Step-by-Step Career Path to Cybersecurity Risk Management Specialist
Cybersecurity risk management is where technical evidence becomes executive action. A strong specialist does more than list vulnerabilities; they translate exposure, likelihood, business impact, control gaps, compliance pressure, and remediation urgency into decisions leaders can fund. This career path rewards professionals who can connect security audits, cybersecurity frameworks, vulnerability assessment, compliance trends, and salary growth strategy into a practical roadmap.
1. Understand What a Cybersecurity Risk Management Specialist Actually Owns
A cybersecurity risk management specialist sits between technical teams, compliance stakeholders, business owners, auditors, and leadership. The role exists because organizations drown in alerts, tool reports, scan findings, vendor questionnaires, policy exceptions, audit notes, cloud misconfigurations, and board-level risk questions. Someone has to convert that noise into defensible priority. That is why this path overlaps with SOC analyst work, cybersecurity compliance officer roles, cybersecurity auditor careers, incident response improvement, and CISO pathway planning.
The real pain point is that many early cybersecurity professionals collect findings without learning how risk moves through an organization. A critical vulnerability on an isolated lab server may matter less than a medium-severity identity weakness tied to payroll, patient data, payment systems, or production cloud access. A specialist must understand asset value, threat activity, control maturity, business dependency, regulatory exposure, and remediation feasibility. That requires fluency across access control models, endpoint security providers, cloud security tools, data loss prevention software, and privileged access management.
The step-by-step path begins with one mindset shift: risk management is a decision discipline. Tools help gather signals, frameworks help organize evidence, and audits help prove accountability, but the specialist earns trust by showing leaders which risk needs action now, which risk can be accepted with conditions, which risk needs compensating controls, and which risk signals deeper security debt. That is why the best candidates study NIST framework adoption, GDPR cybersecurity challenges, healthcare cybersecurity compliance, financial-sector incidents, and critical infrastructure threats.
Cybersecurity Risk Management Career Path: 26-Step Advancement Matrix
| Career Step | Skill to Build | Proof Employers Want | ACSMI Resource Link |
|---|---|---|---|
| 1. Learn security fundamentals | Controls, threats, assets, CIA triad, basic governance | Can explain risk without hiding behind buzzwords | Free cybersecurity courses |
| 2. Build analyst literacy | Alert triage, evidence review, escalation logic | Understands how operational risk is first detected | SOC analyst guide |
| 3. Study frameworks | NIST, ISO, COBIT, control mapping | Can organize risk into repeatable categories | Cybersecurity frameworks |
| 4. Learn audit mechanics | Evidence requests, testing, findings, remediation tracking | Can support audit without panic or guesswork | Security audit process |
| 5. Master vulnerability context | CVSS, exploitability, asset criticality, compensating controls | Can separate scary scanner output from real exposure | Vulnerability assessment |
| 6. Understand SIEM evidence | Logs, correlation, detection coverage, alert quality | Can ask better questions about monitoring gaps | Best SIEM solutions |
| 7. Learn endpoint exposure | EDR, malware risk, device coverage, isolation capability | Can evaluate endpoint-related business risk | EDR tools guide |
| 8. Study identity risk | RBAC, privileged access, least privilege, access review | Can identify where attackers could inherit power | Access control models |
| 9. Learn compliance language | Requirements, policies, control objectives, exceptions | Can connect security controls to regulatory pressure | Compliance trends |
| 10. Practice risk scoring | Likelihood, impact, inherent risk, residual risk | Can defend ratings without emotional overstatement | Certification impact report |
| 11. Build vendor-risk awareness | Questionnaires, SOC 2 evidence, third-party concentration risk | Can assess external dependency risk clearly | Consulting firm analysis |
| 12. Learn cloud risk | Misconfiguration, IAM, storage exposure, workload protection | Can evaluate cloud control gaps beyond checklist thinking | Cloud security engineer guide |
| 13. Study incident impact | Containment cost, business downtime, root cause, lessons learned | Can turn incidents into control improvement plans | Incident responder pathway |
| 14. Learn ransomware exposure | Backup resilience, lateral movement, recovery readiness | Can explain operational impact in business terms | Ransomware analysis |
| 15. Study phishing risk | User behavior, email controls, awareness, credential theft | Can connect human risk to technical safeguards | Phishing trends |
| 16. Build reporting skill | Dashboards, heat maps, KRIs, executive summaries | Can brief leaders without overwhelming them | Market report |
| 17. Learn sector risk | Healthcare, finance, education, retail, government exposure | Can tailor risk advice to the industry | Healthcare cybersecurity firms |
| 18. Earn targeted credentials | Security+, CySA+, CISSP-track, audit or GRC credentials | Can show structured learning and career intent | Certification directory |
| 19. Build a risk register | Ownership, rating, treatment plan, due date, control linkage | Can manage risk as an operating system | Compliance officer roadmap |
| 20. Practice remediation governance | Exception handling, risk acceptance, escalation, evidence closure | Can prevent findings from dying in spreadsheets | Cybersecurity auditor guide |
| 21. Learn metrics that matter | MTTR, patch aging, control coverage, exception volume | Can measure risk movement over time | Job market trends |
| 22. Build business communication | Risk memos, leadership briefs, plain-English recommendations | Can influence teams without formal authority | Cybersecurity manager pathway |
| 23. Specialize in a domain | Cloud, privacy, OT, vendor risk, compliance, application risk | Can become the risk owner for a high-value area | Future skills |
| 24. Lead risk workshops | Facilitation, scenario planning, stakeholder alignment | Can surface hidden risks before incidents expose them | Zero trust trends |
| 25. Own risk governance | Committee reporting, policy lifecycle, enterprise risk alignment | Can operate at senior stakeholder level | Specialist to CISO |
| 26. Prepare for leadership | Budget defense, risk appetite, security strategy, executive advising | Can connect risk posture to enterprise direction | VP of cybersecurity path |
2. Build the Technical Foundation Before You Speak the Language of Risk
The strongest risk specialists can talk to engineers without sounding vague and talk to executives without drowning them in tool output. Start with technical fundamentals: networks, endpoints, identity, cloud services, email security, logging, vulnerabilities, data protection, and incident response. You do not need to become the deepest exploit developer in the room, but you must know enough to challenge weak assumptions. A risk score built on poor technical understanding collapses under scrutiny from penetration testing teams, ethical hacking specialists, cloud security engineers, network monitoring teams, and application security teams.
A practical beginner sequence is simple: learn how attacks happen, learn how controls reduce attack paths, then learn how failure creates business damage. For example, phishing risk is not only about employees clicking emails; it is about credential capture, MFA fatigue, mailbox rule abuse, payment fraud, lateral movement, and incident response delay. Endpoint risk is not only about antivirus coverage; it is about detection quality, device visibility, isolation speed, patch hygiene, and privilege control. That is why a career-ready foundation should include phishing prevention strategy, endpoint security effectiveness, EDR tool evaluation, PAM solution comparison, and email security solutions.
Once your technical base is credible, begin reading risk through assets. Which systems process revenue? Which store regulated data? Which support patient care, financial transactions, manufacturing uptime, logistics, or student records? A vulnerability becomes more meaningful when it is tied to a business process and a threat scenario. This is where sector awareness creates career leverage. A specialist who understands financial services cybersecurity, healthcare-specific cybersecurity, government cybersecurity providers, education-sector solutions, and retail e-commerce risk can speak with sharper context.
The pain point employers notice quickly is shallow confidence. Candidates often say they understand risk, then treat all “high” findings the same. A better candidate can explain why an internet-facing system with weak authentication may deserve immediate escalation, why an unpatched internal asset may need network segmentation while the patch cycle is coordinated, and why a vendor with poor access controls can create board-level exposure. Build that judgment through vulnerability scanner research, penetration testing tools, data breach analysis, insider threat prevention, and cloud threat analysis.
3. Turn Framework Knowledge Into Business-Ready Risk Decisions
Frameworks matter because they prevent risk management from becoming opinion theater. NIST, ISO, COBIT, CIS Controls, and sector-specific requirements give teams a shared structure for identifying control objectives, testing maturity, documenting gaps, and proving accountability. A cybersecurity risk management specialist should know how to map risks to controls, owners, evidence, treatment plans, and business outcomes. This is where NIST cybersecurity framework adoption, cybersecurity standards predictions, compliance officer career planning, privacy regulation trends, and audit practice evolution become directly useful.
A strong framework workflow starts with scope. Which assets, teams, processes, vendors, systems, data classes, and jurisdictions matter? Then comes risk identification: what could go wrong, how likely it is, what impact it would create, and what controls already exist. Next comes assessment: compare control design and operating effectiveness against the desired maturity. Then comes treatment: remediate, transfer, accept, avoid, or monitor. Finally comes reporting: show residual risk, trend direction, accountability, and decision requests. This workflow connects naturally with security audit best practices, GDPR compliance challenges, healthcare compliance reporting, small business cybersecurity legislation, and global cybersecurity market pressure.
The specialist’s biggest value appears when stakeholders disagree. Engineering may say a fix is complex. Legal may worry about regulatory exposure. Finance may resist funding. Operations may fear downtime. Leadership may ask for a clean answer when the truth has tradeoffs. Your job is to turn scattered pressure into a structured decision: what risk exists, what evidence supports it, what options are available, what each option costs, what deadline matters, and what happens if the organization waits. That type of communication prepares you for cybersecurity manager roles, security manager advancement, director of information security pathways, chief security architect careers, and CISO leadership progression.
Avoid the career-killing mistake of treating frameworks like paperwork. A framework is useful when it improves decisions, reduces blind spots, strengthens evidence, and gives leaders confidence that risk is being handled through a controlled process. If your framework work produces a spreadsheet nobody trusts, it has failed. If your framework work gives asset owners clear priorities, audit teams clean evidence, security teams justified investment, and executives a usable risk view, it has succeeded. Build that level of output by studying cybersecurity compliance trends, cybersecurity workforce shortage data, job market predictions, future cybersecurity skills, and automation workforce trends.
Quick Poll: What Is Your Biggest Blocker to Becoming a Cybersecurity Risk Management Specialist?
Pick the obstacle that feels most urgent, because your next career step changes when the bottleneck is clear.
4. Create a Portfolio That Proves You Can Prioritize Risk Under Pressure
A cybersecurity risk management portfolio should prove judgment, structure, and communication. Recruiters and hiring managers do not only want to hear that you “understand risk.” They want to see examples of how you identify assets, classify exposure, rate likelihood and impact, connect findings to controls, recommend treatment, and explain residual risk. Build portfolio pieces around scenarios tied to data breach mitigation, ransomware impact, cloud environment threats, healthcare cybersecurity risks, and financial cybersecurity incidents.
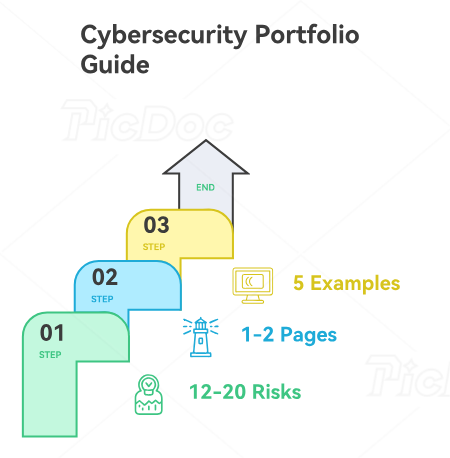
Start with a risk register project. Create a fictional company with business units, critical assets, vendors, data types, and regulatory obligations. Add 12 to 20 realistic risks: exposed storage, privileged access sprawl, weak vendor review, delayed patching, missing incident tabletop testing, poor backup validation, inconsistent endpoint coverage, weak email controls, excessive admin permissions, and incomplete logging. For each risk, include description, threat scenario, impacted asset, inherent rating, existing controls, residual rating, treatment plan, owner, due date, evidence needed, and escalation trigger. Use ACSMI resources on DLP software, SIEM solutions, endpoint providers, email security solutions, and cloud security tools to make control options realistic.
Your second portfolio asset should be an executive risk brief. Keep it to one or two pages. Summarize the top five risks, business impact, recommended action, required investment, deadline, and decision owner. Avoid jargon-heavy paragraphs that force leaders to decode your thinking. Use a heat map only if the scoring logic is clear. Show risk movement: what improved, what worsened, what remains blocked, and what decision is needed. This prepares you for security leadership roles, cybersecurity program manager work, security specialist advancement, IT management to cybersecurity leadership, and senior security analyst growth.
Your third portfolio asset should be an audit evidence tracker. Include control requirement, evidence type, evidence owner, collection status, test result, deficiency, remediation owner, target date, and closure proof. This shows employers you understand the discipline behind risk claims. Many candidates can talk about risk in theory; fewer can show how a finding moves from discovery to closure. Add one example for access review, one for vulnerability remediation, one for backup testing, one for vendor review, and one for incident response tabletop evidence. Link the logic to cybersecurity auditor guidance, audit processes, compliance analyst careers, GDPR 2.0 predictions, and future compliance regulations.
5. Move From Analyst-Level Risk Work Into Specialist-Level Ownership
The move from analyst to specialist happens when you stop waiting for assignments and start owning risk outcomes. At analyst level, you may collect evidence, update trackers, prepare reports, follow checklists, or support audits. At specialist level, you challenge unclear ratings, propose treatment options, run stakeholder meetings, explain tradeoffs, and make sure accepted risks are documented with the right accountability. This is why the path connects strongly with security analyst advancement, senior cybersecurity analyst pathways, SOC manager growth, cybersecurity manager certifications, and director-level security progression.
Certifications can help, but choose them based on role target. For early credibility, Security+ can support baseline security knowledge, while CySA+ can help if your risk work leans toward detection, vulnerability management, and defensive operations. For audit and governance-heavy routes, look for credentials that validate control assessment, governance, compliance, and risk thinking. For long-term senior risk leadership, CISSP-aligned knowledge areas matter because they connect security architecture, governance, access control, operations, software security, and risk management. Use ACSMI’s cybersecurity certification directory, certification career impact report, certification salary growth analysis, certifications of the future, and cybersecurity bootcamp directory to plan deliberately.
The strongest job search strategy is to target roles with adjacent titles. Search for cybersecurity risk analyst, GRC analyst, security compliance analyst, IT risk analyst, third-party risk analyst, vulnerability risk analyst, technology risk specialist, cyber governance analyst, and information security risk specialist. Read postings carefully. Some roles are control-testing heavy, some are vendor-risk heavy, some are audit-heavy, some are technical risk-heavy, and some are executive-reporting heavy. Align your résumé with the route you want, using evidence from IT support to cyber analyst transitions, security analyst to engineer paths, threat intelligence analyst careers, incident responder pathways, and cybersecurity job market predictions.
Interview preparation should focus on scenarios. Be ready to explain how you would prioritize five overdue vulnerabilities, respond to an audit finding with unclear ownership, assess a vendor handling sensitive data, brief leadership on ransomware readiness, or handle a business unit that wants to accept risk without understanding exposure. The winning answer shows evidence, tradeoffs, communication, and accountability. Employers trust candidates who can say what they would inspect, who they would involve, how they would rate risk, what options they would present, and how they would document the decision. Build examples using ransomware evolution insights, AI-powered cyberattack predictions, zero trust innovations, cloud security trends, and specialized role demand.
6. FAQs About Becoming a Cybersecurity Risk Management Specialist
-
Start by turning your IT knowledge into security-risk language. If you understand systems, networks, endpoints, tickets, access requests, patching, or cloud administration, you already have exposure to operational risk. Build a simple risk register from real IT scenarios, then connect each item to business impact, controls, and remediation ownership. Pair that with IT support to cybersecurity analyst guidance, cybersecurity analyst advancement, security audits, vulnerability assessment, and cybersecurity frameworks.
-
You need enough technical depth to understand evidence, question weak assumptions, and avoid generic risk ratings. You should understand vulnerabilities, identity, endpoint protection, logging, cloud exposure, email threats, incident response, and data protection. You can build that foundation through SIEM solution research, EDR tools, cloud security tools, email security solutions, and PAM solutions.
-
The right certification depends on your entry point. Security+ supports baseline security credibility, CySA+ supports defensive and vulnerability-oriented risk work, and governance or audit-focused credentials can support GRC, compliance, and control assessment roles. Senior risk paths often benefit from CISSP-aligned domains because they connect governance, architecture, operations, access control, and risk strategy. Use ACSMI’s certification directory, certification impact report, salary growth analysis, future certification trends, and bootcamp directory.
-
Include a risk register, executive risk brief, audit evidence tracker, vendor-risk review, vulnerability prioritization memo, and one scenario-based remediation plan. Each piece should show how you identify the asset, describe the threat, rate inherent and residual risk, map controls, assign ownership, and recommend treatment. Strong portfolio work can draw from data breach reports, ransomware analysis, incident response effectiveness, healthcare threat reporting, and financial incident analysis.
-
Search for IT risk analyst, cyber risk analyst, GRC analyst, security compliance analyst, technology risk specialist, third-party risk analyst, information security risk analyst, cybersecurity governance analyst, and vulnerability risk analyst. Then align your résumé to the posting’s emphasis: audit, vendor risk, technical exposure, compliance, cloud, or executive reporting. Use related ACSMI pathways such as cybersecurity compliance officer, cybersecurity auditor, threat intelligence analyst, incident responder, and cybersecurity manager.
-
Create a one-page executive brief that ranks the top risks, explains business impact, shows treatment options, names decision owners, and states the cost of delay. Avoid tool-heavy language unless the audience needs it. Leaders want clarity, accountability, and decision support. Practice turning technical evidence from vulnerability assessments, security audits, NIST adoption, compliance trends, and CISO advancement planning into clear recommendations.
-
This role can grow into senior cyber risk specialist, GRC manager, security compliance manager, technology risk manager, director of information security, cybersecurity program manager, chief security architect, VP of cybersecurity, or CISO. The strongest growth comes from combining technical credibility, framework discipline, business communication, and leadership judgment. Map your next step through cybersecurity program management, director of information security, chief security architect, VP of cybersecurity, and specialist-to-CISO advancement.