design mistakes, insecure service exposure, brittle patching patterns, and authentication weaknesses across Windows environments,” you are suddenly speaking the language behind access control models, PKI design, endpoint security effectiveness, and privileged access management solutions. Hiring managers for offensive roles want proof that you can see abuse paths where others only see infrastructure.
That translation exercise should become part of your résumé, your LinkedIn headline, your portfolio, and your interview answers. A networking professional can connect their background to vulnerability scanners, network monitoring and security tools, SIEM platforms, and DoS attack prevention. A cloud-focused professional can tie experience directly into cloud security tools, the cloud security engineer career guide, future cloud security trends, and emerging threats in cloud environments. A defensive analyst can bridge into offense through SOC analyst pathways, incident responder roles, threat intelligence analysis, and ransomware response and recovery.
The mistake is trying to hide your IT past because you think pentesting employers only want “pure” hackers. In reality, your IT background can become your differentiator if you frame it correctly. Someone who has spent years troubleshooting identity failures, broken change windows, shadow admin access, weak email controls, and endpoint drift often has a more realistic view of attack surface than someone who only trained inside labs. That is why smart transitioners study email security solutions, data loss prevention strategies, application security tools, and managed security providers not as product catalogs, but as clues about how real environments fail. Your goal is not to erase your background. Your goal is to weaponize its relevance.
3. Build a Transition Plan That Produces Evidence, Not Just Knowledge
A good transition plan has four layers: foundations, offensive methodology, hands-on repetition, and marketable proof. Foundations matter because weak fundamentals create shallow hackers. If TCP/IP, Linux, Windows internals, authentication flows, web requests, DNS, certificates, and common protocols still feel fuzzy, fix that first with the help of free cybersecurity courses and resources, curated training providers, reputable bootcamps and academies, and trusted cybersecurity books. The point is not to stay in study mode forever. The point is to remove the embarrassing blind spots that make you freeze when an interviewer asks why a misconfiguration actually matters.
Then build offensive methodology. You need a repeatable process: scope review, reconnaissance, enumeration, hypothesis generation, vulnerability validation, safe exploitation, privilege analysis, impact explanation, remediation guidance, and reporting. That process gets sharper when you study vulnerability assessment techniques, compare penetration testing tools, read how top penetration testing companies position their services, and look at adjacent career paths such as the OSCP penetration tester guide. You should also study how offensive work intersects with security awareness platforms, because many real findings come from human weakness, not just technical flaws.
Most importantly, create evidence. Do not tell employers you are passionate. Show them a portfolio with lab reports, attack chains, screenshots, remediation write-ups, and brief videos explaining your methodology. Build a small portfolio around web testing, Active Directory enumeration, Linux privilege escalation, Windows privilege escalation, exposed secrets, cloud misconfigurations, and weak identity design. Support your learning loop with cybersecurity blogs and industry news, strong YouTube channels for learning and updates, expert cybersecurity podcasts, and selective conferences. The market does not reward the person who consumed the most content. It rewards the person who can show repeatable, credible offensive work.
Quick Poll: What Is the Biggest Barrier Blocking Your Move From IT to Ethical Hacking?
Pick the pain point that feels most real, because your transition strategy should solve that exact bottleneck first.
4. Choose Certifications, Labs, and Tools That Actually Move You Forward
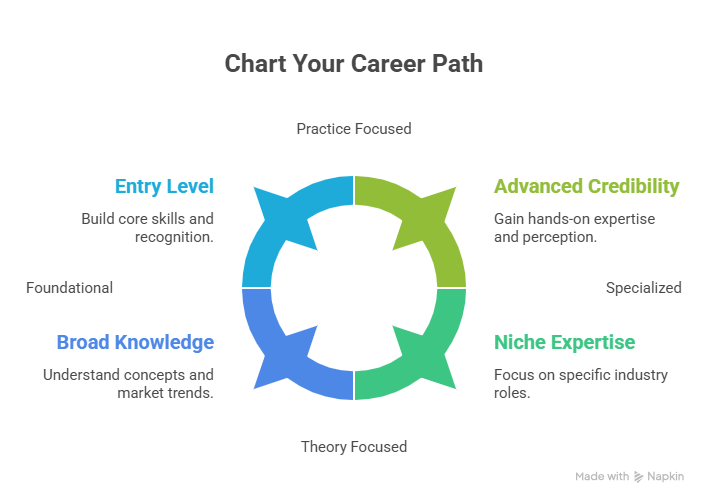
Certification strategy matters, but the wrong sequence wastes months. If you are coming from general IT and need structure, vocabulary, and résumé recognition, CEH can help as an entry signal, especially when paired with your broader understanding of top cybersecurity certifications, long-range employer signals in future cybersecurity certifications, and compensation context from salary growth for security certifications. But if you want stronger hands-on credibility, few credentials reshape employer perception the way the OSCP path can. The point is not that one is universally better. The point is that one may be better for your current gap.
Think in stages. Stage one is baseline employability. That can come from security foundations, your existing IT experience, one recognizable credential, and a transition story supported by job market trends, future cybersecurity roles that will thrive by 2030, and the broader future skills employers will need. Stage two is practical credibility, where labs matter more than badges. This is where you compare penetration testing tools, study application security tools, explore endpoint security providers, and analyze DLP software or cloud security tools to understand how real enterprise environments are defended. Strong ethical hackers know the attacker’s playbook, but they also know what defenders deploy.
Stage three is specialization. Not every ethical hacker should remain a generalist. Some professionals grow toward web and application testing. Some lean into cloud. Some move into red-team-adjacent work. Some end up blending offensive and advisory work through cybersecurity consulting firms, freelance pathways in the cybersecurity consulting market, or sector-focused roles in areas like financial services cybersecurity firms, healthcare cybersecurity firms, or IoT security careers. Choose certifications and labs that move you toward the work you want to do, not the badge people on social media happen to praise this month.
5. Turn Your Learning Into Interviews, Bridge Roles, and Your First Ethical Hacking Job
The first truth is harsh: many people will not go directly from generic IT into a clean pentester title. That does not mean the transition failed. It means you should be strategic. Bridge roles can be powerful if they increase your exposure to attack paths, vulnerabilities, controls, or assessment language. Good bridges include internal security analyst roles, vulnerability management, junior consulting, SOC positions, incident response, or security engineering support. Those paths are visible across guides like how to become a SOC analyst, the full SOC analyst career path, incident responder roles, cybersecurity auditor careers, and the route from security manager to director of cybersecurity. A good bridge job compounds the right evidence instead of trapping you in unrelated admin work.
Your résumé should show four things. First, technical depth from IT. Second, offensive curiosity proven through labs. Third, written communication through clean reports. Fourth, business usefulness. Hiring managers do not want someone who can only produce screenshots. They want someone who can explain why a flaw matters, how an attacker would use it, how likely it is to be exploited, and what remediation is realistic. That is why it helps to study adjacent business-facing material like compliance officer roadmaps, cybersecurity compliance trends, NIST framework adoption analysis, and future audit practice changes. Offensive roles become easier to win when you sound like someone who can help a client or employer reduce risk, not just “hack stuff.”
Finally, interview like a practitioner. Be ready to explain how you enumerate a target, how you validate a finding without causing damage, how you decide severity, how you document evidence, and how you think about defensive controls such as MSSPs, email security, endpoint detection and response, SIEM tooling, and access control design. If you can connect your IT background, your offensive proof, and your remediation mindset into one story, you stop looking like a hopeful beginner and start looking like a low-risk hire.
6. Frequently Asked Questions About Moving From IT to Ethical Hacking
-
Yes, but only if they stop underselling what they already know. Support professionals often understand real-world user behavior, password weakness, endpoint drift, privilege mistakes, and operational shortcuts better than they realize. That experience becomes valuable when paired with structured study, lab proof, and a transition path like IT support to cybersecurity analyst, then onward into the broader ethical hacker roadmap. The key is not your title. The key is how quickly you can build offensive evidence.
-
Choose based on your gap. If you need structure, recognition, and a confidence-building milestone, CEH can help. If you already have strong fundamentals and want hands-on credibility, OSCP usually delivers stronger practical signaling. Compare your decision against broader employer trends in certification value and long-term hiring direction in future cybersecurity certifications.
-
You do not need to be a software engineer, but you do need enough scripting literacy to automate repetitive tasks, read exploit logic, modify proof-of-concept code carefully, and understand web behavior. Strong command-line skills, Bash, PowerShell, and basic Python are usually enough to get moving. Over time, coding depth becomes more valuable in appsec, tooling, automation, and research-heavy roles, especially when combined with material like application security tools and cloud security engineering.
-
Quality beats volume. Three excellent lab reports with a clear methodology beat fifteen shallow screenshots. Your best portfolio pieces usually include one web application test, one privilege escalation or identity abuse case, one network or service enumeration case, and one remediation-focused report. Use ideas from vulnerability assessment techniques, penetration testing tools, and the pathway from junior penetration tester to senior consultant to shape what “good proof” actually looks like.
-
That is common, and it is not a dead end. A strong bridge role can accelerate your transition if it gets you closer to attack paths, detection logic, vulnerability workflows, or client communication. Good bridges include SOC analyst roles, incident response positions, threat intelligence analysis, or security analyst to cybersecurity engineer pathways. The wrong bridge keeps you busy. The right bridge builds offensive relevance.
-
It depends less on calendar time and more on evidence density. Someone with solid IT fundamentals, a disciplined study plan, a usable portfolio, and a realistic bridge strategy can become interview-ready far faster than someone who spends a year collecting content without producing proof. Use compensation and demand references such as the global cybersecurity salary report, entry-level to CISO salary progression data, and job market predictions to stay realistic about the upside while keeping your process brutally practical.