How to Transition from IT Manager to Security Leadership Roles
An IT manager already sits close to security leadership. You oversee infrastructure, identity, change windows, vendors, outages, budgets, and executive expectations every week. The gap is rarely raw capability. The real gap is how your experience gets translated into the language of cybersecurity frameworks, risk ownership, incident readiness, career advancement, and security leadership pathways.
That translation decides whether you get viewed as “strong in IT” or as someone ready for a cybersecurity manager role, a director-level move, a compliance leadership track, or a future CISO path. This guide shows how to make that shift with proof, leverage, and hiring-market credibility.
1. Why IT Managers Already Have More Security Leadership Leverage Than They Realize
Most IT managers underestimate how much of their current work already overlaps with security leadership. When you enforce MFA, review privileged access, standardize patching, manage remote access, approve infrastructure changes, and coordinate recovery after outages, you are already influencing the control environment. That matters because security leaders are judged on whether controls are defined, adopted, measured, and improved over time. Your background can already support conversations around access control models, firewall technologies, intrusion detection systems, encryption standards, and public key infrastructure.
Where many transitions fail is framing. An IT manager may describe a project as “server refresh completed on time.” A security leader would present the same effort as reduced attack surface, improved unsupported-asset exposure, stronger logging coverage, tighter admin-path control, and better recovery posture. That shift in framing connects your work to vulnerability assessment techniques, SIEM strategy, endpoint defense maturity, incident response effectiveness, and ransomware resilience.
Hiring committees also trust leaders who understand tradeoffs. Security leadership lives inside tradeoffs every day: user friction versus stronger controls, vendor speed versus third-party risk, cloud agility versus visibility gaps, and growth targets versus audit pressure. IT managers already make these calls in adjacent form. That gives you a strong base for roles tied to cloud security engineering, security analyst to engineer progression, incident responder pathways, cybersecurity auditing, and compliance analyst growth.
IT Manager to Security Leadership Transition Matrix: 26 Responsibilities That Already Carry Security Weight
| Current IT Management Responsibility | Security Leadership Translation | Where It Creates Real Leverage | Best Proof Artifact to Build |
|---|---|---|---|
| Asset inventory ownership | Supports visibility, lifecycle control, and unsupported-system risk reduction | Foundational governance, audit readiness, attack surface control | Asset criticality matrix with risk-based refresh priorities |
| Patch management oversight | Shows control discipline and exposure reduction cadence | Vulnerability management leadership credibility | Patch SLA dashboard by severity, business unit, and exception rate |
| MFA rollout or enforcement | Demonstrates identity-first security decision making | IAM, zero trust, insider-risk reduction | Executive summary showing adoption, exceptions, and residual risk |
| Privileged access review | Maps directly to least-privilege governance | PAM, admin-risk control, audit defense | Quarterly privileged account review process with remediation log |
| VPN and remote access administration | Connects to secure access policy and remote workforce risk | Hybrid work security leadership | Remote access control standard with high-risk use-case decisions |
| Endpoint policy enforcement | Shows baseline control ownership across user devices | EDR, hardening, endpoint hygiene | Endpoint compliance scorecard and enforcement escalation path |
| Backup and restore testing | Demonstrates resilience thinking beyond uptime | Ransomware recovery, business continuity, executive trust | Recovery testing report with RPO/RTO gaps and business impact |
| Change advisory board participation | Shows governance over production risk introduction | Secure change control and control exception review | Security-impact change review checklist with approval criteria |
| Vendor onboarding and renewals | Transfers into third-party risk assessment experience | Supply-chain security, procurement influence | Vendor risk questionnaire and tiering model |
| Cloud admin oversight | Signals exposure to identity, storage, logging, and config risk | Cloud security and security architecture conversations | Cloud control gap register with remediation roadmap |
| Network segmentation planning | Shows preventative security thinking through design choices | Lateral movement reduction and containment strategy | Segmentation map tied to crown-jewel systems |
| SIEM or log retention coordination | Demonstrates security visibility and evidence-awareness | Detection maturity and investigations support | Logging coverage matrix by critical system and use case |
| Service desk escalation management | Maps to incident triage and escalation governance | Operational response discipline | Escalation severity framework with incident routing logic |
| Root cause analysis after outages | Supports post-incident learning culture | Security postmortems, control improvement, board confidence | Blameless review template with control-correction actions |
| Disaster recovery planning | Connects to resilience and crisis leadership readiness | Business continuity leadership | Scenario-based tabletop exercise plan with owners and triggers |
| Policy documentation | Proves ability to formalize controls and standards | GRC, internal audit, regulator-facing maturity | Policy library map aligned to business systems |
| Audit evidence collection | Transfers directly into control validation discipline | Audit, compliance, control assurance | Evidence tracker linked to control owners and due dates |
| CMDB governance | Strengthens visibility into dependencies and critical assets | Incident prioritization and exposure mapping | Dependency model for critical services and business impact |
| Business continuity coordination | Shows enterprise-level risk thinking across departments | Security leadership beyond pure tooling | Continuity plan review cadence with role assignments |
| Security tool budget participation | Signals decision-making around cost, efficacy, and tradeoffs | Director-level leadership credibility | Tool rationalization paper with ROI, overlap, and reduction cases |
| Executive reporting | Demonstrates concise risk communication | Board updates, CISO briefings, leadership presence | Quarterly risk dashboard with trend narrative |
| Team coaching and performance management | Supports leadership maturity in security teams | Manager and director role readiness | Skill matrix and coaching plan for analysts or admins |
| Cross-functional conflict resolution | Maps to security’s need to influence engineering, legal, HR, and finance | Enterprise change adoption | Stakeholder map with resistance points and decision pathways |
| Procurement standards enforcement | Shows control over technology sprawl and risky purchases | Shadow IT reduction and policy governance | Security review checklist for new technology requests |
| SLA and KPI management | Builds foundation for security metrics leadership | Service quality, risk trends, maturity measurement | Security operations scorecard with outcome-based KPIs |
| Leadership during high-pressure outages | Shows calm decision making under ambiguity | Major incidents, breach response, crisis credibility | Incident commander playbook with communication workflows |
2. Translate Your IT Management Experience Into the Security Language Hiring Committees Want
A hiring panel rarely promotes someone into security leadership because they “supported infrastructure well.” They move when they see evidence of control thinking, measurable risk reduction, and executive-ready judgment. That means your résumé, portfolio, and interview stories should translate operational work into security outcomes. A server migration becomes attack-surface reduction. A remote-device program becomes stronger endpoint governance through EDR strategy, improved network monitoring, better data loss prevention, cleaner security awareness enforcement, and stronger SIEM visibility.
The best translation framework is simple. First, identify the business asset involved. Second, state the security exposure attached to it. Third, show the control you influenced. Fourth, quantify the improvement. Fifth, connect the result to leadership judgment. This framework works whether you led identity cleanup, improved backup coverage, tightened admin permissions, or standardized vendor onboarding. It also aligns your story with NIST adoption trends, compliance reporting priorities, future audit practice expectations, next-generation security standards, and future compliance direction.
Your proof should also become more visible outside daily operations. Build a one-page risk dashboard. Write a control-gap summary after major projects. Run a tabletop exercise and document lessons. Create a third-party risk checklist. Present a patch-exception narrative that ties technical debt to business exposure. Those artifacts tell employers you already think like someone who can lead a program rather than only maintain one. They also create bridges into adjacent tracks such as SOC leadership, threat intelligence analysis, security operations careers, incident response specialization, and cloud security leadership.
3. Close the Gaps That Actually Block IT Managers From Security Leadership
The transition usually stalls in five places. The first is risk language. Many strong IT managers can explain outages, budgets, and vendor issues clearly, yet they struggle to express likelihood, impact, control maturity, residual exposure, and decision priority in a security framework. Start fixing that by reading more deeply across security audit best practices, cybersecurity frameworks, compliance officer pathways, cybersecurity auditor career guidance, and cybersecurity compliance analyst progression.
The second gap is detection and response judgment. Security leaders do not need to be the deepest hands-on analyst in the room, yet they must understand how investigations move, how incidents escalate, how evidence gets preserved, and how business impact shapes containment decisions. That means building working fluency in SIEM operations, cyber threat intelligence, incident response planning, ransomware response, and insider threat patterns.
The third gap is architecture fluency across cloud, identity, application, and endpoint layers. You do not need mastery in every domain before moving up. You do need enough depth to ask good questions, spot weak assumptions, and fund the right priorities. That is where focused study around cloud security tools, application security tools, privileged access management, top vulnerability scanners, and penetration testing tools pays off fast.
The fourth gap is career signaling. Smart candidates waste time collecting certifications that add résumé mass without changing employer perception. Pick credentials based on target role. A governance-heavy move may benefit from the broader career logic in the cybersecurity certifications directory, the data inside the certification impact report, the compensation patterns in the salary growth analysis, the employer lens in future certification trends, and the broader context from job market predictions.
The fifth gap is learning velocity. Security leadership rewards people who build a constant intake system. Strong candidates read cybersecurity blogs and news sources, follow cybersecurity podcasts, use the best YouTube channels for cybersecurity learning, work through books that sharpen judgment, and attend security conferences that expand perspective. That ongoing intake makes your interviews sharper and your executive conversations more current.
Quick Poll: What Is Really Slowing Your Move From IT Management Into Security Leadership?
Pick the barrier that hurts most, because the fastest transition plan depends on the obstacle that keeps your experience from being seen as security leadership material.
4. Build a Transition Plan That Produces Proof, Not Just Effort
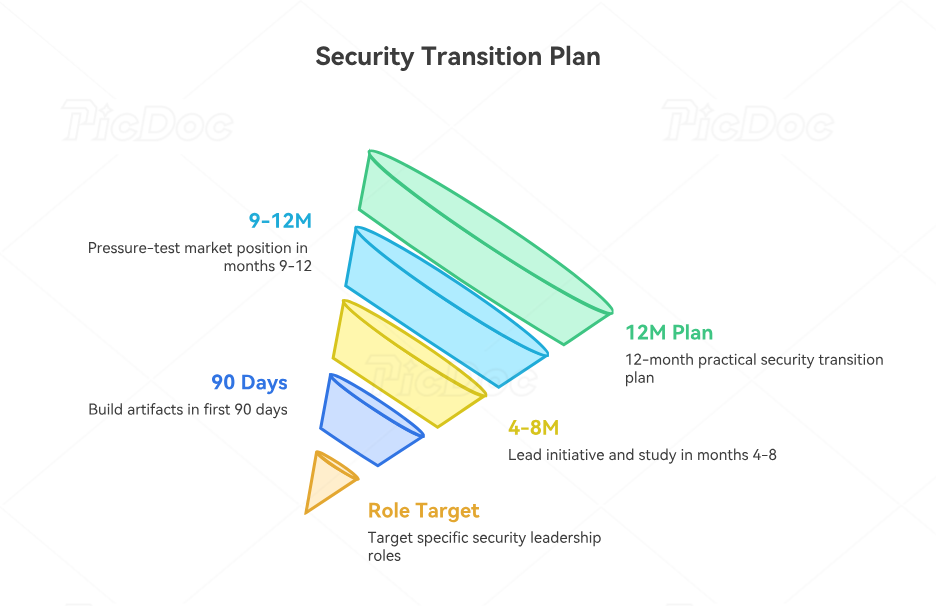
The strongest transition plan starts with role targeting. “Security leadership” is too broad to guide action. Choose a first destination such as security operations manager, security engineering manager, GRC manager, compliance manager, or deputy security director. Each path changes what proof matters most. Someone targeting operations leadership should spend more time with SOC analyst growth paths, SOC manager progression, incident response reporting, ransomware threat analysis, and threat intelligence collection.
A practical 12-month plan usually works better than a loose “learn security” goal. In the first 90 days, translate your current work into security outcomes and build one leadership artifact: risk dashboard, tabletop plan, control-gap register, third-party review workflow, or patch-risk narrative. In months four through eight, lead a visible security-adjacent initiative and pair it with targeted study through free cybersecurity resources, credible bootcamps and academies, the broader training provider directory, stronger conference exposure, and long-form reading through the top cybersecurity books directory.
In months nine through twelve, pressure-test your market position. Update your résumé around security outcomes, request interviews for stretch roles, and compare compensation using the global cybersecurity salary report, remote versus on-site salary patterns, entry-level to CISO salary progression, the broader cybersecurity job market report, and the labor dynamics inside the cybersecurity workforce shortage study. Your plan should create leverage, visibility, and role-fit evidence at the same time.
5. How to Win Interviews for Security Manager, Director, and CISO-Track Roles
Security leadership interviews reward specific stories. A hiring panel wants to hear how you identified exposure, prioritized action, got buy-in from resistant stakeholders, measured improvement, and made a judgment call under pressure. Bring stories about identity cleanup, privileged access review, segmentation decisions, backup validation, vendor-risk escalation, or cloud logging gaps. Then frame those stories using the language employers already use across security manager pathways, director advancement roadmaps, CISO progression guides, security consultant paths, and ethical hacker career development.
Expect technical leadership questions that test breadth more than deep command-line skill. You may be asked how you would prioritize budget between EDR, IAM, logging, email defense, awareness training, and cloud visibility. Prepare by studying email security solution landscapes, SIEM options, endpoint security provider comparisons, data loss prevention platforms, and security awareness training platforms. That preparation lets you speak like someone who can evaluate tradeoffs instead of someone repeating product labels.
You should also be ready for future-facing questions. Boards want leaders who can adapt to change fast. Show awareness of AI-powered cyberattacks, deepfake security threats, future cloud security trends, future workforce dynamics, and the broader future skills employers will value. That perspective signals long-term readiness rather than short-term certification chasing.
6. FAQs
-
Yes, when the current IT role already includes ownership over identity, access, endpoint policy, vendor governance, incident coordination, budgeting, and executive reporting. The deciding factor is proof. A candidate who can show framework alignment through cybersecurity frameworks, control validation through security audit practices, measurable exposure reduction through vulnerability management, stronger resilience through incident response planning, and market positioning through the career advancement impact report has a realistic path into manager-level security roles.
-
The right answer depends on target role. A governance-oriented move benefits from credentials that strengthen control, policy, and audit credibility. An operations-heavy move benefits from certifications that reinforce incident response, threat handling, or defensive operations. Use the cybersecurity certifications directory, compare real-world outcomes in the salary growth analysis, review the employer signal inside the certification impact report, watch long-term relevance in future certification trends, and line everything up with the job market outlook.
-
Evidence of judgment matters most. Employers want to see that you can prioritize controls, defend budget decisions, lead cross-functional action, and communicate clearly under pressure. Strong examples include a privileged-access cleanup, a tabletop exercise, a third-party risk workflow, a cloud-control gap review, or a patch-risk escalation model. Those projects become more valuable when they reflect the concerns covered in incident response reports, insider threat analysis, cloud threat reporting, ransomware threat research, and compliance trend reporting.
-
A focused candidate can become interview-ready within 9 to 18 months if they already manage infrastructure, users, vendors, and executive expectations. The timeline gets shorter when you select a specific destination, build proof artifacts early, and tighten your learning loop with the right inputs from free training resources, reputable training providers, targeted bootcamps and academies, respected industry publications, and current conference ecosystems. Drift usually comes from vague role targeting and weak proof.
-
The most realistic landing spots are often security operations manager, security engineering manager, GRC manager, compliance manager, vulnerability management lead, or a deputy security manager role in a mid-sized company. These positions reward operational maturity, stakeholder coordination, and governance discipline. To compare tracks, study the pathways into security management, SOC management, compliance leadership, auditing leadership, and long-range director progression. The best first move is the one closest to your strongest existing proof.
-
Lead with a security-framed summary, then rewrite experience bullets around exposure reduction, control implementation, risk ownership, and leadership under pressure. Include identity governance, privileged access, endpoint hardening, logging coverage, backup validation, vendor review, policy ownership, and audit support wherever they are true. Use language shaped by security leadership career guides, security manager pathways, salary progression data, job market trends, and the long-term future skills report. The résumé should make your security judgment visible within the first few lines.