How to Build a Successful Career as a Cybersecurity Content Creator
Cybersecurity content creation looks easy from the outside. People see articles, videos, newsletters, LinkedIn threads, and tool reviews, then assume the job is mostly opinion, trend-chasing, and surface commentary. The real version is much harder. Strong creators translate technical complexity into clarity, earn trust without hype, and build an audience that comes back because the material improves decisions, careers, and security outcomes.
That makes this path far more than “posting about cyber.” A successful cybersecurity content creator becomes a researcher, explainer, curator, educator, market interpreter, and credibility bridge between practitioners, employers, buyers, and learners. Done well, it can turn technical knowledge into authority, income, opportunity, and long-term career resilience.
1. Why Cybersecurity Content Creation Has Become a Serious Career Path
A lot of professionals still underestimate this lane because they confuse content creation with casual posting. That misunderstanding causes talented specialists to miss one of the highest-leverage career plays in the field. Good cybersecurity content influences how people learn, what tools they evaluate, which certifications they pursue, how leaders think about risk, and where employers place trust. That is real market power.
The demand exists because the field is noisy. Buyers are overwhelmed by vendor claims. Learners are confused by shallow roadmaps. Career changers waste months studying the wrong material. Security leaders need faster ways to understand tool categories, workforce shifts, regulatory pressure, and sector-specific risks. A creator who can explain these clearly becomes useful fast. That is why content that draws from resources like the best cybersecurity blogs and industry news sites, the directory of top cybersecurity podcasts for industry professionals, the best YouTube channels for cybersecurity learning and updates, and the top cybersecurity books directory performs so well when it is filtered through real judgment instead of recycled summaries.
A successful cybersecurity content creator does not just gather information. They reduce friction. They help a junior analyst understand whether to pursue the path in the complete guide to becoming a security operations center SOC analyst or take a route closer to the career roadmap from security analyst to cybersecurity engineer. They help tool buyers compare the best cloud security tools, the best application security tools, the best privileged access management PAM solutions, and the best DLP software without drowning in marketing fog.
This matters because content creation can compound faster than many traditional cybersecurity roles. A strong analyst may solve problems for one employer. A strong creator can influence hiring managers, learners, vendors, founders, training providers, consultants, and security leaders at once. Content also creates portable career capital. If you understand emerging markets through the global cybersecurity market report, workforce realities through the cybersecurity workforce shortage study, salary movement through the entry-level to CISO salary progression analysis, and future opportunity through the cybersecurity job market trends report, your content stops being filler and starts becoming infrastructure for other people’s decisions.
The professionals who win here usually understand one hard truth early: audience trust is brutally hard to earn and incredibly easy to destroy. That is why the job is not to sound intelligent. The job is to be useful under scrutiny. Anyone can post a prediction. Far fewer can build a body of work that helps readers navigate the realities of remote cybersecurity careers, the pressure of automation and the future cybersecurity workforce, and the changing employer expectations inside the future skills for cybersecurity professionals conversation.
| Content Asset | Why It Builds a Career | Best Use Case | What It Can Lead To |
|---|---|---|---|
| Long-form tool comparison article | Builds search visibility and buyer trust | Tool-category education | Affiliate, sponsorship, consulting |
| Industry trend report breakdown | Shows analytical depth and market awareness | Research commentary | Thought leadership, advisory work |
| Career roadmap guide | Pulls in ambitious early-career readers | Career education | Audience growth and email signups |
| Newsletter | Creates direct audience ownership | Weekly industry curation | Sponsorship and product launches |
| LinkedIn post series | Builds discoverability fast | Short-form authority building | Inbound opportunities |
| Video explainers | Improves trust through voice and presence | Concept clarification | Course creation, speaking |
| Sector-specific threat analysis | Signals domain relevance | Finance, healthcare, retail, education | Niche authority and B2B work |
| Certification comparison guide | Attracts intent-rich readers | Career decision support | Training partnerships |
| Interview with practitioner | Adds credibility and fresh perspective | Community building | Network expansion |
| Mini course or workshop | Turns audience trust into product value | Skill-based teaching | Training revenue |
| Original survey report | Differentiates you from commentary-only creators | Workforce or salary insights | Press mentions, backlinks |
| Tool stack framework | Simplifies buyer confusion | Category mapping | Consulting or vendor analysis |
| Beginner glossary content | Captures top-of-funnel learning traffic | Foundational education | Audience trust and retention |
| Case-study deconstruction | Shows practical thinking, not abstract theory | Breach and incident lessons | High-authority reputation |
| Vendor-neutral comparison chart | Builds decision-making credibility | Tool evaluation support | Buyer audience loyalty |
| Job market analysis post | Taps into career urgency and salary pain | Role trend commentary | Recruiter and learner attention |
| Template or checklist | Provides immediate practical value | IR, audits, risk reviews | Lead generation |
| Conference recap | Shows market fluency and curation skill | Event-based content | Industry visibility |
| Research organization summary | Improves source quality and trust | Research digest | Analyst brand positioning |
| Threat prediction article | Performs well when grounded in evidence | Forward-looking analysis | Thought leadership growth |
| Compliance explainer | Appeals to governance-heavy audiences | Regulatory translation | Enterprise trust building |
| Framework tutorial | Establishes teaching ability | NIST, ISO, COBIT content | Training and educator pathways |
| Podcast guest appearance | Accelerates reputation transfer | Expert commentary | Audience crossover growth |
| Freelance research brief | Monetizes analytical writing early | Client deliverables | Retainer or contract work |
| Community Q&A content | Sharpens empathy and topic selection | Audience pain-point mining | Higher content-market fit |
| Resource hub or directory | Becomes a linkable evergreen asset | High-intent reference content | Organic traffic and authority |
2. Pick the Right Content Lane Before You Start Posting Everywhere
Many people fail in this space because they try to speak to everyone. That creates generic output, weak positioning, and almost no memorability. Cybersecurity content rewards specificity. Before you build a content engine, you need to choose a lane that matches both your expertise and audience demand.
One strong lane is career content. That includes breakdowns around the top cybersecurity certifications directory, the salary growth analysis for CISSP, CEH, and security certifications, the impact of cybersecurity certifications on career advancement, and the broader global cybersecurity salary report. This lane works because ambition creates repeat visits. People return when your content helps them earn more, pivot faster, and avoid dead-end skill choices.
Another strong lane is tools and buyer education. A creator who can compare the best SIEM solutions, the best EDR tools, the leading endpoint security providers, the top vulnerability scanners, and the top network monitoring and security tools can attract practitioners, buyers, and vendors at once. This works best when you explain tradeoffs instead of pretending there is one perfect stack for every environment.
A third lane is threat and sector analysis. The strongest versions do not merely report incidents. They interpret patterns. You can build authority by connecting the state of ransomware report, the data breach report on industries most at risk, the healthcare cybersecurity threat report, the financial sector cybersecurity incidents analysis, and the critical infrastructure cybersecurity report into clear lessons that operators and executives can use.
You can also choose a learning-and-education lane. This is powerful for creators who naturally explain well. Think content built around the directory of free cybersecurity courses and resources, the best cybersecurity bootcamps and academies, the global directory of cybersecurity training providers, and even role-based guides such as the cloud security engineer career guide, the threat intelligence analyst career guide, and the cybersecurity instructor career guide.
The best lane is usually the one where three things overlap: you have real understanding, the audience has expensive confusion, and the market has enough depth for repeated content without forced repetition. Pick that intersection and stay there long enough for people to associate your name with something concrete.
3. The Skills That Separate Real Cybersecurity Creators From Shallow Posters
Technical knowledge matters, but it is not enough. Plenty of technically capable people produce unreadable, forgettable, or untrustworthy content because they lack the skills that turn knowledge into audience value.
The first of those skills is translation. Can you explain security audits, processes, and best practices in a way that makes sense to a junior analyst, a compliance lead, and a founder evaluating external support? Can you unpack cybersecurity frameworks like NIST, ISO, and COBIT without turning the article into a terminology graveyard? Can you make incident response plan development and execution feel operational instead of theoretical? Great creators simplify without flattening.
The second skill is topic judgment. Weak creators chase whatever feels loud. Strong creators identify what matters, why it matters now, and who specifically needs the explanation. That means knowing when to write about AI-powered cyberattacks and future defenses, when to interpret deepfake cybersecurity threats, when to analyze the future of zero trust security, and when the audience actually needs a more foundational piece on access control models or SIEM fundamentals.
The third skill is structure. Search engines, readers, AI systems, buyers, and skimmers all reward organization. A strong article has a visible promise, sharp segmentation, useful comparisons, and clear takeaways. A good creator also learns how to mix formats. Long-form evergreen work can be supported by short-form commentary. Tool directories can lead into strategic explainers. Research summaries can feed newsletter curation. Industry reports can become visual charts, clips, and quote cards.
The fourth skill is source discipline. Cybersecurity is full of exaggerated claims, shallow predictions, and recycled takes. Your content gets stronger when it pulls intelligently from quality source ecosystems like the directory of top cybersecurity research organizations and institutes, the best cybersecurity conferences global guide, and rigorous industry analysis such as the NIST cybersecurity framework adoption report, the cybersecurity compliance trends report, and the healthcare compliance cybersecurity report.
The fifth skill is business awareness. The creators who actually build careers understand monetization, audience intent, and trust economics. They know why some readers want education while others want vendor selection help. They understand that a CISO evaluating a sector provider has different needs than someone browsing the top cybersecurity companies worldwide, the best MSSPs guide, or the top 25 cybersecurity consulting firms. That commercial awareness helps you make content that earns attention from audiences who can create opportunities, not just impressions.
Quick Poll: What Result Are You Really Chasing With Cybersecurity Content?
Pick the outcome that matters most, because the right content strategy changes with the target.
4. A Practical Roadmap to Build Your Cybersecurity Content Career
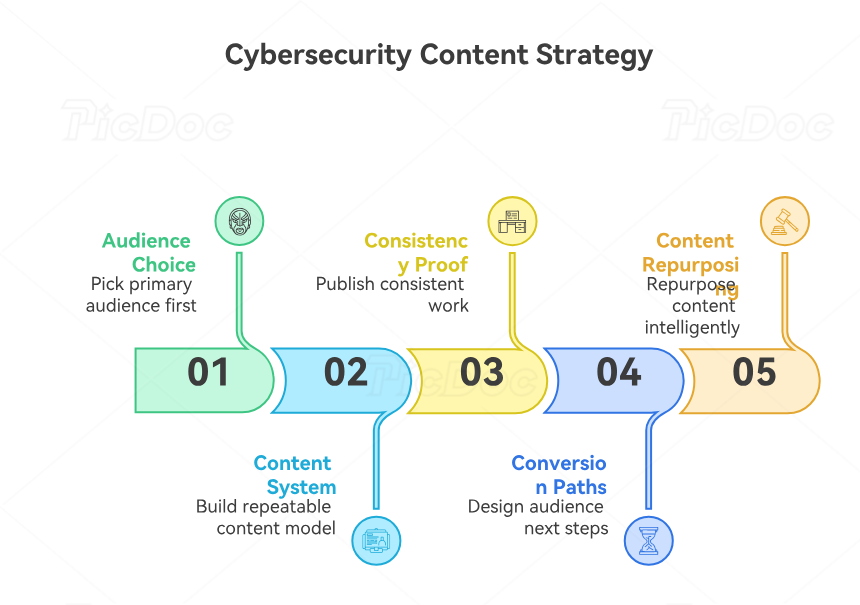
Start by choosing a primary audience. This matters more than platform choice. You can write for security buyers, practitioners, beginners, executives, compliance teams, or career changers. You can create content for sectors like healthcare, finance, education, government, or manufacturing. You can focus on operators, managers, or learners. Until you make this decision, your content will keep sounding vague.
Then choose a repeatable content system. One effective model is to split output into four buckets: evergreen explainers, timely analysis, comparison content, and audience pain-point content. Evergreen explainers might draw on subjects like firewall technologies and configurations, intrusion detection systems deployment, public key infrastructure components, and encryption standards beyond AES and RSA. Timely analysis might cover the future of cloud security, the next generation of cybersecurity standards, or the future of cybersecurity compliance. Comparison content might center on the best email security solutions, the best security awareness training platforms, or the best cybersecurity firms for SMBs. Pain-point content should answer the urgent questions your target audience keeps asking.
Next, build visible proof of consistency. One strong article does not build a career. A body of work does. Publish enough content that people can infer your standards. That also helps algorithms and human readers understand your niche. If you want to be known for sector analysis, create linked clusters around the best cybersecurity companies for retail and e-commerce, the cybersecurity directory for the education sector, the best cybersecurity providers for nonprofits, the best cybersecurity companies for energy and utilities, and the directory of cybersecurity firms for transportation and logistics.
After that, create conversion paths. Content should not only inform. It should also give the audience a next step. That may be subscribing, downloading a checklist, booking consulting, requesting research support, joining a training waitlist, or exploring related content. A creator who understands audience movement can turn attention into opportunity without making the work feel salesy.
Finally, learn to repurpose intelligently. A long article on the emerging cybersecurity threats in cloud environments can become a video, a carousel, a thread, a webinar talking point, and a newsletter section. A post on the annual insider threats report can become a checklist for managers. A deep piece on the cybersecurity incident response report can turn into executive takeaways and team-level lessons. The smartest creators squeeze more value from each research cycle without diluting quality.
5. Monetization, Reputation, and the Mistakes That Kill Momentum
A sustainable cybersecurity content career usually grows through more than one path. Some creators monetize through sponsorships. Some through affiliate revenue on software categories. Some through consulting, research services, ghostwriting, courses, workshops, or paid communities. Others use content as a career asset that attracts better roles, speaking invitations, partnerships, and advisory opportunities. The key is to avoid building an audience that trusts you while publishing in a way that quietly destroys that trust.
The first career-killing mistake is pretending certainty where nuance is required. Cybersecurity readers can smell borrowed conviction. If your tool rankings, trend predictions, or role guides sound overconfident and under-examined, you will lose serious readers fast. This is especially dangerous in future-focused material around the top cybersecurity threats predicted to dominate by 2030, the future of AI-driven cybersecurity tools, the impact of quantum computing on cybersecurity, and the next evolution of privacy regulations.
The second mistake is creating content that is technically accurate but strategically empty. Readers need help making decisions. A list of facts about blockchain in cybersecurity or IoT security breaches does not move anyone unless you translate it into implications, tradeoffs, priorities, and action.
The third mistake is weak audience empathy. Security professionals often write as if everyone starts with the same baseline. They do not. A founder buying managed services, a junior analyst studying how to become a SOC analyst, a specialist pursuing the career path to senior cybersecurity analyst, and a professional exploring the roadmap to cybersecurity compliance officer each need a different explanation style.
The fourth mistake is chasing vanity metrics. Views matter. Reach matters. Neither automatically means career value. A smaller audience of security leaders, tool buyers, or ambitious practitioners can be far more valuable than a bigger audience that rarely converts into trust or opportunity. That is why niche positioning often beats broad commentary.
The fifth mistake is underestimating consistency. Momentum in this space compounds slowly, then suddenly. The creators who look established usually spent a long period publishing into relative quiet while learning what their audience actually cared about. They improved by staying close to the field, reading deeply, listening carefully, and refining their voice around real needs instead of personal ego.
6. FAQs
-
You need enough real understanding to be useful and honest about your limits. Seniority helps, but clarity, rigor, and judgment matter more than inflated status. A mid-level practitioner who explains well and respects nuance can outperform a senior professional who writes shallow content.
-
The best niche sits at the intersection of your actual expertise, audience confusion, and commercial or career relevance. Career content, tool comparisons, sector-specific risk analysis, compliance translation, and hands-on explainer content are all strong options when supported by real depth.
-
Start with the format that best matches your strengths and your audience’s behavior. Long-form articles work well for search and evergreen authority. LinkedIn works well for professional discovery. Newsletters help you own audience relationships. Video works when your explanations benefit from voice, screen sharing, or live examples.
-
By being more useful, more specific, and more structured than the average post. Surface hot takes are crowded. Clear decision support is not. Strong creators win by answering expensive questions better than everyone else.
-
Yes. A strong body of content can signal expertise, communication ability, market awareness, and leadership potential. It can strengthen your position for analyst, engineer, manager, consultant, instructor, and advisory roles.
-
Usually longer than people expect. The first phase is often quiet. That phase still matters because it is where you improve your positioning, quality, and topic judgment. Consistency plus usefulness tends to compound.
-
The best-performing content usually reduces uncertainty around tools, roles, threats, regulations, skills, or market changes. People remember content that helps them decide, not content that only repeats information.