Step-by-Step Guide to Becoming a Cybersecurity Red Team Specialist
Breaking into red teaming is not about collecting flashy tools, memorizing exploit names, or calling yourself “offensive security” after a few labs. Employers want someone who can think like an adversary, operate within scope, document clearly, avoid reckless noise, and turn technical actions into meaningful business risk. That is a much higher bar than most aspiring candidates realize.
This guide is built for people who want a real pathway, not empty motivation. Whether you are coming from IT support, SOC, cloud, audit, or penetration testing, the goal is to help you build the exact capabilities, proof, and positioning that make hiring managers take you seriously.
1. Understand What a Red Team Specialist Actually Does Before You Chase the Title
A red team specialist is not just a penetration tester with a cooler title. Penetration testing usually answers a narrower question: “What weaknesses can be found and validated in this target?” Red teaming goes further. It asks, “If a realistic, authorized adversary pursued a mission objective, how far could they get, what defenses would notice them, and what would actually fail under pressure?” That distinction matters because many candidates prepare for the wrong job.
If you are still building fundamentals, start by understanding where red teaming sits relative to a SOC analyst path, a security analyst to engineer progression, or the move from IT support into cybersecurity analyst work. Those routes teach the defensive visibility, alert logic, asset context, and operational maturity that many red-team candidates lack. Someone who understands how defenders think writes sharper attack paths and delivers more useful findings.
This field also overlaps with the journey to becoming an ethical hacker, the path from junior penetration tester to senior security consultant, and the roadmap to incident responder roles. The common mistake is assuming those paths are interchangeable. They are not. Red teaming demands offensive curiosity, defensive empathy, disciplined reporting, and strong judgment under authorization boundaries.
That is why your first checkpoint should be brutally honest: do you actually enjoy long-form investigation, careful documentation, controlled experimentation, and business-context thinking? If you only enjoy one-click tools and screenshot-driven lab wins, you will hit a wall. Real teams need people who can map attack paths, understand identity exposures, analyze detection surfaces, and explain why a misconfiguration matters to leadership. Reading through vulnerability assessment techniques and tools, security audits processes and best practices, and cybersecurity frameworks like NIST, ISO, and COBIT will help you see why offensive work has to connect cleanly to governance, assurance, and measurable risk.
Cybersecurity Red Team Specialist: 27-Skill Readiness Matrix
Use this matrix to spot the gaps that actually block interviews, performance, and promotion in offensive security roles.
| Capability | Why It Matters In Red Teaming | What Good Looks Like | Best ACSMI Resource |
|---|---|---|---|
| Networking fundamentals | You cannot model attack paths if you do not understand how systems communicate. | You can explain ports, segmentation, routing, and exposure without guessing. | Network monitoring and security tools |
| Linux administration | Most offensive labs and tradecraft assume strong Linux comfort. | You navigate, script, troubleshoot, and automate basic workflows cleanly. | Free cybersecurity courses and resources |
| Windows administration | Enterprise offensive work often lives or dies in Windows-heavy environments. | You understand services, logs, permissions, GPO concepts, and admin workflows. | How to become a SOC analyst |
| Active Directory literacy | Identity and privilege structure create many real enterprise pathways. | You can explain trust relationships, privilege tiers, and admin risk clearly. | Access control models explained |
| Bash, PowerShell, Python basics | Operators who cannot script stay slow, noisy, and tool-dependent. | You automate small tasks, parse outputs, and adapt workflows fast. | Global cybersecurity training providers |
| Recon discipline | Weak reconnaissance leads to shallow testing and missed paths. | You build a target picture before touching controls or assumptions. | Penetration testing tools directory |
| Vulnerability validation | Scanning is not enough; you need context, proof, and prioritization. | You separate noise from exploitable risk and document the distinction. | Vulnerability scanners guide |
| Web application understanding | Many real-world attack paths begin with application weakness. | You understand auth flows, sessions, input handling, and exposure logic. | Application security tools directory |
| Cloud identity awareness | Modern attack paths frequently involve cloud misconfigurations and IAM drift. | You can reason through privilege spread, token risk, and access design. | Cloud security tools directory |
| Credential risk analysis | Credential abuse remains one of the most business-relevant risk paths. | You identify weak authentication design and privilege hygiene issues. | PAM solutions directory |
| Email threat understanding | Initial access simulations often depend on realistic email risk knowledge. | You understand controls, user behavior risk, and common weak points. | Email security solutions directory |
| Endpoint visibility literacy | You need to understand what defenders can see while you test. | You can reason about telemetry, alerts, and containment response triggers. | EDR tools guide |
| SIEM awareness | A red teamer without logging awareness produces less useful exercises. | You know how offensive actions appear in monitoring pipelines. | SIEM overview |
| Threat intelligence mapping | Adversary emulation must reflect realistic behaviors and goals. | You map actions to actor logic instead of random technique collecting. | Cyber threat intelligence |
| Phishing and social engineering judgment | Human-layer testing requires restraint, ethics, and very clear scope boundaries. | You can design realistic but responsible simulations with approval controls. | Security awareness training platforms |
| Access control thinking | Privilege logic and authorization design drive many meaningful findings. | You can explain where policy design breaks under real business behavior. | DAC, MAC, and RBAC explained |
| Encryption and PKI understanding | Weak certificate handling and key management can create serious exposure. | You understand trust chains, cert use, and common implementation failure points. | Encryption standards guide |
| Network defense awareness | Offensive work improves when you understand how controls are tuned. | You can discuss firewalling, IDS, and VPN design in plain language. | Firewall technologies |
| Intrusion detection familiarity | Red teams create more value when they help improve alert logic. | You can connect an activity path to what should have been seen. | IDS functionality and deployment |
| Data protection awareness | Exfiltration risk is often what turns a weakness into a board-level issue. | You understand where controls should stop data movement or misuse. | DLP strategies and tools |
| Incident response empathy | Good operators help defenders learn, not just feel embarrassed. | You can show what happened, what was missed, and how to close gaps. | Incident response plan development |
| Compliance context | Findings matter more when tied to regulatory and governance consequences. | You can explain how offensive results affect audits, reporting, and exposure. | Cybersecurity compliance trends |
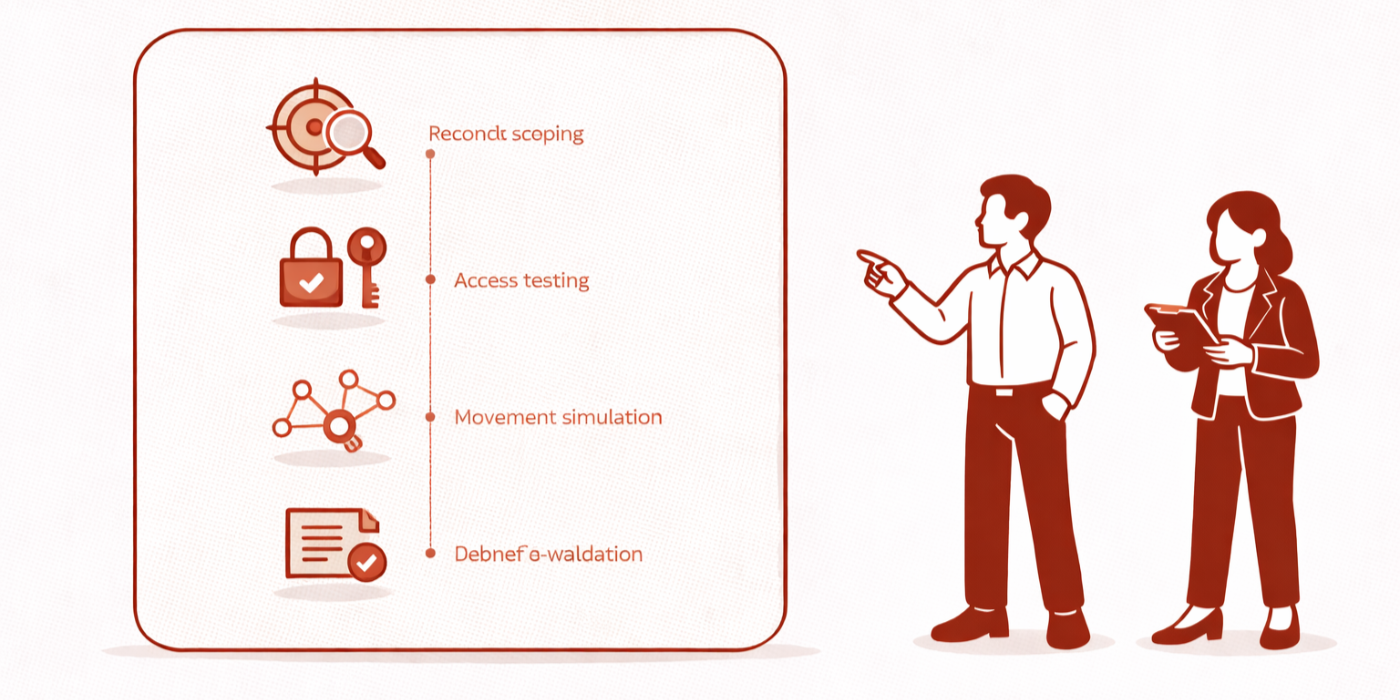
| Scoping and rules of engagement | Poor scope control destroys trust faster than weak technical skill. | You know how to respect boundaries, timing, approvals, and escalation rules. | Security audits and best practices |
| Reporting quality | Weak reports make strong technical work look immature. | You write findings with evidence, impact, and actionable remediation logic. | Cybersecurity auditor career guide |
| Executive communication | Leadership wants exposure, likelihood, and business consequence, not jargon dumps. | You can summarize mission outcome, control failure, and next steps cleanly. | Cybersecurity manager pathway |
| Portfolio evidence | Hiring teams believe proof faster than claims. | You can show sanitized reports, labs, write-ups, and learning progression. | Cybersecurity instructor career guide |
| Continuous learning system | Offensive talent decays fast without structured practice. | You maintain a study loop across labs, reading, reporting, and review. | Cybersecurity learning channels |
| Industry signal building | The best candidates learn in public without oversharing or pretending. | You engage with research, events, and communities that sharpen judgment. | Cybersecurity conferences directory |
2. Build the Foundation Red Team Hiring Managers Quietly Screen For
The fastest way to stall this career move is to jump straight into attack tools before you can explain the environment you are testing. Red team interviews expose shallow foundations very quickly. A candidate may know popular tooling, but freeze when asked about Windows internals, enterprise authentication, identity risk, segmentation logic, common cloud exposure patterns, or why a certain control would create telemetry. That is why your build order matters more than your enthusiasm.
Start with system fluency. You should be comfortable with Linux administration, Windows behavior, scripting basics, and networking because those layers shape everything else. Then move into identity, access, and enterprise architecture by studying access control models, public key infrastructure components and applications, and virtual private networks and their limitations. These are not abstract theory topics. They are the difference between understanding why a path works and blindly repeating lab motions.
Next, build defensive context. The best red-team candidates do not fear blue-team concepts; they use them. Study EDR tools, SIEM platforms, intrusion detection systems, incident response planning, and ransomware detection, response, and recovery. You are not learning these to abandon offense. You are learning them so your offensive work becomes relevant to actual defense improvement, not just personal entertainment.
After that, choose a track that matches your background. Someone coming from SOC analyst work should lean harder into adversary emulation and reporting depth. Someone following a cloud security engineer path needs stronger offensive application and identity attack-path thinking. Someone coming from cybersecurity compliance officer work or a cybersecurity auditor track must build far more technical reps, but already has an advantage in risk framing and written communication. That self-awareness saves months of wasted effort.
3. Build Hands-On Offensive Skill the Right Way: Labs, Notes, Reporting, and Adversary Thinking
Most candidates fail here because they confuse activity with progress. They spend hundreds of hours inside labs, yet cannot show a hiring manager how their judgment improved. They completed rooms, copied techniques, maybe passed a few challenge milestones, but they did not build operator discipline. That is the gap you need to close.
Your lab work should always answer four questions. What was the objective? What assumptions did you begin with? What evidence changed your plan? What would you tell a client or internal security leader afterward? If your notes do not capture those four things, you are probably training like a hobbyist instead of a professional. Reading top penetration testing tools, best application security tools, cloud security tools, and leading endpoint security providers is useful only if it improves your decisions, not because it helps you name-drop products.
You also need breadth without becoming scattered. Study firewall technologies, botnet structure and disruption, denial-of-service prevention and mitigation, encryption standards, and cyber threat intelligence collection and analysis. Not because a red team specialist must be a deep expert in every niche, but because enterprise attack paths cross multiple control families. The more completely you understand the environment, the better your scenario design becomes.
One of the smartest moves you can make is to build a purple-team lens early. Pair each offensive exercise with a defensive review. Ask what logs should have existed, what alerts should have fired, which controls should have constrained the behavior, and which remediation step would reduce risk fastest. That habit makes you valuable to teams investing in next-generation SIEM thinking, future zero-trust strategy, and stronger endpoint security effectiveness. It also helps you avoid the candidate trap of sounding clever but operationally useless.
Quick Poll: What Is The Biggest Thing Blocking Your Move Into Red Teaming?
Pick the pain point that feels most real right now. The right next step depends on the bottleneck, not the hype.
4. Pick the Right Certifications, Build Real Proof, and Stop Treating Credentials Like a Shortcut
Certifications matter, but not in the simplistic way candidates hope. They do not automatically make you employable, and they do not rescue weak fundamentals. What they do is reduce hiring uncertainty when paired with the right evidence. A credential can tell an employer, “This person has crossed a known bar.” Your job is to make sure that bar matches your target role and current stage.
For many aspiring red-team specialists, the best sequence starts with broad validation, then moves toward practical proof. Use the top cybersecurity certifications directory to understand the landscape, compare it with the impact of cybersecurity certifications on career advancement, and review the salary growth analysis for CISSP, CEH, and security certifications. If you are early, a baseline credential can help credibility. If you are targeting offensive roles directly, the more important question is whether your next certification proves practical skill or just expands HR recognition.
That is where resources like the guide to becoming a certified ethical hacker and the pathway to becoming an OSCP-certified penetration tester become useful. Do not treat them as trophy hunts. Treat them as filters. CEH may help certain résumé screens. OSCP-style proof usually carries more practical weight in offensive hiring conversations. But neither matters much if you cannot discuss scope, methodology, tradeoffs, reporting, and remediation with maturity.
Your portfolio is where the certification story becomes believable. Build sanitized artifacts that prove you can think, not just follow instructions. Strong artifacts include a scoped lab assessment, a well-structured finding write-up, a short executive summary, a remediation prioritization note, a control-gap analysis informed by NIST framework adoption, and a defensive reflection tied to cybersecurity compliance trends or GDPR and cybersecurity challenges. That combination signals something rare: offensive skill with enterprise maturity.
5. Land the Role, Position Your Background Correctly, and Grow Beyond “Junior Offensive Talent”
The title “red team specialist” is not always the front door. Many people reach it through adjacent roles with stronger hiring volume: SOC analyst, security analyst, detection engineer, junior penetration tester, cloud security analyst, incident responder, or security consultant. That is not a compromise. It is often the smartest route because it gives you context, stories, and credibility. If you are already working in cybersecurity, your pitch should not be “I want to do something cooler.” It should be “I already understand enterprise environments, I have built offensive proof, and I can help the organization test defenses more realistically.”
That positioning works especially well if you can connect your journey to a senior cybersecurity analyst pathway, a threat intelligence analyst guide, a cloud security engineer roadmap, or the progression from security analyst to cybersecurity engineer. Each of those routes builds something red teams need: telemetry literacy, attacker modeling, architecture awareness, or technical depth.
When you rewrite your résumé, remove vague skill inflation. “Experienced with offensive tools” is weak. “Built and documented multi-stage lab assessments focused on identity exposure, application risk, and defensive visibility gaps” is stronger. “Interested in red teaming” is weak. “Translated findings into business impact, remediation priority, and control-improvement recommendations” is stronger. Hiring managers are not hiring passion alone; they are buying reduced risk. That is why reading cybersecurity job market trends and salary predictions, the entry-level to CISO salary progression analysis, and predicting demand for specialized cybersecurity roles is so useful. It helps you target roles where your current profile can plausibly compete.
Long term, your growth depends on whether you stay a tool operator or become a trusted operator. Trusted operators understand sector context through research like the financial sector cybersecurity incidents analysis, the healthcare cybersecurity threat report, the critical infrastructure cybersecurity report, and cloud environment threat analysis. They also keep evolving through training providers, podcasts, books, research organizations, and conferences. That learning system is what turns a candidate into a career asset.
6. FAQs
-
No, but SOC experience is extremely useful because it teaches you how events are monitored, prioritized, escalated, and investigated. Candidates who have studied the SOC analyst career path or moved through the SOC analyst to manager progression often have stronger defender empathy and better reporting instincts. That said, a strong route can also come from ethical hacking, cloud security, or incident response if you build the missing offensive pieces intentionally.
-
Prioritize the certification that closes your biggest credibility gap. If you need basic trust, use a broad foundational credential. If you already have that and want offensive proof, move toward more practical hands-on validation using the cybersecurity certifications directory, the CEH guide, and the OSCP pathway. The mistake is copying someone else’s certification stack without checking whether it aligns with your current experience and target employers.
-
For someone with no technical base, it can take many months of disciplined study before the résumé is credible. For someone already in IT, SOC, or security analysis, the timeline is usually shorter because the environment knowledge is already there. The better benchmark is not months; it is evidence. Once you can show strong fundamentals, structured lab notes, clear findings, and role-aligned proof comparable to pathways like security analyst to engineer or junior penetration tester to senior consultant, you are moving from “aspiring” to “interviewable.”
-
A good portfolio proves judgment, communication, and progression. Include sanitized lab assessments, concise executive summaries, remediation notes, and short reflections that connect offensive findings to defensive improvement. You can also reference how your thinking aligns with security audits best practices, NIST framework adoption, and incident response planning. A weak portfolio is a pile of screenshots. A strong one makes an employer feel safer hiring you.
-
You do not need to begin as a software engineer, but weak scripting will slow you down. Bash, PowerShell, and Python matter because they help you automate repetitive work, parse outputs, and adapt faster inside labs and assessments. This is one reason many candidates benefit from structured learning through training providers, free cybersecurity resources, and curated cybersecurity bootcamps and academies. You are not aiming for elegant software architecture. You are aiming for technical independence.
-
Yes, but you must close the hands-on gap fast. People from cybersecurity compliance officer, cybersecurity auditor, or policy-heavy roles often underestimate how valuable their written communication and control awareness already are. The missing piece is practical technical proof. Once that is built, those backgrounds can become an advantage because you already know how to frame risk in language leadership understands.
-
Do not try to out-hype everyone. Out-clarify them. Build better artifacts, write better summaries, understand business context, and show learning discipline. Use market context from the cybersecurity workforce shortage study, remote versus on-site salary insights, future skills for cybersecurity professionals, and job-market predictions through 2030 to aim your development where demand is compounding, not where social media is loudest.
-
They chase identity through tools instead of earning trust through competence. They want the offensive title before building the reporting, scoping, systems knowledge, and business framing that make offensive work valuable. The better approach is to use resources like the top cybersecurity certifications directory, the career pathway to a senior cybersecurity analyst, the OSCP career guide, and the ethical hacking roadmap to build a progression that employers can trust, not just admire from a distance.