Comprehensive Guide: Career Path to Director of Information Security
Reaching Director of Information Security takes far more than technical credibility. This is the point where companies stop asking whether you can find security problems and start asking whether you can lead teams, reduce enterprise risk, influence budgets, strengthen governance, and help the business make safer decisions without slowing growth. That shift breaks many otherwise strong cybersecurity careers.
This guide is built for professionals who want to make that move deliberately. Whether you are coming from a SOC, security engineering, ethical hacking, audit, compliance, cloud, or incident response background, the goal here is to help you build director-level judgment, visibility, and promotion-ready proof.
1. Understand What the Director of Information Security Role Actually Demands
A Director of Information Security is not simply a senior technical specialist with more meetings. This role sits at the intersection of security strategy, team leadership, operational oversight, risk prioritization, executive communication, and cross-functional influence. Someone who already understands the path to becoming a cybersecurity manager, the progression from security manager to director of cybersecurity, the roadmap to Chief Information Security Officer, and the wider entry-level to CISO salary progression usually sees this earlier than most: the role is about scaling security decision-making, not just deepening individual contribution.
This matters because many talented practitioners aim at the wrong target. A strong SOC analyst, a capable cybersecurity engineer, an experienced ethical hacker, or a credible incident responder can still fall short at director level if they cannot connect technical work to business priorities, leadership confidence, and repeatable program improvement. The company is looking for someone who can align teams, explain tradeoffs, defend investment, and turn security into an operating function instead of a disconnected technical island.
The Director role also demands broader context than many candidates expect. You need working fluency in security audits and best practices, cybersecurity frameworks such as NIST, ISO, and COBIT, cybersecurity compliance trends, GDPR and cybersecurity challenges, and the realities of incident response planning. That fluency does not mean doing every role personally. It means knowing how these domains connect, where the blind spots sit, and which failures create business exposure fastest.
It also means understanding that Director is often the first role where your success depends heavily on how well other people perform under your leadership. That is why professionals who study the path from SOC analyst to SOC manager, the journey to cybersecurity auditor, the roadmap to cybersecurity compliance officer, and the route into cybersecurity instructor or trainer work often become stronger director candidates. They learn structure, communication, governance, and capability building, not just technical execution.
Director of Information Security: 27-Capability Advancement Matrix
Use this matrix to identify the specific gaps that separate strong cybersecurity professionals from promotion-ready security directors.
| Capability | Why It Matters | Director-Level Standard | Best ACSMI Resource |
|---|---|---|---|
| Security strategy | Directors need a multi-quarter direction, not just tactical wins. | Builds a security roadmap tied to business risk and operating reality. | CISO career roadmap |
| Team leadership | The role scales through people, not individual heroics. | Coaches managers, grows specialists, and stabilizes performance. | Cybersecurity manager pathway |
| Operational governance | Security programs fail when responsibilities stay vague. | Clarifies ownership, cadence, escalation, and accountability. | Security audits guide |
| Framework fluency | Executives and auditors expect structured control language. | Maps gaps and investments to recognized frameworks. | Frameworks guide |
| Compliance judgment | Regulatory pressure shapes prioritization and board visibility. | Balances real risk reduction with audit-readiness. | Compliance trends report |
| Cloud risk management | Modern environments expand identity and configuration risk fast. | Understands IAM, exposure patterns, and cloud security governance. | Cloud security engineer guide |
| Incident readiness | Boards care quickly when response fails under pressure. | Owns readiness, escalation, lessons learned, and follow-through. | Incident response planning |
| SOC oversight | Detection maturity affects credibility across the whole program. | Knows how monitoring, triage, and escalation should work. | SOC analyst guide |
| Threat intelligence alignment | Programs weaken when they defend against everything equally. | Prioritizes by relevant adversaries and business exposure. | Threat intelligence guide |
| Identity governance | Privilege drift creates large-scale enterprise risk. | Strengthens access models, reviews, and privilege strategy. | Access control models |
| Endpoint and telemetry understanding | Directors need visibility into control effectiveness. | Can question gaps in EDR coverage and response logic. | EDR tools guide |
| SIEM program awareness | Logging without prioritization wastes budget and staff attention. | Knows how visibility, use cases, and noise reduction should improve. | SIEM overview |
| Vulnerability governance | Scanning programs often generate activity without real reduction. | Drives prioritization by exploitability, exposure, and asset value. | Vulnerability assessment guide |
| Audit partnership | Security friction increases when assurance and operations stay disconnected. | Builds productive relationships with audit and compliance teams. | Cybersecurity auditor guide |
| Executive communication | Leaders need clarity, not technical theater. | Explains exposure, tradeoffs, and investment needs crisply. | Leadership communication path |
| Program metrics | Weak metrics create weak credibility. | Uses metrics that guide action rather than decorate slides. | Incident response effectiveness report |
| Budget influence | Directors often need to justify spend and sequencing. | Frames investment around risk reduction and operational resilience. | Cybersecurity market report |
| Sector awareness | Security decisions differ across regulated and high-risk sectors. | Adapts strategy to industry-specific threats and constraints. | Financial sector analysis |
| Healthcare security literacy | Healthcare pressure mixes privacy, uptime, and clinical disruption risk. | Understands compliance and operational sensitivity. | Healthcare compliance report |
| Ransomware preparedness | Ransomware remains an executive-level concern. | Improves prevention, containment, recovery, and communication readiness. | Ransomware response guide |
| Email and human-layer defense | Human error and phishing still create large exposure. | Coordinates awareness, controls, and process improvements. | Email security solutions |
| Data protection governance | Data movement risk reaches legal and executive audiences quickly. | Understands DLP, retention, and data-handling control maturity. | DLP strategies and tools |
| Cloud and application partnership | Security leaders must work across engineering, not around it. | Influences secure architecture without becoming a bottleneck. | Application security tools |
| Talent development | Weak pipelines create burnout and fragile teams. | Builds progression paths and develops future leaders. | Instructor career guide |
| Hiring judgment | Bad hires slow programs for quarters, not weeks. | Hires for capability, potential, and team balance. | Specialized role demand forecast |
| Career leverage awareness | Promotion paths vary by market, sector, and structure. | Uses salary and market data to time the next move well. | Cybersecurity job market trends |
| Board-facing risk translation | The higher you go, the less jargon survives. | Translates security posture into business consequence and decision options. | CISO pathway guide |
2. Build the Experience Stack That Actually Creates Director-Level Credibility
The strongest Director candidates rarely come from a single narrow lane. They usually develop breadth through two or three adjacent security domains and then learn how those domains connect. Someone who began in the SOC analyst track, then added incident response capability, then matured into security analyst to cybersecurity engineer work often has stronger operational judgment than someone who stayed highly specialized without broader exposure. Someone who came through ethical hacking, penetration testing, and eventually cybersecurity consulting can also become a strong candidate if they learn governance, prioritization, and cross-functional influence.
What matters most is the sequence. Early career roles build depth. Mid-career roles should build ownership. Director-track roles build operating judgment. That means you need exposure not only to technical work but also to program-level problems: recurring incident patterns, staffing constraints, tool sprawl, audit friction, weak vendor decisions, inconsistent remediation, and the politics of prioritization. Reading internal resources on managed security service providers, best SIEM solutions, best endpoint providers, cloud security tools, and application security tools helps you understand the control environment, yet real growth comes when you learn how to govern these capabilities rather than merely admire them.
This is also where many professionals stall. They remain excellent doers but weak owners. A Director must be able to ask sharper questions. Which exposures are repeating quarter after quarter? Which teams keep generating preventable exceptions? Which investments are underperforming? Where are we measuring activity instead of risk reduction? How are phishing trends, ransomware evolution, insider threats, and cloud-environment threats changing our priorities? Those are director-level questions because they tie the security function to resource allocation and business consequence.
A smart career stack therefore includes technical grounding, control awareness, governance exposure, and leadership reps. That is why the route through cybersecurity compliance analyst work, cybersecurity auditing, cloud security engineering, threat intelligence analysis, or the move from security manager to director can each work. The path matters less than the fact that you are learning to run a security function instead of merely contributing inside one.
3. Master the Skills That Separate Senior Practitioners From Security Directors
The first differentiator is executive-grade communication. Directors need to explain posture, tradeoffs, incident implications, and investment priorities in language that works for leadership. A security leader who only speaks in tooling, attack chains, and jargon sounds expensive, not strategic. That is why it helps to study the communication style behind cybersecurity compliance leadership, privacy regulation trends, healthcare compliance realities, and government or public-sector cybersecurity demands. These areas force leaders to translate technical gaps into decisions with policy, legal, and operational consequences.
The second differentiator is prioritization discipline. Directors are constantly forced to choose between important things. They must weigh identity risk against cloud misconfiguration, endpoint visibility against staffing shortages, audit remediation against urgent incident work, and platform consolidation against tool replacement. Professionals who read across NIST adoption analysis, GDPR and best practices, data breach patterns by industry, and critical infrastructure threat assessments develop a better instinct for which issues deserve executive urgency.
The third differentiator is talent leadership. Security programs do not mature because one brilliant person works longer hours. They mature because a leader builds clearer roles, cleaner escalation, better hiring judgment, stronger coaching, and realistic growth pathways. That is why future Directors benefit from the content around cybersecurity instructor careers, curriculum development, global training providers, and future cybersecurity skills. Teaching, coaching, and team design are not side skills at director level. They are part of the job.
The fourth differentiator is business literacy. Directors need enough commercial and organizational understanding to know how security proposals will land. A recommendation that ignores delivery timelines, customer commitments, growth targets, sector regulation, or staffing realities will be resisted even if technically correct. This is where reading market and sector resources such as the global cybersecurity market report, North America cybersecurity analysis, Europe’s cybersecurity landscape, Asia-Pacific cybersecurity trends, and job-market forecasts strengthens your strategic lens.
Quick Poll: What Is Blocking Your Path to Director of Information Security?
Pick the obstacle that feels most real. The right move depends on the bottleneck, not the title you want next.
4. Build Promotion-Ready Proof Inside Your Current Role
Waiting for someone to magically declare you director material is a losing strategy. Director-track professionals build evidence before the title arrives. That evidence usually comes in five forms: ownership of a cross-functional initiative, leadership during pressure events, clear program improvement, credible communication with senior stakeholders, and development of other people. If your current role is limited, look for openings in incident readiness work, vulnerability governance, cloud security modernization, security awareness improvements, or audit and framework alignment. These projects create visibility because they affect more than one team.
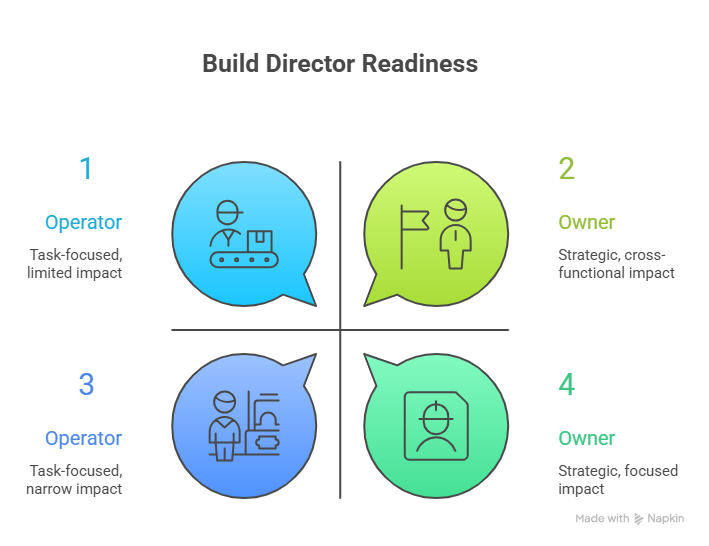
Your résumé and internal reputation must also shift from task language to ownership language. “Managed alerts” is not director-track wording. “Improved triage quality, escalation consistency, and cross-team incident coordination” is stronger. “Handled compliance findings” is weak. “Reduced audit friction by clarifying control ownership and remediation tracking” is stronger. “Worked on cloud security” is vague. “Strengthened cloud access governance and risk visibility across shared environments” is stronger. The language should increasingly resemble the concerns visible in remote versus on-site security salary analysis, salary growth for major certifications, job-market trends, and the future demand for specialized roles. The market rewards owners more than operators.
Certifications can help, although only when they support a clearer story. A technical credential may validate depth. A governance- or leadership-adjacent credential may signal broader readiness. Use the top cybersecurity certifications directory, the analysis of certifications and career advancement, and the discussion of future-valued certifications to decide whether your next move should close a credibility gap or simply deepen what you already prove elsewhere. Director readiness is rarely decided by certifications alone. It is decided by whether you look safe to trust with broader scope.
You also need evidence that you can influence laterally. Directors spend a huge amount of time working with engineering, infrastructure, compliance, audit, legal, finance, and product teams that do not report to them. That is why experience with network monitoring and security tooling, privileged access management, DLP programs, email security platforms, and cloud-security operating models becomes valuable. You learn how security choices affect workflows outside your own domain.
5. A Practical 12- to 36-Month Roadmap to Director of Information Security
In the first phase, strengthen breadth without losing your core edge. Keep excelling in your current specialty, whether that is SOC operations, incident response, ethical hacking, cloud security, or compliance analysis. Then deliberately add one adjacent domain that forces you to think more broadly. The goal is connected judgment, not random exposure.
In the second phase, look for management and program ownership reps. That may mean leading a recurring operational cadence, owning a control improvement initiative, coordinating a readiness exercise, mentoring junior staff, or becoming the person who can explain security posture to nontechnical stakeholders. Use external perspective from cybersecurity workforce shortage research, workforce demographics and inclusion analysis, and the freelance and consulting market report to understand how leadership shortages and hiring patterns affect timing.
In the third phase, sharpen your strategic lens. That means reading more than technical content. Follow top cybersecurity blogs and news sites, cybersecurity podcasts, YouTube learning channels, industry conferences, and research organizations. Pair that with forward-looking work on zero trust, AI-driven cybersecurity tools, next-generation SIEM, and the next generation of cybersecurity standards. Directors need to sound current, yet grounded.
In the final phase, make your move based on leverage, not impatience. Sometimes the better path is internal promotion after visible ownership. Sometimes it is a lateral move into a manager role with broader scope. Sometimes it is leaving for a company where your mixed background is more valuable. Use the global cybersecurity salary report, the entry-level to CISO salary progression analysis, the remote career outlook, and job-market predictions through 2030 to judge which move actually compounds long-term authority. The title matters. The scope matters more.
6. FAQs
-
In most cases, management experience makes the transition far more realistic because Director roles depend heavily on people leadership, prioritization, and cross-functional influence. That is why the route through cybersecurity manager, the progression from SOC analyst to SOC manager, and the move from security manager to director is so common. Individual excellence alone rarely proves leadership readiness at that level.
-
Several can work well. Strong candidates often come from SOC operations, cloud security engineering, incident response, cybersecurity auditing, compliance analysis, or ethical hacking and consulting. What matters most is whether you convert that background into program ownership and business translation.
-
Technical credibility still matters because it shapes judgment, credibility with practitioners, and decision quality. At the same time, director-level value comes from broader operating awareness across EDR, SIEM, vulnerability assessment, DLP, and incident response planning. The goal is not to out-hack specialists. The goal is to lead sound security decisions.
-
The best certification choice depends on your gap. Use the top cybersecurity certifications directory, the research on career advancement impact, and the discussion of future-valued certifications to decide whether you need broader leadership credibility, governance alignment, or deeper technical proof. The credential should support your story, not replace it.
-
Build evidence through ownership. Lead initiatives across teams, improve a measurable process, mentor people, handle higher-stakes communication, and show that you can connect security work to risk, compliance, and operations. Strong examples often emerge from work tied to audit readiness, cloud security maturity, incident-response improvement, and compliance priorities.
-
The two roles overlap, although the scope, reporting line, and business visibility often differ by company size and structure. The Director role usually sits closer to operational program ownership, while the CISO often carries broader executive and board-facing responsibility. Studying both the Director-level pathway and the CISO roadmap helps clarify the distinction.
-
There is no fixed timeline because the real variable is not years alone. It is whether you have accumulated enough scope, leadership proof, breadth, and trust. The market data in the salary progression analysis, the job-market trends report, and the future-skills outlook can help you judge when your profile is likely to compete.