Complete Guide to Cybersecurity Policy Analyst Career
A cybersecurity policy analyst turns security risk, regulatory pressure, operational reality, and executive decisions into usable policy. The role requires comfort with cybersecurity frameworks, security audits, compliance trends, privacy regulations, and incident response planning. This career guide shows how to build the research skill, control fluency, writing discipline, stakeholder confidence, and evidence mindset needed to become a serious cybersecurity policy analyst.
1. Understand the Cybersecurity Policy Analyst Role Clearly
A cybersecurity policy analyst studies security requirements, regulatory expectations, organizational risk, and technical controls, then converts them into policies that people can follow and auditors can review. The role connects NIST and ISO frameworks, access control models, data loss prevention strategies, encryption standards, and security incident response into practical rules for employees, systems, vendors, and leadership teams.
The pain point is that many organizations have policies that sound formal yet fail in daily operations. A password policy may ignore real identity workflows. A vendor policy may request questionnaires without verifying control evidence. A remote work policy may mention VPNs while overlooking endpoint monitoring, phishing resistance, and device ownership. A policy analyst has to close those gaps by understanding both written governance and security execution across VPN security, endpoint security providers, email security solutions, SIEM capabilities, and cloud security tools.
A strong cybersecurity policy analyst must write with precision. Every policy statement should answer who owns the control, what is required, when it applies, which exceptions are allowed, how evidence is maintained, and what happens when the policy is violated. Vague policy language creates confusion during audits, breach investigations, vendor reviews, and executive reporting. The analyst’s job is to make expectations clear enough for a SOC analyst, cybersecurity compliance officer, cybersecurity auditor, security manager, and CISO to apply without guessing.
The role is especially valuable in regulated industries. Healthcare teams need policies that support patient data protection, breach response, vendor oversight, and staff access discipline through resources like the healthcare cybersecurity threat report and healthcare compliance report. Financial institutions need policy structures that support fraud prevention, auditability, and third-party risk using insights from financial sector cybersecurity incidents and financial services cybersecurity firms. Education, government, retail, and manufacturing teams need the same discipline adjusted to their own operational risks.
| Policy Analyst Skill | Why It Matters | Career Proof to Build | Best ACSMI Resource Path |
|---|---|---|---|
| Framework mapping | Policy work needs a defensible structure tied to recognized security expectations. | NIST, ISO, and COBIT control map. | Cybersecurity frameworks guide |
| Audit readiness | Policies must produce evidence when auditors ask for proof. | Policy evidence checklist. | Security audits guide |
| Compliance analysis | Analysts translate regulatory pressure into practical requirements. | Regulation-to-policy crosswalk. | Compliance trends report |
| Privacy policy writing | Data protection rules must align with collection, use, sharing, retention, and deletion practices. | Data handling policy draft. | Privacy regulations guide |
| Incident policy design | Response teams need clear triggers, roles, escalation points, and evidence rules. | Incident response policy. | Incident response plan guide |
| Access governance | Weak access policy creates privilege creep and audit exposure. | RBAC policy and review schedule. | Access control models |
| Encryption policy | Organizations need consistent rules for protecting stored and transmitted data. | Encryption standard document. | Encryption standards guide |
| PKI understanding | Certificate, identity, and trust-chain policy affects secure systems. | Certificate lifecycle policy. | PKI components guide |
| DLP governance | Data protection policies must balance security enforcement with business usability. | DLP policy exception model. | DLP strategies guide |
| Endpoint policy | Device rules shape patching, monitoring, acceptable use, and response readiness. | Endpoint security policy. | Endpoint security providers |
| SIEM and logging policy | Teams need rules for log collection, retention, monitoring, and investigation evidence. | Logging and monitoring policy. | SIEM overview |
| Email security policy | Phishing risk demands clear controls for filtering, reporting, and user behavior. | Email security policy brief. | Email security solutions |
| Ransomware policy | Clear backup, reporting, containment, and communication rules reduce crisis confusion. | Ransomware readiness policy. | Ransomware response guide |
| Cloud policy | Cloud environments require identity, storage, workload, vendor, and configuration discipline. | Cloud usage policy. | Cloud security tools |
| Application security policy | Development teams need secure coding, testing, release, and vulnerability rules. | AppSec policy checklist. | Application security tools |
| Vendor policy | Third-party systems can create security and compliance exposure. | Vendor risk policy. | Cybersecurity consulting firms |
| Healthcare policy focus | Patient-data environments demand careful access, retention, breach, and vendor rules. | Healthcare data protection policy. | Healthcare compliance report |
| Financial policy focus | Financial organizations need stronger governance for fraud, data, access, and incident reporting. | Financial security policy memo. | Financial sector incidents |
| Government policy focus | Public-sector systems need procurement, mission, access, and data-handling discipline. | Public-sector policy control map. | Government cybersecurity firms |
| Education policy focus | Schools and universities need clear rules for student data, devices, access, and cloud tools. | Education security policy brief. | Education cybersecurity directory |
| SMB policy simplification | Smaller organizations need policies that are realistic, enforceable, and budget-aware. | Small-business policy starter pack. | Small business solutions |
| Threat intelligence awareness | Policy analysts need threat context to keep rules relevant. | Threat-informed policy update memo. | Threat intelligence guide |
| Vulnerability policy | Patch, scanning, remediation, and exception rules need measurable deadlines. | Vulnerability management policy. | Vulnerability assessment guide |
| Security awareness policy | Human-risk programs need training, phishing reporting, and accountability rules. | Awareness and training policy. | Security awareness platforms |
| Career positioning | Analysts need proof that connects research, writing, and security judgment. | Policy portfolio and résumé evidence. | Cybersecurity job market trends |
| Certification planning | Targeted credentials help validate cybersecurity and compliance knowledge. | Certification roadmap tied to policy gaps. | Cybersecurity certifications directory |
| Salary strategy | Career decisions improve when analysts understand compensation signals. | Salary benchmark and promotion plan. | Cybersecurity salary report |
| Executive communication | Policy analysts must translate risk into decisions leaders can fund and enforce. | Board-ready policy risk briefing. | CISO roadmap |
2. Build the Core Skills That Make Policy Work Useful
The first skill is regulatory and framework interpretation. A policy analyst must read security standards, privacy expectations, industry requirements, and internal risk language without turning them into bloated documents. Start with cybersecurity frameworks, NIST adoption, GDPR cybersecurity challenges, privacy regulation trends, and future compliance predictions. The goal is to extract requirements that can be assigned, tested, and enforced.
The second skill is control literacy. Policies become weak when analysts write rules without knowing how controls operate. An access policy should reflect DAC, MAC, and RBAC models. A data protection policy should reflect DLP strategies, encryption standards, cloud security tools, and endpoint detection and response. A monitoring policy should reflect SIEM workflows, intrusion detection systems, and network monitoring tools.
The third skill is policy writing. Good cybersecurity policies use specific verbs, clear scope, accountable owners, measurable review cycles, exception handling, and evidence requirements. Weak policies overuse phrases like “as appropriate,” “where possible,” and “employees should be careful.” A serious policy analyst turns those vague lines into enforceable requirements: privileged access must be reviewed quarterly, critical vulnerabilities must follow defined remediation windows, security incidents must be reported through a named channel, and exceptions must have an owner and expiration date. This kind of writing supports security audits, incident response plans, vulnerability assessment, and cybersecurity compliance.
The fourth skill is stakeholder interviewing. Policies fail when they are written in isolation. A policy analyst should interview IT admins, SOC analysts, HR, legal, compliance, finance, procurement, engineering, executives, and business-unit leaders. The analyst must uncover how work is actually done, where shadow processes exist, which controls are ignored, and where employees need clearer guidance. This matters for remote cybersecurity careers, SMB cybersecurity solutions, healthcare cybersecurity, financial cybersecurity, and education-sector cybersecurity.
3. Choose the Best Entry Path Into Cybersecurity Policy Analysis
A compliance background gives you a strong starting point because you already understand documentation, controls, reviews, and evidence. Your next move is to deepen technical fluency through security information and event management, firewall technologies, VPN security, endpoint security, and application security tools. This prevents your policy work from sounding disconnected from real systems.
A cybersecurity operations background gives you practical security credibility. Your next move is to build stronger writing, governance, and compliance interpretation. SOC analysts, incident responders, threat intelligence analysts, and security engineers can transition well because they know where policy gaps create operational pain. Study SOC analyst career paths, incident responder roles, threat intelligence careers, security analyst advancement, and cybersecurity compliance analyst pathways.
A legal, privacy, or risk background can also lead into cybersecurity policy analysis. Your strength may be interpretation, documentation, and executive caution. Your gap may be technical control awareness, incident workflow, cloud environments, and monitoring language. Build fluency through privacy regulations, GDPR cybersecurity, data breach reporting, cloud security trends, and AI in cybersecurity.
An IT support or systems administration background gives you operational insight into devices, access, tickets, user behavior, and tool limitations. Your transition should focus on governance language, compliance structure, and policy evidence. Start with the IT support to cybersecurity analyst pathway, then study vulnerability assessment, network monitoring tools, email security solutions, and security awareness platforms. Your daily experience with user mistakes can become valuable policy insight.
Quick Poll: What Is Blocking Your Cybersecurity Policy Analyst Career Move?
Choose the gap that would make your policy work feel weakest in a real security, audit, or compliance meeting.
4. Build a Portfolio That Proves Policy Analyst Readiness
A cybersecurity policy analyst portfolio should show more than interest. It should prove that you can research requirements, understand security controls, write enforceable language, and prepare evidence for review. Start with an access control policy based on DAC, MAC, and RBAC, privileged access management, zero trust security, security audits, and NIST framework adoption. Include role assignment, approval workflow, periodic review, emergency access, and evidence requirements.
Your second portfolio artifact should be an incident response policy. This policy should define reportable events, response roles, escalation levels, evidence handling, communications approval, containment expectations, and post-incident review. Use incident response planning, ransomware response, data breach mitigation, phishing trends, and insider threat prevention to make the policy practical rather than ceremonial.
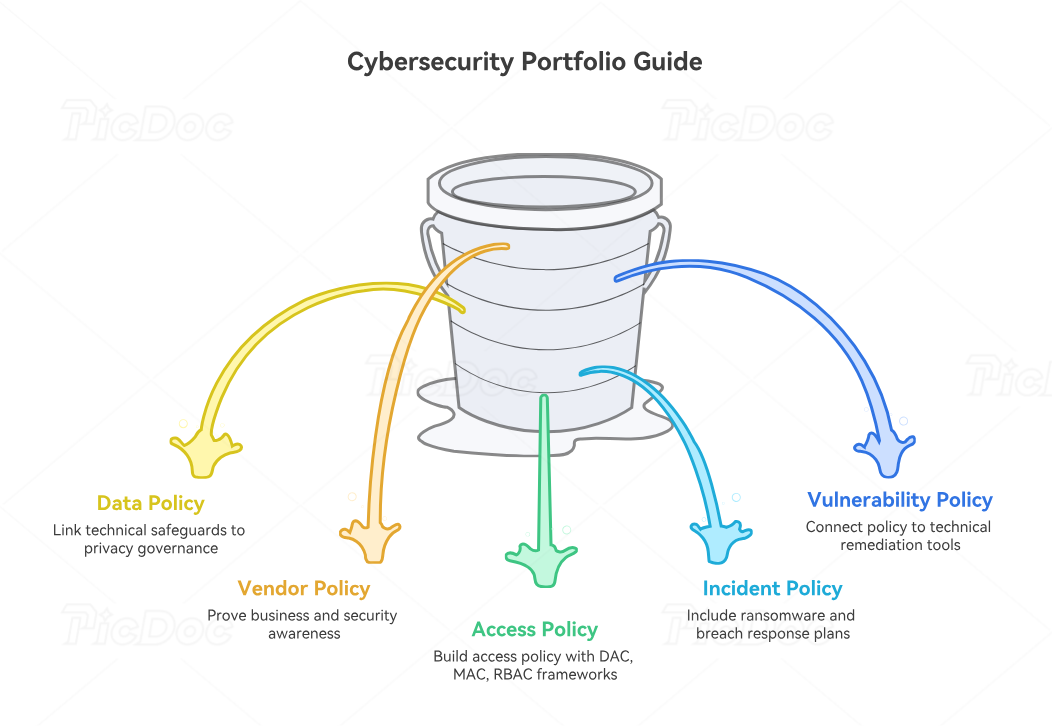
Your third artifact should be a data protection policy. Cover data classification, collection limits, storage rules, access controls, encryption, sharing, retention, deletion, and vendor processing. Reference data loss prevention, DLP software, encryption standards, cloud security tools, and privacy regulations. This artifact is powerful because it connects technical safeguards with privacy governance.
Your fourth artifact should be a vulnerability management policy. This should define asset scope, scanning frequency, severity categories, remediation timelines, exception handling, compensating controls, and reporting. Use vulnerability assessment techniques, top vulnerability scanners, penetration testing tools, ethical hacking career guidance, and OSCP penetration testing pathways to show that you understand how policy supports technical remediation.
Your fifth artifact should be a vendor risk policy. Include vendor classification, security questionnaires, contract clauses, data processing review, incident notification expectations, audit rights, and renewal review. Tie this to cybersecurity consulting firms, MSSP comparisons, healthcare cybersecurity firms, financial services cybersecurity providers, and small business cybersecurity solutions. Vendor policy work proves business awareness, because third-party risk often sits between procurement pressure and security accountability.
5. Follow a 12- to 36-Month Career Roadmap
During the first 90 days, build vocabulary and policy structure. Read core resources on cybersecurity frameworks, security audits, compliance trends, access control, and incident response. Draft one short policy each week. Keep each draft structured around purpose, scope, requirements, roles, exceptions, evidence, review cycle, and enforcement. This rhythm builds skill faster than passive reading.
During months 4 to 12, create role-adjacent experience. Look for junior GRC analyst, cybersecurity compliance analyst, IT policy analyst, security documentation specialist, risk analyst, audit analyst, privacy operations analyst, or SOC governance support roles. Use cybersecurity compliance analyst guidance, cybersecurity auditor guidance, SOC analyst career paths, cybersecurity certification directories, and free cybersecurity courses to fill knowledge gaps while producing visible artifacts.
During months 13 to 24, own policy lifecycle work. That means you should participate in policy review cycles, control mapping, audit evidence collection, exception tracking, risk registers, incident tabletop documentation, vendor review, security awareness updates, and executive reporting. Build stronger sector knowledge through healthcare cybersecurity predictions, finance cybersecurity trends, government cybersecurity predictions, manufacturing cybersecurity trends, and retail cybersecurity predictions.
During months 25 to 36, position yourself for senior analyst, GRC lead, security policy manager, cybersecurity compliance manager, or governance advisor roles. Your résumé should show policy improvements, audit results, control mapping, exception reduction, training rollout, incident documentation, or vendor review maturity. Use cybersecurity job market trends, salary progression analysis, certification salary growth, workforce shortage research, and future cybersecurity skills to choose moves with long-term value.
A strong cybersecurity policy analyst can eventually move into cybersecurity compliance officer, GRC manager, privacy officer, cybersecurity auditor, risk manager, security governance lead, or CISO-track leadership. The career path works because policy sits at the center of enforcement, evidence, education, and executive accountability. When policies are clear, security teams waste less time arguing about ownership. When policies are weak, every audit, incident, vendor review, and exception request becomes harder than it should be.
6. FAQs About Cybersecurity Policy Analyst Careers
-
A cybersecurity policy analyst researches security requirements, writes policies, maps controls to frameworks, supports audits, tracks exceptions, and helps teams understand enforceable security rules. The role often touches cybersecurity frameworks, security audits, incident response, data loss prevention, and privacy regulations.
-
The role is technical enough that you must understand controls, systems, threats, and evidence. You may write policies for access control, encryption, SIEM logging, endpoint security, and cloud security. Coding depth helps in some environments, while control fluency and clear writing matter more for most policy analyst roles.
-
Cybersecurity, information systems, public policy, law, risk management, compliance, business, or IT backgrounds can all work. The strongest candidates combine writing ability with security understanding and evidence discipline. Helpful preparation includes cybersecurity compliance officer pathways, cybersecurity auditor training, SOC analyst fundamentals, free cybersecurity learning resources, and cybersecurity certifications.
-
Useful certifications depend on your gap. If you need security fundamentals, start with broad cybersecurity credentials using ACSMI’s certification directory. If you need governance depth, focus on compliance, audit, risk, and framework-oriented learning through cybersecurity compliance trends, NIST adoption, security audits, and future compliance regulation.
-
Build sample policies for access control, incident response, vulnerability management, vendor risk, data protection, acceptable use, cloud security, and security awareness. Add a control crosswalk, risk register sample, exception request form, evidence checklist, and policy review calendar. Strong portfolios connect to real security domains like vulnerability assessment, ransomware response, DLP, application security, and vendor cybersecurity.
-
Beginners often write policies that sound official while missing ownership, scope, evidence, exceptions, and enforcement. A better approach is to write policy language that a security engineer, HR manager, auditor, and executive can all act on. Study security audit processes, incident response execution, access control models, cloud security, and cybersecurity frameworks before writing advanced policies.